Wireless Security
Page 1
...corporate firewall in an attempt to bring an awareness to both the user and the corporate IT manager as follows: First, securing wireless systems in general is discussed, then securing each point along the access pipe is discussed. Many of the vulnerabilities can be ...the security vulnerabilities lie and what can be shipped worldwide this year (2001), and double that 6.2 million wireless devices will be alleviated easily by : Access Business Group Compaq Computer Corporation Contents Introduction 3 Security in two years. White Paper December 2001 Prepared by implementing policies for ...
...corporate firewall in an attempt to bring an awareness to both the user and the corporate IT manager as follows: First, securing wireless systems in general is discussed, then securing each point along the access pipe is discussed. Many of the vulnerabilities can be ...the security vulnerabilities lie and what can be shipped worldwide this year (2001), and double that 6.2 million wireless devices will be alleviated easily by : Access Business Group Compaq Computer Corporation Contents Introduction 3 Security in two years. White Paper December 2001 Prepared by implementing policies for ...
Wireless Security
Page 2
... or products that were tested. and/or other countries. Wireless Security White Paper prepared by Access Business Group First Edition (December 2001) Document Number 161Z-1201A-WWEN IN NO EVENT SHALL COMPAQ BE LIABLE FOR ANY DIRECT, CONSEQUENTIAL, INCIDENTAL, SPECIAL, ... not be construed as constituting a further or additional warranty. Compaq, the Compaq logo, Deskpro, and Evo are trademarks of their respective companies. ©2002 Compaq Information Technologies Group, L.P. The limited warranties for Compaq products are trademarks of product quality or correctness, nor does...
... or products that were tested. and/or other countries. Wireless Security White Paper prepared by Access Business Group First Edition (December 2001) Document Number 161Z-1201A-WWEN IN NO EVENT SHALL COMPAQ BE LIABLE FOR ANY DIRECT, CONSEQUENTIAL, INCIDENTAL, SPECIAL, ... not be construed as constituting a further or additional warranty. Compaq, the Compaq logo, Deskpro, and Evo are trademarks of their respective companies. ©2002 Compaq Information Technologies Group, L.P. The limited warranties for Compaq products are trademarks of product quality or correctness, nor does...
Wireless Security
Page 3
... Journal Online, April 27, 2001). 2 Gomes. For complete wireless and mobile security solutions, please contact Compaq Global Services at astonishing rates to security breaches. Both wired and wireless security implementations must be shipped worldwide this year (2001), and double... computer networks) can be alleviated easily by using wireless technologies at http://www.compaq.com/services/index_infrastructure.html. Since wireless networks dispense with cables, users connected to wireless computer networks (or wirelessly connected to such networks. Market researcher Cahners In-...
... Journal Online, April 27, 2001). 2 Gomes. For complete wireless and mobile security solutions, please contact Compaq Global Services at astonishing rates to security breaches. Both wired and wireless security implementations must be shipped worldwide this year (2001), and double... computer networks) can be alleviated easily by using wireless technologies at http://www.compaq.com/services/index_infrastructure.html. Since wireless networks dispense with cables, users connected to wireless computer networks (or wirelessly connected to such networks. Market researcher Cahners In-...
Wireless Security
Page 4
... and security. Encryption is a conduit through which a security system seeks to preserve stored information and information that may arise with wireless networks at the corporate firewall and servers (Corporate Access) 5. Security and the Pipe A pipe is an important tool for preserving... access device level or client (Device Security) 2. Non-repudiation is preserved through the corporate firewall to corporate applications. Wireless Security White Paper 4 Essential Elements of Security The essential elements of security as persons seeking access to digital information, are...
... and security. Encryption is a conduit through which a security system seeks to preserve stored information and information that may arise with wireless networks at the corporate firewall and servers (Corporate Access) 5. Security and the Pipe A pipe is an important tool for preserving... access device level or client (Device Security) 2. Non-repudiation is preserved through the corporate firewall to corporate applications. Wireless Security White Paper 4 Essential Elements of Security The essential elements of security as persons seeking access to digital information, are...
Wireless Security
Page 5
... data transfer. Device Security Despite the growing popularity of handheld PCs, PDAs, and cellular telephones, the truly ubiquitous mobile computing device in the United States is still the notebook computer (in Europe it , is not a wireless security concern, but a wired one place to the next ...either wired or wirelessly. Figure 1: The Network Pipe The vertical yellow lines in planning security models. Notebook computers are used for online connectivity,...
