User Guide
Page 3
... time interval. 17 Storm Constrain Display, create, modify, and remove the port traffic threshold, and display or set the interval for logged-in users. 6 System Time Display and configure the system date and time. 7 Log Management Clear system logs, display and configure the loghost, display and refresh system logs. Restore the factory default settings. Display the electronic label of the device. Generate diagnostic information file, and view or save the file to local host. 10 File Management Manage files on...
... time interval. 17 Storm Constrain Display, create, modify, and remove the port traffic threshold, and display or set the interval for logged-in users. 6 System Time Display and configure the system date and time. 7 Log Management Clear system logs, display and configure the loghost, display and refresh system logs. Restore the factory default settings. Display the electronic label of the device. Generate diagnostic information file, and view or save the file to local host. 10 File Management Manage files on...
User Guide
Page 4
... 19 Energy Saving 20 SNMP 21 Interface Statistics 22 VLAN 23 VLAN Interface 24 Voice VLAN 25 MAC Address 26 MSTP 27 Link Aggregation and LACP 28 LLDP 29 IGMP Snooping 30 Routing 31 DHCP 32 Service Management 33 Diagnostic Tools 34 ARP 35 802.1X 36 AAA 37 RADIUS 38 User 39 PKI 40 Port Isolation Group 41 Authorized IP 42 ACL-QoS 43 PoE Contents Configure RMON, and dissplay, create, modify, and clear RMON statistics. Configure a port isolation...
... 19 Energy Saving 20 SNMP 21 Interface Statistics 22 VLAN 23 VLAN Interface 24 Voice VLAN 25 MAC Address 26 MSTP 27 Link Aggregation and LACP 28 LLDP 29 IGMP Snooping 30 Routing 31 DHCP 32 Service Management 33 Diagnostic Tools 34 ARP 35 802.1X 36 AAA 37 RADIUS 38 User 39 PKI 40 Port Isolation Group 41 Authorized IP 42 ACL-QoS 43 PoE Contents Configure RMON, and dissplay, create, modify, and clear RMON statistics. Configure a port isolation...
User Guide
Page 7
... Interface 2-1 Web-Based Network Management Operating Environment 2-1 Logging In to the Web Interface 2-1 Default Login Information 2-1 Example 2-2 Logging Out of the Web Interface 2-3 Introduction to the Web Interface 2-3 Web User Level 2-4 Introduction to the Web-Based NM Functions 2-4 Introduction to the Controls on the Web Pages 2-11 Configuration Guidelines 2-13 3 Configuration Through the Command Line Interface 3-1 Getting Started with the Command Line Interface 3-1 Setting Up the Configuration Environment 3-1 Setting Terminal Parameters 3-2 Logging In to the CLI 3-6 CLI...
... Interface 2-1 Web-Based Network Management Operating Environment 2-1 Logging In to the Web Interface 2-1 Default Login Information 2-1 Example 2-2 Logging Out of the Web Interface 2-3 Introduction to the Web Interface 2-3 Web User Level 2-4 Introduction to the Web-Based NM Functions 2-4 Introduction to the Controls on the Web Pages 2-11 Configuration Guidelines 2-13 3 Configuration Through the Command Line Interface 3-1 Getting Started with the Command Line Interface 3-1 Setting Up the Configuration Environment 3-1 Setting Terminal Parameters 3-2 Logging In to the CLI 3-6 CLI...
User Guide
Page 14
... n Storm Constrain Display and set the interval for collecting traffic statistics on interfaces. Display, create, modify, and remove the port traffic threshold. Configure Alarm View, create, modify, and clear alarm entries. Configure Initialize Restore the factory default settings. Port Manage ment Summary Detail Setup Display port information by ports. Create a port mirroring group. Configure Summary Display the brief information of the cables connected to Ethernet ports. Configure VCT VCT Check the status of FTP and Telnet users. Configure RMON...
