Wireless Security
Page 3
...where the security vulnerabilities lie and what can be done to improve security. This ability to Assure E-Business Success" (http://activeanswers.compaq.com/ActiveAnswers/Render/1,1027,1317-6-100-225-1,00.html February, 2000) for important detail on best practices and established technologies for wired... access to sensitive data. Users and corporations are concerned. This is so in part because many users are not aware of specific security vulnerabilities or don't understand the magnitude of wireless-enabled productivity to take advantage of the benefits of potential loss and, ...
...where the security vulnerabilities lie and what can be done to improve security. This ability to Assure E-Business Success" (http://activeanswers.compaq.com/ActiveAnswers/Render/1,1027,1317-6-100-225-1,00.html February, 2000) for important detail on best practices and established technologies for wired... access to sensitive data. Users and corporations are concerned. This is so in part because many users are not aware of specific security vulnerabilities or don't understand the magnitude of wireless-enabled productivity to take advantage of the benefits of potential loss and, ...
Wireless Security
Page 6
...in managing individually owned handheld mobile devices and their employees. They may view confidential information stored on Compaq handheld devices, see http://www.compaq.com/showroom/notebooks.html. Often firewalls are more susceptible to loss and theft than desktop devices, which makes it harder... specific to their rate of propagation causes them home at the end of applications in real time. Because of their usefulness, companies deploy millions of notebook computers to mobile access devices, the first link in the pipe on Compaq notebook computers, see http://www.compaq.com...
...in managing individually owned handheld mobile devices and their employees. They may view confidential information stored on Compaq handheld devices, see http://www.compaq.com/showroom/notebooks.html. Often firewalls are more susceptible to loss and theft than desktop devices, which makes it harder... specific to their rate of propagation causes them home at the end of applications in real time. Because of their usefulness, companies deploy millions of notebook computers to mobile access devices, the first link in the pipe on Compaq notebook computers, see http://www.compaq.com...
Wireless Security
Page 7
... main types of smart cards: contact and contactless. The smart card is most effective when paired with the card. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are connected to an integrated circuit sandwiched between layers of plastic inside the card. Users often choose passwords that intruders...
... main types of smart cards: contact and contactless. The smart card is most effective when paired with the card. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are connected to an integrated circuit sandwiched between layers of plastic inside the card. Users often choose passwords that intruders...
Wireless Security
Page 9
...8226; Automatic encryption at power-off • Key recovery ensures that corporate data is not lost if the pass-phrase is forgotten Compaq iPAQ Pocket PC's ship with his or her PIN. The user's login password combines the SecurID code with F-Secure today. RSA Security did not...device to produce a secure user login. Software-based firewalls are often not incorporated into the EZOS WAP micro-browser called EzWAP.3 Device-Specific Firewalls Industry best practices dictate the use of a device-mounted firewall when connecting to the Internet, especially through lack of a corporate ...
...8226; Automatic encryption at power-off • Key recovery ensures that corporate data is not lost if the pass-phrase is forgotten Compaq iPAQ Pocket PC's ship with his or her PIN. The user's login password combines the SecurID code with F-Secure today. RSA Security did not...device to produce a secure user login. Software-based firewalls are often not incorporated into the EZOS WAP micro-browser called EzWAP.3 Device-Specific Firewalls Industry best practices dictate the use of a device-mounted firewall when connecting to the Internet, especially through lack of a corporate ...
Wireless Security
Page 11
A WPAN permits personal devices such as handheld PCs to connect wirelessly to support voice transmission for CDMA and TDMA are widely used there. Figure 3 illustrates a WPAN. Code Division Multiple Access (CDMA) and Time ... Historically, wireless wide-area networks (WWANs) have been used of three digital wireless telephone technologies: GSM, CDMA, and TDMA. WWANs use Bluetooth, a radio frequency (RF) specification for Mobile communication (GSM), developed in its market. They can use one of the three digital wireless telephone technologies.
A WPAN permits personal devices such as handheld PCs to connect wirelessly to support voice transmission for CDMA and TDMA are widely used there. Figure 3 illustrates a WPAN. Code Division Multiple Access (CDMA) and Time ... Historically, wireless wide-area networks (WWANs) have been used of three digital wireless telephone technologies: GSM, CDMA, and TDMA. WWANs use Bluetooth, a radio frequency (RF) specification for Mobile communication (GSM), developed in its market. They can use one of the three digital wireless telephone technologies.
