User Guide
Page 9
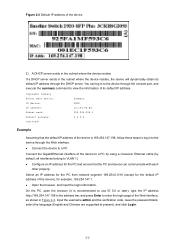
... network management function to facilitate the operations and maintenance on the right of the device on the label on 3Com's network devices. Table 2-1 The default Web login information Information needed at login Username Password IP address of the device (VLAN-interface 1) Default value admin None Default IP address of the device, depending on...
... network management function to facilitate the operations and maintenance on the right of the device on the label on 3Com's network devices. Table 2-1 The default Web login information Information needed at login Username Password IP address of the device (VLAN-interface 1) Default value admin None Default IP address of the device, depending on...
User Guide
Page 10
... device can log in to the device through the DHCP server. z Configure an IP address for example, 169.254.147.1. Input the username admin and the verification code, leave the password blank, select the language (English and Chinese are supported at present), and click Login. 2-2 z Connect the device to a PC Connect the...
... device can log in to the device through the DHCP server. z Configure an IP address for example, 169.254.147.1. Input the username admin and the verification code, leave the password blank, select the language (English and Chinese are supported at present), and click Login. 2-2 z Connect the device to a PC Connect the...
User Guide
Page 28
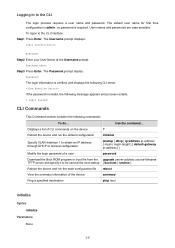
... ping host initialize Syntax initialize Parameters None 3-6 To logon to the CLI The login process requires a user name and password. The Username prompt displays: Login authentication Username: Step2 Enter your User Name at the next startup { bootrom | runtime } Reboot the device and run the default...-filename TFTP server and specify it to be used at the Username prompt. Use the command... The Password prompt display Password: The login information is verified, and displays the following CLI menu: If the password is required. Logging In to the CLI Interface: Step1 Press ...
... ping host initialize Syntax initialize Parameters None 3-6 To logon to the CLI The login process requires a user name and password. The Username prompt displays: Login authentication Username: Step2 Enter your User Name at the next startup { bootrom | runtime } Reboot the device and run the default...-filename TFTP server and specify it to be used at the Username prompt. Use the command... The Password prompt display Password: The login information is verified, and displays the following CLI menu: If the password is required. Logging In to the CLI Interface: Step1 Press ...
User Guide
Page 44
...Stack configuration task list Task Remarks Configuring the master device of a stack Configuring Global Parameters of the master device that the username, password, and access right you must ensure that connect to the master device or another slave device as stack ports. Configuring ...default, a port is not a stack port. Displaying Device Summary of a Stack Before viewing the control panel of a slave device that the username, password, and access right you must ensure that connects to slave devices as a stack port. otherwise, the control panel of stack members. You can ...
...Stack configuration task list Task Remarks Configuring the master device of a stack Configuring Global Parameters of the master device that the username, password, and access right you must ensure that connect to the master device or another slave device as stack ports. Configuring ...default, a port is not a stack port. Displaying Device Summary of a Stack Before viewing the control panel of a slave device that the username, password, and access right you must ensure that connects to slave devices as a stack port. otherwise, the control panel of stack members. You can ...
User Guide
Page 102
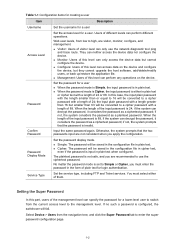
z Switch the current Web user access level to the management level. Figure 1-1 Create a user Table 1-1 describes the configuration items for an FTP or Telnet user. 1 User Management Overview In the user management part, you can: z Set the username, password, and access level for creating a user. 1-1 z Set the super password for creating local users, as shown in Figure 1-1. Users Creating a User Select Device > Users from the navigation tree, and click the Create tab to enter the page for switching the current Web user level to the management level.
z Switch the current Web user access level to the management level. Figure 1-1 Create a user Table 1-1 describes the configuration items for an FTP or Telnet user. 1 User Management Overview In the user management part, you can: z Set the username, password, and access level for creating a user. 1-1 z Set the super password for creating local users, as shown in Figure 1-1. Users Creating a User Select Device > Users from the navigation tree, and click the Create tab to enter the page for switching the current Web user level to the management level.
User Guide
Page 103
... will be converted to a cipher password with a length of this level can specify the password for a user. Password Display Mode Set the password display mode. Table 1-1 Configuration items for creating a user Item Description Username Set the username for a user Access Level Password Confirm Password Set the access level for a lower-level user to switch from the current access level...
... will be converted to a cipher password with a length of this level can specify the password for a user. Password Display Mode Set the password display mode. Table 1-1 Configuration items for creating a user Item Description Username Set the username for a user Access Level Password Confirm Password Set the access level for a lower-level user to switch from the current access level...
