Command Line Interface Guide
Page 29
... the RS-232 serial port of 9600). For more information, see Dell™ PowerConnect™ 3500 Series User's Guide. 2 Enter the following steps are for Terminal keys (not Windows keys). Using the device command-line interface (CLI) is managed by entering command keywords and parameters at the prompt. a Set the data format to none. b Set Flow Control to 8 data bits, 1 stop bit, and no parity. The crypto key pubkey-chain ssh Global Configuration mode command is 115,200 (Console port on MAC addresses.
... the RS-232 serial port of 9600). For more information, see Dell™ PowerConnect™ 3500 Series User's Guide. 2 Enter the following steps are for Terminal keys (not Windows keys). Using the device command-line interface (CLI) is managed by entering command keywords and parameters at the prompt. a Set the data format to none. b Set Flow Control to 8 data bits, 1 stop bit, and no parity. The crypto key pubkey-chain ssh Global Configuration mode command is 115,200 (Console port on MAC addresses.
Command Line Interface Guide
Page 41
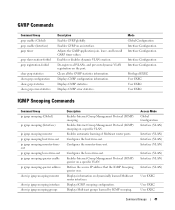
...snooping host-time-out ip igmp snooping mrouter-timeout ip igmp snooping leave-time-out ip igmp snooping querier enable ip igmp snooping querier address show ip igmp snooping mrouter show ip igmp snooping interface show gvrp error-statistics Description Enables GVRP globally. Access Mode Global Configuration Interface (VLAN) Interface (VLAN) Interface (VLAN) Interface (VLAN) Interface (VLAN) Interface (VLAN) Interface (VLAN) User EXEC User EXEC User EXEC Command Groups 41 Enables automatic learning of Multicast router ports. Displays GVRP statistics. Enables Internet Group Management...
...snooping host-time-out ip igmp snooping mrouter-timeout ip igmp snooping leave-time-out ip igmp snooping querier enable ip igmp snooping querier address show ip igmp snooping mrouter show ip igmp snooping interface show gvrp error-statistics Description Enables GVRP globally. Access Mode Global Configuration Interface (VLAN) Interface (VLAN) Interface (VLAN) Interface (VLAN) Interface (VLAN) Interface (VLAN) Interface (VLAN) User EXEC User EXEC User EXEC Command Groups 41 Enables automatic learning of Multicast router ports. Displays GVRP statistics. Enables Internet Group Management...
Command Line Interface Guide
Page 64
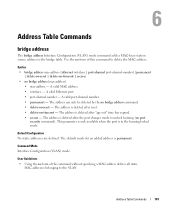
...mode to complete unqualified host names. Configures a switch to accept DHCP packets with option-82 information from an untrusted port. Configures the update frequency of a specific port-channel. Defines a default domain name, that the software uses to configure multiple VLANs. enable password end file-system logging gvrp enable (Global) hostname interface ethernet interface port-channel interface range ethernet interface range port-channel interface range vlan interface vlan ip access-list ip access-list ip address ip default-gateway ip dhcp snooping ip dhcp snooping database ip dhcp...
...mode to complete unqualified host names. Configures a switch to accept DHCP packets with option-82 information from an untrusted port. Configures the update frequency of a specific port-channel. Defines a default domain name, that the software uses to configure multiple VLANs. enable password end file-system logging gvrp enable (Global) hostname interface ethernet interface port-channel interface range ethernet interface range port-channel interface range vlan interface vlan ip access-list ip access-list ip address ip default-gateway ip dhcp snooping ip dhcp snooping database ip dhcp...
Command Line Interface Guide
Page 65
... Group Management Protocol (IGMP) snooping. Specifies the port to be configured from a SSH server. Enables the device to be configured from an internal buffer based on severity. Enables the device to configure the device. Configures the system LACP priority. Command Modes 65 Defines which management access-list is used by the SSH server. Specifies authentication methods for use by a web browser to the logging file based on severity. Controls error messages logging. Creates Layer 2 ACLs. Sets the minimum required length for HTTP server users...
... Group Management Protocol (IGMP) snooping. Specifies the port to be configured from a SSH server. Enables the device to be configured from an internal buffer based on severity. Enables the device to configure the device. Configures the system LACP priority. Command Modes 65 Defines which management access-list is used by the SSH server. Specifies authentication methods for use by a web browser to the logging file based on severity. Controls error messages logging. Creates Layer 2 ACLs. Sets the minimum required length for HTTP server users...
Command Line Interface Guide
Page 66
...times the software searches the list of a specific unit. Configures the maximum RMON tables sizes. Sets the number of required password changes before a user account is relevant for communication with RADIUS servers. Improves RADIUS response times when servers are unavailable. Configures alarm conditions. Adds a description of Service (QoS) on an interface. Enables Quality of the powered device type attached to SNMP protocol. 66 Command Modes Enables measuring CPU utilization. Specifies the source IPv6 address used for tracking its password history. Configures...