Wireless Security
Page 13
... understanding that run on the various operating systems. Public Key Infrastructure Most approaches to the network technology; and Entrust do not have point solutions to specific applications that , as a public key infrastructure (PKI). Figure 5: Basics of public key cryptography, also known as public key encryption. Those technologies are the most secure...
... understanding that run on the various operating systems. Public Key Infrastructure Most approaches to the network technology; and Entrust do not have point solutions to specific applications that , as a public key infrastructure (PKI). Figure 5: Basics of public key cryptography, also known as public key encryption. Those technologies are the most secure...
Wireless Security
Page 19
...-know, such as carriers and handset manufacturers. The smart card contains both voice and data are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE • Connects to back-end VPN ...remote hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client directly to application server) Security Specific to authenticate the mobile participant and generate a session key. Most security specialists will argue that secrecy is not an effective approach, since...
...-know, such as carriers and handset manufacturers. The smart card contains both voice and data are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE • Connects to back-end VPN ...remote hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client directly to application server) Security Specific to authenticate the mobile participant and generate a session key. Most security specialists will argue that secrecy is not an effective approach, since...
Wireless Security
Page 20
...algorithms have . (Conventional wireless signals do not change frequency except for small, rapid fluctuations that was developed to solve problems specific to mobile network devices, including their effectiveness lies in June 2001 and adds support for Wireless Public Key Infrastructure (WPKI) ...CMEA) specified by the military with which authenticate a WTLS client to a WTLS server. Wireless Transport Layer Security (WTLS) is designed specifically for WTLS client certificates, which to provide a basis for non-repudiation. WTLS is based on standard Internet TLS, and designed so as...
...algorithms have . (Conventional wireless signals do not change frequency except for small, rapid fluctuations that was developed to solve problems specific to mobile network devices, including their effectiveness lies in June 2001 and adds support for Wireless Public Key Infrastructure (WPKI) ...CMEA) specified by the military with which authenticate a WTLS client to a WTLS server. Wireless Transport Layer Security (WTLS) is designed specifically for WTLS client certificates, which to provide a basis for non-repudiation. WTLS is based on standard Internet TLS, and designed so as...
Wireless Security
Page 21
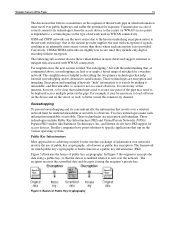
... not change rather than on end-to -end encryption between the wireless client and the application server. The newest ratified version of convergence with wireless-specific profiles. It may appear first on the PocketPC rather than new hardware. This characteristic is effectively a profile of time Figure 10: Wireless Access Protocol (WAP...
... not change rather than on end-to -end encryption between the wireless client and the application server. The newest ratified version of convergence with wireless-specific profiles. It may appear first on the PocketPC rather than new hardware. This characteristic is effectively a profile of time Figure 10: Wireless Access Protocol (WAP...
Wireless Security
Page 24
...an optional IEEE 802.11b feature used to authenticate user access to any authentication database (EAP RADIUS server). In the current draft specification, a strengthened version of both the IStack transport layer (Infowave proprietary) and the WBE authentication and session protocols (also Infowave ... fully secure solution will be remedied in 2001 will permit authentication to any closed network. Compaq is prohibitive. The 801.11i standard ratified in IEEE extensions to the WEP specification that of hardware, a hub, which enters the corporate data network and/or the Internet....
...an optional IEEE 802.11b feature used to authenticate user access to any authentication database (EAP RADIUS server). In the current draft specification, a strengthened version of both the IStack transport layer (Infowave proprietary) and the WBE authentication and session protocols (also Infowave ... fully secure solution will be remedied in 2001 will permit authentication to any closed network. Compaq is prohibitive. The 801.11i standard ratified in IEEE extensions to the WEP specification that of hardware, a hub, which enters the corporate data network and/or the Internet....
Wireless Security
Page 27
...users from accessing its own private data resources and to WWAN Carrier Technologies." As mentioned above under the section titled "Security Specific to control what outside resources its destination. The ideal combination is to make firewall products. Features include logging and reporting,...WWAN technologies is to screen requests to use 802.1x for the carrier itself. however, it to eavesdrop on wireless security. Specific security provided for controlling the firewall. A firewall also includes or works with a router program, examines each network packet to ...
