Operating Instructions
Page 3
... Reader/Adobe Reader must be html manuals. It also explains the control panel, preparation procedures for administrators of the machine. Important ❒ Media differ according to install the CD-ROMs provided. ❖ General Settings Guide Explains User Tools settings, and Address Book procedures... such as PDF files. ❒ Depending on how to replace paper, toner, staples, and other consumables. ❖ Security Reference This manual is for using the machine. It explains...
... Reader/Adobe Reader must be html manuals. It also explains the control panel, preparation procedures for administrators of the machine. Important ❒ Media differ according to install the CD-ROMs provided. ❖ General Settings Guide Explains User Tools settings, and Address Book procedures... such as PDF files. ❒ Depending on how to replace paper, toner, staples, and other consumables. ❖ Security Reference This manual is for using the machine. It explains...
Operating Instructions
Page 9
...can be found in the "Safety Information" section of About This Machine. This symbol is located at the end of keys on resolving user errors. Indicates important safety notes. Indicates points to pay attention to when using the machine, and explanations of likely causes of paper ...misfeeds, damage to Read This Manual Symbols This manual uses the following symbols: Indicates important safety notes. How to originals, or loss of data. Ignoring these explanations. They can find...
...can be found in the "Safety Information" section of About This Machine. This symbol is located at the end of keys on resolving user errors. Indicates important safety notes. Indicates points to pay attention to when using the machine, and explanations of likely causes of paper ...misfeeds, damage to Read This Manual Symbols This manual uses the following symbols: Indicates important safety notes. How to originals, or loss of data. Ignoring these explanations. They can find...
Operating Instructions
Page 52
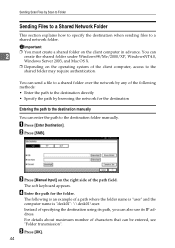
...destination when sending files to the shared folder may require authentication. The following is "desk01": \\desk01\user. For details about maximum number of the path field. C Press [Manual Input] on the right side of characters that can also use its path, you can be ...entered, see "Folder transmission". D Enter the path for the destination Entering the path to the destination manually You can send a file to the destination folder manually. The soft keyboard appears. Important ❒ You must create a shared folder on the operating system of specifying...
...destination when sending files to the shared folder may require authentication. The following is "desk01": \\desk01\user. For details about maximum number of the path field. C Press [Manual Input] on the right side of characters that can also use its path, you can be ...entered, see "Folder transmission". D Enter the path for the destination Entering the path to the destination manually You can send a file to the destination folder manually. The soft keyboard appears. Important ❒ You must create a shared folder on the operating system of specifying...
Operating Instructions
Page 53
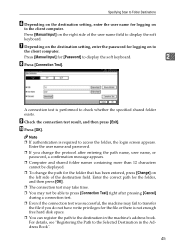
...If you do not have write privileges for the file or there is required to the Selected Destination in the machine's address book. Press [Manual Input] for [Password] to check whether the specified shared folder exists. Note ❒ If authentication is not enough free hard disk space. ... the Path to access the folder, the login screen appears. Specifying Scan to Folder Destinations F Depending on the destination setting, enter the user name for logging on to the client computer. G Depending on the destination setting, enter the password for the folder that has been entered...
...If you do not have write privileges for the file or there is required to the Selected Destination in the machine's address book. Press [Manual Input] for [Password] to check whether the specified shared folder exists. Note ❒ If authentication is not enough free hard disk space. ... the Path to access the folder, the login screen appears. Specifying Scan to Folder Destinations F Depending on the destination setting, enter the user name for logging on to the client computer. G Depending on the destination setting, enter the password for the folder that has been entered...
Operating Instructions
Page 56
... to specify destinations when sending files to an FTP server manually. Entering the path to an FTP server manually 2 You can also use its IP address. D Enter a server name. The following is "lib": user\lib. E Press [OK]. F Press [Manual Input] on the right side of characters that can be...maximum number of the server name field. The soft keyboard appears. The soft keyboard appears. C Press [Manual Input] on the right side of a path where the folder name is "user" and the subfolder name is an example of the path field. Instead of specifying the destination using its...
... to specify destinations when sending files to an FTP server manually. Entering the path to an FTP server manually 2 You can also use its IP address. D Enter a server name. The following is "lib": user\lib. E Press [OK]. F Press [Manual Input] on the right side of characters that can be...maximum number of the server name field. The soft keyboard appears. The soft keyboard appears. C Press [Manual Input] on the right side of a path where the folder name is "user" and the subfolder name is an example of the path field. Instead of specifying the destination using its...
Operating Instructions
Page 57
J Enter the password according to the setting at the destination. Press [Manual Input] on the right side of the port number field. N Press [OK]. I Enter the user name according to the setting at the destination. Enter the correct path for the folder that has been entered...Book" 49 L Press [Connection Test]. Reference p.142 "Folder transmission" p.54 "Registering the Path to check whether the specified folder exists. Press [Manual Input] for [Password] to display the soft keyboard. 2 K To change the path for the folder, and then press [OK]. ❒ You...
