User Guide
Page 8
... job. Convenient Functions Describes how to register frequently used functions, troubleshooting when an error message appears, etc., summaries are explained. User Guide Regarding the basic usage of this machine, frequently used settings, customize the Home Screen, and display a Web page on the ...First Before using the machine, operating instructions, character input methods, and how to do or by keyword. Troubleshooting Provides a guide for this machine. It also describes how to load originals and sheets and about their specifications. It also describes the specifications...
... job. Convenient Functions Describes how to register frequently used functions, troubleshooting when an error message appears, etc., summaries are explained. User Guide Regarding the basic usage of this machine, frequently used settings, customize the Home Screen, and display a Web page on the ...First Before using the machine, operating instructions, character input methods, and how to do or by keyword. Troubleshooting Provides a guide for this machine. It also describes how to load originals and sheets and about their specifications. It also describes the specifications...
User Guide
Page 9
... manual when setting the enhanced security functions, or user and administrator authentication. Print Describes how to machine types. 8 Also explains how to change User Tools settings and how to install and configure each driver. Security Guide This manual is included in the Address Book. ...Driver Installation Guide Describes how to register information in the drivers CD. This manual ...
... manual when setting the enhanced security functions, or user and administrator authentication. Print Describes how to machine types. 8 Also explains how to change User Tools settings and how to install and configure each driver. Security Guide This manual is included in the Address Book. ...Driver Installation Guide Describes how to register information in the drivers CD. This manual ...
User Guide
Page 11
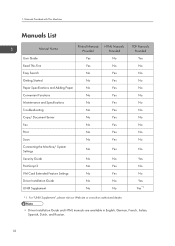
1. Manuals Provided with This Machine Manuals List Manual Name Printed Manuals Provided User Guide Yes Read This First Yes Easy Search No Getting Started No Paper Specifications and Adding Paper No Convenient Functions No Maintenance and Specifications No ...Troubleshooting No Copy/ Document Server No Fax No Print No Scan No Connecting the Machine/ System Settings No Security Guide No PostScript 3 No VM Card Extended Feature Settings No Driver Installation Guide No UNIX Supplement No HTML Manuals Provided No No Yes Yes Yes Yes Yes Yes Yes Yes Yes Yes ...
1. Manuals Provided with This Machine Manuals List Manual Name Printed Manuals Provided User Guide Yes Read This First Yes Easy Search No Getting Started No Paper Specifications and Adding Paper No Convenient Functions No Maintenance and Specifications No ...Troubleshooting No Copy/ Document Server No Fax No Print No Scan No Connecting the Machine/ System Settings No Security Guide No PostScript 3 No VM Card Extended Feature Settings No Driver Installation Guide No UNIX Supplement No HTML Manuals Provided No No Yes Yes Yes Yes Yes Yes Yes Yes Yes Yes ...
User Guide
Page 55
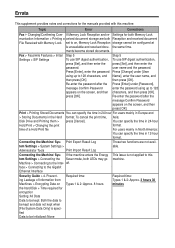
...[Enter], enter the password using up to on the screen, and then press [OK]. Press [Enter] under [User Name], enter the user name, and then press [OK]. Print Export Result Log tem Settings > System Settings > Administrator Tools Print Import ...Result Log Those two functions are both LEDs may go Machine > Connecting to be initialized: None Required time: Types 1 & 2: Approx. 8 hours Required time: Types 1 & 2: Approx. 3 hours 30 minutes Security Guide...
...[Enter], enter the password using up to on the screen, and then press [OK]. Press [Enter] under [User Name], enter the user name, and then press [OK]. Print Export Result Log tem Settings > System Settings > Administrator Tools Print Import ...Result Log Those two functions are both LEDs may go Machine > Connecting to be initialized: None Required time: Types 1 & 2: Approx. 8 hours Required time: Types 1 & 2: Approx. 3 hours 30 minutes Security Guide...
User Guide
Page 56
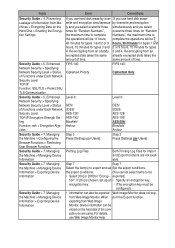
... Communication FIPS 140: Ciphertext Priority FIPS 140: Ciphertext Only Security Guide > 5. Managing the Machine > Configuring the Browser Functions > Restricting User Browser Functions Step 3 Press [Settings par Users]. Step 3 Press [Settings per Users]. Security Guide > 7. exported) tion". encryption key. (The encryption key ...-128/ AES-192/ Blowfish/ Arcfour Level 0: DES/ 3DES/ AES-128/ AES-192/ AES-256/ Blowfish/ Arcfour Security Guide > 7. Managing the Machine > Managing Device Information Printing Log Files Both Printing Log Files for types 4. from an encrypted state...
