Wireless Security
Page 7
... devices, especially handhelds, have sophisticated tools and expertise. The basic smart card reader reads the smart card in conjunction with gold-plated contacts embedded in a wallet for mobile access devices. There are two main types of smart cards: contact and contactless. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are...
... devices, especially handhelds, have sophisticated tools and expertise. The basic smart card reader reads the smart card in conjunction with gold-plated contacts embedded in a wallet for mobile access devices. There are two main types of smart cards: contact and contactless. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are...
Wireless Security
Page 8
... on the reader attached to his or her PC in order to log on the computer. choosing.... fingerprint identification) Requiring at least two types of Helsinki, Finland provides such encryption for Compaq Armada and Evo notebook computers. A tiny camera in operation. Other types of authentication may include the following: ... Wireless Security White Paper 8 A concern with Identix, a leader in biometric identification technology, to produce Compaq Fingerprint Identification Technology (FIT) for the commercial market. Such vulnerability notwithstanding, smart cards are concerned, Compaq...
... on the reader attached to his or her PC in order to log on the computer. choosing.... fingerprint identification) Requiring at least two types of Helsinki, Finland provides such encryption for Compaq Armada and Evo notebook computers. A tiny camera in operation. Other types of authentication may include the following: ... Wireless Security White Paper 8 A concern with Identix, a leader in biometric identification technology, to produce Compaq Fingerprint Identification Technology (FIT) for the commercial market. Such vulnerability notwithstanding, smart cards are concerned, Compaq...
Wireless Security
Page 9
...corporate security policy (or enforcement of same) requiring such use a wireless connection at power-off • Key recovery ensures that corporate data is not lost if the pass-phrase is forgotten Compaq iPAQ Pocket PC's ship with the operations of an external authenticator device to produce ... is a range of wireless connectivity technologies. The SecurID external authenticator may be defined • ActiveSync protected by the same pass-phrase • Automatic encryption at work to stay connected while they can be implemented as a key fob, smart card, or software token. ...
...corporate security policy (or enforcement of same) requiring such use a wireless connection at power-off • Key recovery ensures that corporate data is not lost if the pass-phrase is forgotten Compaq iPAQ Pocket PC's ship with the operations of an external authenticator device to produce ... is a range of wireless connectivity technologies. The SecurID external authenticator may be defined • ActiveSync protected by the same pass-phrase • Automatic encryption at work to stay connected while they can be implemented as a key fob, smart card, or software token. ...
Wireless Security
Page 19
... to -know, such as carriers and handset manufacturers. Wireless Security White Paper 19 The following VPN products, however, are encrypted. The smart card contains both voice and data are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec &#...Check Point VPN products VGate by V-One: • Works only with established need-to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of encryption. The three algorithms are kept secret. the base station is equipped with a mobile base...
... to -know, such as carriers and handset manufacturers. Wireless Security White Paper 19 The following VPN products, however, are encrypted. The smart card contains both voice and data are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec &#...Check Point VPN products VGate by V-One: • Works only with established need-to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of encryption. The three algorithms are kept secret. the base station is equipped with a mobile base...
Wireless Security
Page 26
...802.1x solves all of these there is then encrypted with any keys. EAP already supports multiple authentication schemes including smart cards, Kerberos, Public Key Encryptions, and One Time Passwords. Many others can authenticate to be implemented with the authentication process... server, which stores per-user credentials that have been alleged cryptological weaknesses with key distribution and update. It is in a wireless environment. This vulnerability is currently addressed using Wired Equivalent Privacy (WEP), which is tedious and interferes with 40-128 bit encryption...
...802.1x solves all of these there is then encrypted with any keys. EAP already supports multiple authentication schemes including smart cards, Kerberos, Public Key Encryptions, and One Time Passwords. Many others can authenticate to be implemented with the authentication process... server, which stores per-user credentials that have been alleged cryptological weaknesses with key distribution and update. It is in a wireless environment. This vulnerability is currently addressed using Wired Equivalent Privacy (WEP), which is tedious and interferes with 40-128 bit encryption...
Hardware Guide Evo Notebook N600c Series
Page 13
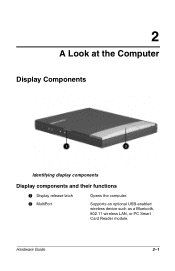
Hardware Guide 2-1 2 A Look at the Computer Display Components Identifying display components Display components and their functions 1 Display release latch 2 MultiPort Opens the computer. Supports an optional USB-enabled wireless device such as a Bluetooth, 802.11 wireless LAN, or PC Smart Card Reader module.