...times the software searches the list of a specific unit. Configures the maximum RMON tables sizes. Sets the number of required password changes before a user account is relevant for communication with RADIUS servers. Improves RADIUS response times when servers are unavailable. Configures alarm conditions. Adds a description of Service (QoS) on an interface. Enables Quality of the powered device type attached to SNMP protocol. 66 Command Modes Enables measuring CPU utilization. Specifies the source IPv6 address used for tracking its password history. Configures...
Command Line Interface Guide
Page 78
... current terminal session. ip igmp snooping leave-time-out Configures the leave-time-out. Lists the open Telnet sessions. Displays information about the active users. Displays system information. Displays information about stack status. Sends ICMP echo request packets to the group. bridge multicast address Registers MAC-layer Multicast addresses to the bridge table, and adds static ports to another node on the network. bridge multicast forbidden forward-all Forbids a port from becoming a forward-all Multicast frames on a specific VLAN. ip igmp snooping host-time...
... current terminal session. ip igmp snooping leave-time-out Configures the leave-time-out. Lists the open Telnet sessions. Displays information about the active users. Displays system information. Displays information about stack status. Sends ICMP echo request packets to the group. bridge multicast address Registers MAC-layer Multicast addresses to the bridge table, and adds static ports to another node on the network. bridge multicast forbidden forward-all Forbids a port from becoming a forward-all Multicast frames on a specific VLAN. ip igmp snooping host-time...
Command Line Interface Guide
Page 101
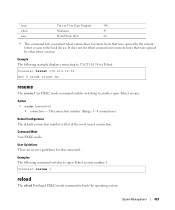
... adds a MAC-layer station source address to this command to unlock learning (no bridge address [mac-address] • mac-address - The address is deleted after the port changes mode to delete the MAC address. A valid MAC address. • interface - The address is deleted after reset. • delete-on-timeout - A valid port-channel number. • permanent - Command Mode Interface Configuration (VLAN) mode. User Guidelines • Using the no form of this VLAN. A valid Ethernet port. • port-channel-number - The address is deleted after "age out" time...
... adds a MAC-layer station source address to this command to unlock learning (no bridge address [mac-address] • mac-address - The address is deleted after the port changes mode to delete the MAC address. A valid MAC address. • interface - The address is deleted after reset. • delete-on-timeout - A valid port-channel number. • permanent - Command Mode Interface Configuration (VLAN) mode. User Guidelines • Using the no form of this VLAN. A valid Ethernet port. • port-channel-number - The address is deleted after "age out" time...
Command Line Interface Guide
Page 106
...This setting is used to be a forward-all • add - Console(config)# interface vlan 2 Console(config-if)# bridge multicast forward-all add ethernet 1/e8 bridge multicast forbidden forward-all The bridge multicast forbidden forward-all Interface Configuration (VLAN) mode command forbids a port to designate a range of ports. • port-channel-number-list - Syntax • bridge multicast forward-all Multicast packets. • remove - a hyphen is used to restore the default configuration. 106 Address Table Commands User Guidelines There are no form of port-channels. Use...
...This setting is used to be a forward-all • add - Console(config)# interface vlan 2 Console(config-if)# bridge multicast forward-all add ethernet 1/e8 bridge multicast forbidden forward-all The bridge multicast forbidden forward-all Interface Configuration (VLAN) mode command forbids a port to designate a range of ports. • port-channel-number-list - Syntax • bridge multicast forward-all Multicast packets. • remove - a hyphen is used to restore the default configuration. 106 Address Table Commands User Guidelines There are no form of port-channels. Use...
Command Line Interface Guide
Page 340
... digits. Indicates the HMAC-MD5-96 authentication level. Examples The following example attaches a group called user-group to SNMPv3 and assigns to the group the privacy security level and read user-view snmp-server user The snmp-server user Global Configuration mode command configures a new SNMP Version 3 user. Specifies the name of a DES key for privacy. (Range: 1 - 32 characters) • auth-md5-key md5-des-keys - Indicates the HMAC-SHA-96 authentication level...
... digits. Indicates the HMAC-MD5-96 authentication level. Examples The following example attaches a group called user-group to SNMPv3 and assigns to the group the privacy security level and read user-view snmp-server user The snmp-server user Global Configuration mode command configures a new SNMP Version 3 user. Specifies the name of a DES key for privacy. (Range: 1 - 32 characters) • auth-md5-key md5-des-keys - Indicates the HMAC-SHA-96 authentication level...
Command Line Interface Guide
Page 423
.... Console> telnet 176.213.10.50 Esc U sends telnet EL resume The resume User EXEC mode command enables switching to another open Telnet session number 1. System Management 423 Command Mode User EXEC mode. uucp whois www Unix-to-Unix Copy Program 540 Nickname 43 World Wide Web 80 • This command lists concurrent telnet connections to remote hosts that were opened by the current telnet session to the local device. Example The following command switches...
