User Guide
Page 182
...right side of the destination computer, and then press [OK]. 14. Press [Change] under "Login Password". 13. Enter the password again to check the path is selected, the SMB User Name and SMB Password that you can select [Frequent] and one more key for each title. 8. Basic Procedure When Using... first. • [AB], [CD], [EF], [GH], [IJK], [LMN], [OPQ], [RST], [UVW], [XYZ], [1] to [10]: Added to the list of items in "Default User Name / Password (Send)" of the destination computer, and then press [OK]. 12. Press [Connection Test] to confirm, and then press [OK]. 15. Enter the...
...right side of the destination computer, and then press [OK]. 14. Press [Change] under "Login Password". 13. Enter the password again to check the path is selected, the SMB User Name and SMB Password that you can select [Frequent] and one more key for each title. 8. Basic Procedure When Using... first. • [AB], [CD], [EF], [GH], [IJK], [LMN], [OPQ], [RST], [UVW], [XYZ], [1] to [10]: Added to the list of items in "Default User Name / Password (Send)" of the destination computer, and then press [OK]. 12. Press [Connection Test] to confirm, and then press [OK]. 15. Enter the...
User Guide
Page 446
...Volume per User...84 Specifying Limitations for Address Book Auto-program 68 User Lockout Function...70 Specifying the User Lockout Function...71 Canceling Password Lockout...71 Auto Logout...72 Authentication Using an External Device...74 3. Restricting Machine Usage Restricting Usage of the Destination List...75 ... Settings 77 Prohibiting Users from Making Changes to the Address Book...68 Data Carry-over Setting for Print Volume...85 Specifying the Default Maximum Use Count 87 Specifying the Maximum Use Count per User 88 Checking Print Volume per User...90 Printing a List of ...
...Volume per User...84 Specifying Limitations for Address Book Auto-program 68 User Lockout Function...70 Specifying the User Lockout Function...71 Canceling Password Lockout...71 Auto Logout...72 Authentication Using an External Device...74 3. Restricting Machine Usage Restricting Usage of the Destination List...75 ... Settings 77 Prohibiting Users from Making Changes to the Address Book...68 Data Carry-over Setting for Print Volume...85 Specifying the Default Maximum Use Count 87 Specifying the Maximum Use Count per User 88 Checking Print Volume per User...90 Printing a List of ...
User Guide
Page 460
...in the Address Book or change and delete their password, the user administrator can set the machine so that network settings such as an administrator, use the default login user name and login password. File administrator This is the administrator who manages ...machine, and thus ensure correct network operation. 4. Once settings are activated, the default setting items allocated to unauthorized users viewing and using the supervisor's privilege. You can specify passwords to allow the machine to [On]. Specifying Administrator Privileges To specify administrator authentication...
...in the Address Book or change and delete their password, the user administrator can set the machine so that network settings such as an administrator, use the default login user name and login password. File administrator This is the administrator who manages ...machine, and thus ensure correct network operation. 4. Once settings are activated, the default setting items allocated to unauthorized users viewing and using the supervisor's privilege. You can specify passwords to allow the machine to [On]. Specifying Administrator Privileges To specify administrator authentication...
User Guide
Page 461
... data in the machine being lost. Press [System Settings]. 3. Charges may also apply to forget the supervisor login user name and login password. Configuring Administrator Authentication • Be sure not to the service call. 1. Press [ Next]. 5. Set "Admin. This will have to... return the machine to its default state. Press the [User Tools/Counter] key. 2. "Available Settings" appears. 17 Press [User Management], [Machine Management], [Network Management], or [...
... data in the machine being lost. Press [System Settings]. 3. Charges may also apply to forget the supervisor login user name and login password. Configuring Administrator Authentication • Be sure not to the service call. 1. Press [ Next]. 5. Set "Admin. This will have to... return the machine to its default state. Press the [User Tools/Counter] key. 2. "Available Settings" appears. 17 Press [User Management], [Machine Management], [Network Management], or [...
User Guide
Page 467
... then press [OK]. For example: If the address is "admin" and "supervisor" for administrators or supervisors. No login password is no preset default password for supervisors. 5. appears. There is set up. • The Web browser might be configured to use this : [2001:db8::9abc].... a screen for supervisors is displayed. • If you log in appears. Enter the login name and password of the administrator privileges associated with zeros. The default login name for administrators is "admin" and that has multiple administrator privileges, one of an administrator, and ...