... Communication FIPS 140: Ciphertext Priority FIPS 140: Ciphertext Only Security Guide > 5. Managing the Machine > Configuring the Browser Functions > Restricting User Browser Functions Step 3 Press [Settings par Users]. Step 3 Press [Settings per Users]. Security Guide > 7. exported) tion". encryption key. (The encryption key ...-128/ AES-192/ Blowfish/ Arcfour Level 0: DES/ 3DES/ AES-128/ AES-192/ AES-256/ Blowfish/ Arcfour Security Guide > 7. Managing the Machine > Managing Device Information Printing Log Files Both Printing Log Files for types 4. from an encrypted state...
User Guide
Page 57
... > Managing Device When the device setting informa- Personal Boxes, Information Boxes, or Transfer Boxes cannot be imported is set with the User Parameter (switch 10, bit 7). Managing Device Informa- •• The device configurations of the Output Mode parameter other than [Print... imported from Information Boxes may not print. If the number of transmission logs reaches the maximum, further communication may occur. Security Guide > 5. Print Export Result Log tings > Administrator Tools Corrections Step 7 Specify the encryption key that the device settings are not...
... > Managing Device When the device setting informa- Personal Boxes, Information Boxes, or Transfer Boxes cannot be imported is set with the User Parameter (switch 10, bit 7). Managing Device Informa- •• The device configurations of the Output Mode parameter other than [Print... imported from Information Boxes may not print. If the number of transmission logs reaches the maximum, further communication may occur. Security Guide > 5. Print Export Result Log tings > Administrator Tools Corrections Step 7 Specify the encryption key that the device settings are not...
User Guide
Page 59
User Guide What You Can Do with This Machine Getting Started Copy Fax Print Scan Document Server Web Image Monitor Adding Paper and Toner Troubleshooting Appendix For information not in "Read This First" before you use , be sure to the HTML/PDF files on the supplied CD-ROM. Read this manual carefully before using the machine. For safe and correct use this manual, refer to read the Safety Information in this machine and keep it handy for future reference.
User Guide What You Can Do with This Machine Getting Started Copy Fax Print Scan Document Server Web Image Monitor Adding Paper and Toner Troubleshooting Appendix For information not in "Read This First" before you use , be sure to the HTML/PDF files on the supplied CD-ROM. Read this manual carefully before using the machine. For safe and correct use this manual, refer to read the Safety Information in this machine and keep it handy for future reference.
User Guide
Page 83
... on the hard disk to prevent the information from leaking out. • You can limit the volume of the usage of the machine for each user. • See Security Guide . 23
... on the hard disk to prevent the information from leaking out. • You can limit the volume of the usage of the machine for each user. • See Security Guide . 23
User Guide
Page 85
... printed document. You Can Prevent an Unauthorized Copy You Can Prevent an Unauthorized Copy You can print embedded pattern on paper to notify users that unauthorized copying is being attempted. CJQ613 • Using the printer driver, you can embed text in the copy, discouraging such ...unauthorized copying. • For details, see the printer driver Help, Print , and Security Guide . 25 If the document is equipped with the Copy Data Security unit, protected pages are grayed out before being copied. If a document protected ...
... printed document. You Can Prevent an Unauthorized Copy You Can Prevent an Unauthorized Copy You can print embedded pattern on paper to notify users that unauthorized copying is being attempted. CJQ613 • Using the printer driver, you can embed text in the copy, discouraging such ...unauthorized copying. • For details, see the printer driver Help, Print , and Security Guide . 25 If the document is equipped with the Copy Data Security unit, protected pages are grayed out before being copied. If a document protected ...
User Guide
Page 109
... or Web pages to the [Home] screen using the browser function. Delete unused icons if the limit is reached. For details, see Security Guide . 49 Adding icons to the [Home] screen. Shortcut icon You can also review icons of functions and embedded software applications that are registered... to Favorites by User cannot be registered to Web Image Monitor as an administrator. For details about kinds of Icons on the machine's hard disk. Adding Icons...
... or Web pages to the [Home] screen using the browser function. Delete unused icons if the limit is reached. For details, see Security Guide . 49 Adding icons to the [Home] screen. Shortcut icon You can also review icons of functions and embedded software applications that are registered... to Favorites by User cannot be registered to Web Image Monitor as an administrator. For details about kinds of Icons on the machine's hard disk. Adding Icons...
