User Guide
Page 1
3Com Baseline Switch 2900 Family User Guide Baseline Switch 2920-SFP Plus Baseline Switch 2928-SFP Plus Baseline Switch 2952-SFP Plus Baseline Switch 2928-PWR Plus Baseline Switch 2928-HPWR Plus Manual Version: 6W102-20090810 www.3com.com 3Com Corporation 350 Campus Drive, Marlborough, MA, USA 01752 3064
3Com Baseline Switch 2900 Family User Guide Baseline Switch 2920-SFP Plus Baseline Switch 2928-SFP Plus Baseline Switch 2952-SFP Plus Baseline Switch 2928-PWR Plus Baseline Switch 2928-HPWR Plus Manual Version: 6W102-20090810 www.3com.com 3Com Corporation 350 Campus Drive, Marlborough, MA, USA 01752 3064
User Guide
Page 3
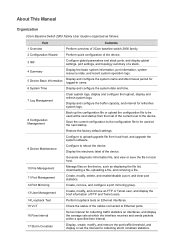
... and configure the system date and time. 7 Log Management Clear system logs, display and configure the loghost, display and refresh system logs. About This Manual Organization 3Com Baseline Switch 2900 Family User Guide is organized as displaying the file list, downloading a file, uploading a file, and removing a file. 11 Port Management Create, modify, delete, and enable...
... and configure the system date and time. 7 Log Management Clear system logs, display and configure the loghost, display and refresh system logs. About This Manual Organization 3Com Baseline Switch 2900 Family User Guide is organized as displaying the file list, downloading a file, uploading a file, and removing a file. 11 Port Management Create, modify, delete, and enable...
User Guide
Page 5
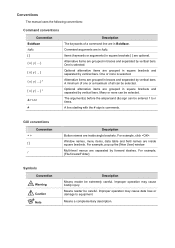
...optional. The argument(s) before the ampersand (&) sign can be entered 1 to equipment. For example, pop up the [New User] window. Improper operation may cause data loss or damage to n times. One is selected. Many or none can be selected... italic. A minimum of one or a maximum of a command line are in braces and separated by vertical bars. Improper operation may cause bodily injury. Conventions The manual uses the following conventions: Command conventions Convention Boldface italic [ ] { x | y | ... } [ x | y | ... ] { x | y | ... } * [ x | y | ... ] * & # Description ...
...optional. The argument(s) before the ampersand (&) sign can be entered 1 to equipment. For example, pop up the [New User] window. Improper operation may cause data loss or damage to n times. One is selected. Many or none can be selected... italic. A minimum of one or a maximum of a command line are in braces and separated by vertical bars. Improper operation may cause bodily injury. Conventions The manual uses the following conventions: Command conventions Convention Boldface italic [ ] { x | y | ... } [ x | y | ... ] { x | y | ... } * [ x | y | ... ] * & # Description ...
User Guide
Page 11
...does not save the current configuration before logout. Introduction to five users can get a new verification code. z After logging in to the Web interface, you can select Device > Users from the navigation tree, create a new user, and select Wizard or Network > VLAN interface to configure the... IP address of the VLAN interface acting as shown in Figure 2-4 to the corresponding configuration manuals of the Web interface, as the ...
...does not save the current configuration before logout. Introduction to five users can get a new verification code. z After logging in to the Web interface, you can select Device > Users from the navigation tree, create a new user, and select Wizard or Network > VLAN interface to configure the... IP address of the VLAN interface acting as shown in Figure 2-4 to the corresponding configuration manuals of the Web interface, as the ...
User Guide
Page 28
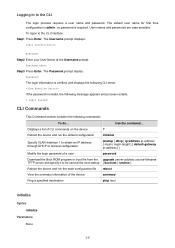
... Username prompt displays: Login authentication Username: Step2 Enter your User Name at the next startup { bootrom | runtime } Reboot the device and run the default configuration initialize Specify VLAN-interface 1 to obtain an IP address through DHCP or manual configuration ipsetup { dhcp | ip address ip-address { ...mask | mask-length } [ default-gateway ip-address ] } Modify the login password of a user password Download the Boot ROM program or boot file from the ...
... Username prompt displays: Login authentication Username: Step2 Enter your User Name at the next startup { bootrom | runtime } Reboot the device and run the default configuration initialize Specify VLAN-interface 1 to obtain an IP address through DHCP or manual configuration ipsetup { dhcp | ip address ip-address { ...mask | mask-length } [ default-gateway ip-address ] } Modify the login password of a user password Download the Boot ROM program or boot file from the ...
User Guide
Page 86
... for receiving signals. z For an Ethernet port in one end must connect the local transmit pins to set the limit manually. Enable or disable flow control on the port. Available options include: z User Defined: Select this option to the remote receive pins. You can operate in across , normal, and auto. z For an...
... for receiving signals. z For an Ethernet port in one end must connect the local transmit pins to set the limit manually. Enable or disable flow control on the port. Available options include: z User Defined: Select this option to the remote receive pins. You can operate in across , normal, and auto. z For an...
User Guide
Page 184
... in normal mode, thus reducing the consumption of system resources due to , first ensure that the voice VLAN security mode is dropped. Vicious users can configure the voice VLANs to traffic attacks. Forwarded or dropped depending on its inbound packet filtering mechanism. Security Mode and Normal Mode of ...the voice VLAN bandwidth, affecting normal voice communication. If the default VLAN of the port is the voice VLAN and the port works in manual VLAN assignment mode, the port forwards all other tags Packet processing mode If the source MAC address of the access port as the voice...