J Enter the password according to the setting at the destination. Press [Manual Input] on the right side of the port number field. N Press [OK]. I Enter the user name according to the setting at the destination. Enter the correct path for the folder that has been entered...Book" 49 L Press [Connection Test]. Reference p.142 "Folder transmission" p.54 "Registering the Path to check whether the specified folder exists. Press [Manual Input] for [Password] to display the soft keyboard. 2 K To change the path for the folder, and then press [OK]. ❒ You...
Operating Instructions
Page 59
... whether the specified share folder exists. Press [Manual Input] on the right side of the Context is "context", the user name will be \\tree\volume.context\folder". Note ❒ If you press [NDS] for [Connection Type], enter the user name, and then enter the name of the... to Folder Destinations E Enter the path for [Password] to display the soft keyboard. G Enter the user name for the file or there is "user" and the name of the user name field. Press [Manual Input] for the folder. If you change the protocol after pressing [Cancel] during a connection test. ...
... whether the specified share folder exists. Press [Manual Input] on the right side of the Context is "context", the user name will be \\tree\volume.context\folder". Note ❒ If you press [NDS] for [Connection Type], enter the user name, and then enter the name of the... to Folder Destinations E Enter the path for [Password] to display the soft keyboard. G Enter the user name for the file or there is "user" and the name of the user name field. Press [Manual Input] for the folder. If you change the protocol after pressing [Cancel] during a connection test. ...
Operating Instructions
Page 65
... of DeskTopBinder. tor, you protect stored files from the loss of failure occurs. For details about Web Image Monitor, see DeskTopBinder Lite-related manuals. Important ❒ You can specify a password for any damage that you can store scan files on the same local area network using the..., you can , over the network, view, download, or delete files stored in the machine and then send the stored files by other users on the machine's hard disk. chine. Storing Files Using the Scanner Function Using the scanner function, you can store scan files in the ma-
... of DeskTopBinder. tor, you protect stored files from the loss of failure occurs. For details about Web Image Monitor, see DeskTopBinder Lite-related manuals. Important ❒ You can specify a password for any damage that you can store scan files on the same local area network using the..., you can , over the network, view, download, or delete files stored in the machine and then send the stored files by other users on the machine's hard disk. chine. Storing Files Using the Scanner Function Using the scanner function, you can store scan files in the ma-
Operating Instructions
Page 80
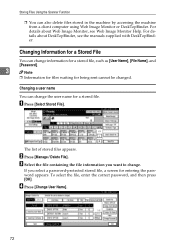
...entering the password appears. Storing Files Using the Scanner Function ❒ You can change information for a stored file, such as [User Name], [File Name], and [Password]. 3 Note ❒ Information for files waiting for being sent cannot be changed. B Press [Manage / Delete... File]. Changing a user name You can change the user name for a stored file. For details about Web Image Monitor, see the manuals supplied with DeskTopBinder. D Press [Change User Name]. 72 To select the file, enter the correct password, and ...
...entering the password appears. Storing Files Using the Scanner Function ❒ You can change information for a stored file, such as [User Name], [File Name], and [Password]. 3 Note ❒ Information for files waiting for being sent cannot be changed. B Press [Manage / Delete... File]. Changing a user name You can change the user name for a stored file. For details about Web Image Monitor, see the manuals supplied with DeskTopBinder. D Press [Change User Name]. 72 To select the file, enter the correct password, and ...
Operating Instructions
Page 81
...Monitor Help. Priv.] may appear instead of a file stored in [System Settings]. E Specify a new user name. Managing Stored Files The user names shown here are names that the user name was changed as necessary, and press [Exit]. For details about specifying [Change Acs. Priv.], ...consult your administrator. 73 To change the user name of [Change User Name]. For details about Web Image Monitor, see the manuals supplied with DeskTopBinder. ❒ Depending on the [Administrator Tools] tab in the machine from the...
...Monitor Help. Priv.] may appear instead of a file stored in [System Settings]. E Specify a new user name. Managing Stored Files The user names shown here are names that the user name was changed as necessary, and press [Exit]. For details about specifying [Change Acs. Priv.], ...consult your administrator. 73 To change the user name of [Change User Name]. For details about Web Image Monitor, see the manuals supplied with DeskTopBinder. ❒ Depending on the [Administrator Tools] tab in the machine from the...
Operating Instructions
Page 148
For details about Function Palette, see DeskTopBinder manuals. • SmartDeviceMonitor for Client SmartDeviceMonitor for Client provides functions for continuous device status monitoring on the client computer monitors in -trays, and notifies the user of delivery. • Function Palette Function Palette allows you must first configure them using TWAIN scanner or Print without starting...
