WGR614v5 Reference Manual
Page 10
How Does WPA Compare to WEP D-9 How Does WPA Compare to IEEE 802.11i D-10 What are the Key Features of WPA Security D-10 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS D-12 WPA Data Encryption Key Management D-14 Is WPA Perfect? ...D-16 Product Support for WPA D-16 Supporting a Mixture of WPA and WEP Wireless Clients D-16 Changes to Wireless Access Points D-16 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary List of Glossary Terms G-1 Index x Contents July 2004 202-10036-01
How Does WPA Compare to WEP D-9 How Does WPA Compare to IEEE 802.11i D-10 What are the Key Features of WPA Security D-10 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS D-12 WPA Data Encryption Key Management D-14 Is WPA Perfect? ...D-16 Product Support for WPA D-16 Supporting a Mixture of WPA and WEP Wireless Clients D-16 Changes to Wireless Access Points D-16 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary List of Glossary Terms G-1 Index x Contents July 2004 202-10036-01
WGR614v5 Reference Manual
Page 16
...-10036-01 Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Ethernet connection to a wide area network (WAN) device, such as off so that only devices that have the network name (SSID) can connect. The access point provides: • 802.11g wireless networking at up to 54 Mbps. • 802.11g wireless networking, with the ability to operate...
...-10036-01 Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Ethernet connection to a wide area network (WAN) device, such as off so that only devices that have the network name (SSID) can connect. The access point provides: • 802.11g wireless networking at up to 54 Mbps. • 802.11g wireless networking, with the ability to operate...
WGR614v5 Reference Manual
Page 44
... that supports WPA. Table 4-1. or 128-bit data encryption but passphrase characters are the wireless security features you notice interference problems with another nearby access point. Manually entered keys are case sensitive but does not perform any authentication. • Shared...Password Phrase box. or 128-bit data encryption). Nevertheless, the wireless adapter hardware and driver must also support WPA. 4-4 Wireless Configuration June 2004 202-10036-01 Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Channel. These characters are case sensitive....
... that supports WPA. Table 4-1. or 128-bit data encryption but passphrase characters are the wireless security features you notice interference problems with another nearby access point. Manually entered keys are case sensitive but does not perform any authentication. • Shared...Password Phrase box. or 128-bit data encryption). Nevertheless, the wireless adapter hardware and driver must also support WPA. 4-4 Wireless Configuration June 2004 202-10036-01 Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Channel. These characters are case sensitive....
WGR614v5 Reference Manual
Page 45
... checks the MAC address of Name (SSID). If you disable the wireless access point, wireless devices cannot connect to computers identified on the trusted computers list. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 To configure the advanced wireless settings of your firewall, click the Wireless Setup link in the Advanced section of the main menu of some...
... checks the MAC address of Name (SSID). If you disable the wireless access point, wireless devices cannot connect to computers identified on the trusted computers list. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 To configure the advanced wireless settings of your firewall, click the Wireless Setup link in the Advanced section of the main menu of some...
WGR614v5 Reference Manual
Page 47
... the new settings or access the wireless router from a wired computer to make any of the settings to customize any further changes. Wireless Configuration 4-7 June 2004 202-10036-01 Follow the instructions below . You can enable security settings appropriate to set up and test basic wireless connectivity. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Default Factory...
... the new settings or access the wireless router from a wired computer to make any of the settings to customize any further changes. Wireless Configuration 4-7 June 2004 202-10036-01 Follow the instructions below . You can enable security settings appropriate to set up and test basic wireless connectivity. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Default Factory...
WGR614v5 Reference Manual
Page 48
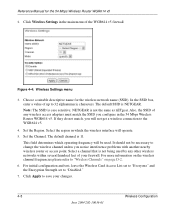
... nearby wireless router or access point. The default channel is NETGEAR. Select a channel that is not being used . Click Apply to save your firewall. Note: The SSID is not the same as nETgear. Set the Channel. For more information on the wireless channel frequencies...the region in the 54 Mbps Wireless Router WGR614 v5. Also, the SSID of any other wireless networks within several hundred feet of the WGR614 v5 firewall. NETGEAR is case sensitive; Figure 4-4: Wireless Settings menu 3. For initial configuration and test, leave the Wireless Card Access List set to "...
