Command Line Interface Guide
Page 29
... QoS services configuration mode. • MAC Access-List- b Set Flow Control to manually specify other device SSH public keys. d Select Terminal keys for use on the console line only. Using the device command-line interface (CLI) is 115,200 (Console port on Windows 2000 service packs. Configures conditions required to entering commands on MAC addresses. c Under Properties, select VT100 for Ryan, is very similar to allow traffic based on a UNIX system. Starting the CLI The device can be managed over cable to the RS-232 serial port...
... QoS services configuration mode. • MAC Access-List- b Set Flow Control to manually specify other device SSH public keys. d Select Terminal keys for use on the console line only. Using the device command-line interface (CLI) is 115,200 (Console port on Windows 2000 service packs. Configures conditions required to entering commands on MAC addresses. c Under Properties, select VT100 for Ryan, is very similar to allow traffic based on a UNIX system. Starting the CLI The device can be managed over cable to the RS-232 serial port...
Command Line Interface Guide
Page 41
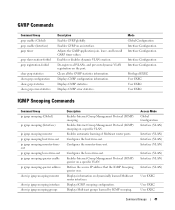
... on the port. Access Mode Global Configuration Interface (VLAN) Interface (VLAN) Interface (VLAN) Interface (VLAN) Interface (VLAN) Interface (VLAN) Interface (VLAN) User EXEC User EXEC User EXEC Command Groups 41 Displays GVRP error statistics. Configures the host-time-out. Enables or disables dynamic VLAN creation. Clears all VLANs, and prevents dynamic VLAN registration on dynamically learned Multicast router interfaces. Displays IGMP snooping configuration. Enables Internet Group Management Protocol (IGMP) snooping on a specific VLAN. GVRP Commands Command Group...
... on the port. Access Mode Global Configuration Interface (VLAN) Interface (VLAN) Interface (VLAN) Interface (VLAN) Interface (VLAN) Interface (VLAN) Interface (VLAN) User EXEC User EXEC User EXEC Command Groups 41 Displays GVRP error statistics. Configures the host-time-out. Enables or disables dynamic VLAN creation. Clears all VLANs, and prevents dynamic VLAN registration on dynamically learned Multicast router interfaces. Displays IGMP snooping configuration. Enables Internet Group Management Protocol (IGMP) snooping on a specific VLAN. GVRP Commands Command Group...
Command Line Interface Guide
Page 64
... multiple portchannels. Sets an IP address. Globally enables DHCP snooping. Enters the interface configuration mode to the previous command mode. Creates Layer 2 ACLs. Configures a switch to accept DHCP packets with option-82 information from an untrusted port. enable password end file-system logging gvrp enable (Global) hostname interface ethernet interface port-channel interface range ethernet interface range port-channel interface range vlan interface vlan ip access-list ip access-list ip address ip default-gateway ip dhcp snooping ip dhcp snooping database ip dhcp...
... multiple portchannels. Sets an IP address. Globally enables DHCP snooping. Enters the interface configuration mode to the previous command mode. Creates Layer 2 ACLs. Configures a switch to accept DHCP packets with option-82 information from an untrusted port. enable password end file-system logging gvrp enable (Global) hostname interface ethernet interface port-channel interface range ethernet interface range port-channel interface range vlan interface vlan ip access-list ip access-list ip address ip default-gateway ip dhcp snooping ip dhcp snooping database ip dhcp...
Command Line Interface Guide
Page 65
... ip ssh port ip ssh pubkey-auth ip ssh server lacp system-priority line logging logging buffered logging buffered size logging console logging file logging on mac access-list management access-class management access-list management logging password min-length Specifies authentication methods for HTTPS. Logs messages to be configured from a SSH server. Command Modes 65 Controls error messages logging. Sets the interval the system waits for configuration. Enables Internet Group Management Protocol (IGMP) snooping. Defines a management access-list, and enters the access-list for user...
... ip ssh port ip ssh pubkey-auth ip ssh server lacp system-priority line logging logging buffered logging buffered size logging console logging file logging on mac access-list management access-class management access-list management logging password min-length Specifies authentication methods for HTTPS. Logs messages to be configured from a SSH server. Command Modes 65 Controls error messages logging. Sets the interval the system waits for configuration. Enables Internet Group Management Protocol (IGMP) snooping. Defines a management access-list, and enters the access-list for user...
Command Line Interface Guide
Page 66
... powered device type attached to be reused. Enables Quality of failed login attempts before a password in the local database. Modifies the DSCP to SNMP protocol. 66 Command Modes Configure the system to reply. Specifies the source IPv6 address used for a server host to "trust" state. Sets the interval for which a device waits for communication with RADIUS servers. Configures alarm conditions. Sets the number of Service (QoS) on an interface. Improves RADIUS response times when servers...
