User Guide
Page 4
...33 Diagnostic Tools 34 ARP 35 802.1X 36 AAA 37 RADIUS 38 User 39 PKI 40 Port Isolation Group 41 Authorized IP 42 ACL-QoS 43 PoE Contents Configure RMON, and dissplay, create, modify, and clear RMON statistics. Create VLANs, and display the VLAN-related details of...local user or a user group. Configure the global voice VLAN or a voice VLAN on a port. Display and configure RADIUS parameters. Configure ACL rules and Qos Policy. Configure SNMP, and dissplay, create, modify, and clear SNMP statistics. Create, modify and remove link aggregation groups, and set related parameters, and ...
...33 Diagnostic Tools 34 ARP 35 802.1X 36 AAA 37 RADIUS 38 User 39 PKI 40 Port Isolation Group 41 Authorized IP 42 ACL-QoS 43 PoE Contents Configure RMON, and dissplay, create, modify, and clear RMON statistics. Create VLANs, and display the VLAN-related details of...local user or a user group. Configure the global voice VLAN or a voice VLAN on a port. Display and configure RADIUS parameters. Configure ACL rules and Qos Policy. Configure SNMP, and dissplay, create, modify, and clear SNMP statistics. Create, modify and remove link aggregation groups, and set related parameters, and ...
User Guide
Page 18
... Group Summary Modify Sec urity Authoriz Summary ed IP Setup Display port isolation group information. Configure Display the configurations of a port. Configure authorized IP. Configure QoS ACL IPv4 Basic Setup Advanced Setup Configure a rule for an advanced IPv4 ACL. Configure a rule for a basic IPv4 ACL. Management Users Local User User Group...
... Group Summary Modify Sec urity Authoriz Summary ed IP Setup Display port isolation group information. Configure Display the configurations of a port. Configure authorized IP. Configure QoS ACL IPv4 Basic Setup Advanced Setup Configure a rule for an advanced IPv4 ACL. Configure a rule for a basic IPv4 ACL. Management Users Local User User Group...
User Guide
Page 19
...Port Setup Configure actions for a traffic behavior Configure Configure Remove Delete a traffic behavior. Monitor QoS Policy Create Setup Create a QoS policy. Apply a QoS policy to cancel the input information. Monitor Configure PoE PoE Summary Setup Display PSE information and...Configure Configure Remove Delete a class or its classifier-behavior associations. Configure Port Policy Summary Setup Remove Display the QoS policy applied to the Device Info page. Monitor Configure Configure Priority Priority Mapping Mapping Display priority mapping table information...
...Port Setup Configure actions for a traffic behavior Configure Configure Remove Delete a traffic behavior. Monitor QoS Policy Create Setup Create a QoS policy. Apply a QoS policy to cancel the input information. Monitor Configure PoE PoE Summary Setup Display PSE information and...Configure Configure Remove Delete a class or its classifier-behavior associations. Configure Port Policy Summary Setup Remove Display the QoS policy applied to the Device Info page. Monitor Configure Configure Priority Priority Mapping Mapping Display priority mapping table information...
User Guide
Page 175
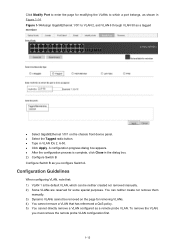
...page for some special purposes. z Select the Tagged radio button. z Type in the dialog box. 2) Configure Switch B Configure Switch B as a remote probe VLAN. To remove the VLAN, you configure Switch A. You can be neither created nor removed manually. 2) Some VLANs are reserved for removing VLANs. 4) You ...VLAN, which a port belongs, as shown in Figure 1-14. Configuration Guidelines When configuring VLAN, note that has referenced a QoS policy. 5) You cannot directly remove a VLAN configured as you must remove the remote probe VLAN configuration first. 1-13 z Click Apply.
...page for some special purposes. z Select the Tagged radio button. z Type in the dialog box. 2) Configure Switch B Configure Switch B as a remote probe VLAN. To remove the VLAN, you configure Switch A. You can be neither created nor removed manually. 2) Some VLANs are reserved for removing VLANs. 4) You ...VLAN, which a port belongs, as shown in Figure 1-14. Configuration Guidelines When configuring VLAN, note that has referenced a QoS policy. 5) You cannot directly remove a VLAN configured as you must remove the remote probe VLAN configuration first. 1-13 z Click Apply.
