User Guide
Page 1
Copyright © 2012 ZyXEL Communications Corporation READ CAREFULLY BEFORE USE. ISG50 Integrated Service Gateway Default Login Details LAN IP Address https://192.168.1.1 User Name admin Password 1234 Version 2.30 Editionw3w,w.0zy5x/el2.c0om12 www.zyxel.com IMPORTANT! KEEP THIS GUIDE FOR FUTURE REFERENCE.
Copyright © 2012 ZyXEL Communications Corporation READ CAREFULLY BEFORE USE. ISG50 Integrated Service Gateway Default Login Details LAN IP Address https://192.168.1.1 User Name admin Password 1234 Version 2.30 Editionw3w,w.0zy5x/el2.c0om12 www.zyxel.com IMPORTANT! KEEP THIS GUIDE FOR FUTURE REFERENCE.
User Guide
Page 7
... Up Available Bandwidth on Ethernet Interfaces 111 7.3.2 Configure the WAN Trunk ...112 7.4 How to Set Up an IPSec VPN Tunnel 113 7.4.1 Set Up the VPN Gateway ...114 7.4.2 Set Up the VPN Connection 115 7.4.3 Configure Security Policies for the VPN Tunnel 116 7.5 How to Configure User-aware Access Control 116 7.5.1 Set Up...
... Up Available Bandwidth on Ethernet Interfaces 111 7.3.2 Configure the WAN Trunk ...112 7.4 How to Set Up an IPSec VPN Tunnel 113 7.4.1 Set Up the VPN Gateway ...114 7.4.2 Set Up the VPN Connection 115 7.4.3 Configure Security Policies for the VPN Tunnel 116 7.5 How to Configure User-aware Access Control 116 7.5.1 Set Up...
User Guide
Page 13
... Connection Screen ...370 24.2.1 The VPN Connection Add/Edit (IKE) Screen 371 24.2.2 The VPN Connection Add/Edit Manual Key Screen 377 24.3 The VPN Gateway Screen ...379 24.3.1 The VPN Gateway Add/Edit Screen 381 24.4 IPSec VPN Background Information 386 Chapter 25 Bandwidth Management...397...
... Connection Screen ...370 24.2.1 The VPN Connection Add/Edit (IKE) Screen 371 24.2.2 The VPN Connection Add/Edit Manual Key Screen 377 24.3 The VPN Gateway Screen ...379 24.3.1 The VPN Gateway Add/Edit Screen 381 24.4 IPSec VPN Background Information 386 Chapter 25 Bandwidth Management...397...
User Guide
Page 37
... you to call the telephones connected to the IP PBX. Telephones that convert voice into IP packets. C: VoIP Gateways - Devices (for example ZyXEL's P-2302HWUDL) with other SIP devices. Other SIP based IP PBXs with the ISG50. A: IP Phones - B: Softphones - SIP is an internationally-recognized standard for implementing Voice over an IP network. E: Peer...
... you to call the telephones connected to the IP PBX. Telephones that convert voice into IP packets. C: VoIP Gateways - Devices (for example ZyXEL's P-2302HWUDL) with other SIP devices. Other SIP based IP PBXs with the ISG50. A: IP Phones - B: Softphones - SIP is an internationally-recognized standard for implementing Voice over an IP network. E: Peer...
User Guide
Page 49
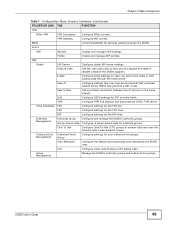
...or disable a feature the ISG50 supports. VPN Gateway Configure IKE tunnels. Fake IP Configure settings that may help avoid potential VoIP problems caused be the ISG50 being behind a NAT router.... LCR Configure Least Cost Routing (LCR) dialing rules. TAPI Configure TAPI line settings and download the ZYXEL TAPI driver. Extension Management Authority Group Configure and manage the ISG50's authority groups. ISG50...
