Product Manual
Page 15
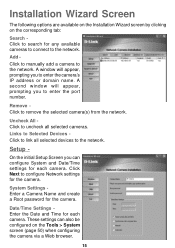
... settings can configure System and Date/Time settings for each camera. Links to Selected Devices Click to the network. Setup - Click Next to remove the selected camera(s) from the network. Remove Click to configure Network settings for the camera. System Settings Enter a Camera Name and create a Root password for the camera. A second window will appear, prompting you can also be...
... settings can configure System and Date/Time settings for each camera. Links to Selected Devices Click to the network. Setup - Click Next to remove the selected camera(s) from the network. Remove Click to configure Network settings for the camera. System Settings Enter a Camera Name and create a Root password for the camera. A second window will appear, prompting you can also be...
Product Manual
Page 22
...22 Installing IP surveillance Software The IP surveillance Software on the CD included with the DCS-5300 Internet Camera converts the DCS-5300 into a powerful, yet flexible, surveillance system for home or business, with the... following features: Real-time Monitoring Video and Audio Recording to hard disk High quality video High compression ratio Maximum of 16 cameras with different monitor layouts Smart playback Triggered event browsing Fast database searching Configurable automated alarms Account password...
...22 Installing IP surveillance Software The IP surveillance Software on the CD included with the DCS-5300 Internet Camera converts the DCS-5300 into a powerful, yet flexible, surveillance system for home or business, with the... following features: Real-time Monitoring Video and Audio Recording to hard disk High quality video High compression ratio Maximum of 16 cameras with different monitor layouts Smart playback Triggered event browsing Fast database searching Configurable automated alarms Account password...
Product Manual
Page 27
...the Admin screen. Once the Password is assigned by the Internet Camera. The Internet Camera supports multi-level password protection/access to the Internet Camera that can release a public user name and password so that when remote users access the Internet Camera they will not be restricted to... set the Administrator Password to constrain user access to the Internet Camera since the security features of the Internet Camera will have a User Name and User Password, which is defined, only the Administrator has access to the management of the Internet Camera, the Administrator has...
...the Admin screen. Once the Password is assigned by the Internet Camera. The Internet Camera supports multi-level password protection/access to the Internet Camera that can release a public user name and password so that when remote users access the Internet Camera they will not be restricted to... set the Administrator Password to constrain user access to the Internet Camera since the security features of the Internet Camera will have a User Name and User Password, which is defined, only the Administrator has access to the management of the Internet Camera, the Administrator has...
Product Manual
Page 39
General Settings IP address Subnet mask - Used to determine if the destination is lost, run Installation Wizard to find the camera's IP address. Primary DNS Secondary DNS - SMTP account name 1 - Multiple recipients must be unchecked at all times. If ...account. (The password will appear as dots instead of transmissions to destinations in the same subnet. Default router - The domain name or IP address of recipients for network identification. Invalid router settings may cause the failure of entered characters.) Recipient email address 1 - Using the DCS-5300 with an ...
General Settings IP address Subnet mask - Used to determine if the destination is lost, run Installation Wizard to find the camera's IP address. Primary DNS Secondary DNS - SMTP account name 1 - Multiple recipients must be unchecked at all times. If ...account. (The password will appear as dots instead of transmissions to destinations in the same subnet. Default router - The domain name or IP address of recipients for network identification. Invalid router settings may cause the failure of entered characters.) Recipient email address 1 - Using the DCS-5300 with an ...
Product Manual
Page 40
Using the DCS-5300 with an Internet browser (continued) Configuration > Advanced >Network (continued) SMTP(mail) server 2 - If you find that you want... external FTP server. The following user settings must conform to log into the second e-mail account. (The password will need to specify the port when connecting to send. (This address should be open for authentication purposes.)... FTP Settings Local FTP server port - 1st FTP server - 1st FTP user name 1st FTP password 1st FTP remote folder - The domain name or IP address of the external FTP server for the secondary...
Using the DCS-5300 with an Internet browser (continued) Configuration > Advanced >Network (continued) SMTP(mail) server 2 - If you find that you want... external FTP server. The following user settings must conform to log into the second e-mail account. (The password will need to specify the port when connecting to send. (This address should be open for authentication purposes.)... FTP Settings Local FTP server port - 1st FTP server - 1st FTP user name 1st FTP password 1st FTP remote folder - The domain name or IP address of the external FTP server for the secondary...
Product Manual
Page 41
... the firewall. . 41 Passive mode setting for FTP may be used if the 1st FTP is unavailable. Control channel port - If the DCS-5300 is located inside a network that the 2nd FTP server will be set to other than the default port 5001 to correspond with an Internet browser (continued) Configuration >... does not support passive mode. Granted user name on the backup FTP server. 2nd FTP password - 2nd FTP remote folder Secondary FTP passive Mode - When the administrator changes the HTTP port of the DCS-5300 (which has an IP address of 192.168.0.146) from 80 to other than the ...