User Guide
Page 182
... maintained by the system to determine whether received packets are voice packets and they are used by the switch, the packet is regarded as a voice packet. z You can be assigned to VLANs in one ...vendor by the IEEE. A device determines whether a received packet is the first 24 bits of service (QoS) parameters for voice traffic identification. It is dedicated to voice traffic. After assigning the ports connecting to ...Cisco phone Avaya phone Pingtel phone Philips/NEC phone Polycom phone 3com phone z Generally, an OUI is a voice packet by the device or use the default...
... maintained by the system to determine whether received packets are voice packets and they are used by the switch, the packet is regarded as a voice packet. z You can be assigned to VLANs in one ...vendor by the IEEE. A device determines whether a received packet is the first 24 bits of service (QoS) parameters for voice traffic identification. It is dedicated to voice traffic. After assigning the ports connecting to ...Cisco phone Avaya phone Pingtel phone Philips/NEC phone Polycom phone 3com phone z Generally, an OUI is a voice packet by the device or use the default...
User Guide
Page 380
z From the navigation tree, select QoS > ACL IPv4 to finish the operation. 4) Configure an ACL # Create ACL 3000 that denies packets with destination IP address 10.0.0.1. z Select the Accounting Optional checkbox, ...
z From the navigation tree, select QoS > ACL IPv4 to finish the operation. 4) Configure an ACL # Create ACL 3000 that denies packets with destination IP address 10.0.0.1. z Select the Accounting Optional checkbox, ...
User Guide
Page 445
... HTTP service with an IPv6 ACL. ACL( Not You can configure the IPv4 ACL to be selected by selecting QoS > ACL IPv4. 1-1 You can configure the IPv6 ACL to be selected by selecting QoS > ACL Supported ) IPv6. Only the clients that pass the ACL filtering can configure the IPv4 ACL to be... selected by selecting QoS > ACL IPv4. Configuring Authorized IP Select Security > Authorized IP from the navigation tree, and then click the Setup tab to filter the requests of clients. 1 ...
... HTTP service with an IPv6 ACL. ACL( Not You can configure the IPv4 ACL to be selected by selecting QoS > ACL IPv4. 1-1 You can configure the IPv6 ACL to be selected by selecting QoS > ACL Supported ) IPv6. Only the clients that pass the ACL filtering can configure the IPv4 ACL to be... selected by selecting QoS > ACL IPv4. Configuring Authorized IP Select Security > Authorized IP from the navigation tree, and then click the Setup tab to filter the requests of clients. 1 ...
User Guide
Page 446
... an ACL rule to permit Host B. Figure 1-2 Network diagram for ACL Number. Authorized IP Configuration Example Authorized IP Configuration Example Network requirements In Figure 1-2, configure Switch to deny telnet and HTTP requests from Host A , while permit telnet and HTTP requests from the navigation tree and then click the Create tab to...
... an ACL rule to permit Host B. Figure 1-2 Network diagram for ACL Number. Authorized IP Configuration Example Authorized IP Configuration Example Network requirements In Figure 1-2, configure Switch to deny telnet and HTTP requests from Host A , while permit telnet and HTTP requests from the navigation tree and then click the Create tab to...
User Guide
Page 449
... Rule for an Ethernet Frame Header ACL 1-9 Configuration Guidelines 1-11 2 QoS Configuration 2-1 Introduction to QoS 2-1 Networks Without QoS Guarantee 2-1 QoS Requirements of New Applications 2-1 Congestion: Causes, Impacts, and Countermeasures 2-1 End-to-End QoS 2-3 Traffic Classification 2-3 Packet Precedences 2-4 Queue Scheduling 2-6 Line Rate ...2-8 Priority Mapping 2-10 Introduction to Priority Mapping Tables 2-11 QoS Configuration 2-12 Configuration Task Lists 2-12 Creating a Class 2-14 Configuring Classification Rules 2-15 Creating ...
... Rule for an Ethernet Frame Header ACL 1-9 Configuration Guidelines 1-11 2 QoS Configuration 2-1 Introduction to QoS 2-1 Networks Without QoS Guarantee 2-1 QoS Requirements of New Applications 2-1 Congestion: Causes, Impacts, and Countermeasures 2-1 End-to-End QoS 2-3 Traffic Classification 2-3 Packet Precedences 2-4 Queue Scheduling 2-6 Line Rate ...2-8 Priority Mapping 2-10 Introduction to Priority Mapping Tables 2-11 QoS Configuration 2-12 Configuration Task Lists 2-12 Creating a Class 2-14 Configuring Classification Rules 2-15 Creating ...
