User Guide
Page 8
...Phones ...140 8.2 Auto Provisioning ...141 8.2.1 Configuring the snom VoIP Phones for Auto Provisioning 142 8.3 Making PSTN Calls ...143 8.3.1 The PSTN Connection ...143 8.3.2 Creating a Dialing Rule for PSTN 144 8.3.3 Assigning an LCR to an Authority Group 146 8.4 Making ITSP Calls ...147 8.4.1 The ITSP ... Connection ...155 8.5.2 Creating a Dialing Rule for ISDN 156 8.5.3 Assigning an LCR to an Authority Group 158 8.6 ISDN Network Configuration Examples 159 8.6.1 Example 1: Small/Medium Business 160 8.6.2 Example 2: Company with Existing PBX 161 8.6.3 Example 3: Company with Existing...
...Phones ...140 8.2 Auto Provisioning ...141 8.2.1 Configuring the snom VoIP Phones for Auto Provisioning 142 8.3 Making PSTN Calls ...143 8.3.1 The PSTN Connection ...143 8.3.2 Creating a Dialing Rule for PSTN 144 8.3.3 Assigning an LCR to an Authority Group 146 8.4 Making ITSP Calls ...147 8.4.1 The ITSP ... Connection ...155 8.5.2 Creating a Dialing Rule for ISDN 156 8.5.3 Assigning an LCR to an Authority Group 158 8.6 ISDN Network Configuration Examples 159 8.6.1 Example 1: Small/Medium Business 160 8.6.2 Example 2: Company with Existing PBX 161 8.6.3 Example 3: Company with Existing...
User Guide
Page 14
... Together 439 27.7 The QoS Screen ...440 27.8 The TAPI Screen ...442 27.8.1 Setting Up the TAPI Driver and Utility on Your Computer 443 27.9 Network Technical Reference ...447 Chapter 28 Voice Interfaces ...448 14...
... Together 439 27.7 The QoS Screen ...440 27.8 The TAPI Screen ...442 27.8.1 Setting Up the TAPI Driver and Utility on Your Computer 443 27.9 Network Technical Reference ...447 Chapter 28 Voice Interfaces ...448 14...
User Guide
Page 27
... a unique telephone number within an organization typically consisting of the following networks: • A traditional Public Switched Telephone Network (PSTN): ISG50-PSTN • An Internet connection to an Internet Telephony Service Provider (ITSP): all ISG50 models • An Integrated Services Digital Network/Basic Rate Interface Network (ISDN BRI): ISG50-ISDN Each telephone connected to an IP PBX has an extension...
... a unique telephone number within an organization typically consisting of the following networks: • A traditional Public Switched Telephone Network (PSTN): ISG50-PSTN • An Internet connection to an Internet Telephony Service Provider (ITSP): all ISG50 models • An Integrated Services Digital Network/Basic Rate Interface Network (ISDN BRI): ISG50-ISDN Each telephone connected to an IP PBX has an extension...
User Guide
Page 28
... Messaging (IM) and Peer to the PSTN, ITSP, or ISDN. The ISG50 also provides two separate LAN networks. It can also supplement a legacy PBX within an organization by dialing extensions. The ISG50 lets you set up the network and enforce security policies efficiently. See Chapter...company. Figure 1 IP PBX Example ITSP Internet ISG PPSSTTNN/ISDN The ISG50 can function as a transparent firewall in an existing network with the reliability of the ISG50's features. 1.1.2 Security and Routing The ISG50's security features include VPN, firewall, ADP (Anomaly Detection and Protection...
... Messaging (IM) and Peer to the PSTN, ITSP, or ISDN. The ISG50 also provides two separate LAN networks. It can also supplement a legacy PBX within an organization by dialing extensions. The ISG50 lets you set up the network and enforce security policies efficiently. See Chapter...company. Figure 1 IP PBX Example ITSP Internet ISG PPSSTTNN/ISDN The ISG50 can function as a transparent firewall in an existing network with the reliability of the ISG50's features. 1.1.2 Security and Routing The ISG50's security features include VPN, firewall, ADP (Anomaly Detection and Protection...
User Guide
Page 29
... protection for VPN connections and VoIP. 1.1.3.2 DMZ Installation Use the ISG50 with a USG, ZyXEL's Unified Threat Management (UTM) firewall to provide VoIP and security services. Security Services: • Firewall protected Internet access and DMZ network for publicly accessible servers. • IPSec VPN-secured VoIP services ..., or Google Voice to call recording to a USG model's DMZ, the ISG50 ISG50 User's Guide 29 Long distance calls (to C in the figure) use VoIP and local calls (to D) use PSTN or ISDN. • Auto attendant menu systems act as automatic switchboard operators to...
... protection for VPN connections and VoIP. 1.1.3.2 DMZ Installation Use the ISG50 with a USG, ZyXEL's Unified Threat Management (UTM) firewall to provide VoIP and security services. Security Services: • Firewall protected Internet access and DMZ network for publicly accessible servers. • IPSec VPN-secured VoIP services ..., or Google Voice to call recording to a USG model's DMZ, the ISG50 ISG50 User's Guide 29 Long distance calls (to C in the figure) use VoIP and local calls (to D) use PSTN or ISDN. • Auto attendant menu systems act as automatic switchboard operators to...