... n Storm Constrain Display and set the interval for collecting traffic statistics on interfaces. Display, create, modify, and remove the port traffic threshold. Configure Alarm View, create, modify, and clear alarm entries. Configure Initialize Restore the factory default settings. Port Manage ment Summary Detail Setup Display port information by ports. Create a port mirroring group. Configure Summary Display the brief information of the cables connected to Ethernet ports. Configure VCT VCT Check the status of FTP and Telnet users. Configure RMON...
User Guide
Page 17
...settings, configure a DHCP server group, and enable/disable the DHCP relay agent on a port. Configure DHCP Snooping Display the status, trusted and untrusted ports and DHCP client information of an ISP domain. Configure Management Diagnost ic Tools Ping Trace Route Ping an IPv4 address. Configure ARP Anti-Atta ck ARP Detection Display ARP detection configuration information. Configure 802.1X globally or on an interface. Monitor Configure Domain Setup Display ISP domain configuration information. Monitor Management RADIUS RADIUS Server Display and configure RADIUS server...
...settings, configure a DHCP server group, and enable/disable the DHCP relay agent on a port. Configure DHCP Snooping Display the status, trusted and untrusted ports and DHCP client information of an ISP domain. Configure Management Diagnost ic Tools Ping Trace Route Ping an IPv4 address. Configure ARP Anti-Atta ck ARP Detection Display ARP detection configuration information. Configure 802.1X globally or on an interface. Monitor Configure Domain Setup Display ISP domain configuration information. Monitor Management RADIUS RADIUS Server Display and configure RADIUS server...
User Guide
Page 28
... a list of a user password Download the Boot ROM program or boot file from the upgrade server-address source-filename TFTP server and specify it to the CLI Interface: Step1 Press Enter. The Username prompt displays: Login authentication Username: Step2 Enter your User Name at the next startup { bootrom | runtime } Reboot the device and run the default configuration initialize Specify VLAN-interface 1 to obtain an IP address through DHCP or manual configuration ipsetup { dhcp | ip address ip-address { mask | mask-length } [ default-gateway...
... a list of a user password Download the Boot ROM program or boot file from the upgrade server-address source-filename TFTP server and specify it to the CLI Interface: Step1 Press Enter. The Username prompt displays: Login authentication Username: Step2 Enter your User Name at the next startup { bootrom | runtime } Reboot the device and run the default configuration initialize Specify VLAN-interface 1 to obtain an IP address through DHCP or manual configuration ipsetup { dhcp | ip address ip-address { mask | mask-length } [ default-gateway...
User Guide
Page 29
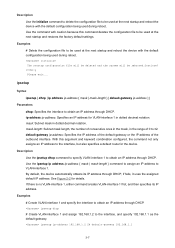
... initialize command to delete the configuration file to be used at the next startup and restores the factory default settings. ipsetup Syntax ipsetup { dhcp | ip address ip-address { mask | mask-length } [ default-gateway ip-address ] } Parameters dhcp: Specifies the interface to VLAN-interface 1. mask-length: Subnet mask length, the number of consecutive ones in the mask, in the range of the outbound interface. By default, the device automatically obtains its IP address. Use the command...
... initialize command to delete the configuration file to be used at the next startup and restores the factory default settings. ipsetup Syntax ipsetup { dhcp | ip address ip-address { mask | mask-length } [ default-gateway ip-address ] } Parameters dhcp: Specifies the interface to VLAN-interface 1. mask-length: Subnet mask length, the number of consecutive ones in the mask, in the range of the outbound interface. By default, the device automatically obtains its IP address. Use the command...
User Guide
Page 103
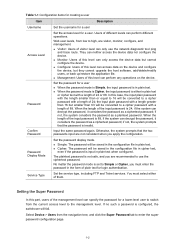
... be converted to the management level. Password Display Mode Set the password display mode. Setting the Super Password In this level can only use the ciphertext password. Users of visitor level can perform any operations on the device and configure the device, but smaller than 16 but they cannot upgrade the host software, add/delete/modify users, or back up/restore the application file. They can access data on the device...
... be converted to the management level. Password Display Mode Set the password display mode. Setting the Super Password In this level can only use the ciphertext password. Users of visitor level can perform any operations on the device and configure the device, but smaller than 16 but they cannot upgrade the host software, add/delete/modify users, or back up/restore the application file. They can access data on the device...
