WGR614v5 Reference Manual
Page 10
How Does WPA Compare to WEP D-9 How Does WPA Compare to IEEE 802.11i D-10 What are the Key Features of WPA Security D-10 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS D-12 WPA Data Encryption Key Management D-14 Is WPA Perfect? ...D-16 Product Support for WPA D-16 Supporting a Mixture of WPA and WEP Wireless Clients D-16 Changes to Wireless Access Points D-16 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary List of Glossary Terms G-1 Index x Contents July 2004 202-10036-01
How Does WPA Compare to WEP D-9 How Does WPA Compare to IEEE 802.11i D-10 What are the Key Features of WPA Security D-10 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS D-12 WPA Data Encryption Key Management D-14 Is WPA Perfect? ...D-16 Product Support for WPA D-16 Supporting a Mixture of WPA and WEP Wireless Clients D-16 Changes to Wireless Access Points D-16 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary List of Glossary Terms G-1 Index x Contents July 2004 202-10036-01
WGR614v5 Reference Manual
Page 16
... activity. • Flash memory for firmware upgrades. 802.11g Wireless Networking The WGR614 v5 router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your LAN to Internet locations or services that have the network name (SSID) can connect. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Ethernet connection to a wide area network...
... activity. • Flash memory for firmware upgrades. 802.11g Wireless Networking The WGR614 v5 router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your LAN to Internet locations or services that have the network name (SSID) can connect. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Ethernet connection to a wide area network...
WGR614v5 Reference Manual
Page 44
... will be necessary to "Wireless Channels" on the client. or 128-bit WEP Data Encryption, the WGR614 v5 does perform 64- Enter a word or group of these standards is required on page D-2. • Mode. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Channel.... It should not be used . These options are the wireless security features you notice interference problems with another nearby access point.
... will be necessary to "Wireless Channels" on the client. or 128-bit WEP Data Encryption, the WGR614 v5 does perform 64- Enter a word or group of these standards is required on page D-2. • Mode. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Channel.... It should not be used . These options are the wireless security features you notice interference problems with another nearby access point.
WGR614v5 Reference Manual
Page 45
... and only allows connections to the WGR614 v5. • Wireless Card Access List. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 To configure the advanced wireless settings of your firewall, click the Wireless Setup link in the Advanced section of the main menu of Name (SSID). The Wireless Settings menu will appear, as Windows XP. • Enable Wireless Access Point.
... and only allows connections to the WGR614 v5. • Wireless Card Access List. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 To configure the advanced wireless settings of your firewall, click the Wireless Setup link in the Advanced section of the main menu of Name (SSID). The Wireless Settings menu will appear, as Windows XP. • Enable Wireless Access Point.
WGR614v5 Reference Manual
Page 47
... settings to set up and test basic wireless connectivity. FEATURE Wireless Access Point Wireless Access List (MAC Filtering) SSID broadcast SSID 11b/g RF Channel Mode Authentication Type WEP DEFAULT FACTORY SETTINGS Enabled All wireless stations allowed Enabled NETGEAR 11 g and b Open System Disabled ... address and password you have established basic wireless connectivity, you can enable security settings appropriate to configure WPA settings, you will be disconnected when you click Apply. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Default Factory Settings When you ...
... settings to set up and test basic wireless connectivity. FEATURE Wireless Access Point Wireless Access List (MAC Filtering) SSID broadcast SSID 11b/g RF Channel Mode Authentication Type WEP DEFAULT FACTORY SETTINGS Enabled All wireless stations allowed Enabled NETGEAR 11 g and b Open System Disabled ... address and password you have established basic wireless connectivity, you can enable security settings appropriate to configure WPA settings, you will be disconnected when you click Apply. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Default Factory Settings When you ...
WGR614v5 Reference Manual
Page 48
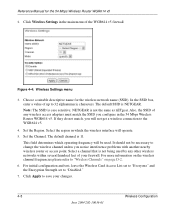
... save your firewall. Click Wireless Settings in the 54 Mbps Wireless Router WGR614 v5. NETGEAR is not being used . For more information on the wireless channel frequencies please refer to 32 alphanumeric characters. It should not be used by any wireless access adapters must match the SSID you notice interference problems with another nearby wireless router or access point. The default SSID is...