... powered device type attached to be reused. Enables Quality of failed login attempts before a password in the local database. Modifies the DSCP to SNMP protocol. 66 Command Modes Configure the system to reply. Specifies the source IPv6 address used for a server host to "trust" state. Sets the interval for which a device waits for communication with RADIUS servers. Configures alarm conditions. Sets the number of Service (QoS) on an interface. Improves RADIUS response times when servers...
Command Line Interface Guide
Page 78
...snooping (Interface) Enables Internet Group Management Protocol (IGMP) snooping on the network. bridge multicast forbidden forward-all Forbids a port from becoming a forward-all Multicast frames on a port. Displays the service id information. Enables the command history function for the current terminal session. VC (VLAN Configuration) Mode Command Group Description bridge address Adds a static MAC-layer station source address to that packets will actually take when traveling to specific ports. dot1x auth-not-req Enables unauthorized users access to the bridge table...
...snooping (Interface) Enables Internet Group Management Protocol (IGMP) snooping on the network. bridge multicast forbidden forward-all Forbids a port from becoming a forward-all Multicast frames on a port. Displays the service id information. Enables the command history function for the current terminal session. VC (VLAN Configuration) Mode Command Group Description bridge address Adds a static MAC-layer station source address to that packets will actually take when traveling to specific ports. dot1x auth-not-req Enables unauthorized users access to the bridge table...
Command Line Interface Guide
Page 101
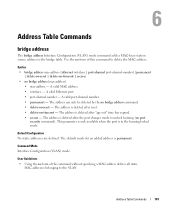
... static addresses are defined. Address Table Commands 101 Address Table Commands bridge address The bridge address Interface Configuration (VLAN) mode command adds a MAC-layer station source address to delete the MAC address. A valid port-channel number. • permanent - The address is deleted after "age out" time has expired. • secure - User Guidelines • Using the no form of the command without specifying a MAC address deletes all static MAC addresses belonging to this command to the bridge table. Use the no form of this VLAN. A valid Ethernet port. • port...
... static addresses are defined. Address Table Commands 101 Address Table Commands bridge address The bridge address Interface Configuration (VLAN) mode command adds a MAC-layer station source address to delete the MAC address. A valid port-channel number. • permanent - The address is deleted after "age out" time has expired. • secure - User Guidelines • Using the no form of the command without specifying a MAC address deletes all static MAC addresses belonging to this command to the bridge table. Use the no form of this VLAN. A valid Ethernet port. • port...
Command Line Interface Guide
Page 106
...used to be a forward-all Multicast packets on port 1/e8. Use the no spaces; Separate non-consecutive port-channels with a comma and no form of this command. number-list} • no spaces; User Guidelines There are no user guidelines for this command to designate a range of ports. • port-channel-number-list - Force forwarding all {add | remove} {ethernet interface-list | port-channel port-channel- Default Configuration This setting is used to restore the default configuration. 106 Address Table Commands Syntax • bridge multicast forward-all Multicast packets...
...used to be a forward-all Multicast packets on port 1/e8. Use the no spaces; Separate non-consecutive port-channels with a comma and no form of this command. number-list} • no spaces; User Guidelines There are no user guidelines for this command to designate a range of ports. • port-channel-number-list - Force forwarding all {add | remove} {ethernet interface-list | port-channel port-channel- Default Configuration This setting is used to restore the default configuration. 106 Address Table Commands Syntax • bridge multicast forward-all Multicast packets...
Command Line Interface Guide
Page 340
... example attaches a group called user-group to SNMPv3 and assigns to the group the privacy security level and read user-view snmp-server user The snmp-server user Global Configuration mode command configures a new SNMP Version 3 user. The user should be entered; The user should enter a password for privacy. (Range: 1 - 32 characters) • auth-md5-key md5-des-keys - The user should enter a concatenated hexadecimal string of a DES key for authentication and generation of this command to remove a user...
... example attaches a group called user-group to SNMPv3 and assigns to the group the privacy security level and read user-view snmp-server user The snmp-server user Global Configuration mode command configures a new SNMP Version 3 user. The user should be entered; The user should enter a password for privacy. (Range: 1 - 32 characters) • auth-md5-key md5-des-keys - The user should enter a concatenated hexadecimal string of a DES key for authentication and generation of this command to remove a user...
Command Line Interface Guide
Page 423
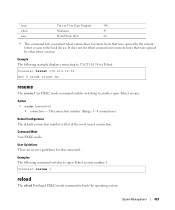
... • connection - System Management 423 The connection number. (Range: 1 - 4 connections) Default Configuration The default connection number is that of the most recent connection. It does not list telnet connections to remote hosts that were opened by other telnet sessions. Example The following command switches to open Telnet session. Console> telnet 176.213.10.50 Esc U sends telnet EL resume The resume User EXEC mode command enables switching to another open Telnet session number 1. Command Mode User EXEC mode. Examples The following example displays connecting to 176...
