Wireless Security
Page 3
...the newest and potentially most of access is a great convenience. This is so in part because many users are not aware of specific security vulnerabilities or don't understand the magnitude of potential loss and, therefore, do not put the subject of wireless security into ...constantly evaluated and improved as printers, by implementing policies for users and adding security layers to Assure E-Business Success" (http://activeanswers.compaq.com/ActiveAnswers/Render/1,1027,1317-6-100-225-1,00.html February, 2000) for important detail on best practices and established technologies for wired...
...the newest and potentially most of access is a great convenience. This is so in part because many users are not aware of specific security vulnerabilities or don't understand the magnitude of potential loss and, therefore, do not put the subject of wireless security into ...constantly evaluated and improved as printers, by implementing policies for users and adding security layers to Assure E-Business Success" (http://activeanswers.compaq.com/ActiveAnswers/Render/1,1027,1317-6-100-225-1,00.html February, 2000) for important detail on best practices and established technologies for wired...
Wireless Security
Page 6
... places (hotel lobbies, airplanes, and the like) than larger stationary devices. For information on Compaq handheld devices, see http://www.compaq.com/showroom/notebooks.html. They may be accomplished when both access devices and portals themselves are protected by their ...devices, the first link in monitoring their own firewalls. For information on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. The following subsections describe security problems specific to public and private networks in managing individually owned handheld mobile devices ...
... places (hotel lobbies, airplanes, and the like) than larger stationary devices. For information on Compaq handheld devices, see http://www.compaq.com/showroom/notebooks.html. They may be accomplished when both access devices and portals themselves are protected by their ...devices, the first link in monitoring their own firewalls. For information on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. The following subsections describe security problems specific to public and private networks in managing individually owned handheld mobile devices ...
Wireless Security
Page 7
... card with a PIN. Moreover, a person attacking a smart card must not only possess the card but in the subsections below. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of these are outlined in addition does not allow the PIN back out to...
... card with a PIN. Moreover, a person attacking a smart card must not only possess the card but in the subsections below. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of these are outlined in addition does not allow the PIN back out to...
Wireless Security
Page 9
...to corporate servers. RSA Security did not develop a Pocket PC client, but instead incorporated SecurID into the access device; Software-based firewalls are often not incorporated into the EZOS WAP micro-browser called EzWAP.3 Device-Specific Firewalls Industry best practices dictate the use of a device-...to travel wirelessly between mobile clients and the wired lines that corporate data is not lost if the pass-phrase is forgotten Compaq iPAQ Pocket PC's ship with his or her PIN. Different connection technologies are used at different times, depending on the availability and efficiency...
...to corporate servers. RSA Security did not develop a Pocket PC client, but instead incorporated SecurID into the access device; Software-based firewalls are often not incorporated into the EZOS WAP micro-browser called EzWAP.3 Device-Specific Firewalls Industry best practices dictate the use of a device-...to travel wirelessly between mobile clients and the wired lines that corporate data is not lost if the pass-phrase is forgotten Compaq iPAQ Pocket PC's ship with his or her PIN. Different connection technologies are used at different times, depending on the availability and efficiency...
Wireless Security
Page 11
A WPAN permits personal devices such as handheld PCs to connect wirelessly to support voice transmission for CDMA and TDMA are widely used to peripheral devices such as printers or other personal devices. They can use Bluetooth, a radio frequency (RF) specification for Mobile communication (GSM), developed in Europe, is a TDMA technology. The Global System...
A WPAN permits personal devices such as handheld PCs to connect wirelessly to support voice transmission for CDMA and TDMA are widely used to peripheral devices such as printers or other personal devices. They can use Bluetooth, a radio frequency (RF) specification for Mobile communication (GSM), developed in Europe, is a TDMA technology. The Global System...
Wireless Security
Page 13
... ramifications. Two key technologies make such information unreadable or invisible. Popular PKI vendors like Baltimore Technologies, Inc. and Entrust do not have point solutions to specific applications that run on the various operating systems. Public Key Infrastructure Most approaches to the network technology; In Figure 5 the originator encrypts the data using...