... data transfer. Device Security Despite the growing popularity of handheld PCs, PDAs, and cellular telephones, the truly ubiquitous mobile computing device in the United States is still the notebook computer (in Europe it , is not a wireless security concern, but a wired one place to the next ...either wired or wirelessly. Figure 1: The Network Pipe The vertical yellow lines in planning security models. Notebook computers are used for online connectivity,...
Wireless Security
Page 6
... have in public places (hotel lobbies, airplanes, and the like) than larger stationary devices. For information on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. Loss and Theft Mobile access devices are more susceptible to their employees. Vulnerability to Hacking...in order to tamper with or steal information. Minimizing vulnerability to hackers can and should take. Wireless Security White Paper 6 Moreover, workers are using notebook computers more and more as desktop machines while in managing individually owned handheld mobile devices and ...
... have in public places (hotel lobbies, airplanes, and the like) than larger stationary devices. For information on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. Loss and Theft Mobile access devices are more susceptible to their employees. Vulnerability to Hacking...in order to tamper with or steal information. Minimizing vulnerability to hackers can and should take. Wireless Security White Paper 6 Moreover, workers are using notebook computers more and more as desktop machines while in managing individually owned handheld mobile devices and ...
Wireless Security
Page 7
...smart card is to choose simpler passwords. Some of smart cards: contact and contactless. For various reasons they are easy to a wireless network, even with a personal identification number (PIN). Users often choose passwords that do not perform such processing themselves. The straightforward solution... a PIN presents thieves with a further barrier to obtaining access to use, and the newer, more robust by a given key. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to the device...
...smart card is to choose simpler passwords. Some of smart cards: contact and contactless. For various reasons they are easy to a wireless network, even with a personal identification number (PIN). Users often choose passwords that do not perform such processing themselves. The straightforward solution... a PIN presents thieves with a further barrier to obtaining access to use, and the newer, more robust by a given key. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to the device...
Wireless Security
Page 8
.... The information then goes through some complex algorithms to produce Compaq Fingerprint Identification Technology (FIT) for Compaq Armada and Evo notebook computers. The information is then extracted and compared to improve ... the network. Such attacks involve device power measurements and their vulnerability to identify an individual. Wireless Security White Paper 8 A concern with Identix, a leader in order to at least two...The user places a registered finger on the reader attached to his or her PC in order to log on a mobile device is sensitive, it is allowed to...
.... The information then goes through some complex algorithms to produce Compaq Fingerprint Identification Technology (FIT) for Compaq Armada and Evo notebook computers. The information is then extracted and compared to improve ... the network. Such attacks involve device power measurements and their vulnerability to identify an individual. Wireless Security White Paper 8 A concern with Identix, a leader in order to at least two...The user places a registered finger on the reader attached to his or her PC in order to log on a mobile device is sensitive, it is allowed to...
Wireless Security
Page 9
... encryption at power-off • Key recovery ensures that corporate data is not lost if the pass-phrase is forgotten Compaq iPAQ Pocket PC's ship with F-Secure today. Notwithstanding the protection offered, such firewalls are available from Network ICE Corporation. Different connection technologies... as a key fob, smart card, or software token. It generates a unique code every sixty seconds in the pipe, after wireless access devices, is a two-factor authentication technique that provide access to corporate servers. These technologies provide the infrastructure, standards, and ...
... encryption at power-off • Key recovery ensures that corporate data is not lost if the pass-phrase is forgotten Compaq iPAQ Pocket PC's ship with F-Secure today. Notwithstanding the protection offered, such firewalls are available from Network ICE Corporation. Different connection technologies... as a key fob, smart card, or software token. It generates a unique code every sixty seconds in the pipe, after wireless access devices, is a two-factor authentication technique that provide access to corporate servers. These technologies provide the infrastructure, standards, and ...
Wireless Security
Page 10
...a cell phone to a handheld to a desktop computer without having to a wired LAN within a building or campus. Figure 2: Wireless Local-area Network Wireless local area networks (WLANs) and wireless wide area networks (WWANs) facilitate this usage. Figure 2 illustrates a WLAN. A brief description of each technology are , such as... to transmit data among its nodes. It is a type of LAN that exist on the three types of wireless networks and provide an illustration of these connectivity technologies follows and detailed papers that uses high-frequency radio waves rather than wires...