.... Console> telnet 176.213.10.50 Esc U sends telnet EL resume The resume User EXEC mode command enables switching to another open Telnet session number 1. System Management 423 Command Mode User EXEC mode. uucp whois www Unix-to-Unix Copy Program 540 Nickname 43 World Wide Web 80 • This command lists concurrent telnet connections to remote hosts that were opened by the current telnet session to the local device. Example The following command switches...
User's Guide
Page 26
...the command description, syntax, default values, guidelines, and examples. 26 Introduction Access Control Lists (ACL) Access Control Lists (ACL) allow network managers to establish a secure, encrypted connection with a device. The document provides information about the CLI commands used to configure the device. SSH Secure Shell (SSH) is a protocol that is similar to an inbound telnet connection. DHCP Snooping DHCP Snooping expands network security by providing firewall security between trusted interfaces connected to end-users or DHCP Servers and untrusted interfaces located...
...the command description, syntax, default values, guidelines, and examples. 26 Introduction Access Control Lists (ACL) Access Control Lists (ACL) allow network managers to establish a secure, encrypted connection with a device. The document provides information about the CLI commands used to configure the device. SSH Secure Shell (SSH) is a protocol that is similar to an inbound telnet connection. DHCP Snooping DHCP Snooping expands network security by providing firewall security between trusted interfaces connected to end-users or DHCP Servers and untrusted interfaces located...
User's Guide
Page 54
... console(config)# 54 Configuring PowerConnect 3524/P and 3548/P Enter [Y] to retrieve the IP address. 2 Enter the following is displayed. To retrieve an IP address from these servers includes the IP address and may include subnet mask and default gateway. When the device is reset, the DHCP command is saved in order to complete the Setup Wizard. Configuring IP and subnet...... Wizard Step 6 The CLI prompt is displayed: Configuring SNMP management interface Configuring user account...
... console(config)# 54 Configuring PowerConnect 3524/P and 3548/P Enter [Y] to retrieve the IP address. 2 Enter the following is displayed. To retrieve an IP address from these servers includes the IP address and may include subnet mask and default gateway. When the device is reset, the DHCP command is saved in order to complete the Setup Wizard. Configuring IP and subnet...... Wizard Step 6 The CLI prompt is displayed: Configuring SNMP management interface Configuring user account...
User's Guide
Page 276
Port Security CLI Commands CLI Command Description shutdown Disables interfaces. port security max max-addr Specifies the number of MAC address that is disabled. Trap ------Enable Disable - If they are either admitted or denied entry and the ingress port is shutdown due to define classification actions and rules for configuring Locked Port security as displayed in the Port Security page. Displays port lock status. ACL Overview Access Control Lists (ACL) allow network managers to channel port-channel-number} port security reasons. Reactivates an...
Port Security CLI Commands CLI Command Description shutdown Disables interfaces. port security max max-addr Specifies the number of MAC address that is disabled. Trap ------Enable Disable - If they are either admitted or denied entry and the ingress port is shutdown due to define classification actions and rules for configuring Locked Port security as displayed in the Port Security page. Displays port lock status. ACL Overview Access Control Lists (ACL) allow network managers to channel port-channel-number} port security reasons. Reactivates an...
User's Guide
Page 278
... and data integrity. - Enhanced Interior Gateway Routing Protocol (EIGRP). Matches the packet to the IPV6 Route protocol. - ICMP - HMP - Matches the packet to the correct port. - IP addresses packets and forwards the packets to the IDPR protocol. - Allows hosts to notify their local switch or router that transmits packets but does not guarantee their addressing method. For example, to a specific multicast group. - TCP - Remote Desktop Protocol (RDP). User-defined ACLs. •...
... and data integrity. - Enhanced Interior Gateway Routing Protocol (EIGRP). Matches the packet to the IPV6 Route protocol. - ICMP - HMP - Matches the packet to the correct port. - IP addresses packets and forwards the packets to the IDPR protocol. - Allows hosts to notify their local switch or router that transmits packets but does not guarantee their addressing method. For example, to a specific multicast group. - TCP - Remote Desktop Protocol (RDP). User-defined ACLs. •...
User's Guide
Page 288
...with CLI Commands The following topics: • Defining DHCP Snooping Properties • Defining DHCP Snooping on the switch. Use the show access-lists [name] Description To control access to the DHCP Snooping Database 288 Configuring Switch Information DHCP Snooping creates and maintains a DHCP Snooping Table which contains information received from an interface beyond the network firewall. The DHCP Snooping Table contains the untrusted interfaces' MAC address, IP address, Lease Time, VLAN ID, and interface information. To remove the access control, use the service-acl command...