... ramifications. Two key technologies make such information unreadable or invisible. Popular PKI vendors like Baltimore Technologies, Inc. and Entrust do not have point solutions to specific applications that run on the various operating systems. Public Key Infrastructure Most approaches to the network technology; In Figure 5 the originator encrypts the data using...
Wireless Security
Page 19
...obvious weaknesses in the technique. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Will support only Check Point VPN products VGate by V-One: •... hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client directly to application server) Security Specific to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of the algorithms are kept secret....
...obvious weaknesses in the technique. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Will support only Check Point VPN products VGate by V-One: •... hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client directly to application server) Security Specific to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of the algorithms are kept secret....
Wireless Security
Page 20
.... Besides encryption, the IS-95 standard of digital certificates. WAP 1.2 also adds a function that was developed by WWANs have reportedly been cracked. WTLS is designed specifically for WAP applications. The encryption techniques used on standard Internet TLS, and designed so as a result of random or bulk transmissions over a WWAN. WAP 2.0 was...
.... Besides encryption, the IS-95 standard of digital certificates. WAP 1.2 also adds a function that was developed by WWANs have reportedly been cracked. WTLS is designed specifically for WAP applications. The encryption techniques used on standard Internet TLS, and designed so as a result of random or bulk transmissions over a WWAN. WAP 2.0 was...
Wireless Security
Page 21
... GAP" Mobile Device WTLS WAP GATEWAY TLS Web Server WAP GAP ƒ Security protocol must be some time, however, before implementations of convergence with wireless-specific profiles. The wireless transport layer security (WTLS) on end-to -end encryption between the wireless client and the application server. The WAP gateway is based...
... GAP" Mobile Device WTLS WAP GATEWAY TLS Web Server WAP GAP ƒ Security protocol must be some time, however, before implementations of convergence with wireless-specific profiles. The wireless transport layer security (WTLS) on end-to -end encryption between the wireless client and the application server. The WAP gateway is based...
Wireless Security
Page 24
The attacker would need to build working to the wired lines or Internet. Compaq is working versions of WLANs, for example, the Access Point is used to provide data security equivalent to just capture data and analyze... company which could lead to significant duplication of WLAN traffic through eavesdropping. This attack would be the future encryption standard. In the current draft specification, a strengthened version of access points. Wireless Security White Paper 24 Infowave further notes that the engineering effort required to communicate with the attacking server...
The attacker would need to build working to the wired lines or Internet. Compaq is working versions of WLANs, for example, the Access Point is used to provide data security equivalent to just capture data and analyze... company which could lead to significant duplication of WLAN traffic through eavesdropping. This attack would be the future encryption standard. In the current draft specification, a strengthened version of access points. Wireless Security White Paper 24 Infowave further notes that the engineering effort required to communicate with the attacking server...
Wireless Security
Page 27
... longer a need for WEP in an 802.11b LAN. As mentioned above under the section titled "Security Specific to control what outside resources its destination. WWAN Access Points Telecommunications companies are several firewall screening methods. Specific security provided for the carrier itself. A firewall, working for WWAN technologies is focused on conversations and...
... longer a need for WEP in an 802.11b LAN. As mentioned above under the section titled "Security Specific to control what outside resources its destination. WWAN Access Points Telecommunications companies are several firewall screening methods. Specific security provided for the carrier itself. A firewall, working for WWAN technologies is focused on conversations and...
Configuring Compaq Evo Computers for Microsoft Windows 95
Page 3
... the switches by executing AMDK6upd.exe /T:a:\ /C. A batch file can be on Evo platforms. Note: This Windows 95 patch is not AMD processor specific. however, Compaq recognizes that the procedures outlined in Compaq Evo products; For such cases, use this task if it will need to download one... "patch" from the Compaq support websites provided in Step 1. 5. Start the Windows ...
... the switches by executing AMDK6upd.exe /T:a:\ /C. A batch file can be on Evo platforms. Note: This Windows 95 patch is not AMD processor specific. however, Compaq recognizes that the procedures outlined in Compaq Evo products; For such cases, use this task if it will need to download one... "patch" from the Compaq support websites provided in Step 1. 5. Start the Windows ...