...or disable a feature the ISG50 supports. VPN Gateway Configure IKE tunnels. Fake IP Configure settings that may help avoid potential VoIP problems caused be the ISG50 being behind a NAT router.... LCR Configure Least Cost Routing (LCR) dialing rules. TAPI Configure TAPI line settings and download the ZYXEL TAPI driver. Extension Management Authority Group Configure and manage the ISG50's authority groups. ISG50...
User Guide
Page 61
... these (in the previous screen. The Domain Name System (DNS) maps a domain name to configure DNS servers. ISG50 User's Guide 61 Figure 37 Internet Access: Ethernet Encapsulation • Encapsulation: This displays the type of Internet connection you are configuring. • First WAN...information exactly as the IP Address Assignment in the order you specify here) to resolve domain names for this WAN connection's IP address. • Gateway IP Address: Enter the IP address of a computer before you can access it. Auto displays if you selected Auto as given to which this ...
... these (in the previous screen. The Domain Name System (DNS) maps a domain name to configure DNS servers. ISG50 User's Guide 61 Figure 37 Internet Access: Ethernet Encapsulation • Encapsulation: This displays the type of Internet connection you are configuring. • First WAN...information exactly as the IP Address Assignment in the order you specify here) to resolve domain names for this WAN connection's IP address. • Gateway IP Address: Enter the IP address of a computer before you can access it. Auto displays if you selected Auto as given to which this ...
User Guide
Page 76
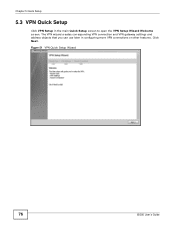
Figure 51 VPN Quick Setup Wizard 76 ISG50 User's Guide Click Next. The VPN wizard creates corresponding VPN connection and VPN gateway settings and address objects that you can use later in the main Quick Setup screen to open the VPN Setup Wizard Welcome screen. Chapter 5 Quick Setup 5.3 VPN Quick Setup Click VPN Setup in configuring more VPN connections or other features.
Figure 51 VPN Quick Setup Wizard 76 ISG50 User's Guide Click Next. The VPN wizard creates corresponding VPN connection and VPN gateway settings and address objects that you can use later in the main Quick Setup screen to open the VPN Setup Wizard Welcome screen. Chapter 5 Quick Setup 5.3 VPN Quick Setup Click VPN Setup in configuring more VPN connections or other features.
User Guide
Page 78
... initiate the VPN tunnel. You may use 1-31 alphanumeric characters, underscores (_), or dashes (-), but the first character cannot be a number. This ISG50 is case-sensitive. Select the scenario that best describes your intended VPN connection. Choose this if the remote IPSec device has a static IP address... dynamic IP addresses and are also known as shown in users. Choose this VPN connection (and VPN gateway). See Application Scenarios on page 369 for more on the scenarios. 78 ISG50 User's Guide Figure 53 VPN Express Wizard: Step 2 Rule Name: Type the name used to identify...
... initiate the VPN tunnel. You may use 1-31 alphanumeric characters, underscores (_), or dashes (-), but the first character cannot be a number. This ISG50 is case-sensitive. Select the scenario that best describes your intended VPN connection. Choose this if the remote IPSec device has a static IP address... dynamic IP addresses and are also known as shown in users. Choose this VPN connection (and VPN gateway). See Application Scenarios on page 369 for more on the scenarios. 78 ISG50 User's Guide Figure 53 VPN Express Wizard: Step 2 Rule Name: Type the name used to identify...
User Guide
Page 79
...this field, it is not configurable for the chosen scenario. If this field, it is not configurable for the chosen scenario. 5.5.1 VPN Express Wizard - ISG50 User's Guide 79 Use 0.0.0.0 if the remote IPSec router has a dynamic WAN IP address. • Pre-Shared Key: Type the password. You can... also specify a subnet. This must use the same password. Configuration Figure 54 VPN Express Wizard: Step 3 Chapter 5 Quick Setup • Secure Gateway: If Any displays in this field is not used on both ends. • Local Policy (IP/Mask): Type the IP address of a computer on ...