User Guide
Page 36
.... Wait for the device to shut down and powering up , checks the hardware, and starts the system processes. Chapter 1 Introducing the ISG50 Always use the reboot command. Clicking Maintenance > Shutdown > Shutdown or using the shutdown command Clicking Maintenance > Shutdown > Shutdown or using ...the shutdown command writes all cached data to network resources. 36 ISG50 User's Guide It does not stop or start . The ISG50 simply turns off the ISG50 or remove the power. The ISG50 does not stop the system processes or write cached data to the...
.... Wait for the device to shut down and powering up , checks the hardware, and starts the system processes. Chapter 1 Introducing the ISG50 Always use the reboot command. Clicking Maintenance > Shutdown > Shutdown or using the shutdown command Clicking Maintenance > Shutdown > Shutdown or using ...the shutdown command writes all cached data to network resources. 36 ISG50 User's Guide It does not stop or start . The ISG50 simply turns off the ISG50 or remove the power. The ISG50 does not stop the system processes or write cached data to the...
User Guide
Page 37
...and vice versa (for example ZyXEL's P-2024) aggregate a large number of the ISG50. 2.1 Features Voice over Internet Protocol (VoIP) Implementation The ISG50 uses SIP (Session Initiation Protocol)... to communicate with the ISG50. A: IP Phones - C: VoIP Gateways - B: Softphones - Software-based phones installed on PCs. Analog Telephone Adapters (for example ZyXEL's V-500). The following...their signal into IP packets. D: ATAs - ISG50 User's Guide 37 SIP is an internationally-recognized standard for example ZyXEL's P-2302HWUDL) with which allow traditional analog ...
...and vice versa (for example ZyXEL's P-2024) aggregate a large number of the ISG50. 2.1 Features Voice over Internet Protocol (VoIP) Implementation The ISG50 uses SIP (Session Initiation Protocol)... to communicate with the ISG50. A: IP Phones - C: VoIP Gateways - B: Softphones - Software-based phones installed on PCs. Analog Telephone Adapters (for example ZyXEL's V-500). The following...their signal into IP packets. D: ATAs - ISG50 User's Guide 37 SIP is an internationally-recognized standard for example ZyXEL's P-2302HWUDL) with which allow traditional analog ...
User Guide
Page 38
... as attachments when they receive voicemail. For example you to set up the ISG50 to IP phones on the Internet or traditional phones on your network. • Set up and manage features on an internal telephone network without relying on the PSTN. Adding a USB hard disk to provide intercom (calling by : • A - Figure 12...
... as attachments when they receive voicemail. For example you to set up the ISG50 to IP phones on the Internet or traditional phones on your network. • Set up and manage features on an internal telephone network without relying on the PSTN. Adding a USB hard disk to provide intercom (calling by : • A - Figure 12...
User Guide
Page 39
... extensions anywhere in tandem with that you to distribute incoming calls to specific groups of the ISG50's extensions. Connecting several ISG50s together to your telephone network. Figure 13 Scalable Design ITSP ISG ISG ISG Automatic Call Distribution Automatic Call Distribution (ACD)... assigned skill sets. Next, it assigns the call by the ISG50 administrator and constitute a set up one of phones connected to manage a larger telephone network. High Availability To ensure the ISG50 provides reliable, secure Internet access, set of telecommunications device they are...
... extensions anywhere in tandem with that you to distribute incoming calls to specific groups of the ISG50's extensions. Connecting several ISG50s together to your telephone network. Figure 13 Scalable Design ITSP ISG ISG ISG Automatic Call Distribution Automatic Call Distribution (ACD)... assigned skill sets. Next, it assigns the call by the ISG50 administrator and constitute a set up one of phones connected to manage a larger telephone network. High Availability To ensure the ISG50 provides reliable, secure Internet access, set of telecommunications device they are...
User Guide
Page 40
Figure 14 Applications: Multiple WAN Interfaces ISG Virtual Private Networks (VPN) Use IPSec VPN to the Internet on the same port, or set up multiple connections on different ports. In either case, you can balance the loads between two sites over the Internet or any insecure network that uses TCP/IP for communication. The ISG50 also offers hub-and-spoke IPSec VPN. Set up VPN tunnels with other companies, branch offices, telecommuters, and business 40 ISG50 User's Guide Chapter 2 Features and Applications Set up multiple connections to provide secure communication between them.
Figure 14 Applications: Multiple WAN Interfaces ISG Virtual Private Networks (VPN) Use IPSec VPN to the Internet on the same port, or set up multiple connections on different ports. In either case, you can balance the loads between two sites over the Internet or any insecure network that uses TCP/IP for communication. The ISG50 also offers hub-and-spoke IPSec VPN. Set up VPN tunnels with other companies, branch offices, telecommuters, and business 40 ISG50 User's Guide Chapter 2 Features and Applications Set up multiple connections to provide secure communication between them.
