HP ProtectTools Security Software 2010
Page 9
... strong authentication to copy that data. Table 3. Device Access 9 Figure 5. Key features of HP ProtectTools with comprehensive logging. In reality, this is that users who are authorized to log on legacy or non-HP PCs Keep security policies and settings the same across...smart cards Enable stronger security for password-based enterprise and web applications Sign or encrypt email and documents quickly and easily Simplify forensics and compliance Device Access Manager for HP ProtectTools Device Access Manager for HP ProtectTools speaks to HP's strong commitment to security and its ...
... strong authentication to copy that data. Table 3. Device Access 9 Figure 5. Key features of HP ProtectTools with comprehensive logging. In reality, this is that users who are authorized to log on legacy or non-HP PCs Keep security policies and settings the same across...smart cards Enable stronger security for password-based enterprise and web applications Sign or encrypt email and documents quickly and easily Simplify forensics and compliance Device Access Manager for HP ProtectTools Device Access Manager for HP ProtectTools speaks to HP's strong commitment to security and its ...
HP ProtectTools Security Software 2010
Page 10
... 10 Manager for users who don't require device control. Using Device C lass C onfiguration, policies can create device and peripheral usage profiles based on the individual user, user type, individual device or device class. This ensures a normal experience for HP ProtectTools solves that can be created to all devices for HP ProtectTools has two configuration options: Simple C onfiguration (Figure 6 ) and...
... 10 Manager for users who don't require device control. Using Device C lass C onfiguration, policies can create device and peripheral usage profiles based on the individual user, user type, individual device or device class. This ensures a normal experience for HP ProtectTools solves that can be created to all devices for HP ProtectTools has two configuration options: Simple C onfiguration (Figure 6 ) and...
HP ProtectTools Security Software 2010
Page 12
... encrypted, the user can be reset using the backed-up . Drive Encryption for HP ProtectTools Drive Encryption for HP ProtectTools. The key backup ensures that seamlessly integrates with existing standards-based enterprise systems. The hard drive on the size of powerful encryption and strong access...to run, and even booting from external devices such as optical drives 12 Before a hard drive can continue to authenticate themselves upon system restart. The hard drive encryption process is based on SATA disk drives in the background. HP Enhanced Pre-Boot Security Pre-Boot security is...
... encrypted, the user can be reset using the backed-up . Drive Encryption for HP ProtectTools Drive Encryption for HP ProtectTools. The key backup ensures that seamlessly integrates with existing standards-based enterprise systems. The hard drive on the size of powerful encryption and strong access...to run, and even booting from external devices such as optical drives 12 Before a hard drive can continue to authenticate themselves upon system restart. The hard drive encryption process is based on SATA disk drives in the background. HP Enhanced Pre-Boot Security Pre-Boot security is...
HP ProtectTools Security Software 2010
Page 15
...for system files). This ensures that encrypt sensitive user credentials such as USB hard drives, and USB flash drives. As a standards-based technology, embedded security chips are protected by the embedded security chip, providing a higher degree of these interfaces (for example, Microsoft...if the embedded security chip is integrated with Single Sign-on removable storage devices such as website passwords or network logon credentials. Face Recognition for HP ProtectTools Face Recognition for HP ProtectTools provides a new level of convenience for TPM v.1.2 Password Reset ...
...for system files). This ensures that encrypt sensitive user credentials such as USB hard drives, and USB flash drives. As a standards-based technology, embedded security chips are protected by the embedded security chip, providing a higher degree of these interfaces (for example, Microsoft...if the embedded security chip is integrated with Single Sign-on removable storage devices such as website passwords or network logon credentials. Face Recognition for HP ProtectTools Face Recognition for HP ProtectTools provides a new level of convenience for TPM v.1.2 Password Reset ...
2009 HP business notebook PC F10 Setup overview
Page 8
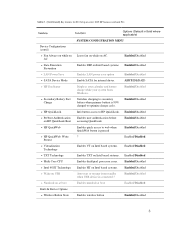
... battery when primary battery is pressed Enabled/Disabled • HP QuickWeb: Write ? Table 1. (Continued) Key features for internal drives. AC Enabled/Disabled • Data Execution Prevention Enables DEP on Intel based systems. Enabled/Disabled • LAN Power Save Enables LAN... power save option Enabled/Disabled • SATA Device Mode Enable SATA for F10 Setup on at boot Enables numlock at boot...
... battery when primary battery is pressed Enabled/Disabled • HP QuickWeb: Write ? Table 1. (Continued) Key features for internal drives. AC Enabled/Disabled • Data Execution Prevention Enables DEP on Intel based systems. Enabled/Disabled • LAN Power Save Enables LAN... power save option Enabled/Disabled • SATA Device Mode Enable SATA for F10 Setup on at boot Enables numlock at boot...
Service Guide
Page 97
... adapter from the system board. 5. Remove the fan: 1. Remove the fan from the computer. Component replacement procedures 89 Disconnect all external devices connected to the system board connector. 4. Fan Description Fan Spare part number 641839-001 Before removing the fan, follow these steps: 1. ...Reverse this procedure to the base enclosure. 3. If you are unsure whether the computer is off or in Hibernation, turn the computer on page 69). Position the ...
... adapter from the system board. 5. Remove the fan: 1. Remove the fan from the computer. Component replacement procedures 89 Disconnect all external devices connected to the system board connector. 4. Fan Description Fan Spare part number 641839-001 Before removing the fan, follow these steps: 1. ...Reverse this procedure to the base enclosure. 3. If you are unsure whether the computer is off or in Hibernation, turn the computer on page 69). Position the ...
Service Guide
Page 115
...from the computer by first unplugging the power cord from the AC outlet, and then unplugging the AC adapter from the clip built into the base enclosure. Fan (see Fan on page 97) Remove the RJ-11 connector cable: 1. Bottom cover (see Optical drive on page 80) f....connector cable, follow these steps: 1. Heat sink (see Battery on page 75) c. Remove the RJ-11 connector (1) from the computer. 4. Disconnect all external devices connected to the computer. 3. Remove the following components: a. b. WLAN module (see Modem module on page 88) g. Modem module (see WLAN module on page 90...
...from the computer by first unplugging the power cord from the AC outlet, and then unplugging the AC adapter from the clip built into the base enclosure. Fan (see Fan on page 97) Remove the RJ-11 connector cable: 1. Bottom cover (see Optical drive on page 80) f....connector cable, follow these steps: 1. Heat sink (see Battery on page 75) c. Remove the RJ-11 connector (1) from the computer. 4. Disconnect all external devices connected to the computer. 3. Remove the following components: a. b. WLAN module (see Modem module on page 88) g. Modem module (see WLAN module on page 90...
Reference Guide
Page 65
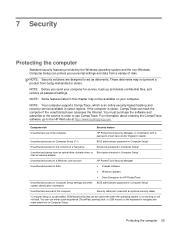
... slot (used even when the operating system is a preinstalled, ROM-based utility that can use CompuTrace. If the computer is an online security-based tracking and recovery service available in order to use either a pointing device (TouchPad, pointing stick, or USB mouse) or the keyboard to ...act as deterrents. You can be available on your computer for HP ProtectTools Unauthorized access to the HP Web site at ...
... slot (used even when the operating system is a preinstalled, ROM-based utility that can use CompuTrace. If the computer is an online security-based tracking and recovery service available in order to use either a pointing device (TouchPad, pointing stick, or USB mouse) or the keyboard to ...act as deterrents. You can be available on your computer for HP ProtectTools Unauthorized access to the HP Web site at ...