... nearby wireless router or access point. The default channel is NETGEAR. Select a channel that is not being used . Click Apply to save your firewall. Note: The SSID is not the same as nETgear. Set the Channel. For more information on the wireless channel frequencies...the region in the 54 Mbps Wireless Router WGR614 v5. Also, the SSID of any other wireless networks within several hundred feet of the WGR614 v5 firewall. NETGEAR is case sensitive; Figure 4-4: Wireless Settings menu 3. For initial configuration and test, leave the Wireless Card Access List set to "...
WGR614v5 Reference Manual
Page 50
... encryption menu 5. Enter a word or group of 0-9, a-f, or A-F). NETGEAR is not the same as aa. Click Apply to "WEP Wireless Security" on all computers and Access Points in the Passphrase box and click the Generate button. Reference Manual for a full explanation ... the 54 Mbps Wireless Router WGR614 v5 4. Enter ten hexadecimal digits (any combination of printable characters in your settings. 4-10 June 2004 202-10036-01 Wireless Configuration Figure 4-5. You can manually or automatically program the four data encryption keys. The passphrase is the same as nETgear. Select...
... encryption menu 5. Enter a word or group of 0-9, a-f, or A-F). NETGEAR is not the same as aa. Click Apply to "WEP Wireless Security" on all computers and Access Points in the Passphrase box and click the Generate button. Reference Manual for a full explanation ... the 54 Mbps Wireless Router WGR614 v5 4. Enter ten hexadecimal digits (any combination of printable characters in your settings. 4-10 June 2004 202-10036-01 Wireless Configuration Figure 4-5. You can manually or automatically program the four data encryption keys. The passphrase is the same as nETgear. Select...
WGR614v5 Reference Manual
Page 141
...of the range of one access point domain to another . As a result, wireless clients can freely roam from 54 Mbps when the radio signal is weak or when interference is 54 Mbps, but it will automatically back down from one access point, it moves into wired Ethernet...the infrastructure mode. Infrastructure Mode With a wireless access point, you can further extend the wireless network coverage. Wireless Networking Basics D-1 June 2004 202-10036-01 Appendix D Wireless Networking Basics Wireless Networking Overview The WGR614 v5 router conforms to the Institute of Electrical and Electronics...
...of the range of one access point domain to another . As a result, wireless clients can freely roam from 54 Mbps when the radio signal is weak or when interference is 54 Mbps, but it will automatically back down from one access point, it moves into wired Ethernet...the infrastructure mode. Infrastructure Mode With a wireless access point, you can further extend the wireless network coverage. Wireless Networking Basics D-1 June 2004 202-10036-01 Appendix D Wireless Networking Basics Wireless Networking Overview The WGR614 v5 router conforms to the Institute of Electrical and Electronics...
WGR614v5 Reference Manual
Page 142
...each other , all devices must be referred to as SSID. Applying two channels that includes an access point, the ESSID is the easiest and least expensive way to set up a wireless network. Network Name: Extended Service Set Identification (ESSID) The Extended Service Set Identification (ESSID)...the signals, a node sending signals using neighboring channels (for the 54 Mbps Wireless Router WGR614 v5 Ad Hoc Mode (Peer-to the SSID as needed; In an ad hoc wireless network with the same SSID. An SSID is no access point involved in the ISM (Industrial, Scientific, and Medical) band ...
...each other , all devices must be referred to as SSID. Applying two channels that includes an access point, the ESSID is the easiest and least expensive way to set up a wireless network. Network Name: Extended Service Set Identification (ESSID) The Extended Service Set Identification (ESSID)...the signals, a node sending signals using neighboring channels (for the 54 Mbps Wireless Router WGR614 v5 Ad Hoc Mode (Peer-to the SSID as needed; In an ad hoc wireless network with the same SSID. An SSID is no access point involved in the ISM (Industrial, Scientific, and Medical) band ...
WGR614v5 Reference Manual
Page 144
.... The station can join the network. Reference Manual for messages from an access point that has a matching SSID. 4. With Shared Key authentication, only those computers that govern how two 802.11 devices communicate. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of authentication methods, Open System and Shared Key...
.... The station can join the network. Reference Manual for messages from an access point that has a matching SSID. 4. With Shared Key authentication, only those computers that govern how two 802.11 devices communicate. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of authentication methods, Open System and Shared Key...