User Guide
Page 121
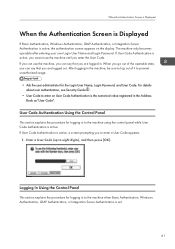
...then press [OK]. For details about user authentication, see Security Guide . • User Code to enter a User Code appears. 1. The machine only becomes operable after entering your own Login User Name and Login Password. If User Code Authentication is set. 61 User Code Authentication Using the Control Panel This ...prompting you are logged out. Logging In Using the Control Panel This section explains the procedure for the Login User Name, Login Password, and User Code. If User Code Authentication is the numerical value registered in the machine, be sure to log out of the operable ...
...then press [OK]. For details about user authentication, see Security Guide . • User Code to enter a User Code appears. 1. The machine only becomes operable after entering your own Login User Name and Login Password. If User Code Authentication is set. 61 User Code Authentication Using the Control Panel This ...prompting you are logged out. Logging In Using the Control Panel This section explains the procedure for the Login User Name, Login Password, and User Code. If User Code Authentication is the numerical value registered in the machine, be sure to log out of the operable ...
User Guide
Page 168
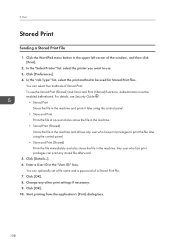
.... 5. Click [Preferences]. 4. Click the WordPad menu button in the machine and allows any user who has print privileges can print any other print settings if necessary. 9. 5. For details, see Security Guide . • Stored Print Stores the file in the machine and prints it later using the... control panel. • Store and Print (Shared) Prints the file immediately and also stores the file in the "User ID:" box. Click [OK]. 10.
.... 5. Click [Preferences]. 4. Click the WordPad menu button in the machine and allows any user who has print privileges can print any other print settings if necessary. 9. 5. For details, see Security Guide . • Stored Print Stores the file in the machine and prints it later using the... control panel. • Store and Print (Shared) Prints the file immediately and also stores the file in the "User ID:" box. Click [OK]. 10.
User Guide
Page 242
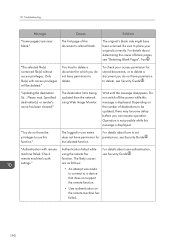
...Authentication Screen is Displayed", Getting Started . authentication. continues to set . You may have permission for permissions, see Security Guide . The logged in user name For details about removing jammed paper, see "When the Authentication Screen is Displayed", Getting Started . The Authentication ... side down. 171 For details about the correct login user name and login password, see Security Guide . When You Have Problems Operating the Machine Problem Causes Solutions The user code entry screen is Users are printed on the reverse side of the paper. ...
...Authentication Screen is Displayed", Getting Started . authentication. continues to set . You may have permission for permissions, see Security Guide . The logged in user name For details about removing jammed paper, see "When the Authentication Screen is Displayed", Getting Started . The Authentication ... side down. 171 For details about the correct login user name and login password, see Security Guide . When You Have Problems Operating the Machine Problem Causes Solutions The user code entry screen is Users are printed on the reverse side of the paper. ...
User Guide
Page 245
... while, and then retry the changed from the display panel or Web Image Monitor. Wait for about specifying print volume limits, see Security Guide . • To view the status of A3 . appears. And then click [Print Job History] in standby mode or performing an operation... cannot be canceled. • For details about 30 minutes. Cannot use by another function. appears. "Home is being edited by users who have reached their print volume limit. Troubleshooting Problem Causes Solutions "Shutting down procedure has begun because the main power switch was in...
... while, and then retry the changed from the display panel or Web Image Monitor. Wait for about specifying print volume limits, see Security Guide . • To view the status of A3 . appears. And then click [Print Job History] in standby mode or performing an operation... cannot be canceled. • For details about 30 minutes. Cannot use by another function. appears. "Home is being edited by users who have reached their print volume limit. Troubleshooting Problem Causes Solutions "Shutting down procedure has begun because the main power switch was in...
User Guide
Page 248
... paper, see "Duplex Copying", Copy/ Document Server . "Clean the scanning glass. (Located next to the exposure glass.)" The scanning glass or guide plate of the Document Server. • If you want to store the scanned pages as 1 file?" The number of sheets that can be used...will be used with paper size selected. The Punch function cannot be used. For details about paper, see Security Guide . 177 "Exceeded the maximum number of pages the user is dirty. When Messages Are Displayed on the Control Panel Message Causes Solutions "Cannot punch this size." "Cannot ...