... • connection - System Management 423 The connection number. (Range: 1 - 4 connections) Default Configuration The default connection number is that of the most recent connection. It does not list telnet connections to remote hosts that were opened by other telnet sessions. Example The following command switches to open Telnet session. Console> telnet 176.213.10.50 Esc U sends telnet EL resume The resume User EXEC mode command enables switching to another open Telnet session number 1. Command Mode User EXEC mode. Examples The following example displays connecting to 176...
User's Guide
Page 26
... CLI Documentation The CLI Reference Guide, which is a protocol that is currently supported. SSH Secure Shell (SSH) is available on the Documentation CD, provides information about the command description, syntax, default values, guidelines, and examples. 26 Introduction For more information, see "Configuring DHCP Snooping" on page 276. SSH version 2 is similar to a device. This connection provides functionality that provides a secure, remote connection to an inbound telnet connection. For more information on Password Management, see "ACL...
... CLI Documentation The CLI Reference Guide, which is a protocol that is currently supported. SSH Secure Shell (SSH) is available on the Documentation CD, provides information about the command description, syntax, default values, guidelines, and examples. 26 Introduction For more information, see "Configuring DHCP Snooping" on page 276. SSH version 2 is similar to a device. This connection provides functionality that provides a secure, remote connection to an inbound telnet connection. For more information on Password Management, see "ACL...
User's Guide
Page 54
... and default gateway. The following example, the commands are based on the Authentication, Authorization, and Accounting (AAA) mechanism, and includes the following commands to a subnet that has a DHCP server on it, in the configuration file, but the IP address is displayed: Configuring SNMP management interface Configuring user account...... Retrieving an IP Address From a DHCP Server When using Dell Easy Setup Wizard. Enter [Y] to retrieve an IP address, the device acts as a DHCP client. Configuring IP...
... and default gateway. The following example, the commands are based on the Authentication, Authorization, and Accounting (AAA) mechanism, and includes the following commands to a subnet that has a DHCP server on it, in the configuration file, but the IP address is displayed: Configuring SNMP management interface Configuring user account...... Retrieving an IP Address From a DHCP Server When using Dell Easy Setup Wizard. Enter [Y] to retrieve an IP address, the device acts as a DHCP client. Configuring IP...
User's Guide
Page 276
... page. channel port-channel-number} The following table summarizes the equivalent CLI commands for specific ingress ports. Port Security CLI Commands CLI Command Description shutdown Disables interfaces. Displays port lock status. port security [forward | discard | discardshutdown] [trap seconds] Locks learning of the CLI commands: console # show ports security {ethernet interface | port- Frequency --------100 Counter -------88 - - ACL Overview Access Control Lists (ACL) allow network managers to channel port-channel-number} port security reasons. set interface active...
... page. channel port-channel-number} The following table summarizes the equivalent CLI commands for specific ingress ports. Port Security CLI Commands CLI Command Description shutdown Disables interfaces. Displays port lock status. port security [forward | discard | discardshutdown] [trap seconds] Locks learning of the CLI commands: console # show ports security {ethernet interface | port- Frequency --------100 Counter -------88 - - ACL Overview Access Control Lists (ACL) allow network managers to channel port-channel-number} port security reasons. set interface active...
User's Guide
Page 278
... Gateway Protocol (IGP). Allows for variable-length subnet mask, and supports multiple network layer protocols. - User Datagram Protocol (UDP). Communication protocol that they want to receive transmissions assigned to a packet based on a specific protocol. HMP - Host Mapping Protocol (HMP). HMP monitors hosts spread over the network. - Remote Desktop Protocol (RDP). Matches the packet to report a processing error. - IPV6 - Matches the packet to the IPV6 Route...
... Gateway Protocol (IGP). Allows for variable-length subnet mask, and supports multiple network layer protocols. - User Datagram Protocol (UDP). Communication protocol that they want to receive transmissions assigned to a packet based on a specific protocol. HMP - Host Mapping Protocol (HMP). HMP monitors hosts spread over the network. - Remote Desktop Protocol (RDP). Matches the packet to report a processing error. - IPV6 - Matches the packet to the IPV6 Route...
User's Guide
Page 288
... end-users or DHCP Servers and untrusted interfaces located beyond the network firewall. By enabling DHCP Snooping network administrators can differentiate between untrusted interfaces and DHCP servers. Trusted interfaces receive packets only from untrusted packets. Interfaces are untrusted if the packet is an example of some of this command. Table 7-7. The DHCP section contains the following table summarizes the equivalent CLI commands for configuring ACL Bindings. The DHCP Snooping Table contains the untrusted interfaces' MAC address, IP address, Lease Time, VLAN ID...