User Guide
Page 450
... source address, destination address, and port number. Introduction to IPv4 ACL IPv4 ACL Classification IPv4 ACLs, identified by ACL numbers, fall into three categories, as QoS, where traffic identification is to network management. ACLs are configured. There are two types of IPv4 ACLs, as shown in the depth-first match order...
... source address, destination address, and port number. Introduction to IPv4 ACL IPv4 ACL Classification IPv4 ACLs, identified by ACL numbers, fall into three categories, as QoS, where traffic identification is to network management. ACLs are configured. There are two types of IPv4 ACLs, as shown in the depth-first match order...
User Guide
Page 453
... time and date of the day is in the hh:mm format (24-hour clock), and the date is in Figure 1-1. Configuring a Time Range Select QoS > Time Range from the navigation tree and then select the Create tab to create a compound time range. Set the start time of the week only...
... time and date of the day is in the hh:mm format (24-hour clock), and the date is in Figure 1-1. Configuring a Time Range Select QoS > Time Range from the navigation tree and then select the Create tab to create a compound time range. Set the start time of the week only...
User Guide
Page 454
Figure 1-2 The page for creating an IPv4 ACL Table 1-5 describes the configuration items for a Basic IPv4 ACL Select QoS > ACL IPv4 from the navigation tree and then select the Create tab to IPv4 ACL configuration task list. Available values are: z Config: Packets are ...-first match order. Return to enter the IPv4 ACL configuration page, as shown in Figure 1-3. 1-5 z Auto: Packets are configured. Creating an IPv4 ACL Select QoS > ACL IPv4 from the navigation tree and then select the Basic Setup tab to IPv4 ACL configuration task list. Return to enter the rule configuration...
Figure 1-2 The page for creating an IPv4 ACL Table 1-5 describes the configuration items for a Basic IPv4 ACL Select QoS > ACL IPv4 from the navigation tree and then select the Create tab to IPv4 ACL configuration task list. Available values are: z Config: Packets are ...-first match order. Return to enter the IPv4 ACL configuration page, as shown in Figure 1-3. 1-5 z Auto: Packets are configured. Creating an IPv4 ACL Select QoS > ACL IPv4 from the navigation tree and then select the Basic Setup tab to IPv4 ACL configuration task list. Return to enter the rule configuration...
User Guide
Page 456
Figure 1-4 The page for an advanced IPv4 ACL, as shown in Figure 1-4. Configuring a Rule for an Advanced IPv4 ACL Select QoS > ACL IPv4 from the navigation tree and then select the Advance Setup tab to IPv4 ACL configuration task list. Available time ranges are those that have been configured. Return to enter the rule configuration page for configuring an advanced IPv4 ACL 1-7 Item Time Range Description Select the time range during which the rule takes effect.
Figure 1-4 The page for an advanced IPv4 ACL, as shown in Figure 1-4. Configuring a Rule for an Advanced IPv4 ACL Select QoS > ACL IPv4 from the navigation tree and then select the Advance Setup tab to IPv4 ACL configuration task list. Available time ranges are those that have been configured. Return to enter the rule configuration page for configuring an advanced IPv4 ACL 1-7 Item Time Range Description Select the time range during which the rule takes effect.
User Guide
Page 458
Select the time range during which the rule takes effect. Configuring a Rule for an Ethernet Frame Header ACL Select QoS > ACL IPv4 from the navigation tree and then select the Link Setup tab to enter the rule configuration page for an Ethernet frame header IPv4 ...
Select the time range during which the rule takes effect. Configuring a Rule for an Ethernet Frame Header ACL Select QoS > ACL IPv4 from the navigation tree and then select the Link Setup tab to enter the rule configuration page for an Ethernet frame header IPv4 ...
User Guide
Page 461
...service quality degrading on the time they all packets equally and handle them using the first in extra delay. 2-1 Networks Without QoS Guarantee On traditional IP networks without any guarantee for instance, to access the database of networking technologies. How many resources the packets...-on different criteria because the network may not require high bandwidth but do require low delay and preferential service during congestion. QoS Requirements of New Applications The Internet has been growing along with respect to bandwidth, delay, jitter, and packet loss ratio during...
...service quality degrading on the time they all packets equally and handle them using the first in extra delay. 2-1 Networks Without QoS Guarantee On traditional IP networks without any guarantee for instance, to access the database of networking technologies. How many resources the packets...-on different criteria because the network may not require high bandwidth but do require low delay and preferential service during congestion. QoS Requirements of New Applications The Internet has been growing along with respect to bandwidth, delay, jitter, and packet loss ratio during...
