User Guide
Page 7
...Overview 1-1 2 Configuration Through the Web Interface 2-1 Web-Based Network Management Operating Environment 2-1 Logging In to the Web Interface 2-1 Default Login Information 2-1 Example 2-2 Logging Out of the Web Interface 2-3 Introduction to the Web Interface 2-3 Web User Level 2-4 Introduction...the Configuration Environment 3-1 Setting Terminal Parameters 3-2 Logging In to the CLI 3-6 CLI Commands 3-6 initialize 3-6 ipsetup 3-7 password 3-8 ping 3-8 quit 3-9 reboot 3-9 summary 3-10 upgrade 3-11 Configuration Example for Upgrading the Host Software Through the CLI 3-12 i
...Overview 1-1 2 Configuration Through the Web Interface 2-1 Web-Based Network Management Operating Environment 2-1 Logging In to the Web Interface 2-1 Default Login Information 2-1 Example 2-2 Logging Out of the Web Interface 2-3 Introduction to the Web Interface 2-3 Web User Level 2-4 Introduction...the Configuration Environment 3-1 Setting Terminal Parameters 3-2 Logging In to the CLI 3-6 CLI Commands 3-6 initialize 3-6 ipsetup 3-7 password 3-8 ping 3-8 quit 3-9 reboot 3-9 summary 3-10 upgrade 3-11 Configuration Example for Upgrading the Host Software Through the CLI 3-12 i
User Guide
Page 9
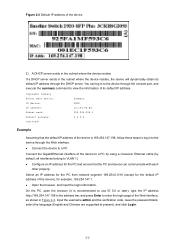
...at login Username Password IP address of the device (VLAN-interface 1) Default value admin None Default IP address of the device, depending on the status of the device rear panel, as shown in to log in Figure 2-2. The default subnet mask is provided with the default Web login information.... Figure 2-1 shows a Web-based network management operating environment. You can get the default IP address of the device on the label on 3Com's network devices. Figure 2-1 Web-based ...
...at login Username Password IP address of the device (VLAN-interface 1) Default value admin None Default IP address of the device, depending on the status of the device rear panel, as shown in to log in Figure 2-2. The default subnet mask is provided with the default Web login information.... Figure 2-1 shows a Web-based network management operating environment. You can get the default IP address of the device on the label on 3Com's network devices. Figure 2-1 Web-based ...
User Guide
Page 10
... is 169.254.147.198, follow these steps to log in to view the information of its default IP address through the Web interface. z Open the browser, and input the login information. Figure 2-2 Default IP address of the device 2) A DHCP server exists in the subnet where the device resides If... an IP address for example, 169.254.147.1. z Connect the device to VLAN 1). Input the username admin and the verification code, leave the password blank, select the language (English and Chinese are supported at present), and click Login. 2-2 You can communicate with each other properly.
... is 169.254.147.198, follow these steps to log in to view the information of its default IP address through the Web interface. z Open the browser, and input the login information. Figure 2-2 Default IP address of the device 2) A DHCP server exists in the subnet where the device resides If... an IP address for example, 169.254.147.1. z Connect the device to VLAN 1). Input the username admin and the verification code, leave the password blank, select the language (English and Chinese are supported at present), and click Login. 2-2 You can communicate with each other properly.
User Guide
Page 14
...mirroring group. Configure VCT VCT Check the status of the cables connected to the management level. Configure 2-6 Monitor Super Password Configure a password for collecting traffic statistics on the device, such as displaying the Manageme file list, downloading a file, uploading a ..., and clear alarm entries. Configure Initialize Restore the factory default settings. Modify FTP or Telnet user information. Interval Configurati on Set an interval for a lower-level user to switch from the current access level to Ethernet ports. Configure RMON...
...mirroring group. Configure VCT VCT Check the status of the cables connected to the management level. Configure 2-6 Monitor Super Password Configure a password for collecting traffic statistics on the device, such as displaying the Manageme file list, downloading a file, uploading a ..., and clear alarm entries. Configure Initialize Restore the factory default settings. Modify FTP or Telnet user information. Interval Configurati on Set an interval for a lower-level user to switch from the current access level to Ethernet ports. Configure RMON...
User Guide
Page 28
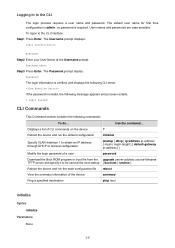
...the next startup { bootrom | runtime } Reboot the device and run the default configuration initialize Specify VLAN-interface 1 to be used at the Username prompt. Displays a list of a user password Download the Boot ROM program or boot file from the upgrade server-address source-...IP address through DHCP or manual configuration ipsetup { dhcp | ip address ip-address { mask | mask-length } [ default-gateway ip-address ] } Modify the login password of CLI commands on the device ? CLI Commands This Command section contains the following message appears and process restarts. % ...
...the next startup { bootrom | runtime } Reboot the device and run the default configuration initialize Specify VLAN-interface 1 to be used at the Username prompt. Displays a list of a user password Download the Boot ROM program or boot file from the upgrade server-address source-...IP address through DHCP or manual configuration ipsetup { dhcp | ip address ip-address { mask | mask-length } [ default-gateway ip-address ] } Modify the login password of CLI commands on the device ? CLI Commands This Command section contains the following message appears and process restarts. % ...