User Guide
Page 187
... option is available when the voice VLAN port state is assigned to Configuring voice VLAN on a port in automatic voice VLAN assignment mode. Configuring Voice VLAN on a Port Select Network > Voice VLAN from the navigation tree, and click the Port Setup tab on a port Table 1-7 describes the configuration items of a port to: z Auto, that is, automatic voice VLAN assignment mode z Manual, that is removed from the voice VLAN. Figure 1-2 Configure voice VLAN on the displayed page to Enable.
... option is available when the voice VLAN port state is assigned to Configuring voice VLAN on a port in automatic voice VLAN assignment mode. Configuring Voice VLAN on a Port Select Network > Voice VLAN from the navigation tree, and click the Port Setup tab on a port Table 1-7 describes the configuration items of a port to: z Auto, that is, automatic voice VLAN assignment mode z Manual, that is removed from the voice VLAN. Figure 1-2 Configure voice VLAN on the displayed page to Enable.
User Guide
Page 268
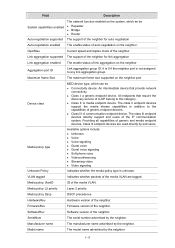
... z Router Auto-negotiation supported The support of the neighbor for link aggregation Link aggregation enabled The enable status of the neighbor. FirmwareRev Firmware version of the media VLAN. z Class III: A communication endpoint device. z Class II: A media endpoint device. Media policy VlanID ID of the neighbor. Providing all capabilities of auto negotiation on the neighbor port. SerialNum The serial number advertised by end users. OperMau Current speed and duplex mode of the neighbor Link aggregation supported...
... z Router Auto-negotiation supported The support of the neighbor for link aggregation Link aggregation enabled The enable status of the neighbor. FirmwareRev Firmware version of the media VLAN. z Class III: A communication endpoint device. z Class II: A media endpoint device. Media policy VlanID ID of the neighbor. Providing all capabilities of auto negotiation on the neighbor port. SerialNum The serial number advertised by end users. OperMau Current speed and duplex mode of the neighbor Link aggregation supported...
User Guide
Page 285
... in the multicast information addressed to announce its interest in the outgoing port list, the switch resets the member port aging timer for that the host has left the multicast group. This is because if the switch forwards a report message through a member port, all the router ports in the outgoing port list, the switch adds the port as it through a non-router port. You can add or delete only dynamic ports rather than static ports.
... in the multicast information addressed to announce its interest in the outgoing port list, the switch resets the member port aging timer for that the host has left the multicast group. This is because if the switch forwards a report message through a member port, all the router ports in the outgoing port list, the switch adds the port as it through a non-router port. You can add or delete only dynamic ports rather than static ports.
User Guide
Page 286
... outgoing port list of the forwarding table entry for that multicast group when the aging timer expires. instead, the switch resets the member port aging timer for that multicast group. The switch removes the port from the outgoing port list; z If no hosts attached to the port are still listening to that group address. Table 1-1 IGMP snooping configuration task list Task Enabling IGMP snooping Globally Required Disabled by default. Upon hearing the IGMP group-specific query, the switch forwards it...
... outgoing port list of the forwarding table entry for that multicast group when the aging timer expires. instead, the switch resets the member port aging timer for that multicast group. The switch removes the port from the outgoing port list; z If no hosts attached to the port are still listening to that group address. Table 1-1 IGMP snooping configuration task list Task Enabling IGMP snooping Globally Required Disabled by default. Upon hearing the IGMP group-specific query, the switch forwards it...
User Guide
Page 327
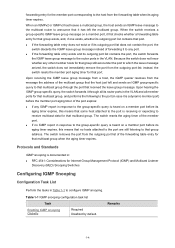
... the MAC address of the IP address. z Enable DHCP snooping on Switch B and configure DHCP snooping to the client. Table 3-3 DHCP snooping user information configuration items Item Description IP Address MAC Address This field displays the IP address assigned by the DHCP server to support Option 82. This field displays the VLAN to DHCP clients through GigabitEthernet 1/0/2 and GigabitEthernet 1/0/3. disable GigabitEthernet 1/0/2 and GigabitEthernet 1/0/3 from the navigation tree, and then click the DHCP Snooping tab. DHCP Snooping Configuration Example Network requirements...