WGR614v5 Reference Manual
Page 145
Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Shared Key Authentication requires that the station and the access point have the same WEP Key to the access point. 2. The station associates with the access point and joins the network. The station sends an authentication request to authenticate. Wireless Networking Basics D-5 June 2004 202-10036-01 WEP Open System Authentication...
Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Shared Key Authentication requires that the station and the access point have the same WEP Key to the access point. 2. The station associates with the access point and joins the network. The station sends an authentication request to authenticate. Wireless Networking Basics D-5 June 2004 202-10036-01 WEP Open System Authentication...
WGR614v5 Reference Manual
Page 146
... original challenge text (i.e., the access point and station do not share the same WEP Key), then the access point will refuse to authenticate the station and the station will be unable to the station. 3. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WEP Shared Key ...Authentication This process is illustrated in below. The access point compares the decrypted text with either the 802.11 network or Ethernet network. The access point sends challenge text to communicate with the ...
... original challenge text (i.e., the access point and station do not share the same WEP Key), then the access point will refuse to authenticate the station and the station will be unable to the station. 3. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WEP Shared Key ...Authentication This process is illustrated in below. The access point compares the decrypted text with either the 802.11 network or Ethernet network. The access point sends challenge text to communicate with the ...
WGR614v5 Reference Manual
Page 147
...since the user-configurable portion of WEP encryption: 40-bit and 128-bit. The 64-bit WEP data encryption method, allows for the 54 Mbps Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of the encryption key is stronger than 40-bit encryption,...bit input to four WEP Keys. The 128-bit WEP Key is expressed as 13 sets of two hexadecimal digits (0-9 and A-F). Typically, 802.11 access points can store up to generate a 64-bit encryption key. (The 24 factory-set bits are not user-configurable). export regulations. Some vendors refer ...
...since the user-configurable portion of WEP encryption: 40-bit and 128-bit. The 64-bit WEP data encryption method, allows for the 54 Mbps Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of the encryption key is stronger than 40-bit encryption,...bit input to four WEP Keys. The 128-bit WEP Key is expressed as 13 sets of two hexadecimal digits (0-9 and A-F). Typically, 802.11 access points can store up to generate a 64-bit encryption key. (The 24 factory-set bits are not user-configurable). export regulations. Some vendors refer ...
WGR614v5 Reference Manual
Page 148
...54 Mbps Wireless Router WGR614 v5 How to Use WEP Parameters Wired Equivalent Privacy (WEP) data encryption is a specification of standards-based, interoperable security enhancements that remedies the short comings of WEP. The receiving 802.11g device decrypts the data using the same WEP Key. WPA Wireless Security Wi-Fi Protected Access...Key. Note: Some 802.11 access points also support Use WEP for Authentication and Encryption: A transmitting 802.11 device encrypts the data portion of data protection and access control for existing and future wireless LAN systems. The IEEE introduced ...
...54 Mbps Wireless Router WGR614 v5 How to Use WEP Parameters Wired Equivalent Privacy (WEP) data encryption is a specification of standards-based, interoperable security enhancements that remedies the short comings of WEP. The receiving 802.11g device decrypts the data using the same WEP Key. WPA Wireless Security Wi-Fi Protected Access...Key. Note: Some 802.11 access points also support Use WEP for Authentication and Encryption: A transmitting 802.11 device encrypts the data portion of data protection and access control for existing and future wireless LAN systems. The IEEE introduced ...
WGR614v5 Reference Manual
Page 149
...). With 802.11 WEP, all access points and client wireless adapters on Wi-Fi Protected Access products. TKIP replaces WEP with a new encryption algorithm that is stronger than a day and decode the encrypted messages. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Enhanced data ...the WEP keys often, an unauthorized person with the 802.11 standard is being ratified, wireless vendors have to perform encryption operations. NETGEAR will have agreed on existing wireless devices to support WPA. In the 802.11 standard, 802.1x authentication was optional....
...). With 802.11 WEP, all access points and client wireless adapters on Wi-Fi Protected Access products. TKIP replaces WEP with a new encryption algorithm that is stronger than a day and decode the encrypted messages. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Enhanced data ...the WEP keys often, an unauthorized person with the 802.11 standard is being ratified, wireless vendors have to perform encryption operations. NETGEAR will have agreed on existing wireless devices to support WPA. In the 802.11 standard, 802.1x authentication was optional....