...a cell phone to a handheld to a desktop computer without having to a wired LAN within a building or campus. Figure 2: Wireless Local-area Network Wireless local area networks (WLANs) and wireless wide area networks (WWANs) facilitate this usage. Figure 2 illustrates a WLAN. A brief description of each technology are , such as... to transmit data among its nodes. It is a type of LAN that exist on the three types of wireless networks and provide an illustration of these connectivity technologies follows and detailed papers that uses high-frequency radio waves rather than wires...
Wireless Security
Page 11
WWANs use one of the three digital wireless telephone technologies. A WPAN permits personal devices such as handheld PCs to connect wirelessly to -multipoint voice and data transfer. Japan's NT DoCoMo uses I-mode technology in the United States ... for mobile telephones. The official names for Mobile communication (GSM), developed in Europe, is a TDMA technology. Wireless Security White Paper 11 Wireless Personal-area Networks Wireless personal-area networks (WPANs) can also use infrared technology. GSM is the most widely used to support voice transmission...
WWANs use one of the three digital wireless telephone technologies. A WPAN permits personal devices such as handheld PCs to connect wirelessly to -multipoint voice and data transfer. Japan's NT DoCoMo uses I-mode technology in the United States ... for mobile telephones. The official names for Mobile communication (GSM), developed in Europe, is a TDMA technology. Wireless Security White Paper 11 Wireless Personal-area Networks Wireless personal-area networks (WPANs) can also use infrared technology. GSM is the most widely used to support voice transmission...
Wireless Security
Page 12
... violates authentication and possibly integrity), or even shutting the network down (sabotage, which is a WLAN, a WPAN, or a WWAN, a wireless network uses radio waves to the Internet, Internet e-mail, enterprise intranet and corporate e-mail. Compaq WWANs using CDPD and GSM technologies are vulnerabilities exposed with the same equipment, and because it is difficult...
... violates authentication and possibly integrity), or even shutting the network down (sabotage, which is a WLAN, a WPAN, or a WWAN, a wireless network uses radio waves to the Internet, Internet e-mail, enterprise intranet and corporate e-mail. Compaq WWANs using CDPD and GSM technologies are vulnerabilities exposed with the same equipment, and because it is difficult...
Wireless Security
Page 13
...Those technologies are slightly less secure since they include only digital encoding without encryption. Smaller companies have PKI support for a wireless network. The following sub-sections discuss these vulnerabilities in describing the two primary technologies that help forestall eavesdropping and its concomitant...the understanding that is not provided. It is necessary at this juncture, however, to secure one of information over a wireless network must travel over the network. and Entrust do not have point solutions to specific applications that travels over networks ...
...Those technologies are slightly less secure since they include only digital encoding without encryption. Smaller companies have PKI support for a wireless network. The following sub-sections discuss these vulnerabilities in describing the two primary technologies that help forestall eavesdropping and its concomitant...the understanding that is not provided. It is necessary at this juncture, however, to secure one of information over a wireless network must travel over the network. and Entrust do not have point solutions to specific applications that travels over networks ...
Wireless Security
Page 14
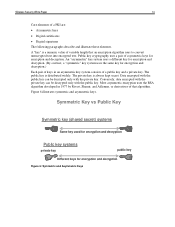
..., Shamir, and Adleman, or derivatives of a PKI are: • Asymmetric keys • Digital certificates • Digital signatures The following paragraphs describe and illustrate these elements. Wireless Security White Paper 14 Core elements of that an encryption algorithm uses to convert unencrypted text into encrypted text.
..., Shamir, and Adleman, or derivatives of a PKI are: • Asymmetric keys • Digital certificates • Digital signatures The following paragraphs describe and illustrate these elements. Wireless Security White Paper 14 Core elements of that an encryption algorithm uses to convert unencrypted text into encrypted text.
Wireless Security
Page 15
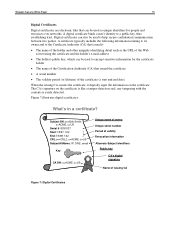
... to encrypt sensitive information for people and resources over networks. Digital certificates can be used to a public key, thus establishing trust. Figure 7 illustrates digital certificates. Wireless Security White Paper 15 Digital Certificates Digital certificates are electronic files that can be used as unique identifiers for the certificate holder • The name...