... the MAC address of the IP address. z Enable DHCP snooping on Switch B and configure DHCP snooping to the client. Table 3-3 DHCP snooping user information configuration items Item Description IP Address MAC Address This field displays the IP address assigned by the DHCP server to support Option 82. This field displays the VLAN to DHCP clients through GigabitEthernet 1/0/2 and GigabitEthernet 1/0/3. disable GigabitEthernet 1/0/2 and GigabitEthernet 1/0/3 from the navigation tree, and then click the DHCP Snooping tab. DHCP Snooping Configuration Example Network requirements...
User Guide
Page 333
... service is disabled by clicking the expanding button in front of the device; You can view this configuration item by default. 1-2 The SSH service is disabled by default. Figure 1-1 Service management Table 1-1 shows the detailed configuration for the device to control the access right of the client, in Figure 1-1. Only the clients that pass the ACL filtering are permitted to enable the Telnet service. The Telnet service is disabled by default. Associates the FTP service...
... service is disabled by clicking the expanding button in front of the device; You can view this configuration item by default. 1-2 The SSH service is disabled by default. Figure 1-1 Service management Table 1-1 shows the detailed configuration for the device to control the access right of the client, in Figure 1-1. Only the clients that pass the ACL filtering are permitted to enable the Telnet service. The Telnet service is disabled by default. Associates the FTP service...
User Guide
Page 400
... the RADIUS server and the client through a series of mechanisms, including the timer management mechanism, retransmission mechanism, and slave server mechanism. From the server to network resources. If any attribute value carried in the Access-Request are as follows: 1) The Code field (1-byte long) is unacceptable, the server rejects the user and sends an Access-Reject response. It contains the Acct-Status-Type attribute...
... the RADIUS server and the client through a series of mechanisms, including the timer management mechanism, retransmission mechanism, and slave server mechanism. From the server to network resources. If any attribute value carried in the Access-Request are as follows: 1) The Code field (1-byte long) is unacceptable, the server rejects the user and sends an Access-Reject response. It contains the Acct-Status-Type attribute...
User Guide
Page 450
... matching criteria such as source MAC address, destination MAC address, 802.1p precedence, and link layer protocol type IPv4 ACL Match Order An ACL may have overlapping or conflicting parts. Introduction to use access control lists (ACLs). Packet filtering can pass and which specify different matching criteria. Table 1-1 IPv4 ACL categories Category ACL number Basic IPv4 ACL 2000 to 2999 Advanced IPv4 ACL 3000 to 3999 Ethernet frame header ACL 4000 to 4999 Matching criteria...
... matching criteria such as source MAC address, destination MAC address, 802.1p precedence, and link layer protocol type IPv4 ACL Match Order An ACL may have overlapping or conflicting parts. Introduction to use access control lists (ACLs). Packet filtering can pass and which specify different matching criteria. Table 1-1 IPv4 ACL categories Category ACL number Basic IPv4 ACL 2000 to 2999 Advanced IPv4 ACL 3000 to 3999 Ethernet frame header ACL 4000 to 4999 Matching criteria...
User Guide
Page 500
... mode. Currently, a PoE interface can examine the Ethernet cables connected to PoE interfaces, search for transmitting data in a category 3/5 twisted pair cable to supply DC power to PDs. otherwise, you cannot configure PoE or the configured PoE function does not take effect. 1-2 z Over spare wires: The PSE uses the pairs (4, 5, 7, 8) not transmitting data in a category 3/5 twisted pair cable to supply DC power while transmitting data to PDs. 3Com Baseline Switch 2920-SFP Plus only support for redundancy power backup. Configuring PoE Before configure PoE...