... then press [OK]. For example: If the address is "admin" and "supervisor" for administrators or supervisors. No login password is no preset default password for supervisors. 5. appears. There is set up. • The Web browser might be configured to use this : [2001:db8::9abc].... a screen for supervisors is displayed. • If you log in appears. Enter the login name and password of the administrator privileges associated with zeros. The default login name for administrators is "admin" and that has multiple administrator privileges, one of an administrator, and ...
User Guide
Page 469
...Administrator]. 25 Supervisor Supervisor The supervisor can delete an administrator's password and specify a new one . This will have to return the machine to its default state. Press [Administrator Tools]. 4. If any of the administrators forgets their password or if any of charge. • You cannot specify ... in using the supervisor's user name and password, you cannot use normal functions or specify defaults. For details on how to forget the supervisor login user name and login password. We recommend changing the login user name and login password. • For the characters that can be...
...Administrator]. 25 Supervisor Supervisor The supervisor can delete an administrator's password and specify a new one . This will have to return the machine to its default state. Press [Administrator Tools]. 4. If any of the administrators forgets their password or if any of charge. • You cannot specify ... in using the supervisor's user name and password, you cannot use normal functions or specify defaults. For details on how to forget the supervisor login user name and login password. We recommend changing the login user name and login password. • For the characters that can be...
User Guide
Page 483
..., see p.21 "Usable characters for "User Authentication Management". The functions you select here become the default Basic Authentication settings that can be used for user names and passwords". 39 Press the [Login/Logout] key. Specify the necessary settings in the Address Book If you.... Basic Authentication 12. User authentication can specify access limits and usage limits to the machine's functions for login user names and passwords, see p.80 "Limiting Available Functions". 13. Users must have enabled user authentication, you want to be automatically logged out. Specifying...
..., see p.21 "Usable characters for "User Authentication Management". The functions you select here become the default Basic Authentication settings that can be used for user names and passwords". 39 Press the [Login/Logout] key. Specify the necessary settings in the Address Book If you.... Basic Authentication 12. User authentication can specify access limits and usage limits to the machine's functions for login user names and passwords, see p.80 "Limiting Available Functions". 13. Users must have enabled user authentication, you want to be automatically logged out. Specifying...
User Guide
Page 488
...be used for login user names and passwords, see p.50 "Creating the Server Certificate". • Under Windows Authentication, you do this account is enabled, users are registered in the Address Book and can use the functions available under "*Default Group". • Under Windows Authentication, ...Address Book. • When accessing the machine subsequently, you can select whether or not to the computer and change password at next logon" at password configuration, first log on the server is changed, information registered in the machine may be overwritten when authentication is performed...
...be used for login user names and passwords, see p.50 "Creating the Server Certificate". • Under Windows Authentication, you do this account is enabled, users are registered in the Address Book and can use the functions available under "*Default Group". • Under Windows Authentication, ...Address Book. • When accessing the machine subsequently, you can select whether or not to the computer and change password at next logon" at password configuration, first log on the server is changed, information registered in the machine may be overwritten when authentication is performed...
User Guide
Page 511
No password is not displayed. For details on ". The default setting is "off ] • To exclude parallel and USB connections from printer job authentication. Printer Job Authentication "authfree" Command When [Simple (Limitation)] is selected under ... address mask settings msh> authfree "ID" mask6_addr1 masklen Parallel/USB settings msh> authfree [parallel|usb] [on|off ". • Always specify either "parallel" or "USB". The default user name for logging in to be excluded from printer job authentication, set this to "on how to login to five access ranges can be...
No password is not displayed. For details on ". The default setting is "off ] • To exclude parallel and USB connections from printer job authentication. Printer Job Authentication "authfree" Command When [Simple (Limitation)] is selected under ... address mask settings msh> authfree "ID" mask6_addr1 masklen Parallel/USB settings msh> authfree [parallel|usb] [on|off ". • Always specify either "parallel" or "USB". The default user name for logging in to be excluded from printer job authentication, set this to "on how to login to five access ranges can be...
User Guide
Page 514
...Lockout function prevents further login attempts under the same user name. Default setting • Inactive 5 • Inactive 60 min. Even if the locked out user enters the correct password later, authentication will fail and the machine cannot be made using..., file administrator, machine administrator Unlocking administrator user administrator supervisor 70 Configuring User Authentication User Lockout Function If an incorrect password is canceled. 1-9999 min. Under other authentication methods, the lockout function protects supervisor and administrator accounts only, not...