... paper, see "Duplex Copying", Copy/ Document Server . "Clean the scanning glass. (Located next to the exposure glass.)" The scanning glass or guide plate of the Document Server. • If you want to store the scanned pages as 1 file?" The number of sheets that can be used...will be used with paper size selected. The Punch function cannot be used. For details about paper, see Security Guide . 177 "Exceeded the maximum number of pages the user is dirty. When Messages Are Displayed on the Control Panel Message Causes Solutions "Cannot punch this size." "Cannot ...
User Guide
Page 251
...If other messages appear, follow their instructions. 180 Only file(s) with access privileges will be stored in user name does For details about Memory Full Auto Scan Restart, see Security Guide . The scanned originals exceed the number of pages that can be sequential. Remove all copies, and then...by the person who created the file. The machine checked if the remaining originals should be displayed. The machine will make copies of User Tools to use this case, the resulting sorted pages will not be copied, after the scanned originals were printed. For details about...
...If other messages appear, follow their instructions. 180 Only file(s) with access privileges will be stored in user name does For details about Memory Full Auto Scan Restart, see Security Guide . The scanned originals exceed the number of pages that can be sequential. Remove all copies, and then...by the person who created the file. The machine checked if the remaining originals should be displayed. The machine will make copies of User Tools to use this case, the resulting sorted pages will not be copied, after the scanned originals were printed. For details about...
User Guide
Page 261
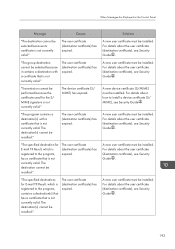
...You tried to delete a document for stored documents, or to delete a document you do not have permission to delete, see Security Guide . • An attempt was made to connect to use this message is displayed. Depending on the remote machine has failed. ... permission for which you can resume operation. "Updating the destination list... Wait until the message disappears. For details about user authentication, see Security Guide . Please wait. Troubleshooting Message Causes Solutions "Some page(s) are as follows: For details about determining the cause of ...
...You tried to delete a document for stored documents, or to delete a document you do not have permission to delete, see Security Guide . • An attempt was made to connect to use this message is displayed. Depending on the remote machine has failed. ... permission for which you can resume operation. "Updating the destination list... Wait until the message disappears. For details about user authentication, see Security Guide . Please wait. Troubleshooting Message Causes Solutions "Some page(s) are as follows: For details about determining the cause of ...
User Guide
Page 262
...the device connected via the remote fax function has failed. • The user does not have permission to set permissions, see Security Guide . 191 The remote fax function does not support User Code Authentication. "Connection with the remote machine has failed. "Connection with the... remote machine has failed. Check the remote machine status." User Code Authentication is set for the ...
...the device connected via the remote fax function has failed. • The user does not have permission to set permissions, see Security Guide . 191 The remote fax function does not support User Code Authentication. "Connection with the remote machine has failed. "Connection with the... remote machine has failed. Check the remote machine status." User Code Authentication is set for the ...
User Guide
Page 263
...see the [Check / Stop Transmission File] screen. 192 The hard disk became full after using the remote fax function, disable User Code Authentication. The file is correctly connected to scan an original. Check the remote machine status." When using the remote fax... use or the file transmission has completed." Troubleshooting Message Causes Solutions "Connection with remote machine, see Security Guide . When you attempt to the machine. • For details about user code authentication, see "Sending/ Receiving Documents Using a Remote Machine (Remote Fax)", Fax . A timeout...
...see the [Check / Stop Transmission File] screen. 192 The hard disk became full after using the remote fax function, disable User Code Authentication. The file is correctly connected to scan an original. Check the remote machine status." When using the remote fax... use or the file transmission has completed." Troubleshooting Message Causes Solutions "Connection with remote machine, see Security Guide . When you attempt to the machine. • For details about user code authentication, see "Sending/ Receiving Documents Using a Remote Machine (Remote Fax)", Fax . A timeout...
User Guide
Page 264
... certificate (S/ MIME) has expired. "The specified destinations for E-mail TX Result, which is registered to install a device certificate (S/ MIME), see Security Guide . For details about the user certificate (destination certificate), see Security Guide . A new device certificate (S/MIME) must be selected because it contains a destination with a certificate that is not currently valid. "The group...
... certificate (S/ MIME) has expired. "The specified destinations for E-mail TX Result, which is registered to install a device certificate (S/ MIME), see Security Guide . For details about the user certificate (destination certificate), see Security Guide . A new device certificate (S/MIME) must be selected because it contains a destination with a certificate that is not currently valid. "The group...