User Guide
Page 44
...control panel of the stack. Optional Log in Table 1-1 to the master device are the same with those configured on the slave device; By default, a port is not a stack port. Configuring slave devices of a stack Configuring Stack Ports Required Configure a port of a slave device from...the same with those configured on the slave device; Configuring Stack Ports Required Configure the ports of the master device that the username, password, and access right you cannot log into a slave device, you must ensure that connects to slave devices as a stack port. Configuring...
...control panel of the stack. Optional Log in Table 1-1 to the master device are the same with those configured on the slave device; By default, a port is not a stack port. Configuring slave devices of a stack Configuring Stack Ports Required Configure a port of a slave device from...the same with those configured on the slave device; Configuring Stack Ports Required Configure the ports of the master device that the username, password, and access right you cannot log into a slave device, you must ensure that connects to slave devices as a stack port. Configuring...
User Guide
Page 362
...when a client goes offline. 11) The client can also send an EAPOL-Logoff frame to the device to the client. By default, if two consecutive handshake attempts end up with failure, the device concludes that the client has gone offline and performs the necessary operations... shows the message exchange procedure with that generated by itself. 9) When receiving the RADIUS Access-Request packet, the RADIUS server compares the password information encapsulated in the packet with CHAP authentication. 1-7 After the client gets online, the device periodically sends handshake requests to the client to...
...when a client goes offline. 11) The client can also send an EAPOL-Logoff frame to the device to the client. By default, if two consecutive handshake attempts end up with failure, the device concludes that the client has gone offline and performs the necessary operations... shows the message exchange procedure with that generated by itself. 9) When receiving the RADIUS Access-Request packet, the RADIUS server compares the password information encapsulated in the packet with CHAP authentication. 1-7 After the client gets online, the device periodically sends handshake requests to the client to...
User Guide
Page 365
...RADIUS server is configured with 802.1X. Configuring 802.1X Configuration Task List 802.1X provides a method for the ports. By default, 802.1X authentication is disabled on a Port Description Required Enable 802.1X authentication globally and configure the authentication method and advanced... parameters. z For remote RADIUS authentication, the username and password information must be configured on the server, you need to network resources and defining access rights. By default, 802.1X authentication is disabled globally. RADIUS or local authentication must be...
...RADIUS server is configured with 802.1X. Configuring 802.1X Configuration Task List 802.1X provides a method for the ports. By default, 802.1X authentication is disabled on a Port Description Required Enable 802.1X authentication globally and configure the authentication method and advanced... parameters. z For remote RADIUS authentication, the username and password information must be configured on the server, you need to network resources and defining access rights. By default, 802.1X authentication is disabled globally. RADIUS or local authentication must be...
User Guide
Page 386
...name part the ISP domain name. Introduction to configure an accounting server. For details about RADIUS scheme configuration, refer to the default ISP domain. Configuring AAA Configuration Prerequisites 1) To deploy local authentication, you also need to ISP Domain An Internet service provider ...users of users. In a networking scenario with multiple ISPs, an access device may have different user attributes (such as username and password structure, service type, and rights), you need to configure different attribute sets including AAA methods for details. 2) To deploy remote ...
...name part the ISP domain name. Introduction to configure an accounting server. For details about RADIUS scheme configuration, refer to the default ISP domain. Configuring AAA Configuration Prerequisites 1) To deploy local authentication, you also need to ISP Domain An Internet service provider ...users of users. In a networking scenario with multiple ISPs, an access device may have different user attributes (such as username and password structure, service type, and rights), you need to configure different attribute sets including AAA methods for details. 2) To deploy remote ...
User Guide
Page 408
... is required to configure the shared key for packet exchange with the switch. On the RADIUS server (an iMC server, using the default port for authentication and accounting), the Telnet user's username and password and the shared key expert have been configured for RADIUS server configuration Configuration procedure Enable the Telnet server function...
... is required to configure the shared key for packet exchange with the switch. On the RADIUS server (an iMC server, using the default port for authentication and accounting), the Telnet user's username and password and the shared key expert have been configured for RADIUS server configuration Configuration procedure Enable the Telnet server function...
User Guide
Page 415
... of a group of local users and has a set of user attributes configured on a device (such as the user password, service type, and authorization attribute), and is automatically created by the username. By default, every newly added local user belongs to implement centralized management of the device. 1 Users Overview This module allows you...
... of a group of local users and has a set of user attributes configured on a device (such as the user password, service type, and authorization attribute), and is automatically created by the username. By default, every newly added local user belongs to implement centralized management of the device. 1 Users Overview This module allows you...
User Guide
Page 428
...CA root certificate verification occurs automatically and you need a long period of the root certificate content. LDAP IP Port Version Request Mode Password Encrypt Password Hash Fingerprint Polling Count Polling Interval Enable CRL Checking CRL Update Period Currently, this item is optional; In a PKI system, the ...hash value is usually addressed by yourself. The SCEP protocol is selected. In offline mode, this URL through the SCEP protocol. By default, the CRL update period depends on the next update field in manual mode. After an entity makes a certificate request, the CA may...
...CA root certificate verification occurs automatically and you need a long period of the root certificate content. LDAP IP Port Version Request Mode Password Encrypt Password Hash Fingerprint Polling Count Polling Interval Enable CRL Checking CRL Update Period Currently, this item is optional; In a PKI system, the ...hash value is usually addressed by yourself. The SCEP protocol is selected. In offline mode, this URL through the SCEP protocol. By default, the CRL update period depends on the next update field in manual mode. After an entity makes a certificate request, the CA may...