...this field, it is not configurable for the chosen scenario. If this field, it is not configurable for the chosen scenario. 5.5.1 VPN Express Wizard - ISG50 User's Guide 79 Use 0.0.0.0 if the remote IPSec router has a dynamic WAN IP address. • Pre-Shared Key: Type the password. You can... also specify a subnet. This must use the same password. Configuration Figure 54 VPN Express Wizard: Step 3 Chapter 5 Quick Setup • Secure Gateway: If Any displays in this field is not used on both ends. • Local Policy (IP/Mask): Type the IP address of a computer on ...
User Guide
Page 80
.... Then you can initiate the VPN connection. • Pre-Shared Key: VPN tunnel password. See the commands reference guide for Secure Gateway commands into another ISG50's command line interface to serve as a shell script file with a ".zysh" filename extension. Chapter 5 Quick Setup 5.5.2 VPN Express ...Wizard: Step 4 • Rule Name: Identifies the VPN gateway policy. • Secure Gateway: IP address or domain name of the computers on the commands displayed in order to run the script in this list. 80 ISG50 User's Guide If this VPN tunnel. If this field displays...
.... Then you can initiate the VPN connection. • Pre-Shared Key: VPN tunnel password. See the commands reference guide for Secure Gateway commands into another ISG50's command line interface to serve as a shell script file with a ".zysh" filename extension. Chapter 5 Quick Setup 5.5.2 VPN Express ...Wizard: Step 4 • Rule Name: Identifies the VPN gateway policy. • Secure Gateway: IP address or domain name of the computers on the commands displayed in order to run the script in this list. 80 ISG50 User's Guide If this VPN tunnel. If this field displays...
User Guide
Page 82
... be a number. Choose this if the remote IPSec device has a static IP address or a domain name. Choose this VPN connection (and VPN gateway). Scenario Click the Advanced radio button as dial-in user) and can initiate the VPN tunnel. • Site-to an IPSec server. This value... (dial-in users. The figure on page 77 to -site - This ISG50 can initiate the VPN tunnel. 82 ISG50 User's Guide Only the clients can initiate the VPN tunnel. • Remote Access (Server Role) - This ISG50 is case-sensitive. Select the scenario that best describes your intended VPN connection....
... be a number. Choose this if the remote IPSec device has a static IP address or a domain name. Choose this VPN connection (and VPN gateway). Scenario Click the Advanced radio button as dial-in user) and can initiate the VPN tunnel. • Site-to an IPSec server. This value... (dial-in users. The figure on page 77 to -site - This ISG50 can initiate the VPN tunnel. 82 ISG50 User's Guide Only the clients can initiate the VPN tunnel. • Remote Access (Server Role) - This ISG50 is case-sensitive. Select the scenario that best describes your intended VPN connection....
User Guide
Page 83
... Any displays in increased latency and decreased throughput. Note: Multiple SAs connecting through a secure gateway must know the same secret key, which can be used to allow more secure than 3DES. ISG50 User's Guide 83 AES128 uses a 128-bit key and is more incoming connections from the drop-... DH5 is faster than DH1 or DH2 (although it is configurable, enter the WAN IP address or domain name of the remote IPSec device (secure gateway) to use on DES that uses a 168-bit key. Triple DES (3DES) is more processing power, resulting in this may affect throughput). As ...
... Any displays in increased latency and decreased throughput. Note: Multiple SAs connecting through a secure gateway must know the same secret key, which can be used to allow more secure than 3DES. ISG50 User's Guide 83 AES128 uses a 128-bit key and is more incoming connections from the drop-... DH5 is faster than DH1 or DH2 (although it is configurable, enter the WAN IP address or domain name of the remote IPSec device (secure gateway) to use on DES that uses a 168-bit key. Triple DES (3DES) is more processing power, resulting in this may affect throughput). As ...