Hardware Guide Evo Notebook N600c Series
Page 1
It also includes instructions for using them. b Hardware Guide Evo Notebook N600c Series Document Part Number: 229045-002 November 2001 This guide identifies computer hardware features and provides procedures for setting up the computer, information about connecting external devices, and computer specifications.
It also includes instructions for using them. b Hardware Guide Evo Notebook N600c Series Document Part Number: 229045-002 November 2001 This guide identifies computer hardware features and provides procedures for setting up the computer, information about connecting external devices, and computer specifications.
Hardware Guide Evo Notebook N600c Series
Page 6
... Connecting an Optional Cable Lock 7-11 8 Hardware Upgrades Adding and Using PC Cards 8-1 Selecting a PC Card slot 8-1 Configuring a PC Card 8-2 Inserting a PC Card 8-3 Removing a PC Card 8-4 Turning Off Power to a PC Card 8-5 Upgrading Memory 8-6 Viewing Memory and Hibernation File Information 8-6 Removing or Inserting a Memory Expansion Board 8-7 9 Specifications Regulatory Agency Series Numbers 9-1 Computer Dimensions 9-2 Operating Environment 9-2 Rated Input...
... Connecting an Optional Cable Lock 7-11 8 Hardware Upgrades Adding and Using PC Cards 8-1 Selecting a PC Card slot 8-1 Configuring a PC Card 8-2 Inserting a PC Card 8-3 Removing a PC Card 8-4 Turning Off Power to a PC Card 8-5 Upgrading Memory 8-6 Viewing Memory and Hibernation File Information 8-6 Removing or Inserting a Memory Expansion Board 8-7 9 Specifications Regulatory Agency Series Numbers 9-1 Computer Dimensions 9-2 Operating Environment 9-2 Rated Input...
Hardware Guide Evo Notebook N600c Series
Page 29
... ✎ The network cable has an 8-pin RJ-45 connector at each end. Connects the modem to an RJ-11 telephone jack or to a country-specific modem adapter. ✎ The modem cable has a 6-pin RJ-11 connector at the Computer Additional standard components and their functions 1 Power cord 2 Modem...adapter (included with internal modem models by region as required) 4 Network cable (network models only) 5 AC Adapter 6 Weight saver 7 Japan-specific outlet adapter (Japan only) 8 QuickRestore kit Connects the AC Adapter to a non-RJ-11 telephone jack. Connects the computer to protect the ...
... ✎ The network cable has an 8-pin RJ-45 connector at each end. Connects the modem to an RJ-11 telephone jack or to a country-specific modem adapter. ✎ The modem cable has a 6-pin RJ-11 connector at the Computer Additional standard components and their functions 1 Power cord 2 Modem...adapter (included with internal modem models by region as required) 4 Network cable (network models only) 5 AC Adapter 6 Weight saver 7 Japan-specific outlet adapter (Japan only) 8 QuickRestore kit Connects the AC Adapter to a non-RJ-11 telephone jack. Connects the computer to protect the ...
Hardware Guide Evo Notebook N600c Series
Page 41
Pointing Devices and Keyboard Set Power Conservation Level (Fn+F7) I Windows NT 4.0-Press Fn+F7 to your docking base documentation for specific bay location information. To select a preset battery conservation level, choose among: ❏ High-Maximizes running time from a single charge. ❏...View Battery Charge Information (Fn+F8) Press Fn+F8 to display charge information about the custom level, refer on this CD to the Compaq Utilities guide, "Power Management" section. For information about all installed battery packs. Battery pack locations are charging and reports the amount of ...
Pointing Devices and Keyboard Set Power Conservation Level (Fn+F7) I Windows NT 4.0-Press Fn+F7 to your docking base documentation for specific bay location information. To select a preset battery conservation level, choose among: ❏ High-Maximizes running time from a single charge. ❏...View Battery Charge Information (Fn+F8) Press Fn+F8 to display charge information about the custom level, refer on this CD to the Compaq Utilities guide, "Power Management" section. For information about all installed battery packs. Battery pack locations are charging and reports the amount of ...
