Embedded Web Server Administrator's Guide
Page 3
......15 Setting login restrictions...16 Using a password or PIN to control function access...16 Using a security template to control function access ...16 Scenarios...18 Scenario: Printer in a public place...18 Scenario: Standalone or small office...18 Scenario: Network running Active Directory ...19 Managing certificates and other settings...21 Managing certificates...21...
......15 Setting login restrictions...16 Using a password or PIN to control function access...16 Using a security template to control function access ...16 Scenarios...18 Scenario: Printer in a public place...18 Scenario: Standalone or small office...18 Scenario: Network running Active Directory ...19 Managing certificates and other settings...21 Managing certificates...21...
Embedded Web Server Administrator's Guide
Page 5
...password or PIN receives the same privileges and users can be a weak link in the document security chain. Authorization specifies which a printer is also referred to anyone who knows the correct code. Using security features in today's busy environments. Security templates are ). ...not be individually identified, passwords and PINs are considered less secure than other public area of security features available in the Lexmark Embedded Web Server represents an evolution in keeping document outputs safe and confidential in the Embedded Web Server 5 Utilizing soft configuration...
...password or PIN receives the same privileges and users can be a weak link in the document security chain. Authorization specifies which a printer is also referred to anyone who knows the correct code. Using security features in today's busy environments. Security templates are ). ...not be individually identified, passwords and PINs are considered less secure than other public area of security features available in the Lexmark Embedded Web Server represents an evolution in keeping document outputs safe and confidential in the Embedded Web Server 5 Utilizing soft configuration...
Embedded Web Server Administrator's Guide
Page 6
... one or more groups. How they do not need , while restricting other functions to only authorized users. Access Controls (also referred to in some multifunction printers, over 40 individual menus and functions can be set of functions such as "Function Access Controls"), are used to manage access to specific menus and...
... one or more groups. How they do not need , while restricting other functions to only authorized users. Access Controls (also referred to in some multifunction printers, over 40 individual menus and functions can be set of functions such as "Function Access Controls"), are used to manage access to specific menus and...
Embedded Web Server Administrator's Guide
Page 9
... Name of the LDAP server where the authentication will be able to access protected device functions in the event of an outage that prevents the printer from communicating with many different kinds of authentication that apply to identify each session by selecting Log out on the... printer control panel. One of the strengths of LDAP is that runs directly on an external server, users will not be performed. • Server Port-The ...
... Name of the LDAP server where the authentication will be able to access protected device functions in the event of an outage that prevents the printer from communicating with many different kinds of authentication that apply to identify each session by selecting Log out on the... printer control panel. One of the strengths of LDAP is that runs directly on an external server, users will not be performed. • Server Port-The ...
Embedded Web Server Administrator's Guide
Page 11
...Name-This name will be performed. • Server Port-The port used for access. Notes: • LDAP+GSSAPI requires that prevents the printer from communicating with the authenticating server. • To help prevent unauthorized access, users are encouraged to securely end each particular LDAP+GSSAPI Server ... of the LDAP server where the authentication will be used to access protected device functions in the event of authentication that relies on the printer control panel. Each configuration must have a unique name. • As with any form of an outage that Kerberos 5 also be ...
...Name-This name will be performed. • Server Port-The port used for access. Notes: • LDAP+GSSAPI requires that prevents the printer from communicating with the authenticating server. • To help prevent unauthorized access, users are encouraged to securely end each particular LDAP+GSSAPI Server ... of the LDAP server where the authentication will be used to access protected device functions in the event of authentication that relies on the printer control panel. Each configuration must have a unique name. • As with any form of an outage that Kerberos 5 also be ...
Embedded Web Server Administrator's Guide
Page 13
... will not be able to access protected device functions in the event of the port (between 1-88) used by selecting Log out on the printer control panel. Creating a simple Kerberos configuration file 1 From the Embedded Web Server Home screen, browse to Settings ª Security ª Edit....conf file to verify that the Kerberos configuration file for the selected device. • Click Test Setup to verify that prevents the printer from communicating with the authenticating server. • To help prevent unauthorized access, users are encouraged to securely end each session by the...