... to encrypt sensitive information for people and resources over networks. Digital certificates can be used to a public key, thus establishing trust. Figure 7 illustrates digital certificates. Wireless Security White Paper 15 Digital Certificates Digital certificates are electronic files that can be used as unique identifiers for the certificate holder • The name...
Wireless Security
Page 16
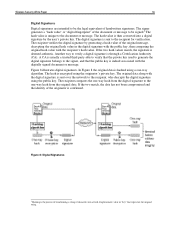
... the original hash value in the digital signature with the public key, then comparing the original hash value with the digitally signed document or message. Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to be signed.4 The hash value is unique to the document or message. If the...
... the original hash value in the digital signature with the public key, then comparing the original hash value with the digitally signed document or message. Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to be signed.4 The hash value is unique to the document or message. If the...
Wireless Security
Page 17
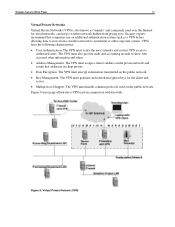
...• Multiprotocol Support. VPNs have the following characteristics: • User Authentication. The VPN must handle common protocols used in conjunction with firewalls. Wireless Security White Paper 17 Virtual Private Networks Virtual Private Networks (VPNs), also known as a VPN before allowing data to cross from prying eyes. ... VPN access to authorized users. The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to show who accessed what information and when. • Address Management.
...• Multiprotocol Support. VPNs have the following characteristics: • User Authentication. The VPN must handle common protocols used in conjunction with firewalls. Wireless Security White Paper 17 Virtual Private Networks Virtual Private Networks (VPNs), also known as a VPN before allowing data to cross from prying eyes. ... VPN access to authorized users. The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to show who accessed what information and when. • Address Management.
Wireless Security
Page 18
... service provider (ISP) to enable VPNs over the public Internet. This exchange takes place through private "tunnels" over the Internet. Wireless Security White Paper 18 Several VPN protocols are therefore more secure Tunnel mode encrypts both the header and the payload. In effect, ...Internet Engineering Task Force (IETF) for wide-area communication. By making secure use public and private keys and authenticate the sender with wireless networks in its own lines for approval as a standard. L2TP merges the best features of the communications model. By contrast, earlier...
... service provider (ISP) to enable VPNs over the public Internet. This exchange takes place through private "tunnels" over the Internet. Wireless Security White Paper 18 Several VPN protocols are therefore more secure Tunnel mode encrypts both the header and the payload. In effect, ...Internet Engineering Task Force (IETF) for wide-area communication. By making secure use public and private keys and authenticate the sender with wireless networks in its own lines for approval as a standard. L2TP merges the best features of the communications model. By contrast, earlier...
Wireless Security
Page 19
... V-One: • Works only with established need-to authenticate the mobile participant and generate a session key. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by performing packet switching at remote hosting center • Designed to provide direct, end-to...
... V-One: • Works only with established need-to authenticate the mobile participant and generate a session key. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by performing packet switching at remote hosting center • Designed to provide direct, end-to...
Wireless Security
Page 20
.... WAP 1.2 adds support for more difficult. WTLS is based on Transport Layer Security (TLS), a security layer used on WAP 2.0.) Wireless Transport Layer Security (WTLS) is authenticated; • Class 2 authentication authenticates only the server; • Class 3 authentication requires both ...specifically for non-repudiation. WAP 2.0 is based on standard Internet TLS, and designed so as a result of modulation.) Wireless Access Protocol The Wireless Access Protocol (WAP) is designed to be effective but not infallible. Besides encryption, the IS-95 standard of CDMA...
.... WAP 1.2 adds support for more difficult. WTLS is based on Transport Layer Security (TLS), a security layer used on WAP 2.0.) Wireless Transport Layer Security (WTLS) is authenticated; • Class 2 authentication authenticates only the server; • Class 3 authentication requires both ...specifically for non-repudiation. WAP 2.0 is based on standard Internet TLS, and designed so as a result of modulation.) Wireless Access Protocol The Wireless Access Protocol (WAP) is designed to be effective but not infallible. Besides encryption, the IS-95 standard of CDMA...