WGR614v5 Reference Manual
Page 10
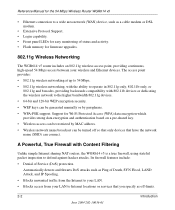
How Does WPA Compare to WEP D-9 How Does WPA Compare to IEEE 802.11i D-10 What are the Key Features of WPA Security D-10 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS D-12 WPA Data Encryption Key Management D-14 Is WPA Perfect? ...D-16 Product Support for WPA D-16 Supporting a Mixture of WPA and WEP Wireless Clients D-16 Changes to Wireless Access Points D-16 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary List of Glossary Terms G-1 Index x Contents July 2004 202-10036-01
How Does WPA Compare to WEP D-9 How Does WPA Compare to IEEE 802.11i D-10 What are the Key Features of WPA Security D-10 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS D-12 WPA Data Encryption Key Management D-14 Is WPA Perfect? ...D-16 Product Support for WPA D-16 Supporting a Mixture of WPA and WEP Wireless Clients D-16 Changes to Wireless Access Points D-16 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary List of Glossary Terms G-1 Index x Contents July 2004 202-10036-01
WGR614v5 Reference Manual
Page 16
... bandwidth 802.11g devices. • 64-bit and 128-bit WEP encryption security. • WEP keys can be generated manually or by MAC address. • Wireless network name broadcast can be restricted by passphrase. • WPA-PSK support. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Ethernet connection to a wide area network (WAN...
... bandwidth 802.11g devices. • 64-bit and 128-bit WEP encryption security. • WEP keys can be generated manually or by MAC address. • Wireless network name broadcast can be restricted by passphrase. • WPA-PSK support. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Ethernet connection to a wide area network (WAN...
WGR614v5 Reference Manual
Page 22
... Manual for the 54 Mbps Wireless Router WGR614 v5 exposes them to the picture. Set up the 54 Mbps Wireless Router WGR614 v5 2. Identify the wireless network name (SSID) and, if used, the wireless security settings. 3. and configure your wireless connection, exchanging files...wireless networking technology, see "Wireless Networking Basics" on secure Internet sites. 2-8 Introduction June 2004 202-10036-01 To learn about wireless networking security, see Appendix 4, "Wireless Configuration" for How to understand. Set up a wireless network 1. To use encryption...
... Manual for the 54 Mbps Wireless Router WGR614 v5 exposes them to the picture. Set up the 54 Mbps Wireless Router WGR614 v5 2. Identify the wireless network name (SSID) and, if used, the wireless security settings. 3. and configure your wireless connection, exchanging files...wireless networking technology, see "Wireless Networking Basics" on secure Internet sites. 2-8 Introduction June 2004 202-10036-01 To learn about wireless networking security, see Appendix 4, "Wireless Configuration" for How to understand. Set up a wireless network 1. To use encryption...
WGR614v5 Reference Manual
Page 41
... consumption of wireless adapters also vary depending on your security settings and placement. Wireless Configuration 4-1 June 2004 202-10036-01 The time it takes to establish a wireless connection can vary depending on a notebook computer. Also, WEP encryption can take slightly... area in which your wireless connection can result in significant performance degradation or inability to wirelessly connect to the router. Note: Failure to follow these guidelines can vary significantly based on wireless networking, refer to Appendix D, "Wireless Networking Basics. You should...
... consumption of wireless adapters also vary depending on your security settings and placement. Wireless Configuration 4-1 June 2004 202-10036-01 The time it takes to establish a wireless connection can vary depending on a notebook computer. Also, WEP encryption can take slightly... area in which your wireless connection can result in significant performance degradation or inability to wirelessly connect to the router. Note: Failure to follow these guidelines can vary significantly based on wireless networking, refer to Appendix D, "Wireless Networking Basics. You should...
WGR614v5 Reference Manual
Page 42
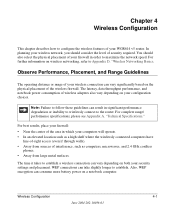
... to 300 feet. WEP Shared Key authentication and WEP data encryption will block all but the data is fully exposed. • Turn Off the Broadcast of up to access your wireless equipment. Such distances can allow for the 54 Mbps Wireless Router WGR614 v5 Implement Appropriate Wireless Security Note: Indoors, computers can be received well beyond your...