... mode. Currently, a PoE interface can examine the Ethernet cables connected to PoE interfaces, search for transmitting data in a category 3/5 twisted pair cable to supply DC power to PDs. otherwise, you cannot configure PoE or the configured PoE function does not take effect. 1-2 z Over spare wires: The PSE uses the pairs (4, 5, 7, 8) not transmitting data in a category 3/5 twisted pair cable to supply DC power while transmitting data to PDs. 3Com Baseline Switch 2920-SFP Plus only support for redundancy power backup. Configuring PoE Before configure PoE...
Data Sheet
Page 1
... auto-voice VLAN, advanced voice QoS, SNMPbased management, Power over the same cabling. a 24-port PoE version delivers data and power over Ethernet (PoE) and other parts of the network. DATA SHEET 3Com® Baseline Switch 2900 Plus Family Enterprise-class, Gigabit switches for small and medium businesses, voice ready with 16, 24 and 48 ports; from left top, clockwise: 3Com Switch 2916-SFP Plus, Switch 2924-PWR Plus, Switch 2948-SFP Plus, Switch 2924-SFP Plus Baseline Switch 2900 models are encrypted with IEEE 802.1X network login and advanced Access Control Lists (ACLs...
... auto-voice VLAN, advanced voice QoS, SNMPbased management, Power over the same cabling. a 24-port PoE version delivers data and power over Ethernet (PoE) and other parts of the network. DATA SHEET 3Com® Baseline Switch 2900 Plus Family Enterprise-class, Gigabit switches for small and medium businesses, voice ready with 16, 24 and 48 ports; from left top, clockwise: 3Com Switch 2916-SFP Plus, Switch 2924-PWR Plus, Switch 2948-SFP Plus, Switch 2924-SFP Plus Baseline Switch 2900 models are encrypted with IEEE 802.1X network login and advanced Access Control Lists (ACLs...
Data Sheet
Page 2
... mirroring) and MAC address port mapping tables. This ensures optimal use of switch status and configuration. and IP-based ACLs enable network traffic filtering and enhance network control. A cable diagnostic tool lets users troubleshoot basic connectivity problems via SFP-based fiber modules. PoE support (PWR model only) Provides power for quality communications. Using the CLI, major switch management options can be used for quality voice communications. Advanced QoS and traffic shaping Traffic prioritization, using a web browser, console port, or SNMP management...
... mirroring) and MAC address port mapping tables. This ensures optimal use of switch status and configuration. and IP-based ACLs enable network traffic filtering and enhance network control. A cable diagnostic tool lets users troubleshoot basic connectivity problems via SFP-based fiber modules. PoE support (PWR model only) Provides power for quality communications. Using the CLI, major switch management options can be used for quality voice communications. Advanced QoS and traffic shaping Traffic prioritization, using a web browser, console port, or SNMP management...
Data Sheet
Page 3
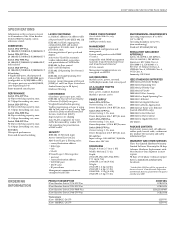
... forwarding rate, max. All models Wirespeed performance Store-and-forward switching LAYER 2 SWITCHING 8,192 MAC addresses in address table 256 port-based VLANs (IEEE 802.1Q) IEEE 802.3ad Link Aggregation, automated (LACP) and manual aggregation: 8 trunks, max.; 8 ports per port, with IEEE 802.1p Class of Service/Quality of Service (CoS/QoS) on egress Weighted Round Robin queuing Traffic prioritization at Layer 2 using 802.1p QoS, and at Layer 3 using Type of Service (TOS) with SNMP management tools like 3Com Network Supervisor and 3Com Network Director* CLI via console Management...
... forwarding rate, max. All models Wirespeed performance Store-and-forward switching LAYER 2 SWITCHING 8,192 MAC addresses in address table 256 port-based VLANs (IEEE 802.1Q) IEEE 802.3ad Link Aggregation, automated (LACP) and manual aggregation: 8 trunks, max.; 8 ports per port, with IEEE 802.1p Class of Service/Quality of Service (CoS/QoS) on egress Weighted Round Robin queuing Traffic prioritization at Layer 2 using 802.1p QoS, and at Layer 3 using Type of Service (TOS) with SNMP management tools like 3Com Network Supervisor and 3Com Network Director* CLI via console Management...