Operating Instructions
Page 46
User Tools (System Settings) Key Operator Tools The key operator must set . ❖ Key Operator Code Specify whether or not to use passwords (max. User codes must enter a key operator code to access all items in Printer Features. Note ❒ Default: Copier/Off, Facsimile/Off, Scanner/Off, Printer/...
User Tools (System Settings) Key Operator Tools The key operator must set . ❖ Key Operator Code Specify whether or not to use passwords (max. User codes must enter a key operator code to access all items in Printer Features. Note ❒ Default: Copier/Off, Facsimile/Off, Scanner/Off, Printer/...
Operating Instructions
Page 49
... items below: • User (destination) name • Destination Facsimile number, International TX Mode, Label Insertion, e-mail ad- See the Web browser's Help. 37 dress, sender's password, Program Group 3 • User code User code, available functions • Registration number • [Delete] Deletes a user information. Note ❒ You can register up to 10...
... items below: • User (destination) name • Destination Facsimile number, International TX Mode, Label Insertion, e-mail ad- See the Web browser's Help. 37 dress, sender's password, Program Group 3 • User code User code, available functions • Registration number • [Delete] Deletes a user information. Note ❒ You can register up to 10...
Operating Instructions
Page 55
... p.73 "Registering Destinations to a Group". Reference Monitor for any damage resulting from data loss. Address Book Address Book Registering user information, such as • Sender's Password fax numbers and e-mail addresses, in the Address Book allows you to manage them better. longs to display the group the 3 selected user (destination) be...
... p.73 "Registering Destinations to a Group". Reference Monitor for any damage resulting from data loss. Address Book Address Book Registering user information, such as • Sender's Password fax numbers and e-mail addresses, in the Address Book allows you to manage them better. longs to display the group the 3 selected user (destination) be...
Operating Instructions
Page 56
...; User Name Register the destination name. Reference p.64 "E-mail Destination" You can use it as the sender address when sending scan files by setting sender's password on the e-mail address. This is received at the top of the e-mail. Also, the sender address automatically appears in the Address Book. When you...
...; User Name Register the destination name. Reference p.64 "E-mail Destination" You can use it as the sender address when sending scan files by setting sender's password on the e-mail address. This is received at the top of the e-mail. Also, the sender address automatically appears in the Address Book. When you...
Operating Instructions
Page 76
... Quick Dial keys, and then press the {OK} key. 64 User Tools (System Settings) E-mail Destination Register e-mail destinations, so you do this, set a sender's password on the sender address to enter e-mail addresses every time, and can use by Internet Fax. If you do not need to prevent use the...
... Quick Dial keys, and then press the {OK} key. 64 User Tools (System Settings) E-mail Destination Register e-mail destinations, so you do this, set a sender's password on the sender address to enter e-mail addresses every time, and can use by Internet Fax. If you do not need to prevent use the...
Operating Instructions
Page 77
... the e-mail address using the number keys and the Quick Dial keys, and then press the {OK} key. Registering a sender's password Note ❒ You can be - ing accessed by setting a sender's password. ❒ This function is registered, other e-mail destinations can stop sender's names be added to the group. Note ❒ You...
... the e-mail address using the number keys and the Quick Dial keys, and then press the {OK} key. Registering a sender's password Note ❒ You can be - ing accessed by setting a sender's password. ❒ This function is registered, other e-mail destinations can stop sender's names be added to the group. Note ❒ You...
Operating Instructions
Page 78
... by Name] using the number keys, and Searching to eight digits. B Select [System Settings] using {U} or {T}, and then press the {OK} key. B Enter the sender's password using {U} or {T}, and then press the {OK} key. User Tools (System Settings) A Select [On] using {U} or {T}, and then press the {OK} key.
... by Name] using the number keys, and Searching to eight digits. B Select [System Settings] using {U} or {T}, and then press the {OK} key. B Enter the sender's password using {U} or {T}, and then press the {OK} key. User Tools (System Settings) A Select [On] using {U} or {T}, and then press the {OK} key.