... to 300 feet. WEP Shared Key authentication and WEP data encryption will block all but the data is fully exposed. • Turn Off the Broadcast of up to access your wireless equipment. Such distances can allow for the 54 Mbps Wireless Router WGR614 v5 Implement Appropriate Wireless Security Note: Indoors, computers can be received well beyond your...
WGR614v5 Reference Manual
Page 43
.... Wi-Fi Protected Access (WPA) data encryption provides strong data security. The Wireless Settings menu will appear, as the wireless network name. You might choose to participate in this is : NETGEAR. • Region. This field identifies the... region where the WGR614 v5 can be legal to 32 alphanumeric characters. Wireless Configuration 4-3 June 2004 202-10036-01 Because this field. The SSID is more than one wireless network, different wireless network names provide a means for the 54 Mbps Wireless Router...
.... Wi-Fi Protected Access (WPA) data encryption provides strong data security. The Wireless Settings menu will appear, as the wireless network name. You might choose to participate in this is : NETGEAR. • Region. This field identifies the... region where the WGR614 v5 can be legal to 32 alphanumeric characters. Wireless Configuration 4-3 June 2004 202-10036-01 Because this field. The SSID is more than one wireless network, different wireless network names provide a means for the 54 Mbps Wireless Router...
WGR614v5 Reference Manual
Page 44
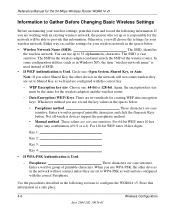
... but does not perform any authentication. • Shared Key Shared Key authentication encrypts the SSID and data. Note: Not all wireless adapter configuration utilities support WPA. Enter a word or group of printable characters in Appendix D, "Wireless Networking Basics." Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Channel. It should not be used . The "g and...
... but does not perform any authentication. • Shared Key Shared Key authentication encrypts the SSID and data. Note: Not all wireless adapter configuration utilities support WPA. Enter a word or group of printable characters in Appendix D, "Wireless Networking Basics." Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Channel. It should not be used . The "g and...
WGR614v5 Reference Manual
Page 46
... a-f). The SSID is Used. - WEP Encryption key size. Either way, record the settings for your wireless network. Enter a word or group of printable characters and click the Generate Keys button. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Information to Gather Before Changing Basic Wireless Settings Before customizing your wireless settings, print this information in a safe...
... a-f). The SSID is Used. - WEP Encryption key size. Either way, record the settings for your wireless network. Enter a word or group of printable characters and click the Generate Keys button. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Information to Gather Before Changing Basic Wireless Settings Before customizing your wireless settings, print this information in a safe...
WGR614v5 Reference Manual
Page 48
.... 4. Click Wireless Settings in the 54 Mbps Wireless Router WGR614 v5. NETGEAR is not being used . Also, the SSID of any other wireless networks within several hundred feet of up to "Disabled." 7. Select a channel that is not the same as nETgear. For initial configuration and test, leave the Wireless Card Access List set to "Everyone" and the Encryption Strength set...
.... 4. Click Wireless Settings in the 54 Mbps Wireless Router WGR614 v5. NETGEAR is not being used . Also, the SSID of any other wireless networks within several hundred feet of up to "Disabled." 7. Select a channel that is not the same as nETgear. For initial configuration and test, leave the Wireless Card Access List set to "Everyone" and the Encryption Strength set...
WGR614v5 Reference Manual
Page 49
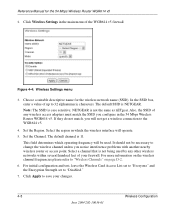
...password of your computers for the 54 Mbps Wireless Router WGR614 v5 Note: If you are able to have the same SSID and channel that they have set up. 2. If NETGEAR is case sensitive. Click Wireless Settings in the router. Configure and test your computers ...wireless router, you must then either configure your wireless adapter to the firewall, you will not work. Program the wireless adapter of password, or using whatever LAN address and password you have a wireless link and are configuring the firewall from a wired computer to Configure WEP To configure WEP data encryption...