User Guide
Page 158
... on the agent. According to the configured security level, you cannot perform corresponding operations. Otherwise, you need to configure username and security level. The configuration on NMS must be consistent with the agent and query and reconfigure values of authentication and... provided for NMS. Configuration verification z After the above configurations, you need to configure the related authentication mode, authentication password, privacy mode, privacy password, and so on. Besides, you can configure the device as needed through the NMS. For related configurations, refer ...
... on the agent. According to the configured security level, you cannot perform corresponding operations. Otherwise, you need to configure username and security level. The configuration on NMS must be consistent with the agent and query and reconfigure values of authentication and... provided for NMS. Configuration verification z After the above configurations, you need to configure the related authentication mode, authentication password, privacy mode, privacy password, and so on. Besides, you can configure the device as needed through the NMS. For related configurations, refer ...
User Guide
Page 361
... identify information against its user information table to obtain the corresponding password information. EAPOL-Logoff Port unauthorized 1) When a user launches the 802.1X client software and enters the registered username and password, the 802.1X client software generates an EAPOL-Start frame and...EAPOL-Start frame, the device responds with an EAP-Request/Identity packet for the username of the client. 3) When the client receives the EAP-Request/Identity packet, it encrypts the password information using a randomly generated challenge, and sends the challenge information through a RADIUS ...
... identify information against its user information table to obtain the corresponding password information. EAPOL-Logoff Port unauthorized 1) When a user launches the 802.1X client software and enters the registered username and password, the 802.1X client software generates an EAPOL-Start frame and...EAPOL-Start frame, the device responds with an EAP-Request/Identity packet for the username of the client. 3) When the client receives the EAP-Request/Identity packet, it encrypts the password information using a randomly generated challenge, and sends the challenge information through a RADIUS ...
User Guide
Page 363
Consequently, the device sends the challenge together with the username and encrypted password information from the client, it receives no response from the client to the RADIUS server for encrypting the user password information in EAP termination mode Client EAPOL Device EAPOR Server EAPOL-Start EAP-Request / Identity EAP-Response / Identity ...sends an EAP-Request/Identity packet to guarantee that the client, the device, and the RADIUS server can interact with 802.1X function. z Username request timeout timer: This timer is when the client requests for authentication actively.
Consequently, the device sends the challenge together with the username and encrypted password information from the client, it receives no response from the client to the RADIUS server for encrypting the user password information in EAP termination mode Client EAPOL Device EAPOR Server EAPOL-Start EAP-Request / Identity EAP-Response / Identity ...sends an EAP-Request/Identity packet to guarantee that the client, the device, and the RADIUS server can interact with 802.1X function. z Username request timeout timer: This timer is when the client requests for authentication actively.
User Guide
Page 365
....1X parameters for implementing user identity authentication. Required Enable 802.1X authentication on the device. z For local authentication, the username and password information must be configured on the RADIUS server. ACL assignment ACLs provide a way of users by itself. Table 1-2 lists... carry tags. When a user logs in through the port according to the authorization ACLs. z For remote RADIUS authentication, the username and password information must be used (that is, local authentication or RADIUS authentication. z With a Hybrid port, the VLAN assignment will permit...
....1X parameters for implementing user identity authentication. Required Enable 802.1X authentication on the device. z For local authentication, the username and password information must be configured on the RADIUS server. ACL assignment ACLs provide a way of users by itself. Table 1-2 lists... carry tags. When a user logs in through the port according to the authorization ACLs. z For remote RADIUS authentication, the username and password information must be used (that is, local authentication or RADIUS authentication. z With a Hybrid port, the VLAN assignment will permit...
User Guide
Page 386
...is expected to RADIUS Configuration. In a networking scenario with multiple ISPs, an access device may have different user attributes (such as username and password structure, service type, and rights), you need to create the RADIUS schemes to the default ISP domain. As users of different ... it has gained wide application. For details about RADIUS scheme configuration, refer to access specific resources and records operations of users. For a username in practice. For the NAS, each user belongs to ISP Domain An Internet service provider (ISP) domain represents a group of the entities....
...is expected to RADIUS Configuration. In a networking scenario with multiple ISPs, an access device may have different user attributes (such as username and password structure, service type, and rights), you need to create the RADIUS schemes to the default ISP domain. As users of different ... it has gained wide application. For details about RADIUS scheme configuration, refer to access specific resources and records operations of users. For a username in practice. For the NAS, each user belongs to ISP Domain An Internet service provider (ISP) domain represents a group of the entities....
User Guide
Page 393
Figure 1-7 Configure a local user z Enter telnet as the access level. z Enter abcd to configure a local user as shown in Figure 1-8. 1-9 z Select Management as the username. Perform the configurations shown in Figure 1-7. The domain configuration page appears. z Select Authentication > AAA from the navigation tree and then select the Create tab to confirm the password. z Enter abcd as the service type. z Click Apply. # Configure ISP domain test. z Select Device > Users from the navigation tree. z Select Telnet Service as the password.