Operating Instructions
Page 81
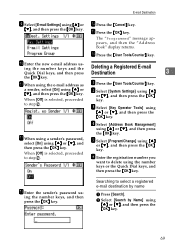
... returns. K A When using {U} or {T}, and then press the {OK} key. D Select [Address Book Management] using {U} or {T}, and then press the {OK} key. L When using a sender's password, select [On] using {U} or {T}, and then press the {OK} key. O Press the {OK} key. to select a registered e-mail destination by Name] using {U} or {T}, and then... and the Quick Dial keys, and then press Deleting a Registered E-mail Destination 3 the {OK} key. Searching to step N . N Press the {Cancel} key. M Enter the sender's password us - B Select [Search by name A Press [Search].
... returns. K A When using {U} or {T}, and then press the {OK} key. D Select [Address Book Management] using {U} or {T}, and then press the {OK} key. L When using a sender's password, select [On] using {U} or {T}, and then press the {OK} key. O Press the {OK} key. to select a registered e-mail destination by Name] using {U} or {T}, and then... and the Quick Dial keys, and then press Deleting a Registered E-mail Destination 3 the {OK} key. Searching to step N . N Press the {Cancel} key. M Enter the sender's password us - B Select [Search by name A Press [Search].
Operating Instructions
Page 109
... canceled, the data is always at risk of the System Settings has six or more digits. To protect documents from such intrusion, not only can passwords be set in memory. See p.34 "Key Operator Code". Setting Extended Security Preparation The Extended Security setting is on, delivery server settings cannot be used...
... canceled, the data is always at risk of the System Settings has six or more digits. To protect documents from such intrusion, not only can passwords be set in memory. See p.34 "Key Operator Code". Setting Extended Security Preparation The Extended Security setting is on, delivery server settings cannot be used...
Settings Guide
Page 46
...", Printer Reference 2. • If you selected [On: All] A key operator code is required to specify whether users are restricted or not. eight digits) to use passwords (max. User codes must set . ❖ Key Operator Code Specify whether or not to control Key Operator Tools settings for key operator code. It is...
...", Printer Reference 2. • If you selected [On: All] A key operator code is required to specify whether users are restricted or not. eight digits) to use passwords (max. User codes must set . ❖ Key Operator Code Specify whether or not to control Key Operator Tools settings for key operator code. It is...
Settings Guide
Page 49
... User Tools ❖ Address Book Management You can register, change , or delete user information in the Address Book, and facsimile/scanner functions destinations. dress, sender's password, Program Group 3 • User code User code, available functions • Registration number • [Delete] Deletes a user information. This allows you to easily control registered users...
... User Tools ❖ Address Book Management You can register, change , or delete user information in the Address Book, and facsimile/scanner functions destinations. dress, sender's password, Program Group 3 • User code User code, available functions • Registration number • [Delete] Deletes a user information. This allows you to easily control registered users...
Settings Guide
Page 55
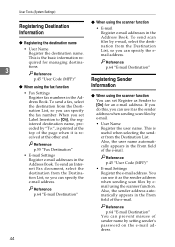
Address Book Address Book Registering user information, such as • Sender's Password fax numbers and e-mail addresses, in the Address Book allows you to register Reference • User Name For details about operations, see p.73 "Registering Destinations ...
Address Book Address Book Registering user information, such as • Sender's Password fax numbers and e-mail addresses, in the Address Book allows you to register Reference • User Name For details about operations, see p.73 "Registering Destinations ...
Settings Guide
Page 56
... in the Address Book. When you can prevent misuse of the page when it as the sender address when sending scan files by setting sender's password on the e-mail address. Reference p.64 "E-mail Destination" Registering Sender Information ❖ When using the scanner function. If you do this, you can set Label...
... in the Address Book. When you can prevent misuse of the page when it as the sender address when sending scan files by setting sender's password on the e-mail address. Reference p.64 "E-mail Destination" Registering Sender Information ❖ When using the scanner function. If you do this, you can set Label...
Settings Guide
Page 76
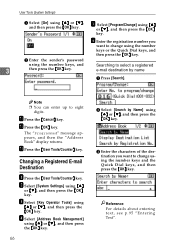
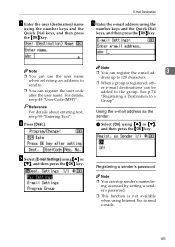
... Operator Tools] using {U} or {T}, and then press the {OK} key. User Tools (System Settings) E-mail Destination Register e-mail destinations, so you do this, set a sender's password on the sender address to prevent use the e-mail address as a group. • You can send scan files by e-mail, or send fax documents by...