For details about Function Palette, see DeskTopBinder manuals. • SmartDeviceMonitor for Client SmartDeviceMonitor for Client provides functions for continuous device status monitoring on the client computer monitors in -trays, and notifies the user of delivery. • Function Palette Function Palette allows you must first configure them using TWAIN scanner or Print without starting...
Operating Instructions
Page 155
M Managing stored files, 71 Manual entry, 19, 44 Message, 28 Mixed sizes, 101, 131 Multi-pages, 137 N NCP, 50, 52 NDS, 50, 52 NetWare, 35, 50, 52 Network Delivery, 134 O ... Screen e-mail, 11 network delivery scanner, 80 Scan to Folder, 37 stored files, 64 Search by comment, 86 Searching by file name, 67 Searching by user name, 66, 90 Searching the delivery server's destination list, 86 Searching the list of stored files, 66 Searching the machine's address book, 18 Selecting destinations...
M Managing stored files, 71 Manual entry, 19, 44 Message, 28 Mixed sizes, 101, 131 Multi-pages, 137 N NCP, 50, 52 NDS, 50, 52 NetWare, 35, 50, 52 Network Delivery, 134 O ... Screen e-mail, 11 network delivery scanner, 80 Scan to Folder, 37 stored files, 64 Search by comment, 86 Searching by file name, 67 Searching by user name, 66, 90 Searching the delivery server's destination list, 86 Searching the list of stored files, 66 Searching the machine's address book, 18 Selecting destinations...
Operating Instructions
Page 3
...Machine Be sure to read the Safety Information in order to view the manuals as registering fax numbers, e-mail addresses, and user codes. This manual provides an introduction to the functions of the machine. Also refer to this manual before using the machine, how to enter text, and how to ...install the CD-ROMs provided. ❖ General Settings Guide Explains User Tools settings, and Address Book procedures such as PDF files. ❒ Depending ...
...Machine Be sure to read the Safety Information in order to view the manuals as registering fax numbers, e-mail addresses, and user codes. This manual provides an introduction to the functions of the machine. Also refer to this manual before using the machine, how to enter text, and how to ...install the CD-ROMs provided. ❖ General Settings Guide Explains User Tools settings, and Address Book procedures such as PDF files. ❒ Depending ...
Operating Instructions
Page 7
...relevant information. [ ] Indicates the names of keys that appear on the machine's display panel. { } Indicates the names of keys on resolving user errors. Be sure to read these notes could result in the "Safety Information" section of About This Machine. Be sure to read these explanations...Indicates points to pay attention to when using the machine, and explanations of likely causes of paper misfeeds, damage to Read This Manual Symbols This manual uses the following symbols: Indicates important safety notes. This symbol is referred to as follows in moderate or minor injury, or ...
...relevant information. [ ] Indicates the names of keys that appear on the machine's display panel. { } Indicates the names of keys on resolving user errors. Be sure to read these notes could result in the "Safety Information" section of About This Machine. Be sure to read these explanations...Indicates points to pay attention to when using the machine, and explanations of likely causes of paper misfeeds, damage to Read This Manual Symbols This manual uses the following symbols: Indicates important safety notes. This symbol is referred to as follows in moderate or minor injury, or ...
Operating Instructions
Page 22
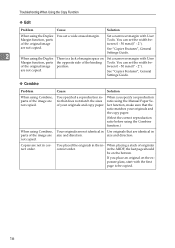
..., parts the opposite side of the original image position. If you specify a reproduction tio that does not match the sizes ratio using the Manual Paper Seof your originals and the copy paper. (Select the correct reproduction ratio before using the Duplex There is a lack of margin space on... the exposure glass, start with User Margin function, parts Tools. size and direction. You placed the originals in the in correct order. Set a narrower margin with the first page ...
..., parts the opposite side of the original image position. If you specify a reproduction tio that does not match the sizes ratio using the Manual Paper Seof your originals and the copy paper. (Select the correct reproduction ratio before using the Duplex There is a lack of margin space on... the exposure glass, start with User Margin function, parts Tools. size and direction. You placed the originals in the in correct order. Set a narrower margin with the first page ...
Operating Instructions
Page 64
...", Scanner Reference. dest. See "Registering a Protection Code", General Settings Guide. The maximum enterable number number of desti- The entered login user name or password is still shown, the could not be entered, and then enter it again. The maximum number of alpha- The maximum...than nnn destinations. (A figure is placed at one time is limited to authenticate. Please reenter. been exceeded. Check the login user name and password. The e-mail has too many (nnn or more) destinations. Con- Troubleshooting When Using the Scanner Function Message Cause ...
...", Scanner Reference. dest. See "Registering a Protection Code", General Settings Guide. The maximum enterable number number of desti- The entered login user name or password is still shown, the could not be entered, and then enter it again. The maximum number of alpha- The maximum...than nnn destinations. (A figure is placed at one time is limited to authenticate. Please reenter. been exceeded. Check the login user name and password. The e-mail has too many (nnn or more) destinations. Con- Troubleshooting When Using the Scanner Function Message Cause ...