User Guide
Page 85
...; Secure Gateway: IP address or domain name of the remote IPSec device. • Pre-Shared Key: VPN tunnel password. • Certificate: The certificate the ISG50 uses to -site and remote access client role scenarios. DH5 is less secure. DH5 refers to save the VPN rule. DH2 ...enable PFS. Summary This is a read-only summary of a computer on the remote IPSec device. • Nailed-Up: This displays for Remote Gateway commands into another ISG50's command line interface. • Click Save to Diffie-Hellman Group 5 a 1536 bit random number (more secure than DH1 or DH2 (although ...
...; Secure Gateway: IP address or domain name of the remote IPSec device. • Pre-Shared Key: VPN tunnel password. • Certificate: The certificate the ISG50 uses to -site and remote access client role scenarios. DH5 is less secure. DH5 refers to save the VPN rule. DH2 ...enable PFS. Summary This is a read-only summary of a computer on the remote IPSec device. • Nailed-Up: This displays for Remote Gateway commands into another ISG50's command line interface. • Click Save to Diffie-Hellman Group 5 a 1536 bit random number (more secure than DH1 or DH2 (although ...
User Guide
Page 87
...the ISG50. • Section 6.2 on page 91 introduces the ISG50's object... ISG50. • Section 6.5 on page 94 covers the ISG50's... to the ISG50. Extensions fall...ISG50 and to route calls from the outside world to the ISG50. Extensions are used by other features. • Section 6.8 on page 104 introduces some terms related to the ISG50 via a VoIP gateway device. ISG50... User's Guide 87 After you configure the trunk, you configure the trunk. The following sections explain how these functions are performed on the ISG50...on the ISG50. 6.1.1.1 Call ...
...the ISG50. • Section 6.2 on page 91 introduces the ISG50's object... ISG50. • Section 6.5 on page 94 covers the ISG50's... to the ISG50. Extensions fall...ISG50 and to route calls from the outside world to the ISG50. Extensions are used by other features. • Section 6.8 on page 104 introduces some terms related to the ISG50 via a VoIP gateway device. ISG50... User's Guide 87 After you configure the trunk, you configure the trunk. The following sections explain how these functions are performed on the ISG50...on the ISG50. 6.1.1.1 Call ...
User Guide
Page 91
...to see Section 6.7 on an interface's IP address, subnet, or gateway. ISG50 User's Guide 91 When you change . For example, if you are configured and which configuration settings reference specific objects. For a list of the ISG50's features and settings. You use the object. If you change ... use these objects whenever the interface's IP address settings change an object's settings, the ISG50 automatically updates all the firewall and other settings that use them. The ISG50 automatically updates every rule or setting that uses objects, you can also usually select Create...
...to see Section 6.7 on an interface's IP address, subnet, or gateway. ISG50 User's Guide 91 When you change . For example, if you are configured and which configuration settings reference specific objects. For a list of the ISG50's features and settings. You use the object. If you change ... use these objects whenever the interface's IP address settings change an object's settings, the ISG50 automatically updates all the firewall and other settings that use them. The ISG50 automatically updates every rule or setting that uses objects, you can also usually select Create...
User Guide
Page 94
... policy (IPSec SA) Source NAT (SNAT) Trigger port, port triggering Address mapping Address mapping (VPN) Interface bandwidth management (outbound) General bandwidth management ISG50 FEATURE / TERM Virtual interface VPN gateway VPN connection Policy route Policy route Policy route IPSec VPN Interface Policy route 6.5 Packet Flow Here is as follows: Stateful Firewall ADP (PA...
... policy (IPSec SA) Source NAT (SNAT) Trigger port, port triggering Address mapping Address mapping (VPN) Interface bandwidth management (outbound) General bandwidth management ISG50 FEATURE / TERM Virtual interface VPN gateway VPN connection Policy route Policy route Policy route IPSec VPN Interface Policy route 6.5 Packet Flow Here is as follows: Stateful Firewall ADP (PA...