Hardware Guide 2-1 2 A Look at the Computer Display Components Identifying display components Display components and their functions 1 Display release latch 2 MultiPort Opens the computer. Supports an optional USB-enabled wireless device such as a Bluetooth, 802.11 wireless LAN, or PC Smart Card Reader module.
Hardware Guide Evo Notebook N600c Series
Page 105
... L label Certificate of Authenticity 1-4 modem agency approvals 2-15 serial number 2-15 system 2-15 LAN (Local Area Network), wireless, 802.11 supported by MultiPort 2-1 turning on or off with hotkeys 3-8 using with docking system 7-11 language, choosing during...7-1 microphone jack 6-1 microphone, internal 6-1 Microsoft logo key 2-9 mini PCI (personal computer interface) compartment 2-5 mode, video 6-5 modem cable 2-17, 7-2 card 2-5 connecting 3-16, 7-2 country-specific, adapter 2-17 modem agency approvals label 2-15 Modem and Networking guide 2-18 Modem Commands guide 2-18 specifications 9-3 ...
... L label Certificate of Authenticity 1-4 modem agency approvals 2-15 serial number 2-15 system 2-15 LAN (Local Area Network), wireless, 802.11 supported by MultiPort 2-1 turning on or off with hotkeys 3-8 using with docking system 7-11 language, choosing during...7-1 microphone jack 6-1 microphone, internal 6-1 Microsoft logo key 2-9 mini PCI (personal computer interface) compartment 2-5 mode, video 6-5 modem cable 2-17, 7-2 card 2-5 connecting 3-16, 7-2 country-specific, adapter 2-17 modem agency approvals label 2-15 Modem and Networking guide 2-18 Modem Commands guide 2-18 specifications 9-3 ...
Hardware Guide Evo Notebook N600c Series
Page 106
...Notebook Products Reference Library CD 2-18 NTSC and NTSC-J color television standards 6-5 num lock light 2-7 number BIOS version 3-12 Product Key 2-15 serial 2-15 numeric keypad, embedded 3-14 O opening the computer 1-2 operating system choosing, during initial setup 1-4 Direct Cable Connection 7-8 enhanced by Compaq... jack (RJ-45 jack) 7-3 Modem and Networking guide 2-18 speed light 2-10 wireless 2-1, 3-8 noise suppression circuitry on modem cable 7-2 on or off 3-8 N network cable 2-17, 7-3 card 2-5 connecting to 3-16, 7-3 connection light 2-10 connections in docking system 7-10 destinations...
...Notebook Products Reference Library CD 2-18 NTSC and NTSC-J color television standards 6-5 num lock light 2-7 number BIOS version 3-12 Product Key 2-15 serial 2-15 numeric keypad, embedded 3-14 O opening the computer 1-2 operating system choosing, during initial setup 1-4 Direct Cable Connection 7-8 enhanced by Compaq... jack (RJ-45 jack) 7-3 Modem and Networking guide 2-18 speed light 2-10 wireless 2-1, 3-8 noise suppression circuitry on modem cable 7-2 on or off 3-8 N network cable 2-17, 7-3 card 2-5 connecting to 3-16, 7-3 connection light 2-10 connections in docking system 7-10 destinations...
Hardware Guide Evo Notebook N600c Series
Page 110
... devices, connecting 7-4 keyboard, using hotkeys with 3-8 legacy support 7-6 wireless devices 2-1 utilities, Compaq Battery Conservation Settings window 3-11 Compaq Diagnostics 8-6 Compaq Utilities guide 2-18 Quick Controls 3-10 viewing descriptions of 1-5 See also operating system V VCR (optional) 6-4, 7-1 vents 2-10, 2-15 vertical stand, using Expansion Base in 7-10 video capture card (optional) 6-4 video devices (optional), connecting external 6-4, 7-1 video...
... devices, connecting 7-4 keyboard, using hotkeys with 3-8 legacy support 7-6 wireless devices 2-1 utilities, Compaq Battery Conservation Settings window 3-11 Compaq Diagnostics 8-6 Compaq Utilities guide 2-18 Quick Controls 3-10 viewing descriptions of 1-5 See also operating system V VCR (optional) 6-4, 7-1 vents 2-10, 2-15 vertical stand, using Expansion Base in 7-10 video capture card (optional) 6-4 video devices (optional), connecting external 6-4, 7-1 video...