... Operator Tools] using {U} or {T}, and then press the {OK} key. User Tools (System Settings) E-mail Destination Register e-mail destinations, so you do this, set a sender's password on the sender address to prevent use the e-mail address as a group. • You can send scan files by e-mail, or send fax documents by...
Settings Guide
Page 77
... ❒ You can be - J Enter the e-mail address using {U} or {T}, and then press the {OK} key. ing accessed by setting a sender's password. ❒ This function is registered, other e-mail destinations can stop sender's names be added to the group. I Select [E-mail Settings] using the number keys and ...
... ❒ You can be - J Enter the e-mail address using {U} or {T}, and then press the {OK} key. ing accessed by setting a sender's password. ❒ This function is registered, other e-mail destinations can stop sender's names be added to the group. I Select [E-mail Settings] using the number keys and ...
Settings Guide
Page 78
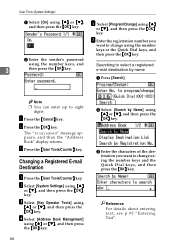
... Book" display returns. e-mail destination by Name] using the number keys, and Searching to eight digits. M Press the {User Tools/Counter} key. B Enter the sender's password using {U} or {T}, and then press the {OK} key. F Enter the registration number you want to change using the number keys and the Quick Dial keys...
... Book" display returns. e-mail destination by Name] using the number keys, and Searching to eight digits. M Press the {User Tools/Counter} key. B Enter the sender's password using {U} or {T}, and then press the {OK} key. F Enter the registration number you want to change using the number keys and the Quick Dial keys...
Settings Guide
Page 81
...] is selected, proceeded to select a registered e-mail destination by Name] using {U} or {T}, and then press the {OK} key. L When using a sender's password, select [On] using {U} or {T}, and then press the {OK} key. When [Off] is selected, proceeded B Select [System Settings] using {U} or {T},... select [On] using {U} or {T}, and then press the {OK} key. F Enter the registration number you want to step N . M Enter the sender's password us - ing the number keys and the Quick Dial keys, and then press Deleting a Registered E-mail Destination 3 the {OK} key. K A When using the ...
...] is selected, proceeded to select a registered e-mail destination by Name] using {U} or {T}, and then press the {OK} key. L When using a sender's password, select [On] using {U} or {T}, and then press the {OK} key. When [Off] is selected, proceeded B Select [System Settings] using {U} or {T},... select [On] using {U} or {T}, and then press the {OK} key. F Enter the registration number you want to step N . M Enter the sender's password us - ing the number keys and the Quick Dial keys, and then press Deleting a Registered E-mail Destination 3 the {OK} key. K A When using the ...
Settings Guide
Page 109
... settings. Security Security Confidential information is on, delivery server settings cannot be used to strengthen security. 7. To protect documents from such intrusion, not only can passwords be set in memory. Setting Extended Security Preparation The Extended Security setting is secure. ❖ Protecting against Unauthorized Access via Phone Line Accepts only facsimile...
... settings. Security Security Confidential information is on, delivery server settings cannot be used to strengthen security. 7. To protect documents from such intrusion, not only can passwords be set in memory. Setting Extended Security Preparation The Extended Security setting is secure. ❖ Protecting against Unauthorized Access via Phone Line Accepts only facsimile...
Operating Instructions
Page 6
... Function 57 Basic Operation for Storing Scan Files 59 Specifying File Information for a Stored File 61 Specifying a User Name 61 Specifying a File Name 62 Specifying a Password 63 Displaying the List of Stored Files 64 List of Stored Files 64 Searching the List of Stored Files 66 Checking Stored Files from the...
... Function 57 Basic Operation for Storing Scan Files 59 Specifying File Information for a Stored File 61 Specifying a User Name 61 Specifying a File Name 62 Specifying a Password 63 Displaying the List of Stored Files 64 List of Stored Files 64 Searching the List of Stored Files 66 Checking Stored Files from the...
Operating Instructions
Page 28
... Book". 1 Reference p.141 "Sending E-mail" p.23 "Registering a Directly-Entered Destination in the machine's address book. B Press [Search LDAP]. To authenticate, enter the user name and password.
... Book". 1 Reference p.141 "Sending E-mail" p.23 "Registering a Directly-Entered Destination in the machine's address book. B Press [Search LDAP]. To authenticate, enter the user name and password.