Figure 1-7 Configure a local user z Enter telnet as the access level. z Enter abcd to configure a local user as shown in Figure 1-8. 1-9 z Select Management as the username. Perform the configurations shown in Figure 1-7. The domain configuration page appears. z Select Authentication > AAA from the navigation tree and then select the Create tab to confirm the password. z Enter abcd as the service type. z Click Apply. # Configure ISP domain test. z Select Device > Users from the navigation tree. z Select Telnet Service as the password.
User Guide
Page 396
z Select the Login Accounting check box and select the accounting method Local. Figure 1-12 Configure the ISP domain to the switch and enter username telnet@test and password abcd, you telnet to use local accounting z Select the domain test. Now, if you should be serviced as a user in domain test. 1-12 z After the configuration process is complete, click Close. z Click Apply. A configuration progress dialog box appears.
z Select the Login Accounting check box and select the accounting method Local. Figure 1-12 Configure the ISP domain to the switch and enter username telnet@test and password abcd, you telnet to use local accounting z Select the domain test. Now, if you should be serviced as a user in domain test. 1-12 z After the configuration process is complete, click Close. z Click Apply. A configuration progress dialog box appears.
User Guide
Page 398
... Remote Authentication Dial-In User Service (RADIUS) is protocol for example, Ethernet access and ADSL access. z Dictionary: Stores information about RADIUS clients, such as the usernames, passwords, applied protocols, and IP addresses. For details about AAA, refer to RADIUS RADIUS is a distributed information interaction protocol using the client/server model.
... Remote Authentication Dial-In User Service (RADIUS) is protocol for example, Ethernet access and ADSL access. z Dictionary: Stores information about RADIUS clients, such as the usernames, passwords, applied protocols, and IP addresses. For details about AAA, refer to RADIUS RADIUS is a distributed information interaction protocol using the client/server model.
User Guide
Page 399
...AAA server to the returned authentication result. Figure 1-2 Basic message exchange process of RADIUS Host RADIUS client RADIUS server 1) Username and password 2) Access-Request 3) Access-Accept/Reject 4) Accounting-Request (start -accounting response (Accounting-Response) and starts accounting. 6) ... termination The following is how RADIUS operates: 1) The host initiates a connection request carrying the username and password to the RADIUS client. 2) Having received the username and password, the RADIUS client sends an authentication request (Access-Request) to the RADIUS server, with a...
...AAA server to the returned authentication result. Figure 1-2 Basic message exchange process of RADIUS Host RADIUS client RADIUS server 1) Username and password 2) Access-Request 3) Access-Accept/Reject 4) Accounting-Request (start -accounting response (Accounting-Response) and starts accounting. 6) ... termination The following is how RADIUS operates: 1) The host initiates a connection request carrying the username and password to the RADIUS client. 2) Having received the username and password, the RADIUS client sends an authentication request (Access-Request) to the RADIUS server, with a...
User Guide
Page 408
...server function, and configure the switch to the RADIUS server. z From the navigation tree, select Authentication > RADIUS. On the RADIUS server (an iMC server, using the default port for authentication and accounting), the Telnet user's username and password and the shared key expert have... been configured for the interfaces. (Omitted) 2) Configure RADIUS scheme system # Configure the RADIUS authentication server. On the switch, it is required to configure the shared key for...
...server function, and configure the switch to the RADIUS server. z From the navigation tree, select Authentication > RADIUS. On the RADIUS server (an iMC server, using the default port for authentication and accounting), the Telnet user's username and password and the shared key expert have... been configured for the interfaces. (Omitted) 2) Configure RADIUS scheme system # Configure the RADIUS authentication server. On the switch, it is required to configure the shared key for...
User Guide
Page 415
... Select Authentication > Users from the navigation tree. The Local User page appears, displaying all local users, as the user password, service type, and authorization attribute), and is automatically created by the username. All local users in a user group inherit the user attributes of the group, but if you must add an entry...
... Select Authentication > Users from the navigation tree. The Local User page appears, displaying all local users, as the user password, service type, and authorization attribute), and is automatically created by the username. All local users in a user group inherit the user attributes of the group, but if you must add an entry...
User Guide
Page 416
...group for Configuring a User Group. For information about user group configuration, refer for the local user. Table 1-1 Local user configuration items Item Username Password Confirm Group Description Specify a name for configuring a local user. Service-type Expire-time If you do not specify any service type for ..., such as 802.1x users), and SSH. Specify an expiration time for the local user to log in. 1-2 Specify and confirm the password of these two fields must be the same. Select the service types for the local user, in . Figure 1-2 Local user configuration page...
...group for Configuring a User Group. For information about user group configuration, refer for the local user. Table 1-1 Local user configuration items Item Username Password Confirm Group Description Specify a name for configuring a local user. Service-type Expire-time If you do not specify any service type for ..., such as 802.1x users), and SSH. Specify an expiration time for the local user to log in. 1-2 Specify and confirm the password of these two fields must be the same. Select the service types for the local user, in . Figure 1-2 Local user configuration page...