Hardware Guide Evo Notebook N600c Series
Page 76
Connecting a modem cable 7-2 Hardware Guide If you are not compatible with the modem. Plug the modem cable into the country-specific modem adapter or into the RJ-45 jack. 3. External Device Connections Connecting a Modem Cable A modem cable, which prevents interference from TV and radio ..., or damage to an analog telephone line. Immediately disconnect an accidental connection to a telephone jack that is not an RJ-11 jack, plug a country-specific modem adapter into the RJ-11 jack on the computer 2. Å WARNING: To reduce the risk of the cable toward the computer. 2. Plug the...
Connecting a modem cable 7-2 Hardware Guide If you are not compatible with the modem. Plug the modem cable into the country-specific modem adapter or into the RJ-45 jack. 3. External Device Connections Connecting a Modem Cable A modem cable, which prevents interference from TV and radio ..., or damage to an analog telephone line. Immediately disconnect an accidental connection to a telephone jack that is not an RJ-11 jack, plug a country-specific modem adapter into the RJ-11 jack on the computer 2. Å WARNING: To reduce the risk of the cable toward the computer. 2. Plug the...
Hardware Guide Evo Notebook N600c Series
Page 86
... can be used only in any combination. Hardware Guide 8-1 Adding and Using PC Cards A PC Card is a credit card-sized accessory designed to conform to the standard specifications of the printed Getting Started guide, included with the computer, to contact a Compaq authorized dealer, reseller, or service provider. 8 Hardware Upgrades To order or learn more...
... can be used only in any combination. Hardware Guide 8-1 Adding and Using PC Cards A PC Card is a credit card-sized accessory designed to conform to the standard specifications of the printed Getting Started guide, included with the computer, to contact a Compaq authorized dealer, reseller, or service provider. 8 Hardware Upgrades To order or learn more...
Hardware Guide Evo Notebook N600c Series
Page 96
Regulatory Agency Series Numbers Regulatory agencies worldwide use the computer only with the limits for product identification. 9 Specifications This computer has been tested and found to Regulatory and Safety Notices. Each approved product displays the assigned agency series number. To ensure continued safe ...
Regulatory Agency Series Numbers Regulatory agencies worldwide use the computer only with the limits for product identification. 9 Specifications This computer has been tested and found to Regulatory and Safety Notices. Each approved product displays the assigned agency series number. To ensure continued safe ...
Hardware Guide Evo Notebook N600c Series
Page 97
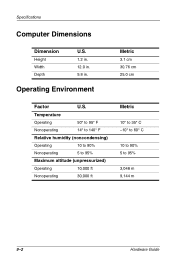
Temperature Operating 50° to 95° F Nonoperating 14° to 140° F Relative humidity (noncondensing) Operating 10 to 90% Nonoperating 5 to 95% Maximum altitude (unpressurized) Operating 10,000 ft Nonoperating 30,000 ft Metric 10° to 35° C -10° to 60° C 10 to 90% 5 to 95% 3,048 m 9,144 m 9-2 Hardware Guide Operating Environment Metric 3.1 cm 30.76 cm 25.0 cm Factor U.S. Specifications Computer Dimensions Dimension Height Width Depth U.S. 1.2 in. 12.0 in. 9.8 in.
Temperature Operating 50° to 95° F Nonoperating 14° to 140° F Relative humidity (noncondensing) Operating 10 to 90% Nonoperating 5 to 95% Maximum altitude (unpressurized) Operating 10,000 ft Nonoperating 30,000 ft Metric 10° to 35° C -10° to 60° C 10 to 90% 5 to 95% 3,048 m 9,144 m 9-2 Hardware Guide Operating Environment Metric 3.1 cm 30.76 cm 25.0 cm Factor U.S. Specifications Computer Dimensions Dimension Height Width Depth U.S. 1.2 in. 12.0 in. 9.8 in.