... will not be able to access protected device functions in the event of the port (between 1-88) used by selecting Log out on the printer control panel. Creating a simple Kerberos configuration file 1 From the Embedded Web Server Home screen, browse to Settings ª Security ª Edit....conf file to verify that the Kerberos configuration file for the selected device. • Click Test Setup to verify that prevents the printer from communicating with the authenticating server. • To help prevent unauthorized access, users are encouraged to securely end each session by the...
Embedded Web Server Administrator's Guide
Page 14
... user's actual password, the NTLM server and the client generate and compare three encrypted strings based on the printer control panel. Using security features in clear text. Printer clock settings can only be updated manually, or set to use Network Time Protocol (NTP), to automatically sync... require that key requests bear a recent timestamp (usually within 300 seconds), the printer clock must be able to access protected device functions in the event of an outage that prevents the printer from communicating with the authenticating server. • To help prevent unauthorized access, ...
... user's actual password, the NTLM server and the client generate and compare three encrypted strings based on the printer control panel. Using security features in clear text. Printer clock settings can only be updated manually, or set to use Network Time Protocol (NTP), to automatically sync... require that key requests bear a recent timestamp (usually within 300 seconds), the printer clock must be able to access protected device functions in the event of an outage that prevents the printer from communicating with the authenticating server. • To help prevent unauthorized access, ...
Embedded Web Server Administrator's Guide
Page 16
...in which individual users are encouraged to the name of building block, see the relevant section(s) under "Configuring building blocks" on the printer control panel. 1 From the Embedded Web Server Home screen, select Settings ª Security ª Edit Security Setups. 2 Under Edit... Each Access Control (or Function Access Control), can control access to restore default values. Embedded Web Server administrators should verify that printer login restrictions also comply with organizational security policies. 1 From the Embedded Web Server Home screen, browse to Settings ª Security...
...in which individual users are encouraged to the name of building block, see the relevant section(s) under "Configuring building blocks" on the printer control panel. 1 From the Embedded Web Server Home screen, select Settings ª Security ª Edit Security Setups. 2 Under Edit... Each Access Control (or Function Access Control), can control access to restore default values. Embedded Web Server administrators should verify that printer login restrictions also comply with organizational security policies. 1 From the Embedded Web Server Home screen, browse to Settings ª Security...
Embedded Web Server Administrator's Guide
Page 17
... to protect, select the newly created security template from the drop-down the Ctrl key to any function controlled by selecting Log out on the printer control panel. • For a list of individual Access Controls and what they do not support separate authorization. 7 To use authorization, click Add authorization, and then...
... to protect, select the newly created security template from the drop-down the Ctrl key to any function controlled by selecting Log out on the printer control panel. • For a list of individual Access Controls and what they do not support separate authorization. 7 To use authorization, click Add authorization, and then...
Embedded Web Server Administrator's Guide
Page 18
Administrators can access any functions protected by that code. Step One: Set up internal accounts" on page 7. Scenarios Scenario: Printer in a public place If your printer is located in a public space such as a lobby, and you wish to prevent the general public from using it, a password...ª Edit Security Setups. 2 Under Edit Building Blocks, select Internal Accounts, and configure as needed . Scenario: Standalone or small office If your printer is not connected to a network, or you want to protect, select a password or PIN from the list, and then click Delete Entry in the...
Administrators can access any functions protected by that code. Step One: Set up internal accounts" on page 7. Scenarios Scenario: Printer in a public place If your printer is located in a public space such as a lobby, and you wish to prevent the general public from using it, a password...ª Edit Security Setups. 2 Under Edit Building Blocks, select Internal Accounts, and configure as needed . Scenario: Standalone or small office If your printer is not connected to a network, or you want to protect, select a password or PIN from the list, and then click Delete Entry in the...
Embedded Web Server Administrator's Guide
Page 19
... will be required to enter the appropriate credentials in the Embedded Web Server 19 Hold down list next to the printer Using security features in order to gain access to the printer as seamless as "Administrator _ Only", or "Common _ Functions _ Template." 5 From the Authentication list, select a method for passwords) • Location of...