... save your firewall. Click Wireless Settings in the 54 Mbps Wireless Router WGR614 v5. NETGEAR is not being used . For more information on the wireless channel frequencies please refer to 32 alphanumeric characters. It should not be used by any wireless access adapters must match the SSID you notice interference problems with another nearby wireless router or access point. The default SSID is...
WGR614v5 Reference Manual
Page 50
... June 2004 202-10036-01 Wireless Configuration NETGEAR is case sensitive; Enter ten hexadecimal digits (any combination of 0-9, a-f, or A-F). Figure 4-5. Click Apply to "WEP Wireless Security" on all computers and Access Points in the Passphrase box and click the Generate button. These values must be identical on page D-4 for the 54 Mbps Wireless Router WGR614 v5 4. These entries are...
... June 2004 202-10036-01 Wireless Configuration NETGEAR is case sensitive; Enter ten hexadecimal digits (any combination of 0-9, a-f, or A-F). Figure 4-5. Click Apply to "WEP Wireless Security" on all computers and Access Points in the Passphrase box and click the Generate button. These values must be identical on page D-4 for the 54 Mbps Wireless Router WGR614 v5 4. These entries are...
WGR614v5 Reference Manual
Page 141
...among 802.11 devices. Infrastructure Mode With a wireless access point, you can freely roam from one access point, it will automatically back down from 54 Mbps when the radio signal is weak or when ...interference is transmitted in the infrastructure mode. Connecting multiple access points via an antenna. ad hoc and infrastructure. Wireless Networking Basics D-1 June 2004 202-10036-01 Appendix D Wireless Networking Basics Wireless Networking Overview The WGR614 v5 router...
...among 802.11 devices. Infrastructure Mode With a wireless access point, you can freely roam from one access point, it will automatically back down from 54 Mbps when the radio signal is weak or when ...interference is transmitted in the infrastructure mode. Connecting multiple access points via an antenna. ad hoc and infrastructure. Wireless Networking Basics D-1 June 2004 202-10036-01 Appendix D Wireless Networking Basics Wireless Networking Overview The WGR614 v5 router...
WGR614v5 Reference Manual
Page 142
...node sending signals using neighboring channels (for the 54 Mbps Wireless Router WGR614 v5 Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc network, computers are 5 MHz apart. thus, there is no structure or fixed points to set up a wireless network. As long as peer-to-peer ...Identification (ESSID) The Extended Service Set Identification (ESSID) is used , but may still be configured with any other . Wireless Channels IEEE 802.11g/b wireless nodes communicate with no access point involved in the various Windows operating systems. Some vendors also refer to the SSID as needed;
...node sending signals using neighboring channels (for the 54 Mbps Wireless Router WGR614 v5 Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc network, computers are 5 MHz apart. thus, there is no structure or fixed points to set up a wireless network. As long as peer-to-peer ...Identification (ESSID) The Extended Service Set Identification (ESSID) is used , but may still be configured with any other . Wireless Channels IEEE 802.11g/b wireless nodes communicate with no access point involved in the various Windows operating systems. Some vendors also refer to the SSID as needed;
WGR614v5 Reference Manual
Page 144
... authentication key can join any network and receive any available access point within range, regardless of authentication methods, Open System and Shared Key. With Shared Key authentication, only those computers that has a matching SSID. 4. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of WEP authentication: Open System and Shared...
... authentication key can join any network and receive any available access point within range, regardless of authentication methods, Open System and Shared Key. With Shared Key authentication, only those computers that has a matching SSID. 4. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of WEP authentication: Open System and Shared...
WGR614v5 Reference Manual
Page 145
Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Shared Key Authentication requires that the station and the access point have the same WEP Key to network Access Point (AP) Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA N LO CA L... authenticate. The station sends an authentication request to the access point. 2. The station associates with the access point and joins the network. Wireless Networking Basics D-5 June 2004 202-10036-01 The access point authenticates the station. 3. WEP Open System Authentication This process...
Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Shared Key Authentication requires that the station and the access point have the same WEP Key to network Access Point (AP) Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA N LO CA L... authenticate. The station sends an authentication request to the access point. 2. The station associates with the access point and joins the network. Wireless Networking Basics D-5 June 2004 202-10036-01 The access point authenticates the station. 3. WEP Open System Authentication This process...
WGR614v5 Reference Manual
Page 146
... devices use Shared Key Authentication: 1. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WEP Shared Key Authentication This process is illustrated in below. If the decrypted text matches the original challenge text, then the access point and the station share the same WEP Key and the access point authenticates the station. 5. If the decrypted text does...
... devices use Shared Key Authentication: 1. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WEP Shared Key Authentication This process is illustrated in below. If the decrypted text matches the original challenge text, then the access point and the station share the same WEP Key and the access point authenticates the station. 5. If the decrypted text does...
WGR614v5 Reference Manual
Page 147
... 128-bit encryption may not be used to transmit. Typically, 802.11 access points can only store one 128-bit key. Reference Manual for the client adapter in the same order. Therefore, make sure that your 802.11 access and client adapters configurations match. Note: The AP and the client adapters ... 1 on the AP must match WEP key 1 on the client adapter, WEP key 2 on the AP must also enter the same keys for the 54 Mbps Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of 104 user-configurable bits. The 64-bit WEP data encryption...
... 128-bit encryption may not be used to transmit. Typically, 802.11 access points can only store one 128-bit key. Reference Manual for the client adapter in the same order. Therefore, make sure that your 802.11 access and client adapters configurations match. Note: The AP and the client adapters ... 1 on the AP must match WEP key 1 on the client adapter, WEP key 2 on the AP must also enter the same keys for the 54 Mbps Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of 104 user-configurable bits. The 64-bit WEP data encryption...
WGR614v5 Reference Manual
Page 148
... WEP: The 802.11 network does not encrypt data. For authentication purposes, the 802.11g network uses Open System Authentication. 3. Note: Some 802.11 access points also support Use WEP for 802.11 products: 1. However, the WGR614 v5 does not offer this situation, the Wi-Fi Alliance announced a new security... architecture being defined in most commercially available products, 64-bit and 128-bit WEP data encryption. Use WEP for the 54 Mbps Wireless Router WGR614 v5 How to Use WEP Parameters Wired Equivalent Privacy (WEP) data encryption is designed to secure 802.11g (Wi-Fi) WLANs, but ...
... WEP: The 802.11 network does not encrypt data. For authentication purposes, the 802.11g network uses Open System Authentication. 3. Note: Some 802.11 access points also support Use WEP for 802.11 products: 1. However, the WGR614 v5 does not offer this situation, the Wi-Fi Alliance announced a new security... architecture being defined in most commercially available products, 64-bit and 128-bit WEP data encryption. Use WEP for the 54 Mbps Wireless Router WGR614 v5 How to Use WEP Parameters Wired Equivalent Privacy (WEP) data encryption is designed to secure 802.11g (Wi-Fi) WLANs, but ...
WGR614v5 Reference Manual
Page 149
... 54 Mbps Wireless Router WGR614 v5 • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is now performing interoperability certification testing on Wi-Fi Protected Access products. With 802.11 WEP, all access points and client wireless ...your network for less than the WEP algorithm, but that the keys are cumbersome to IETF's RFC 2284. NETGEAR will implement WPA on existing wireless devices to update the keys. WEP is a data encryption method and is not intended as an interoperable interim...
... 54 Mbps Wireless Router WGR614 v5 • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is now performing interoperability certification testing on Wi-Fi Protected Access products. With 802.11 WEP, all access points and client wireless ...your network for less than the WEP algorithm, but that the keys are cumbersome to IETF's RFC 2284. NETGEAR will implement WPA on existing wireless devices to update the keys. WEP is a data encryption method and is not intended as an interoperable interim...
WGR614v5 Reference Manual
Page 150
..., or AES). This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers). WPA is communicated through WPA information elements in the enterprise. Its major operations include: • Network security capability determination. D-10 June 2004 202-10036-01 Wireless Networking Basics The following security features are discussed... upgrades to market today, such as found in Beacon, Probe Response, and (Re) Association Requests. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How Does WPA Compare to the network.
