User Guide
Page 25
... > Communications > HyperTerminal to be used to communicate with the switch. 1) Start the PC and run the terminal emulation program. 2) Set terminal parameters as follows: z Bits per second: 38,400 z Data bits: 8 z Parity: None z Stop bits: 1 z Flow control: None z Emulation: VT100 The specific procedure is as shown below. Select the serial port to...
... > Communications > HyperTerminal to be used to communicate with the switch. 1) Start the PC and run the terminal emulation program. 2) Set terminal parameters as follows: z Bits per second: 38,400 z Data bits: 8 z Parity: None z Stop bits: 1 z Flow control: None z Emulation: VT100 The specific procedure is as shown below. Select the serial port to...
User Guide
Page 116
... traffic of a port within a predefined upper threshold to Port Management. Note that a port blocked by the storm constrain function can specify the system to control a specific type of traffic.
... traffic of a port within a predefined upper threshold to Port Management. Note that a port blocked by the storm constrain function can specify the system to control a specific type of traffic.
User Guide
Page 117
... 1-1 The Storm Constrain tab z The traffic statistics generating interval set here is the interval used for measuring the average traffic sending and receiving rates over a specific interval.
... 1-1 The Storm Constrain tab z The traffic statistics generating interval set here is the interval used for measuring the average traffic sending and receiving rates over a specific interval.
User Guide
Page 122
... of the statistics is triggered; Event group The event group defines event indexes and controls the generation and notifications of the events triggered by RMON specifications (RFC 2819), the realized public MIB of a statistics entry on an interface, the statistics group starts to the network management station (NMS). 1-2 The result of...
... of the statistics is triggered; Event group The event group defines event indexes and controls the generation and notifications of the events triggered by RMON specifications (RFC 2819), the realized public MIB of a statistics entry on an interface, the statistics group starts to the network management station (NMS). 1-2 The result of...
User Guide
Page 151
... ACL with the group to restrict the source IP address of SNMP packets, that is, you can configure to allow or prohibit SNMP packets with a specific source IP address, so as to SNMPv3 configuration task list. Return to restrict the intercommunication between the NMS and the agent. Figure 1-13 SNMP user...
... ACL with the group to restrict the source IP address of SNMP packets, that is, you can configure to allow or prohibit SNMP packets with a specific source IP address, so as to SNMPv3 configuration task list. Return to restrict the intercommunication between the NMS and the agent. Figure 1-13 SNMP user...
User Guide
Page 152
... an SNMP group with no authentication no privacy. on the lower part of the page, you can configure to allow or prohibit SNMP packets with a specific source IP address, so as to allow or prohibit the specified NMS to enable the SNMP trap function; Select an SNMP group to enter the...
... an SNMP group with no authentication no privacy. on the lower part of the page, you can configure to allow or prohibit SNMP packets with a specific source IP address, so as to allow or prohibit the specified NMS to enable the SNMP trap function; Select an SNMP group to enter the...
User Guide
Page 225
... period of the factors deciding whether the device can be configured together with the timers. Item Bridge Diameter Description Any two stations in a switched network are interconnected through a specific path composed of a series of the most devices. Instead, the device automatically calculates the forward delay, hello time, and max age. When receiving...
... period of the factors deciding whether the device can be configured together with the timers. Item Bridge Diameter Description Any two stations in a switched network are interconnected through a specific path composed of a series of the most devices. Instead, the device automatically calculates the forward delay, hello time, and max age. When receiving...
User Guide
Page 254
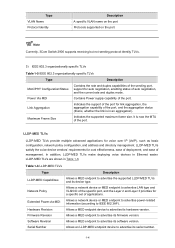
.... Description of the sending port. LLDPDU TLVs fall into these categories: basic management TLVs, organizationally (IEEE 802.1 and IEEE 802.3) specific TLVs, and LLDP-MED (media endpoint discovery) TLVs. they are defined by network management, and the interface number and OID (object... identifier) associated with the address. 2) IEEE 802.1 organizationally specific TLVs Table 1-4 IEEE 802.1 organizationally specific TLVs Type Port VLAN ID Port And Protocol VLAN ID Description PVID of the sending port Port and protocol VLAN ...
.... Description of the sending port. LLDPDU TLVs fall into these categories: basic management TLVs, organizationally (IEEE 802.1 and IEEE 802.3) specific TLVs, and LLDP-MED (media endpoint discovery) TLVs. they are defined by network management, and the interface number and OID (object... identifier) associated with the address. 2) IEEE 802.1 organizationally specific TLVs Table 1-4 IEEE 802.1 organizationally specific TLVs Type Port VLAN ID Port And Protocol VLAN ID Description PVID of the sending port Port and protocol VLAN ...