...users from accessing its own private data resources and to WWAN Carrier Technologies." As mentioned above under the section titled "Security Specific to control what outside resources its destination. The ideal combination is to make firewall products. Features include logging and reporting,...WWAN technologies is to screen requests to use 802.1x for the carrier itself. however, it to eavesdrop on wireless security. Specific security provided for controlling the firewall. A firewall also includes or works with a router program, examines each network packet to ...
Configuring Compaq Evo Computers for Microsoft Windows 95
Page 3
...today. This paper describes the procedures and files required to allow Evo computer systems to function with the AMD K6 processor. Configuring Compaq Evo for Microsoft Windows 95 White Paper 3 Introduction Compaq does not officially support Microsoft Windows 95 Operating System (Windows 95...their Windows 95-based software. A batch file can be followed on Evo platforms. Note: This Windows 95 patch is not AMD processor specific. Download AMDK6upd.exe from the Compaq support websites provided in Compaq Evo products; Document the switches by executing AMDK6upd.exe /T:a:\ /C. As a...
...today. This paper describes the procedures and files required to allow Evo computer systems to function with the AMD K6 processor. Configuring Compaq Evo for Microsoft Windows 95 White Paper 3 Introduction Compaq does not officially support Microsoft Windows 95 Operating System (Windows 95...their Windows 95-based software. A batch file can be followed on Evo platforms. Note: This Windows 95 patch is not AMD processor specific. Download AMDK6upd.exe from the Compaq support websites provided in Compaq Evo products; Document the switches by executing AMDK6upd.exe /T:a:\ /C. As a...
Hardware Guide Evo Notebook N600c Series
Page 1
b Hardware Guide Evo Notebook N600c Series Document Part Number: 229045-002 November 2001 This guide identifies computer hardware features and provides procedures for setting up the computer, information about connecting external devices, and computer specifications. It also includes instructions for using them.
b Hardware Guide Evo Notebook N600c Series Document Part Number: 229045-002 November 2001 This guide identifies computer hardware features and provides procedures for setting up the computer, information about connecting external devices, and computer specifications. It also includes instructions for using them.
Hardware Guide Evo Notebook N600c Series
Page 6
... Connecting an Optional Cable Lock 7-11 8 Hardware Upgrades Adding and Using PC Cards 8-1 Selecting a PC Card slot 8-1 Configuring a PC Card 8-2 Inserting a PC Card 8-3 Removing a PC Card 8-4 Turning Off Power to a PC Card 8-5 Upgrading Memory 8-6 Viewing Memory and Hibernation File Information 8-6 Removing or Inserting a Memory Expansion Board 8-7 9 Specifications Regulatory Agency Series Numbers 9-1 Computer Dimensions 9-2 Operating Environment 9-2 Rated Input...
... Connecting an Optional Cable Lock 7-11 8 Hardware Upgrades Adding and Using PC Cards 8-1 Selecting a PC Card slot 8-1 Configuring a PC Card 8-2 Inserting a PC Card 8-3 Removing a PC Card 8-4 Turning Off Power to a PC Card 8-5 Upgrading Memory 8-6 Viewing Memory and Hibernation File Information 8-6 Removing or Inserting a Memory Expansion Board 8-7 9 Specifications Regulatory Agency Series Numbers 9-1 Computer Dimensions 9-2 Operating Environment 9-2 Rated Input...
Hardware Guide Evo Notebook N600c Series
Page 29
...or to an Ethernet network jack. ✎ The network cable has an 8-pin RJ-45 connector at each end. Connects the computer to a country-specific modem adapter. ✎ The modem cable has a 6-pin RJ-11 connector at each end. Converts AC power to an AC electrical outlet. A ...Look at the Computer Additional standard components and their functions 1 Power cord 2 Modem cable (internal modem models only) 3 Country-specific modem adapter (included with internal modem models by region as required) 4 Network cable (network models only) 5 AC Adapter 6 Weight saver 7 Japan...
...or to an Ethernet network jack. ✎ The network cable has an 8-pin RJ-45 connector at each end. Connects the computer to a country-specific modem adapter. ✎ The modem cable has a 6-pin RJ-11 connector at each end. Converts AC power to an AC electrical outlet. A ...Look at the Computer Additional standard components and their functions 1 Power cord 2 Modem cable (internal modem models only) 3 Country-specific modem adapter (included with internal modem models by region as required) 4 Network cable (network models only) 5 AC Adapter 6 Weight saver 7 Japan...