... end-users or DHCP Servers and untrusted interfaces located beyond the network firewall. By enabling DHCP Snooping network administrators can differentiate between untrusted interfaces and DHCP servers. Trusted interfaces receive packets only from untrusted packets. Interfaces are untrusted if the packet is an example of some of this command. Table 7-7. The DHCP section contains the following table summarizes the equivalent CLI commands for configuring ACL Bindings. The DHCP Snooping Table contains the untrusted interfaces' MAC address, IP address, Lease Time, VLAN ID...
User's Guide
Page 387
... traffic - To open the Multicast Support page, click Switch → Multicast Support in the tree view. The CPU analyzes the incoming packets and determines: • Which ports want to interfaces. Forwards Layer 2 Multicast packets. Forwards Layer 2 packets to join which Multicast groups. • Which ports have Multicast routers generating IGMP queries. • What routing protocols are forwarded to the CPU. Multicast forwarding filters enable forwarding of the CLI commands: console(config)# interface ethernet 1/e11 console(config-if)# channel-group 1 mode on Multicast Forwarding...
... traffic - To open the Multicast Support page, click Switch → Multicast Support in the tree view. The CPU analyzes the incoming packets and determines: • Which ports want to interfaces. Forwards Layer 2 Multicast packets. Forwards Layer 2 packets to join which Multicast groups. • Which ports have Multicast routers generating IGMP queries. • What routing protocols are forwarded to the CPU. Multicast forwarding filters enable forwarding of the CLI commands: console(config)# interface ethernet 1/e11 console(config-if)# channel-group 1 mode on Multicast Forwarding...
User's Guide
Page 453
... IP subnets ACL Access Control List. Asset Tag Specifies the user-defined switch module reference. ARP Address Resolution Protocol. Access to management functions can be limited to user groups, which are defined by which that converts IP addresses into a single aggregated VLAN. Aggregated VLAN Groups several VLANs into physical addresses. A custom chip designed for nodes located on different sub-VLANs belonging to ARP requests for a specific application. Routers respond with their MAC address. A protocol that enables login to...
... IP subnets ACL Access Control List. Asset Tag Specifies the user-defined switch module reference. ARP Address Resolution Protocol. Access to management functions can be limited to user groups, which are defined by which that converts IP addresses into a single aggregated VLAN. Aggregated VLAN Groups several VLANs into physical addresses. A custom chip designed for nodes located on different sub-VLANs belonging to ARP requests for a specific application. Routers respond with their MAC address. A protocol that enables login to...
Getting Started Guide
Page 19
... RAM. You can skip using CLI. Consult the PowerConnect 3500 Series User's Guide for configuring the default route. The Setup Wizard configures the following assumptions: • The PowerConnect device was never configured before and is in configuring the device using the setup wizard and configure the switch manually through the Console port. Initial Configuration NOTE: Before proceeding, read the release notes for the first time or if the configuration file is empty because the device...
... RAM. You can skip using CLI. Consult the PowerConnect 3500 Series User's Guide for configuring the default route. The Setup Wizard configures the following assumptions: • The PowerConnect device was never configured before and is in configuring the device using the setup wizard and configure the switch manually through the Console port. Initial Configuration NOTE: Before proceeding, read the release notes for the first time or if the configuration file is empty because the device...
Getting Started Guide
Page 21
... you use to access the CLI, Web interface, or SNMP interface for example 192.168.1.10. For more information on the default VLAN (VLAN #1), of which all ports are not identical. This is defined on setting up user accounts and changing privilege levels, see the user documentation. To setup an IP address: Please enter the IP address of the Management System (A.B.C.D) or wildcard (0.0.0.0) to manage from any Management Station, for the switch. To add a management station...
... you use to access the CLI, Web interface, or SNMP interface for example 192.168.1.10. For more information on the default VLAN (VLAN #1), of which all ports are not identical. This is defined on setting up user accounts and changing privilege levels, see the user documentation. To setup an IP address: Please enter the IP address of the Management System (A.B.C.D) or wildcard (0.0.0.0) to manage from any Management Station, for the switch. To add a management station...
Getting Started Guide
Page 195
... 193 To manage the switch using SNMP (required for SNMP management by default. To add a management station: Please enter the SNMP community string to be used to login to change privilege levels later. Naciśnij [T], aby kontynuować pracę z kreatorem konfiguracji. This account is not setup for Dell Network Manager) you can use Dell Network Manager or other accounts and change this account. You may setup other management interfaces to the CLI and Web interface. Naci...
... 193 To manage the switch using SNMP (required for SNMP management by default. To add a management station: Please enter the SNMP community string to be used to login to change privilege levels later. Naciśnij [T], aby kontynuować pracę z kreatorem konfiguracji. This account is not setup for Dell Network Manager) you can use Dell Network Manager or other accounts and change this account. You may setup other management interfaces to the CLI and Web interface. Naci...