..., or AES). This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers). WPA is communicated through WPA information elements in the enterprise. Its major operations include: • Network security capability determination. D-10 June 2004 202-10036-01 Wireless Networking Basics The following security features are discussed... upgrades to market today, such as found in Beacon, Probe Response, and (Re) Association Requests. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How Does WPA Compare to the network.
WGR614v5 Reference Manual
Page 151
... elements to decide which in sophisticated cryptographic and security techniques to the access point that it is in the Beacon frames is using full-blown 802.1X. For example, if the access point is the authentication method and the cipher suite. Rather, the supplicant ...a subsequent 4-way handshake between the station and Access Point (AP). • Data Privacy (Encryption). EAP over 802.1X is an authentication method that integrates the authentication and data privacy functions. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 The primary information conveyed in possession ...
... elements to decide which in sophisticated cryptographic and security techniques to the access point that it is in the Beacon frames is using full-blown 802.1X. For example, if the access point is the authentication method and the cipher suite. Rather, the supplicant ...a subsequent 4-way handshake between the station and Access Point (AP). • Data Privacy (Encryption). EAP over 802.1X is an authentication method that integrates the authentication and data privacy functions. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 The primary information conveyed in possession ...
WGR614v5 Reference Manual
Page 152
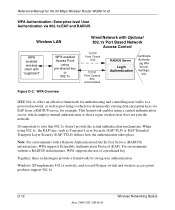
... without a RADIUS infrastructure, WPA supports the use of a preshared key. Windows XP implements 802.1x natively, and several Netgear switch and wireless access point products support 802.1x. This framework enables using a central authentication server, which employs mutual authentication so that 802.1x doesn... Tunneled Transport Layer Security (EAP-TTLS) defines how the authentication takes place. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WPA Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for example. D-12 June 2004 202-10036-...
... without a RADIUS infrastructure, WPA supports the use of a preshared key. Windows XP implements 802.1x natively, and several Netgear switch and wireless access point products support 802.1x. This framework enables using a central authentication server, which employs mutual authentication so that 802.1x doesn... Tunneled Transport Layer Security (EAP-TTLS) defines how the authentication takes place. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WPA Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for example. D-12 June 2004 202-10036-...
WGR614v5 Reference Manual
Page 153
... authenticator (i.e., 802.11 access point). The access point replies with an EAP-request identity message. Wireless Networking Basics June 2004 202-10036-01 D-13 The client sends an EAP-start message. Probe Responses (AP to station) and Association Requests (station to the stations in the service set. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Client with...
... authenticator (i.e., 802.11 access point). The access point replies with an EAP-request identity message. Wireless Networking Basics June 2004 202-10036-01 D-13 The client sends an EAP-start message. Probe Responses (AP to station) and Association Requests (station to the stations in the service set. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Client with...
WGR614v5 Reference Manual
Page 154
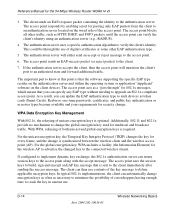
For the unicast encryption key, the Temporal Key Integrity Protocol (TKIP) changes the key for the 54 Mbps Wireless Router WGR614 v5 3. The access point uses the session keys to build, sign and encrypt an EAP key message that is sent to the ...client's identity using an authentication server (e.g., RADIUS). 4. The authentication server uses a specific authentication algorithm to the access point. 6. The access point responds by enabling a port for the wireless AP to advertise the changed key to an authorized state and forward additional traffic. WPA Data Encryption Key Management ...
For the unicast encryption key, the Temporal Key Integrity Protocol (TKIP) changes the key for the 54 Mbps Wireless Router WGR614 v5 3. The access point uses the session keys to build, sign and encrypt an EAP key message that is sent to the ...client's identity using an authentication server (e.g., RADIUS). 4. The authentication server uses a specific authentication algorithm to the access point. 6. The access point responds by enabling a port for the wireless AP to advertise the changed key to an authorized state and forward additional traffic. WPA Data Encryption Key Management ...