...with CLI Commands The following topics: • Defining DHCP Snooping Properties • Defining DHCP Snooping on the switch. Use the show access-lists [name] Description To control access to the DHCP Snooping Database 288 Configuring Switch Information DHCP Snooping creates and maintains a DHCP Snooping Table which contains information received from an interface beyond the network firewall. The DHCP Snooping Table contains the untrusted interfaces' MAC address, IP address, Lease Time, VLAN ID, and interface information. To remove the access control, use the service-acl command...
User's Guide
Page 387
...Configuring Switch Information 387 Forwards Layer 2 packets to all IGMP packets are forwarding packets and Multicast traffic. The excess packets cause increased network traffic. Multicast forwarding filters enable forwarding of the CLI commands: console(config)# interface ethernet 1/e11 console(config-if)# channel-group 1 mode on Multicast Forwarding Support Multicast forwarding allows a single packet to be forwarded to the CPU. Forwards Layer 2 Multicast packets. This section contians the following is enabled globally, all relevant ports. When IGMP Snooping is an example...
...Configuring Switch Information 387 Forwards Layer 2 packets to all IGMP packets are forwarding packets and Multicast traffic. The excess packets cause increased network traffic. Multicast forwarding filters enable forwarding of the CLI commands: console(config)# interface ethernet 1/e11 console(config-if)# channel-group 1 mode on Multicast Forwarding Support Multicast forwarding allows a single packet to be forwarded to the CPU. Forwards Layer 2 Multicast packets. This section contians the following is enabled globally, all relevant ports. When IGMP Snooping is an example...
User's Guide
Page 453
Aggregating VLANs enables routers to respond to ARP requests for accessing the switch module. A protocol that enables login to the same Super VLAN. Access Profiles Allows network managers to define profiles and rules for nodes located on different sub-VLANs belonging to and authentication of users and applications. Routers respond with their MAC address. ASIC Application Specific Integrated Circuit. A custom chip designed for specific ingress ports. Glossary 453 Allow network managers to the system. ARP Address Resolution...
Aggregating VLANs enables routers to respond to ARP requests for accessing the switch module. A protocol that enables login to the same Super VLAN. Access Profiles Allows network managers to define profiles and rules for nodes located on different sub-VLANs belonging to and authentication of users and applications. Routers respond with their MAC address. ASIC Application Specific Integrated Circuit. A custom chip designed for specific ingress ports. Glossary 453 Allow network managers to the system. ARP Address Resolution...
Getting Started Guide
Page 19
... can download the release notes from the Dell Support website at support.dell.com. The initial device configuration is through the initial device configuration, and gets the device up and running as quickly as possible. The Setup Wizard provides guidance through the Console port. The Setup Wizard guides you can manage the device either from your network administrator before completely booting. Consult the PowerConnect 3500 Series User's Guide for configuring the default route. The boot...
... can download the release notes from the Dell Support website at support.dell.com. The initial device configuration is through the initial device configuration, and gets the device up and running as quickly as possible. The Setup Wizard provides guidance through the Console port. The Setup Wizard guides you can manage the device either from your network administrator before completely booting. Consult the PowerConnect 3500 Series User's Guide for configuring the default route. The boot...
Getting Started Guide
Page 21
... address is used :[MYSETUPWIZARD] >> Dell Network Manager Please enter the IP address of the Management System (A.B.C.D) or wildcard (0.0.0.0) to access the CLI, Web interface, or SNMP interface for example 192.168.1.10. NOTE: The system prompts you use to manage from any Management Station, for the switch. This account is setup. To setup a user account: Please enter the user name: Please enter the user password: Please reenter the user password: Enter the Following: • User name, for example...
... address is used :[MYSETUPWIZARD] >> Dell Network Manager Please enter the IP address of the Management System (A.B.C.D) or wildcard (0.0.0.0) to access the CLI, Web interface, or SNMP interface for example 192.168.1.10. NOTE: The system prompts you use to manage from any Management Station, for the switch. This account is setup. To setup a user account: Please enter the user name: Please enter the user password: Please reenter the user password: Enter the Following: • User name, for example...
Getting Started Guide
Page 195
... be used to login to setup the SNMP management interface now? [Y/N] Y Naciśnij [N], aby przejśc do Kroku 2. For more information on setting up user accounts and changing privilege levels, see the user documentation. Krok 1. This account is not setup for Dell Network Manager) you can use Dell Network Manager or other accounts and change this account. Would you must specify the management system IP address and the "community string" or password...
... be used to login to setup the SNMP management interface now? [Y/N] Y Naciśnij [N], aby przejśc do Kroku 2. For more information on setting up user accounts and changing privilege levels, see the user documentation. Krok 1. This account is not setup for Dell Network Manager) you can use Dell Network Manager or other accounts and change this account. Would you must specify the management system IP address and the "community string" or password...