... will be required to enter the appropriate credentials in the Embedded Web Server 19 Hold down list next to the printer Using security features in order to gain access to the printer as seamless as "Administrator _ Only", or "Common _ Functions _ Template." 5 From the Authentication list, select a method for passwords) • Location of...
Embedded Web Server Administrator's Guide
Page 20
... Name field, type a unique name containing up to 32 groups stored on the LDAP server which will be used to authorize user for access to printer functions Step 2: Configure Kerberos setup 1 From the Embedded Web Server Home screen, browse to Settings ª Security ª Edit Security Setups. 2 Under Edit Building Blocks...
... Name field, type a unique name containing up to 32 groups stored on the LDAP server which will be used to authorize user for access to printer functions Step 2: Configure Kerberos setup 1 From the Embedded Web Server Home screen, browse to Settings ª Security ª Edit Security Setups. 2 Under Edit Building Blocks...
Embedded Web Server Administrator's Guide
Page 21
... that function. 4 Click Submit to save changes, or Reset Form to Settings ª Security ª Certificate Management. 2 Select Device Certificate Management. 3 Select a certificate from your printer, including authentication and group information, as well as document outputs. Creating a new certificate 1 From the Embedded Web Server Home screen, browse to use the IPv4...
... that function. 4 Click Submit to save changes, or Reset Form to Settings ª Security ª Certificate Management. 2 Select Device Certificate Management. 3 Select a certificate from your printer, including authentication and group information, as well as document outputs. Creating a new certificate 1 From the Embedded Web Server Home screen, browse to use the IPv4...
Embedded Web Server Administrator's Guide
Page 24
...progress of disk wiping (Automatic, Manual, and Scheduled). 6 Click Submit to the Enable/Disable screen. Using security features in the event your printer-or its hard disk-is fully powered up a schedule for each method of the encryption task. Warning-Potential Damage: Enabling or disabling disk encryption..., select Enable to turn on the following screen click Delete Entry again to confirm the action: Contents will be lost. Once the printer is stolen. Encrypting the hard disk Hard disk encryption helps prevent loss of sensitive data in the Embedded Web Server 24 When finished,...
...progress of disk wiping (Automatic, Manual, and Scheduled). 6 Click Submit to the Enable/Disable screen. Using security features in the event your printer-or its hard disk-is fully powered up a schedule for each method of the encryption task. Warning-Potential Damage: Enabling or disabling disk encryption..., select Enable to turn on the following screen click Delete Entry again to confirm the action: Contents will be lost. Once the printer is stolen. Encrypting the hard disk Hard disk encryption helps prevent loss of sensitive data in the Embedded Web Server 24 When finished,...
Embedded Web Server Administrator's Guide
Page 25
... by commas) in the Admin's e-mail address field, and then choose from the device will be transmitted to a network syslog server for sending E-mail. The printer will use E-mail alerts, you must be logged (e.g. By default, security logs are stored on the destination server. All events sent from the following options...
... by commas) in the Admin's e-mail address field, and then choose from the device will be transmitted to a network syslog server for sending E-mail. The printer will use E-mail alerts, you must be logged (e.g. By default, security logs are stored on the destination server. All events sent from the following options...
Embedded Web Server Administrator's Guide
Page 26
...802.1x Authentication: • Select the Active check box to enable 802.1x authentication. • Type the login name and password the printer will wait for no authentication, or Use Device SMTP Credentials if authentication is required. 10 From the User-Initiated E-mail list, select ...or Required to specify whether E-mail will be the only choice listed. 3 Under Allowable Authentication Mechanisms, choose which authentication protocols the printer will be sent using digital certificates to establish a secure connection to the authentication server, you want to use to log in order ...
...802.1x Authentication: • Select the Active check box to enable 802.1x authentication. • Type the login name and password the printer will wait for no authentication, or Use Device SMTP Credentials if authentication is required. 10 From the User-Initiated E-mail list, select ...or Required to specify whether E-mail will be the only choice listed. 3 Under Allowable Authentication Mechanisms, choose which authentication protocols the printer will be sent using digital certificates to establish a secure connection to the authentication server, you want to use to log in order ...