...password of your computers for the 54 Mbps Wireless Router WGR614 v5 Note: If you are able to have the same SSID and channel that they have set up. 2. If NETGEAR is case sensitive. Click Wireless Settings in the router. Configure and test your computers ...wireless router, you must then either configure your wireless adapter to the firewall, you will not work. Program the wireless adapter of password, or using whatever LAN address and password you have a wireless link and are configuring the firewall from a wired computer to Configure WEP To configure WEP data encryption...
WGR614v5 Reference Manual
Page 50
... active. The passphrase is not the same as nETgear. Select which of the four keys will be automatically populated with key values. • Manual - Wireless Settings encryption menu 5. The four key boxes will be identical on page D-4 for the 54 Mbps Wireless Router WGR614 v5 4. Click Apply to "WEP Wireless Security" on all computers and Access Points in...
... active. The passphrase is not the same as nETgear. Select which of the four keys will be automatically populated with key values. • Manual - Wireless Settings encryption menu 5. The four key boxes will be identical on page D-4 for the 54 Mbps Wireless Router WGR614 v5 4. Click Apply to "WEP Wireless Security" on all computers and Access Points in...
WGR614v5 Reference Manual
Page 144
.... 3. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of WEP authentication: Open System and Shared Key. • Open System Authentication allows any messages that are not encrypted. The IEEE 802.11 standard defines two types of a physical connection between nodes makes the wireless links vulnerable to associate with the...
.... 3. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of WEP authentication: Open System and Shared Key. • Open System Authentication allows any messages that are not encrypted. The IEEE 802.11 standard defines two types of a physical connection between nodes makes the wireless links vulnerable to associate with the...
WGR614v5 Reference Manual
Page 146
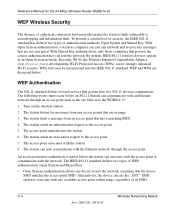
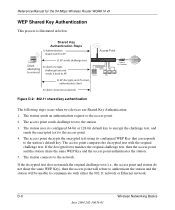
...access point. 4. The access point decrypts the encrypted text using its configured 64-bit or 128-bit default key to encrypt the challenge text, and sends the encrypted text to the station's default key. D-6 Wireless Networking Basics June 2004 202-10036-01 If ... Authentication: 1. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WEP Shared Key Authentication This process is illustrated in below. Shared Key Authentication Steps 1) Authentication request sent to AP 2) AP sends challenge text Client 3) Client encrypts attempting challenge text and to connect sends...
...access point. 4. The access point decrypts the encrypted text using its configured 64-bit or 128-bit default key to encrypt the challenge text, and sends the encrypted text to the station's default key. D-6 Wireless Networking Basics June 2004 202-10036-01 If ... Authentication: 1. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WEP Shared Key Authentication This process is illustrated in below. Shared Key Authentication Steps 1) Authentication request sent to AP 2) AP sends challenge text Client 3) Client encrypts attempting challenge text and to connect sends...
WGR614v5 Reference Manual
Page 147
... The AP and the client adapters can use WEP key 2 as the client's WEP key 3. The 64-bit WEP data encryption method, allows for the 54 Mbps Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of the United States due to generate a 64-...bit encryption key. (The 24 factory-set and not user configurable. Similar to four WEP Keys. Wireless Networking Basics D-7 June 2004 202-...
... The AP and the client adapters can use WEP key 2 as the client's WEP key 3. The 64-bit WEP data encryption method, allows for the 54 Mbps Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of the United States due to generate a 64-...bit encryption key. (The 24 factory-set and not user configurable. Similar to four WEP Keys. Wireless Networking Basics D-7 June 2004 202-...
WGR614v5 Reference Manual
Page 148
...: Some 802.11 access points also support Use WEP for Encryption: A transmitting 802.11 device encrypts the data portion of every packet it sends using a configured WEP Key. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How to Use WEP Parameters Wired Equivalent Privacy (...WEP) data encryption is used when the wireless devices are three WEP Encryption options available for 802.11 products: 1. For authentication purposes, the...
...: Some 802.11 access points also support Use WEP for Encryption: A transmitting 802.11 device encrypts the data portion of every packet it sends using a configured WEP Key. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How to Use WEP Parameters Wired Equivalent Privacy (...WEP) data encryption is used when the wireless devices are three WEP Encryption options available for 802.11 products: 1. For authentication purposes, the...