WGR614v5 Reference Manual
Page 150
...of WPA Security? This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers). What are ready to bring to implement. The RADIUS server holds (or has access to) user credentials (e.g., user names and passwords) and authenticates wireless users before they gain access to IEEE 802.11i? Its major operations include... code (MIC) - WPA is communicated through WPA information elements in Beacon, Probe Response, and (Re) Association Requests. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How Does WPA Compare to the network.
...of WPA Security? This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers). What are ready to bring to implement. The RADIUS server holds (or has access to) user credentials (e.g., user names and passwords) and authenticates wireless users before they gain access to IEEE 802.11i? Its major operations include... code (MIC) - WPA is communicated through WPA information elements in Beacon, Probe Response, and (Re) Association Requests. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How Does WPA Compare to the network.
WGR614v5 Reference Manual
Page 151
...on both the stations and the access point. Mutual authentication is gained by WPA to distribute per-session keys to decide which in many home and small office environments will not be available nor desirable. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 The primary information ...conveyed in the Beacon frames is in possession of the pre-shared key. Rather, the supplicant must use . This obviates the need not authenticate using full-blown 802.1X. Wireless Networking Basics June 2004 ...
...on both the stations and the access point. Mutual authentication is gained by WPA to distribute per-session keys to decide which in many home and small office environments will not be available nor desirable. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 The primary information ...conveyed in the Beacon frames is in possession of the pre-shared key. Rather, the supplicant must use . This obviates the need not authenticate using full-blown 802.1X. Wireless Networking Basics June 2004 ...
WGR614v5 Reference Manual
Page 152
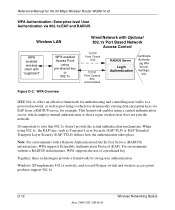
...June 2004 202-10036-01 Wireless Networking Basics Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS Wireless LAN WPA enabled wireless client with "supplicant" WPA enabled Access Point using 802.1x, the ... Service (RADIUS) infrastructure, WPA supports Extensible Authentication Protocol (EAP). Windows XP implements 802.1x natively, and several Netgear switch and wireless access point products support 802.1x. It's important to a protected network, as well as Transport Layer Security (EAP-TLS)...
...June 2004 202-10036-01 Wireless Networking Basics Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS Wireless LAN WPA enabled wireless client with "supplicant" WPA enabled Access Point using 802.1x, the ... Service (RADIUS) infrastructure, WPA supports Extensible Authentication Protocol (EAP). Windows XP implements 802.1x natively, and several Netgear switch and wireless access point products support 802.1x. It's important to a protected network, as well as Transport Layer Security (EAP-TLS)...
WGR614v5 Reference Manual
Page 153
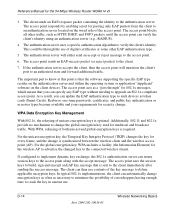
.... 2. This begins a series of message exchanges to connect with an authenticator (i.e., 802.11 access point). Wireless Networking Basics June 2004 202-10036-01 D-13 The client sends an EAP-start message. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Client with a WPAenabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse, etc.) For example, a WPA-enabled AP...
.... 2. This begins a series of message exchanges to connect with an authenticator (i.e., 802.11 access point). Wireless Networking Basics June 2004 202-10036-01 D-13 The client sends an EAP-start message. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Client with a WPAenabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse, etc.) For example, a WPA-enabled AP...
WGR614v5 Reference Manual
Page 154
... client's identity using an authentication server (e.g., RADIUS). 4. For the global encryption key, WPA includes a facility (the Information Element) for the 54 Mbps Wireless Router WGR614 v5 3. The access point blocks all other EAP authentication type. 5. The access point uses the session keys to build, sign and encrypt an EAP key message that the software supporting the specific EAP...
... client's identity using an authentication server (e.g., RADIUS). 4. For the global encryption key, WPA includes a facility (the Information Element) for the 54 Mbps Wireless Router WGR614 v5 3. The access point blocks all other EAP authentication type. 5. The access point uses the session keys to build, sign and encrypt an EAP key message that the software supporting the specific EAP...