User Guide
Page 99
... comes in the order that you have an FTP server connected to limit the amount of interfaces and VPN tunnels. The ISG50 uses zones, not interfaces, in the DMZ zone). If you are using for your WAN connection. 1 Create an address...'s Guide 99 You want to the ISG50. Chapter 6 Configuration Basics PREREQUISITES Criteria: users, user groups, interfaces (incoming), IPSec VPN (incoming), addresses (source, destination), address groups (source, destination), schedules, services, service groups Next-hop: addresses (HOST gateway), IPSec VPN, trunks, interfaces NAT: addresses (translated ...
... comes in the order that you have an FTP server connected to limit the amount of interfaces and VPN tunnels. The ISG50 uses zones, not interfaces, in the DMZ zone). If you are using for your WAN connection. 1 Create an address...'s Guide 99 You want to the ISG50. Chapter 6 Configuration Basics PREREQUISITES Criteria: users, user groups, interfaces (incoming), IPSec VPN (incoming), addresses (source, destination), address groups (source, destination), schedules, services, service groups Next-hop: addresses (HOST gateway), IPSec VPN, trunks, interfaces NAT: addresses (translated ...
User Guide
Page 101
... ITEM(S) PREREQUISITES Configuration > Network > HTTP Redirect Interfaces Example: Suppose you want HTTP requests from which you forward to the proxy server. 6.6.11 ALG The ISG50's Application Layer Gateway (ALG) allows VoIP and FTP applications to go to a HTTP proxy server at IP address 192.168.3.80. 1 Click Configuration > Network > HTTP Redirect. 2 Add...
... ITEM(S) PREREQUISITES Configuration > Network > HTTP Redirect Interfaces Example: Suppose you want HTTP requests from which you forward to the proxy server. 6.6.11 ALG The ISG50's Application Layer Gateway (ALG) allows VoIP and FTP applications to go to a HTTP proxy server at IP address 192.168.3.80. 1 Click Configuration > Network > HTTP Redirect. 2 Add...
User Guide
Page 103
...policies, firewall, user settings (force user authentication) AAA server Authentication methods authentication methods VPN gateways (extended authentication), WWW (client authentication) certificates VPN gateways, WWW, SSH, FTP ISG50 User's Guide 103 MENU ITEM(S) PREREQUISITES Configuration > Anti-X > ADP Zones 6.7 Objects Objects... and user groups. Move your cursor over a configuration object that use this information in response to changes, the ISG50 automatically propagates the change through the features that has a magnifying-glass icon (such as a user group, address,...
...policies, firewall, user settings (force user authentication) AAA server Authentication methods authentication methods VPN gateways (extended authentication), WWW (client authentication) certificates VPN gateways, WWW, SSH, FTP ISG50 User's Guide 103 MENU ITEM(S) PREREQUISITES Configuration > Anti-X > ADP Zones 6.7 Objects Objects... and user groups. Move your cursor over a configuration object that use this information in response to changes, the ISG50 automatically propagates the change through the features that has a magnifying-glass icon (such as a user group, address,...
User Guide
Page 108
Figure 73 Configuration > Network > Interface > Port Roles Example 7.1.3 Configure Zones Do the following to assign the ISG50's wan1 interface a static IP address of 1.2.3.4. Click Configuration > Network > Interface > Ethernet and double-click the wan1 interface's entry. Chapter ...VPN zone. 1 Click Configuration > Network > Zone and then double-click the IPSec_VPN entry. 108 ISG50 User's Guide Select Use Fixed IP Address and configure the IP address, subnet mask, and default gateway settings and click OK. Figure 72 Configuration > Network > Interface > Ethernet > Edit wan1 7.1.2 ...
Figure 73 Configuration > Network > Interface > Port Roles Example 7.1.3 Configure Zones Do the following to assign the ISG50's wan1 interface a static IP address of 1.2.3.4. Click Configuration > Network > Interface > Ethernet and double-click the wan1 interface's entry. Chapter ...VPN zone. 1 Click Configuration > Network > Zone and then double-click the IPSec_VPN entry. 108 ISG50 User's Guide Select Use Fixed IP Address and configure the IP address, subnet mask, and default gateway settings and click OK. Figure 72 Configuration > Network > Interface > Ethernet > Edit wan1 7.1.2 ...