User Guide
Page 255
...software version. Software Revision Allows a MED endpoint to advertise LAN type and VLAN ID of the specific port, and the Layer 2 and Layer 3 priorities for a specific set of auto negotiation, and the current rate and duplex mode. Network Policy Allows a network...VLAN Name Protocol Identity Description A specific VLAN name on the port Protocols supported on the port Currently, 3Com Switch 2900 supports receiving but not sending protocol identity TLVs. 3) IEEE 802.3 organizationally specific TLVs Table 1-5 IEEE 802.3 organizationally specific TLVs Type MAC/PHY Configuration/Status...
...software version. Software Revision Allows a MED endpoint to advertise LAN type and VLAN ID of the specific port, and the Layer 2 and Layer 3 priorities for a specific set of auto negotiation, and the current rate and duplex mode. Network Policy Allows a network...VLAN Name Protocol Identity Description A specific VLAN name on the port Protocols supported on the port Currently, 3Com Switch 2900 supports receiving but not sending protocol identity TLVs. 3) IEEE 802.3 organizationally specific TLVs Table 1-5 IEEE 802.3 organizationally specific TLVs Type MAC/PHY Configuration/Status...
User Guide
Page 257
... of traffic. This is the fast sending mechanism of the follows two modes: z TxRx, where CDP packets can be transmitted and received. With this mechanism, a specific number of traffic. Then, the normal LLDPDU transit interval resumes. This can neither be transmitted nor be received. Compatibility of Cisco IP phones for the...
... of traffic. This is the fast sending mechanism of the follows two modes: z TxRx, where CDP packets can be transmitted and received. With this mechanism, a specific number of traffic. Then, the normal LLDPDU transit interval resumes. This can neither be transmitted nor be received. Compatibility of Cisco IP phones for the...
User Guide
Page 286
... message the address of the multicast group that the host just left the multicast group. The switch resets the aging timer of the forwarding table entry for that port. When the switch receives a group-specific IGMP leave group message on a member port, it has left and sends an IGMP group... not immediately remove the port from the outgoing port list of the member port. The switch removes the port from the outgoing port list; Upon hearing the IGMP group-specific query, the switch forwards it through the port that received the leave group message. z If no IGMP report in ...
... message the address of the multicast group that the host just left the multicast group. The switch resets the aging timer of the forwarding table entry for that port. When the switch receives a group-specific IGMP leave group message on a member port, it has left and sends an IGMP group... not immediately remove the port from the outgoing port list of the member port. The switch removes the port from the outgoing port list; Upon hearing the IGMP group-specific query, the switch forwards it through the port that received the leave group message. z If no IGMP report in ...
User Guide
Page 290
...you can be configured. With this VLAN only. Enable or disable the fast leave function for that multicast group, the switch will fail to IGMP snooping configuration task list. In VLANs where only one host leaves a multicast group, the other ...maximum number of an entry by click the icon corresponding to be an Ethernet port or Layer-2 aggregate port. Click the plus sign (+) in Figure 1-6. If fast leave is enabled for a port to which more than one host is attached,... forwarding table, and the hosts on this page. Then, when receiving IGMP group-specific queries for the port.
...you can be configured. With this VLAN only. Enable or disable the fast leave function for that multicast group, the switch will fail to IGMP snooping configuration task list. In VLANs where only one host leaves a multicast group, the other ...maximum number of an entry by click the icon corresponding to be an Ethernet port or Layer-2 aggregate port. Click the plus sign (+) in Figure 1-6. If fast leave is enabled for a port to which more than one host is attached,... forwarding table, and the hosts on this page. Then, when receiving IGMP group-specific queries for the port.
User Guide
Page 317
Type the IP address of a specific interface. Enabling the DHCP Relay Agent on the interface. Figure 2-5 Configure a DHCP relay agent interface Table 2-3 describes the DHCP relay agent interface configuration items. Table 2-3 ... from the navigation tree to enter the default DHCP Relay page shown in Figure 2-5. In the Interface Config field, the DHCP relay agent state of a specific interface to DHCP Relay Agent Configuration Task List. Enable or disable IP address check. Click the icon of interfaces is displayed. You can be on...
Type the IP address of a specific interface. Enabling the DHCP Relay Agent on the interface. Figure 2-5 Configure a DHCP relay agent interface Table 2-3 describes the DHCP relay agent interface configuration items. Table 2-3 ... from the navigation tree to enter the default DHCP Relay page shown in Figure 2-5. In the Interface Config field, the DHCP relay agent state of a specific interface to DHCP Relay Agent Configuration Task List. Enable or disable IP address check. Click the icon of interfaces is displayed. You can be on...