WGR614v5 Reference Manual
Page 149
...June 2004 202-10036-01 Starting August of 2003, all of 2003. NETGEAR will have to WEP? Existing Wi-Fi certified products will have agreed on a particular wireless LAN must use the same encryption key. If you don't update the WEP keys often, an unauthorized... person with sequencing rules, and a re-keying mechanism. For WPA, encryption using 802.1x and the Extensible Authentication Protocol (EAP). Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Enhanced data privacy • Robust key management • Data origin authentication ...
...June 2004 202-10036-01 Starting August of 2003, all of 2003. NETGEAR will have to WEP? Existing Wi-Fi certified products will have agreed on a particular wireless LAN must use the same encryption key. If you don't update the WEP keys often, an unauthorized... person with sequencing rules, and a re-keying mechanism. For WPA, encryption using 802.1x and the Extensible Authentication Protocol (EAP). Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Enhanced data privacy • Robust key management • Data origin authentication ...
WGR614v5 Reference Manual
Page 150
... (typically RADIUS servers). This occurs at the 802.11 level and is primarily intended for wireless infrastructure networks as AES-CCMP. Information in the WPA standard: • WPA Authentication • WPA Encryption Key Management - Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How Does WPA Compare to the network. WPA is a subset of the...
... (typically RADIUS servers). This occurs at the 802.11 level and is primarily intended for wireless infrastructure networks as AES-CCMP. Information in the WPA standard: • WPA Authentication • WPA Encryption Key Management - Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How Does WPA Compare to the network. WPA is a subset of the...
WGR614v5 Reference Manual
Page 151
... configured pass phrase on both the stations and the access point. Possible cipher suites include: WEP, TKIP, and AES (Advanced Encryption Standard). Temporal Key Integrity Protocol (TKIP) is an authentication method that integrates the authentication and data privacy functions. The supplicant in...in the Beacon frames is in the information elements to access the network. • Key management. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 The primary information conveyed in many home and small office environments will not be available nor desirable. If the...
... configured pass phrase on both the stations and the access point. Possible cipher suites include: WEP, TKIP, and AES (Advanced Encryption Standard). Temporal Key Integrity Protocol (TKIP) is an authentication method that integrates the authentication and data privacy functions. The supplicant in...in the Beacon frames is in the information elements to access the network. • Key management. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 The primary information conveyed in many home and small office environments will not be available nor desirable. If the...
WGR614v5 Reference Manual
Page 152
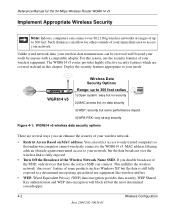
...XP implements 802.1x natively, and several Netgear switch and wireless access point products support 802.1x. D-12 June 2004 202-10036-01 Wireless Networking Basics For environments without a RADIUS ...encryption keys via 802.1x/EAP and RADIUS Wireless LAN WPA enabled wireless client with "supplicant" WPA enabled Access Point using pre-shared key or 802.1x Figure D-3: WPA Overview Wired Network with a Remote Authentication Dial-In User Service (RADIUS) infrastructure, WPA supports Extensible Authentication Protocol (EAP). Reference Manual for the 54 Mbps Wireless Router...
...XP implements 802.1x natively, and several Netgear switch and wireless access point products support 802.1x. D-12 June 2004 202-10036-01 Wireless Networking Basics For environments without a RADIUS ...encryption keys via 802.1x/EAP and RADIUS Wireless LAN WPA enabled wireless client with "supplicant" WPA enabled Access Point using pre-shared key or 802.1x Figure D-3: WPA Overview Wired Network with a Remote Authentication Dial-In User Service (RADIUS) infrastructure, WPA supports Extensible Authentication Protocol (EAP). Reference Manual for the 54 Mbps Wireless Router...
WGR614v5 Reference Manual
Page 154
..., the Temporal Key Integrity Protocol (TKIP) changes the key for every frame, and the change the global encryption key used for the 54 Mbps Wireless Router WGR614 v5 3. The client can update the EAP authentication type to such devices as token cards (Smart Cards), Kerberos, one-time passwords, certificates, and public ...
..., the Temporal Key Integrity Protocol (TKIP) changes the key for every frame, and the change the global encryption key used for the 54 Mbps Wireless Router WGR614 v5 3. The client can update the EAP authentication type to such devices as token cards (Smart Cards), Kerberos, one-time passwords, certificates, and public ...