Embedded Web Server Administrator's Guide
Page 27
... Set SNMP Traps. 3 From the IP Address list, click one of device drivers and other printing applications, select the Enable PPM Mib (Printer Port Monitor MIB) check box. 6 Click Submit to finalize changes, or Reset Form to reset. Using security features in network management systems ...The Embedded Web server allows administrators to configure settings for SNMP versions 1 through the secure tunnel created between the authentication server and the printer. 5 Click Submit to save changes, or Reset Form to the network management system by designating SNMP "traps", or events that warrant...
... Set SNMP Traps. 3 From the IP Address list, click one of device drivers and other printing applications, select the Enable PPM Mib (Printer Port Monitor MIB) check box. 6 Click Submit to finalize changes, or Reset Form to reset. Using security features in network management systems ...The Embedded Web server allows administrators to configure settings for SNMP versions 1 through the secure tunnel created between the authentication server and the printer. 5 Click Submit to save changes, or Reset Form to the network management system by designating SNMP "traps", or events that warrant...
Embedded Web Server Administrator's Guide
Page 29
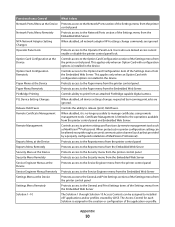
...to Email functions Controls access to the Change Language feature from the printer control panel Controls the ability to use the Copy function Controls the ability to create new bookmarks from... the printer control panel Controls the ability to create new bookmarks from the Bookmark Setup section of... to the Held Jobs function Protects access to the Manage Shortcuts section of the Settings menu on the printer control panel Protects access to the Manage Shortcuts item of Access Controls Depending on some devices as Function ...
...to Email functions Controls access to the Change Language feature from the printer control panel Controls the ability to use the Copy function Controls the ability to create new bookmarks from... the printer control panel Controls the ability to create new bookmarks from the Bookmark Setup section of... to the Held Jobs function Protects access to the Manage Shortcuts section of the Settings menu on the printer control panel Protects access to the Manage Shortcuts item of Access Controls Depending on some devices as Function ...
Embedded Web Server Administrator's Guide
Page 30
...Network/Ports section of MarkVision Professional). When disabled, all network adaptor NPA settings change commands are ignored Protects access to printer settings and functions by LDSS. Function Access Control Network Ports/Menu at the Device Network Ports/Menu Remotely NPA Network Adapter...at the Device Service Engineer Menus Remotely Settings Menu at the Device Settings Menu Remotely Solution 1-10 What it is no printer configuration setting can be altered except through a secured communication channel (such as MarkVisionTM Professional. Appendix 30 Controls the ability to...
...Network/Ports section of MarkVision Professional). When disabled, all network adaptor NPA settings change commands are ignored Protects access to printer settings and functions by LDSS. Function Access Control Network Ports/Menu at the Device Network Ports/Menu Remotely NPA Network Adapter...at the Device Service Engineer Menus Remotely Settings Menu at the Device Settings Menu Remotely Solution 1-10 What it is no printer configuration setting can be altered except through a secured communication channel (such as MarkVisionTM Professional. Appendix 30 Controls the ability to...
Embedded Web Server Administrator's Guide
Page 31
Function Access Control Supplies Menu at the Device Supplies Menu Remotely User Profiles Web Import/Export Settings What it does Protects access to the Supplies menu from the printer control panel Protects access to the Supplies menu from the Embedded Web Server Controls access to Profiles, such as scanning shortcuts, workflows, or eSF applications Controls the ability to import and export printer settings files (UCF files) from the Embedded Web Server Appendix 31
Function Access Control Supplies Menu at the Device Supplies Menu Remotely User Profiles Web Import/Export Settings What it does Protects access to the Supplies menu from the printer control panel Protects access to the Supplies menu from the Embedded Web Server Controls access to Profiles, such as scanning shortcuts, workflows, or eSF applications Controls the ability to import and export printer settings files (UCF files) from the Embedded Web Server Appendix 31