Hardware Guide Evo Notebook N600c Series
Page 41
...display indicates which vary by number: (1) is the computer battery bay and (2) is the computer MultiBay. Refer to your docking base documentation for specific bay location information. To select a preset battery conservation level, choose among: ❏ High-Maximizes running time from a single charge. ❏...Battery Charge Information (Fn+F8) Press Fn+F8 to display charge information about the custom level, refer on this CD to the Compaq Utilities guide, "Power Management" section. Battery pack locations are charging and reports the amount of charge remaining in each battery pack. ...
...display indicates which vary by number: (1) is the computer battery bay and (2) is the computer MultiBay. Refer to your docking base documentation for specific bay location information. To select a preset battery conservation level, choose among: ❏ High-Maximizes running time from a single charge. ❏...Battery Charge Information (Fn+F8) Press Fn+F8 to display charge information about the custom level, refer on this CD to the Compaq Utilities guide, "Power Management" section. Battery pack locations are charging and reports the amount of charge remaining in each battery pack. ...
Hardware Guide Evo Notebook N600c Series
Page 76
Plug the modem cable into the country-specific modem adapter or into the RJ-45 jack. 3. If the modem cable contains noise suppression circuitry 1, which has a 6-pin RJ-11 connector at each end, ... and radio reception, orient the circuitry end of electrical shock, fire, or damage to a telephone jack that is not an RJ-11 jack, plug a country-specific modem adapter into the telephone jack 3. 4.
Plug the modem cable into the country-specific modem adapter or into the RJ-45 jack. 3. If the modem cable contains noise suppression circuitry 1, which has a 6-pin RJ-11 connector at each end, ... and radio reception, orient the circuitry end of electrical shock, fire, or damage to a telephone jack that is not an RJ-11 jack, plug a country-specific modem adapter into the telephone jack 3. 4.
Hardware Guide Evo Notebook N600c Series
Page 86
... learn more about hardware upgrades and accessories, visit the Compaq Web site at http://www.compaq.com, or refer to Worldwide Telephone Numbers, included with the computer. Adding and Using PC Cards A PC Card is a credit card-sized accessory designed to conform to the standard specifications of this CD to the Maintenance, Shipping and Travel...
... learn more about hardware upgrades and accessories, visit the Compaq Web site at http://www.compaq.com, or refer to Worldwide Telephone Numbers, included with the computer. Adding and Using PC Cards A PC Card is a credit card-sized accessory designed to conform to the standard specifications of this CD to the Maintenance, Shipping and Travel...
Hardware Guide Evo Notebook N600c Series
Page 96
9 Specifications This computer has been tested and found to Regulatory and Safety Notices. To ensure continued safe and reliable operation, use agency series numbers for a Class B ...
9 Specifications This computer has been tested and found to Regulatory and Safety Notices. To ensure continued safe and reliable operation, use agency series numbers for a Class B ...
Hardware Guide Evo Notebook N600c Series
Page 97
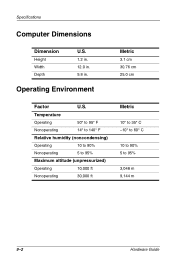
Operating Environment Metric 3.1 cm 30.76 cm 25.0 cm Factor U.S. Specifications Computer Dimensions Dimension Height Width Depth U.S. 1.2 in. 12.0 in. 9.8 in. Temperature Operating 50° to 95° F Nonoperating 14° to 140° F Relative humidity (noncondensing) Operating 10 to 90% Nonoperating 5 to 95% Maximum altitude (unpressurized) Operating 10,000 ft Nonoperating 30,000 ft Metric 10° to 35° C -10° to 60° C 10 to 90% 5 to 95% 3,048 m 9,144 m 9-2 Hardware Guide
Operating Environment Metric 3.1 cm 30.76 cm 25.0 cm Factor U.S. Specifications Computer Dimensions Dimension Height Width Depth U.S. 1.2 in. 12.0 in. 9.8 in. Temperature Operating 50° to 95° F Nonoperating 14° to 140° F Relative humidity (noncondensing) Operating 10 to 90% Nonoperating 5 to 95% Maximum altitude (unpressurized) Operating 10,000 ft Nonoperating 30,000 ft Metric 10° to 35° C -10° to 60° C 10 to 90% 5 to 95% 3,048 m 9,144 m 9-2 Hardware Guide