... the firewall. . 41 Passive mode setting for FTP may be used if the 1st FTP is unavailable. Control channel port - If the DCS-5300 is located inside a network that the 2nd FTP server will be set to other than the default port 5001 to correspond with an Internet browser (continued) Configuration >... does not support passive mode. Granted user name on the backup FTP server. 2nd FTP password - 2nd FTP remote folder Secondary FTP passive Mode - When the administrator changes the HTTP port of the DCS-5300 (which has an IP address of 192.168.0.146) from 80 to other than the ...
Product Manual
Page 44
... password or key used to connect to configure. Enter your operating system is UPnP enabled, the device will be disabled by unselecting "Enable UPnP". The DCS-5300 is a networking architecture that provides compatibility among networking ...equipment, software, and peripherals. If you do not want to use the UPnP functionality, it can be easier to the DDNS server. UPnP Click to make changes effective 44 UPnP is short for Universal Plug and Play, which is a UPnP enabled internet camera...
... password or key used to connect to configure. Enter your operating system is UPnP enabled, the device will be disabled by unselecting "Enable UPnP". The DCS-5300 is a networking architecture that provides compatibility among networking ...equipment, software, and peripherals. If you do not want to use the UPnP functionality, it can be easier to the DDNS server. UPnP Click to make changes effective 44 UPnP is short for Universal Plug and Play, which is a UPnP enabled internet camera...
Product Manual
Page 53
... to access 4 utility screens for controlling and administering the DCS-5300. It is known. This allows multiple visitors to restrict others from controlling your camera. This password is used to access the DCS-5300 (including the Configuration) by default. This allows the ability... to identify the administrator. The DCS-5300 is the Admin screen. The options Permission for I/O...
... to access 4 utility screens for controlling and administering the DCS-5300. It is known. This allows multiple visitors to restrict others from controlling your camera. This password is used to access the DCS-5300 (including the Configuration) by default. This allows the ability... to identify the administrator. The DCS-5300 is the Admin screen. The options Permission for I/O...
Product Manual
Page 54
... log-in screen (once a password has been set). This is useful for demonstrations and keeps guests separate from observing the operation of the window within the Windows operating system. Camera Name Click System Camera name - The text will prevent anyone from users with view -only privileges. Using the DCS-5300 with an Internet browser (continued...
... log-in screen (once a password has been set). This is useful for demonstrations and keeps guests separate from observing the operation of the window within the Windows operating system. Camera Name Click System Camera name - The text will prevent anyone from users with view -only privileges. Using the DCS-5300 with an Internet browser (continued...
Product Manual
Page 64
...user name to a second external FTP server if your camera is behind a router protected by a firewall. snapshot). 6 Primary FTP passive mode- Specify the user name to Configuration > Advanced > Network in the section titled "Using the DCS-5300 With an Internet Browser" (page 38). For detailed ...information about each setting, please refer to access your backup FTP server. Record Snapshots to your backup FTP server. 2nd FTP remote folder- Specify the user password to your camera...
...user name to a second external FTP server if your camera is behind a router protected by a firewall. snapshot). 6 Primary FTP passive mode- Specify the user name to Configuration > Advanced > Network in the section titled "Using the DCS-5300 With an Internet Browser" (page 38). For detailed ...information about each setting, please refer to access your backup FTP server. Record Snapshots to your backup FTP server. 2nd FTP remote folder- Specify the user password to your camera...
Product Manual
Page 68
Click Next You must setup the administrator's password in below will prompt you to continue. Input and confirm your user name and company name and then click "Next" to proceed. Using IP surveillance Software (continued) Installing the IP surveillance software (continued) Next, the "User information" window below . Click Next 68 Enter your password in the window shown in order to continue. This window will appear. Click "Next" to enter the user name and company name.
Click Next You must setup the administrator's password in below will prompt you to continue. Input and confirm your user name and company name and then click "Next" to proceed. Using IP surveillance Software (continued) Installing the IP surveillance software (continued) Next, the "User information" window below . Click Next 68 Enter your password in the window shown in order to continue. This window will appear. Click "Next" to enter the user name and company name.
Product Manual
Page 71
... system tray signifies that allows users to use all the functions. But when users want to leave the computer, it is possible to undergo a username/password check. Below is the login window: 71 If users want to click on the icon of Launcher on the system. System Tray Icon The Launcher...
... system tray signifies that allows users to use all the functions. But when users want to leave the computer, it is possible to undergo a username/password check. Below is the login window: 71 If users want to click on the icon of Launcher on the system. System Tray Icon The Launcher...
Product Manual
Page 72
User Interface Below is the user interface for Launcher: The main user interface for ID and password will appear. The menu items are listed below: Lock Launcher When this dialog is covered in order to invoke the menu, a dialog asking for Launcher ...) When Launcher is locked, the unlock window will appear, prompting for this item is selected, Launcher will enter lock mode. The interface for the user password in the previous section. 72 The input area of the dialog will be grayed (disabled) for 60 seconds after 3 consecutive failures.