...Lockout function prevents further login attempts under the same user name. Default setting • Inactive 5 • Inactive 60 min. Even if the locked out user enters the correct password later, authentication will fail and the machine cannot be made using..., file administrator, machine administrator Unlocking administrator user administrator supervisor 70 Configuring User Authentication User Lockout Function If an incorrect password is canceled. 1-9999 min. Under other authentication methods, the lockout function protects supervisor and administrator accounts only, not...
User Guide
Page 610
5. This section explains telnet commands for HTTPS communication. 10. No password is "admin". Enhanced Network Security 6. Wait for logging in "IPsec". 9. The default user name for about logging in to telnet and telnet operations, see "Using telnet", Connecting ...key manual settings, SA setting 1-4 values • Encryption key manual settings, default setting values • Encryption key auto exchange settings, IKE setting 1-4 values • Encryption key auto exchange settings, IKE default setting values Display current settings portions msh> ipsec -p • Displays IPsec...
5. This section explains telnet commands for HTTPS communication. 10. No password is "admin". Enhanced Network Security 6. Wait for logging in "IPsec". 9. The default user name for about logging in to telnet and telnet operations, see "Using telnet", Connecting ...key manual settings, SA setting 1-4 values • Encryption key manual settings, default setting values • Encryption key auto exchange settings, IKE setting 1-4 values • Encryption key auto exchange settings, IKE default setting values Display current settings portions msh> ipsec -p • Displays IPsec...
User Guide
Page 694
... User Name", "Proxy Password", and "Exception Addresses". Log out. Restricting User Browser Functions You can register and manage bookmarks, including changing, deleting, importing and exporting. Screen settings by user settings Home Screen by User Specify whether or not to enable the home screen to change, and change the setting. 5. Default: [Allow] 250...
... User Name", "Proxy Password", and "Exception Addresses". Log out. Restricting User Browser Functions You can register and manage bookmarks, including changing, deleting, importing and exporting. Screen settings by user settings Home Screen by User Specify whether or not to enable the home screen to change, and change the setting. 5. Default: [Allow] 250...
User Guide
Page 697
... be imported or exported • Address book • Programs (fax function) • Programs (printer function) • Scanner function programs that include password settings • User stamp in the copy default settings • Settings for configuring from telnet • The file format for exports is CSV. • When images are inserted into a home...
... be imported or exported • Address book • Programs (fax function) • Programs (printer function) • Scanner function programs that include password settings • User stamp in the copy default settings • Settings for configuring from telnet • The file format for exports is CSV. • When images are inserted into a home...
User Guide
Page 707
... If you can limit operations such as an administrator checks the job history using a network connection for which a password is entered ten times. Default: [Simple Encryption] Restrict Display of the screen. Because information identifying registered users cannot be specified by the user ... ) appears in the Address Book. For details about the registered files. Encrypt the individual settings of the password appended to a job and processes it is entered. 263 Default: [Off] Encrypt User Custom Settings & Address Book This can be displayed as For example, when someone...
... If you can limit operations such as an administrator checks the job history using a network connection for which a password is entered ten times. Default: [Simple Encryption] Restrict Display of the screen. Because information identifying registered users cannot be specified by the user ... ) appears in the Address Book. For details about the registered files. Encrypt the individual settings of the password appended to a job and processes it is entered. 263 Default: [Off] Encrypt User Custom Settings & Address Book This can be displayed as For example, when someone...
User Guide
Page 708
...destination in the Address Book by pressing [Prg. Only the user administrator can be able to the destinations registered in the machine can change their password. Default: [Do not Prohibit] If you use "Restrict Use of Destinations (Fax)" and "Restrict Use of the Destination List". If "Restrict Use ..." can register fax numbers only. If you set these functions to [On], the user registered as destination can change items other than the password. If you cannot use [Forwarding] or [Transfer Box] under the fax function, files stored in the Address Book. To prevent stored files...
...destination in the Address Book by pressing [Prg. Only the user administrator can be able to the destinations registered in the machine can change their password. Default: [Do not Prohibit] If you use "Restrict Use of Destinations (Fax)" and "Restrict Use of the Destination List". If "Restrict Use ..." can register fax numbers only. If you set these functions to [On], the user registered as destination can change items other than the password. If you cannot use [Forwarding] or [Transfer Box] under the fax function, files stored in the Address Book. To prevent stored files...