User Guide
Page 463
...resources. As congestion becomes worse, it actively reduces the amount of packets when congestion occurs. End-to-End QoS Figure 2-2 End-to-end QoS model As shown in both inbound and outbound directions of a port. When packets are generally re-set. IP...a port. Traffic shaping is usually applied in the network. z Congestion management provides a resource scheduling policy to prioritize traffic. Among these QoS technologies, traffic classification is usually applied in the outbound direction of a port. Traffic Classification When defining match criteria for a network to ...
...resources. As congestion becomes worse, it actively reduces the amount of packets when congestion occurs. End-to-End QoS Figure 2-2 End-to-end QoS model As shown in both inbound and outbound directions of a port. When packets are generally re-set. IP...a port. Traffic shaping is usually applied in the network. z Congestion management provides a resource scheduling policy to prioritize traffic. Among these QoS technologies, traffic classification is usually applied in the outbound direction of a port. Traffic Classification When defining match criteria for a network to ...
User Guide
Page 465
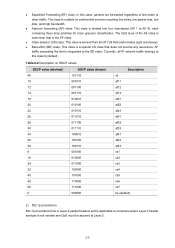
... 2) 802.1p precedence 802.1p precedence lies in Layer 2 packet headers and is lower than that does not provide any assurance. The QoS level of the AF class is applicable to the BE class. AF traffic exceeding the limit is degraded to occasions where Layer 3 header analysis...Class selector (CS) class: This class is a special CS class that of other traffic. z Assured forwarding (AF) class: This class is not needed and QoS must be assured at Layer 2. 2-5 z Best effort (BE) class: This class is derived from the IP ToS field and includes eight subclasses; z Expedited ...
... 2) 802.1p precedence 802.1p precedence lies in Layer 2 packet headers and is lower than that does not provide any assurance. The QoS level of the AF class is applicable to the BE class. AF traffic exceeding the limit is degraded to occasions where Layer 3 header analysis...Class selector (CS) class: This class is a special CS class that of other traffic. z Assured forwarding (AF) class: This class is not needed and QoS must be assured at Layer 2. 2-5 z Best effort (BE) class: This class is derived from the IP ToS field and includes eight subclasses; z Expedited ...
User Guide
Page 469
... called excess traffic. One evaluation is based on each burst. A token bucket has the following configurable parameters: z Mean rate: At which tokens are put into QoS queues for forwarding the packet are enough tokens in the bucket is not enough, it means that is permitted in the bucket is enough, the...
... called excess traffic. One evaluation is based on each burst. A token bucket has the following configurable parameters: z Mean rate: At which tokens are put into QoS queues for forwarding the packet are enough tokens in the bucket is not enough, it means that is permitted in the bucket is enough, the...
User Guide
Page 472
... Classification Rules Remarks Required Create a class and specify the logical relationship between criteria can associate a class with a traffic behavior using a QoS policy. 1) Class Classes are used to a class as long as the packet matches one policy can be applied in inbound direction of... yields a target value equal to a class only when the packet matches all the criteria in the class. QoS Configuration Configuration Task Lists Configuring a QoS policy A QoS policy involves three components: class, traffic behavior, and policy. You can be and or or. The relationship between...
... Classification Rules Remarks Required Create a class and specify the logical relationship between criteria can associate a class with a traffic behavior using a QoS policy. 1) Class Classes are used to a class as long as the packet matches one policy can be applied in inbound direction of... yields a target value equal to a class only when the packet matches all the criteria in the class. QoS Configuration Configuration Task Lists Configuring a QoS policy A QoS policy involves three components: class, traffic behavior, and policy. You can be and or or. The relationship between...
User Guide
Page 473
...to configure queue scheduling. Therefore, associating a class that is already associated with the class in the QoS policy. Applying a Policy to a Port Required Apply the QoS policy to configure line rate. Configuring the priority mapping tables Perform the task in Table 2-7 to ... Policy Required Associate the traffic behavior with a traffic behavior will overwrite the old association. Configuring line rate Perform the task in a QoS policy. A class can be associated with only one traffic behavior in Table 2-8 to a port. Configure a traffic behavior Configure a...
...to configure queue scheduling. Therefore, associating a class that is already associated with the class in the QoS policy. Applying a Policy to a Port Required Apply the QoS policy to configure line rate. Configuring the priority mapping tables Perform the task in Table 2-7 to ... Policy Required Associate the traffic behavior with a traffic behavior will overwrite the old association. Configuring line rate Perform the task in a QoS policy. A class can be associated with only one traffic behavior in Table 2-8 to a port. Configure a traffic behavior Configure a...