User Interface Below is the user interface for Launcher: The main user interface for ID and password will appear. The menu items are listed below: Lock Launcher When this dialog is covered in order to invoke the menu, a dialog asking for Launcher ...) When Launcher is locked, the unlock window will appear, prompting for this item is selected, Launcher will enter lock mode. The interface for the user password in the previous section. 72 The input area of the dialog will be grayed (disabled) for 60 seconds after 3 consecutive failures.
Product Manual
Page 73
.... After logging out, if the user wants to return to autorun Launcher when Window boots up. Logout Logs out user from IP surveillance. The change password is already running , clicking this option, Launcher will show a message box prompting to confirm if users really want to exit, and warn users that exiting... Launcher will re-open the Monitor window. If the Monitor program is implemented. Currently only change password dialog looks like this button will appear prompting for username and...
.... After logging out, if the user wants to return to autorun Launcher when Window boots up. Logout Logs out user from IP surveillance. The change password is already running , clicking this option, Launcher will show a message box prompting to confirm if users really want to exit, and warn users that exiting... Launcher will re-open the Monitor window. If the Monitor program is implemented. Currently only change password dialog looks like this button will appear prompting for username and...
Product Manual
Page 74
...database searching Auto alarm in multiple modes Account-password protection Multiple recording modes: Event-driven, Scheduled, and manual recording for each camera. Using IP surveillance Software (continued) Monitor Program Features of 16 cameras with different monitor layouts Smart playback Triggered ...event browsing with 3 alert windows for each camera 74 Intelligent database index modes: indexing ...
...database searching Auto alarm in multiple modes Account-password protection Multiple recording modes: Event-driven, Scheduled, and manual recording for each camera. Using IP surveillance Software (continued) Monitor Program Features of 16 cameras with different monitor layouts Smart playback Triggered ...event browsing with 3 alert windows for each camera 74 Intelligent database index modes: indexing ...
Product Manual
Page 76
Enter the password for the administrator. 76 Logging In You need to arrange the available storage size of the recorded video database. If you do not have an account, the monitor tool will display the latest alert messages received by the remote Video Server / Network Camera series product ... start the Launcher. The authentication window is shown below. You must log in as admin (administrator) to the remote Video Server/ Network Camera series product associated with the selected video channel. DI/DO control This tool receives the digital input signal and sends digital output signal ...
Enter the password for the administrator. 76 Logging In You need to arrange the available storage size of the recorded video database. If you do not have an account, the monitor tool will display the latest alert messages received by the remote Video Server / Network Camera series product ... start the Launcher. The authentication window is shown below. You must log in as admin (administrator) to the remote Video Server/ Network Camera series product associated with the selected video channel. DI/DO control This tool receives the digital input signal and sends digital output signal ...
Product Manual
Page 77
... tool system, the admin privilege has the right to access the DCS5300 Network Camera through this application software to connect the DCS-5300 in "Configuration Menu > Camera Configurations", shown in the figure below. Camera Configurations When you log in for setting each selected internet camera in the remote site only if you informed. 77 But the admin...
... tool system, the admin privilege has the right to access the DCS5300 Network Camera through this application software to connect the DCS-5300 in "Configuration Menu > Camera Configurations", shown in the figure below. Camera Configurations When you log in for setting each selected internet camera in the remote site only if you informed. 77 But the admin...
Product Manual
Page 79
... images can be inserted to the camera list. Click Ok Once added, you will be viewed from the browser window. If the connection succeeds, the camera will see the IP address of the camera. Specify the IP address, port, and admin password of the network camera, click the "Ok" button to... the selected camera. Then the system will popup, as shown below. The selected camera has been added to the selection list...
... images can be inserted to the camera list. Click Ok Once added, you will be viewed from the browser window. If the connection succeeds, the camera will see the IP address of the camera. Specify the IP address, port, and admin password of the network camera, click the "Ok" button to... the selected camera. Then the system will popup, as shown below. The selected camera has been added to the selection list...
Product Manual
Page 108
The figure below shows the login dialog. Layout Area Selection Indicator Display Area Control Area Pull Bar Area Status Area Histogram Area 108 Using IP surveillance Software (continued) Playback Program (continued) Logging In Before you start the playback program, it is necessary for you to log in to the application software. For security concerns, only the admin account can log in to this program. To change the password of the admin account, please refer to the section titled "Logging In."
The figure below shows the login dialog. Layout Area Selection Indicator Display Area Control Area Pull Bar Area Status Area Histogram Area 108 Using IP surveillance Software (continued) Playback Program (continued) Logging In Before you start the playback program, it is necessary for you to log in to the application software. For security concerns, only the admin account can log in to this program. To change the password of the admin account, please refer to the section titled "Logging In."
Product Manual
Page 120
.... The figure below shows the three elements of the pull bar and alert histogram window change the playback method selector to re-enter the admin's password again. 120 Lock Window If you are away from the newly defined start time or end time exceeds the whole database timeboundary. The scale of...
.... The figure below shows the three elements of the pull bar and alert histogram window change the playback method selector to re-enter the admin's password again. 120 Lock Window If you are away from the newly defined start time or end time exceeds the whole database timeboundary. The scale of...