... in normal mode, thus reducing the consumption of system resources due to , first ensure that the voice VLAN security mode is dropped. Vicious users can configure the voice VLANs to traffic attacks. Forwarded or dropped depending on its inbound packet filtering mechanism. Security Mode and Normal Mode of ...the voice VLAN bandwidth, affecting normal voice communication. If the default VLAN of the port is the voice VLAN and the port works in manual VLAN assignment mode, the port forwards all other tags Packet processing mode If the source MAC address of the access port as the voice...
User Guide
Page 205
... address entry aging time, as shown in the tab are as follows: z Config static: indicates static MAC address entries manually configured by the users z Config dynamic: indicates dynamic MAC address entries manually configured by the users z Blackhole: indicates blackhole MAC address entries z Learned: indicates dynamic MAC address entries learned by the device z Other: indicates...
... address entry aging time, as shown in the tab are as follows: z Config static: indicates static MAC address entries manually configured by the users z Config dynamic: indicates dynamic MAC address entries manually configured by the users z Blackhole: indicates blackhole MAC address entries z Learned: indicates dynamic MAC address entries learned by the device z Other: indicates...
User Guide
Page 315
By default, no static binding is , you can manually configure IP-to-MAC bindings on the DHCP relay agent, so that users can dynamically record clients' IP-to expand the advanced DHCP relay agent configuration field, as shown in the DHCP Service field. The DHCP relay agent ...
By default, no static binding is , you can manually configure IP-to-MAC bindings on the DHCP relay agent, so that users can dynamically record clients' IP-to expand the advanced DHCP relay agent configuration field, as shown in the DHCP Service field. The DHCP relay agent ...
User Guide
Page 327
... static bindings are not supported. Return to support Option 82. z Enable GigabitEthernet 1/0/1 to the client. z Configure Switch B to record clients' IP-to-MAC address bindings in DHCP-REQUEST messages and DHCP-ACK messages received from forwarding...-MAC binding is connected to a DHCP server through GigabitEthernet 1/0/2 and GigabitEthernet 1/0/3. Table 3-3 DHCP snooping user information configuration items Item Description IP Address MAC Address This field displays the IP address assigned by the ... as shown in Figure 3-6, a DHCP snooping device (Switch B) is configured manually.
... static bindings are not supported. Return to support Option 82. z Enable GigabitEthernet 1/0/1 to the client. z Configure Switch B to record clients' IP-to-MAC address bindings in DHCP-REQUEST messages and DHCP-ACK messages received from forwarding...-MAC binding is connected to a DHCP server through GigabitEthernet 1/0/2 and GigabitEthernet 1/0/3. Table 3-3 DHCP snooping user information configuration items Item Description IP Address MAC Address This field displays the IP address assigned by the ... as shown in Figure 3-6, a DHCP snooping device (Switch B) is configured manually.
User Guide
Page 420
... PKI Terms Digital certificate A digital certificate is a file signed by the CA for example, the user name changes, the private key leaks, or the user stops the business. This manual involves two types of certificate owner identity information and public keys. In PKI, the revocation is made... certificates is so large that contains a public key and the related user identity information. A CA policy can be revoked when, for itself. It allows users to remove the binding of the public key with the user identity information. CRL An existing certificate may use certificates, and revoke ...
... PKI Terms Digital certificate A digital certificate is a file signed by the CA for example, the user name changes, the private key leaks, or the user stops the business. This manual involves two types of certificate owner identity information and public keys. In PKI, the revocation is made... certificates is so large that contains a public key and the related user identity information. A CA policy can be revoked when, for itself. It allows users to remove the binding of the public key with the user identity information. CRL An existing certificate may use certificates, and revoke ...
User Guide
Page 423
... This is referred to as to remove the CA certificate and local certificate first. 1-4 A CA identifies a certificate applicant by the user, while the public key is already a local certificate, you need to keep the consistency between certificates and registration information resulting from relevant...generating a new key pair, so as a PKI domain. Generating an RSA key pair is intended only for requesting a certificate manually Task Creating a PKI Entity Remarks Required Create a PKI entity and configure the identity information. Table 1-1 Configuration task list for ...
... This is referred to as to remove the CA certificate and local certificate first. 1-4 A CA identifies a certificate applicant by the user, while the public key is already a local certificate, you need to keep the consistency between certificates and registration information resulting from relevant...generating a new key pair, so as a PKI domain. Generating an RSA key pair is intended only for requesting a certificate manually Task Creating a PKI Entity Remarks Required Create a PKI entity and configure the identity information. Table 1-1 Configuration task list for ...
Data Sheet
Page 2
...port. PoE support (PWR model only) Provides power for data; Advanced Access Control Lists (ACLs) MAC- power can be limited per port; The Switch family also supports ... users to configure the switch during initial setup and monitor it during normal operation. Remotely detect copper cable issues using Link Aggregation Control Protocol (LACP), or manually,.... 3COM® BASELINE SWITCH 2900 PLUS FAMILY KEY BENEFITS (CONTINUED) NO SWITCH SETUP REQUIRED Baseline Plus switches are acceptable, there is no need to configure the switch. Using the CLI, major switch management...
...port. PoE support (PWR model only) Provides power for data; Advanced Access Control Lists (ACLs) MAC- power can be limited per port; The Switch family also supports ... users to configure the switch during initial setup and monitor it during normal operation. Remotely detect copper cable issues using Link Aggregation Control Protocol (LACP), or manually,.... 3COM® BASELINE SWITCH 2900 PLUS FAMILY KEY BENEFITS (CONTINUED) NO SWITCH SETUP REQUIRED Baseline Plus switches are acceptable, there is no need to configure the switch. Using the CLI, major switch management...