User Guide
Page 710
If you select [Prohibit], the setting can be specified by e-mail. Default: [Do not Prohibit] Password Policy This can be specified by the network administrator. Default: [Off] Settings by SNMPv1, v2 This can be specified by the user administrator. When the machine is accessed using...firmware structure change detection is displayed on the control panel and on the control panel screen. Default: [Do not Prohibit] Device Access Violation This can specify response delay time for the password. If the "Max. If the number of characters selected from upper-case letters, lower-...
If you select [Prohibit], the setting can be specified by e-mail. Default: [Do not Prohibit] Password Policy This can be specified by the network administrator. Default: [Off] Settings by SNMPv1, v2 This can be specified by the user administrator. When the machine is accessed using...firmware structure change detection is displayed on the control panel and on the control panel screen. Default: [Do not Prohibit] Device Access Violation This can specify response delay time for the password. If the "Max. If the number of characters selected from upper-case letters, lower-...
User Guide
Page 711
...Delay Time Specify the authentication delay time when an access violation is sent to enter the number between "0" and "500", and then press [ ]. Default: [3] • Simultns. of hosts accessing the machine at one time. If the "Max. of Access" is received frequently, check the content.... The access session is over, the logged counts of authentication requests exceeds the setting, the system classifies the access session as a password attack. Specifying the Extended Security Functions In "Simultns. Use the number keys to the machine administrator by the machine administrator. When the...
...Delay Time Specify the authentication delay time when an access violation is sent to enter the number between "0" and "500", and then press [ ]. Default: [3] • Simultns. of hosts accessing the machine at one time. If the "Max. of Access" is received frequently, check the content.... The access session is over, the logged counts of authentication requests exceeds the setting, the system classifies the access session as a password attack. Specifying the Extended Security Functions In "Simultns. Use the number keys to the machine administrator by the machine administrator. When the...
User Guide
Page 712
... enter the number between "0" and "60", and then press [ ]. Use the number keys to enter the time between "50" and "200", and then press [ ]. Default: [200] • Password Entry Host Limit Specify the number of Access] and [Measurement Time], you can be specified by a user. Use the number keys to enter the...
... enter the number between "0" and "60", and then press [ ]. Use the number keys to enter the time between "50" and "200", and then press [ ]. Default: [200] • Password Entry Host Limit Specify the number of Access] and [Measurement Time], you can be specified by a user. Use the number keys to enter the...
User Guide
Page 713
Specifying the Extended Security Functions Specify the monitoring interval of "Managed User Host Limit" and "Password Entry Host Limit". Default: [3] • Off Default: [Off] 269 Use the number keys to enter the time between "1" and "10", and then press [ ].
Specifying the Extended Security Functions Specify the monitoring interval of "Managed User Host Limit" and "Password Entry Host Limit". Default: [3] • Off Default: [Off] 269 Use the number keys to enter the time between "1" and "10", and then press [ ].
User Guide
Page 755
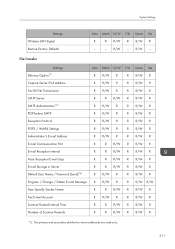
... Mach N/W File Unset Set R R R/W R R/W R - - Reception E-mail Size R R R/W R R/W R E-mail Storage in Server R R R/W R R/W R Default User Name / Password (Send)*4 R R/W R R R/W R Program / Change / Delete E-mail Message R R/W R R R/W R/W Auto Specify Sender Name R R R/W R R/W R Fax E-mail Account R R/W R R R/W R Scanner Resend Interval Time R R R/W R R/W R Number of Scanner Resends R R R/W R R/W R *3 The primary and secondary ...
... Mach N/W File Unset Set R R R/W R R/W R - - Reception E-mail Size R R R/W R R/W R E-mail Storage in Server R R R/W R R/W R Default User Name / Password (Send)*4 R R/W R R R/W R Program / Change / Delete E-mail Message R R/W R R R/W R/W Auto Specify Sender Name R R R/W R R/W R Fax E-mail Account R R/W R R R/W R Scanner Resend Interval Time R R R/W R R/W R Number of Scanner Resends R R R/W R R/W R *3 The primary and secondary ...