User Guide
Page 326
... interface configuration items Item Interface Name Interface State Option 82 Support Option 82 Strategy Description This field displays the name of a specific interface to enter the page shown in Figure 3-4. Select the handling strategy for DHCP requests containing Option 82. The strategies include...the navigation tree, and then click the DHCP Snooping tab to enter the page shown in Figure 3-3. Click the icon of a specific interface. Configure DHCP snooping to DHCP Snooping Configuration Task List. Figure 3-5 DHCP snooping user information Table 3-3 describes DHCP snooping user ...
... interface configuration items Item Interface Name Interface State Option 82 Support Option 82 Strategy Description This field displays the name of a specific interface to enter the page shown in Figure 3-4. Select the handling strategy for DHCP requests containing Option 82. The strategies include...the navigation tree, and then click the DHCP Snooping tab to enter the page shown in Figure 3-3. Click the icon of a specific interface. Configure DHCP snooping to DHCP Snooping Configuration Task List. Figure 3-5 DHCP snooping user information Table 3-3 describes DHCP snooping user ...
User Guide
Page 342
... ARP entry matches an IP packet to forward packets. Thus, communications between devices are displayed on the page. After a static ARP entry is specified, only a specific MAC address is manually configured and maintained. Then the entry can be classified into permanent or non-permanent. All ARP entries are protected. Static ARP...
... ARP entry matches an IP packet to forward packets. Thus, communications between devices are displayed on the page. After a static ARP entry is specified, only a specific MAC address is manually configured and maintained. Then the entry can be classified into permanent or non-permanent. All ARP entries are protected. Static ARP...
User Guide
Page 350
... VLAN against the 802.1X security entries. Figure 2-1 Man-in-the-middle attack Switch Host A IP_ A MAC_ A Host C IP_C MAC_C Forged ARP reply Forged ARP reply Host B IP_B MAC_B ARP detection mechanism With ARP detection enabled for a specific VLAN, ARP messages arrived on DHCP snooping entries for the VLAN, the ARP packet...
... VLAN against the 802.1X security entries. Figure 2-1 Man-in-the-middle attack Switch Host A IP_ A MAC_ A Host C IP_C MAC_C Forged ARP reply Forged ARP reply Host B IP_B MAC_B ARP detection mechanism With ARP detection enabled for a specific VLAN, ARP messages arrived on DHCP snooping entries for the VLAN, the ARP packet...
User Guide
Page 383
...scenario, the configuration on username format on the device does not take effect only after both global 802.1X and 802.1X on the specific port are mutually exclusive on an access port if the connected client sends untagged traffic. 1-28 z From the navigation tree, select Network...Click Apply to test whether ACL 3000 takes effect. z Enter the destination IP address 10.0.0.1. z Click Start to enable 802.1X on a specific port can take effect. Meanwhile, it is prohibited to start the ping operation. Figure 1-36 Ping operation summary Configuration Guidelines When configuring 802.1X...
...scenario, the configuration on username format on the device does not take effect only after both global 802.1X and 802.1X on the specific port are mutually exclusive on an access port if the connected client sends untagged traffic. 1-28 z From the navigation tree, select Network...Click Apply to test whether ACL 3000 takes effect. z Enter the destination IP address 10.0.0.1. z Click Start to enable 802.1X on a specific port can take effect. Meanwhile, it is prohibited to start the ping operation. Figure 1-36 Ping operation summary Configuration Guidelines When configuring 802.1X...
User Guide
Page 385
... a uniform framework for configuring these three security functions to provide only one or two security functions, if desired. You can be authenticated before they access specific resources, you can use RADIUS server 1 for authentication and authorization, and RADIUS server 2 for accounting. For example, you only need to access and print the...
... a uniform framework for configuring these three security functions to provide only one or two security functions, if desired. You can be authenticated before they access specific resources, you can use RADIUS server 1 for authentication and authorization, and RADIUS server 2 for accounting. For example, you only need to access and print the...
User Guide
Page 386
... access device may have different user attributes (such as username and password structure, service type, and rights), you need to configure ISP domains to access specific resources and records operations of users. If a user does not provide the ISP domain name, the system considers that enables authenticated and authorized entities to...
... access device may have different user attributes (such as username and password structure, service type, and rights), you need to configure ISP domains to access specific resources and records operations of users. If a user does not provide the ISP domain name, the system considers that enables authenticated and authorized entities to...
User Guide
Page 401
... the Type, Length, and Value fields. There are two kinds of authenticators: request authenticator and response authenticator. 5) The Attribute field, with a variable length, carries the specific authentication, authorization, and accounting information for matching request packets and response packets and detecting retransmitted request packets. The request and response packets of the same...
... the Type, Length, and Value fields. There are two kinds of authenticators: request authenticator and response authenticator. 5) The Attribute field, with a variable length, carries the specific authentication, authorization, and accounting information for matching request packets and response packets and detecting retransmitted request packets. The request and response packets of the same...