User Guide
Page 41
ISG50 User's Guide 41 As a result, it is much simpler to set up and to provide better service. You can create your network. You can add interfaces and VPN tunnels to your own custom zones. Figure 15 Applications: VPN Connectivity ISG Flexible Security Zones Many security settings are made by zone, not by interface, port, or network. You can also set up additional connections to the Internet to change security settings in the ISG50. Chapter 2 Features and Applications travelers to provide secure access to zones.
ISG50 User's Guide 41 As a result, it is much simpler to set up and to provide better service. You can create your network. You can add interfaces and VPN tunnels to your own custom zones. Figure 15 Applications: VPN Connectivity ISG Flexible Security Zones Many security settings are made by zone, not by interface, port, or network. You can also set up additional connections to the Internet to change security settings in the ISG50. Chapter 2 Features and Applications travelers to provide secure access to zones.
User Guide
Page 42
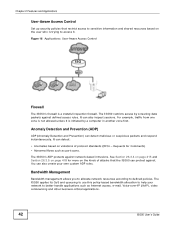
...data packets against defined access rules. Requests for more on the kinds of protocol standards (RFCs - It can also create your network to defined policies. The ISG50's ADP protects against . See Section 26.3.4 on page 415 and Section 26.3.5 on the user who is a stateful inspection...from one zone is not allowed unless it . Bandwidth Management Bandwidth management allows you to allocate network resources according to better handle applications such as port scans. The ISG50 applies its QoS and queueing to use this policy-based bandwidth allocation to help your own custom...
...data packets against defined access rules. Requests for more on the kinds of protocol standards (RFCs - It can also create your network to defined policies. The ISG50's ADP protects against . See Section 26.3.4 on page 415 and Section 26.3.5 on the user who is a stateful inspection...from one zone is not allowed unless it . Bandwidth Management Bandwidth management allows you to allocate network resources according to better handle applications such as port scans. The ISG50 applies its QoS and queueing to use this policy-based bandwidth allocation to help your own custom...
User Guide
Page 48
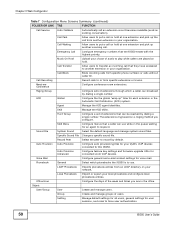
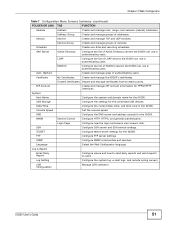
... ports as LAN1 or DMZ. Licensing Registration Registration Register the device and activate trial services. Network Interface Port Role Use this screen to configure the ISG50's features. Cellular Configure a cellular Internet connection for Automatic Call Distribution (ACD) agents. Static Route Create and manage IP static routing information. ALG Configure H.323 and ...
... ports as LAN1 or DMZ. Licensing Registration Registration Register the device and activate trial services. Network Interface Port Role Use this screen to configure the ISG50's features. Cellular Configure a cellular Internet connection for Automatic Call Distribution (ACD) agents. Static Route Create and manage IP static routing information. ALG Configure H.323 and ...
User Guide
Page 50
...File Change a specific sound file. Local Phonebook Import or export your ZyXEL VoIP devices connected to transfer an incoming call . Call Recording Record calls to force user authentication. 50 ISG50 User's Guide Meet-me Conference Configure conference room extensions. Group Create ... in the office. Call Transfer Allow users to this ISG50. Skill Manage the ACD skills. LDAP Phonebook Imports phonebook entries from another extension in your organization. Music On Hold Upload your network. Hunt Group Configure a set of audio to another incoming...
...File Change a specific sound file. Local Phonebook Import or export your ZyXEL VoIP devices connected to transfer an incoming call . Call Recording Record calls to force user authentication. 50 ISG50 User's Guide Meet-me Conference Configure conference room extensions. Group Create ... in the office. Call Transfer Allow users to this ISG50. Skill Manage the ACD skills. LDAP Phonebook Imports phonebook entries from another extension in your organization. Music On Hold Upload your network. Hunt Group Configure a set of audio to another incoming...
User Guide
Page 51
... ISG50....collection. LDAP Configure the list of RADIUS servers the ISG50 can use in authenticating users. FTP Configure FTP server ...UDP services. USB Storage Configure the settings for the ISG50. Date/Time Configure the current date, time, and...LDAP servers the ISG50 can use in authenticating users. SSH Configure SSH...manage the ISG50's certificates. Console Speed Set the console speed. Language Select the Web Configurator language. ISG50 User's.... TELNET Configure telnet server settings for the ISG50. Chapter 3 Web Configurator Table 7 Configuration Menu Screens Summary ...
... ISG50....collection. LDAP Configure the list of RADIUS servers the ISG50 can use in authenticating users. FTP Configure FTP server ...UDP services. USB Storage Configure the settings for the ISG50. Date/Time Configure the current date, time, and...LDAP servers the ISG50 can use in authenticating users. SSH Configure SSH...manage the ISG50's certificates. Console Speed Set the console speed. Language Select the Web Configurator language. ISG50 User's.... TELNET Configure telnet server settings for the ISG50. Chapter 3 Web Configurator Table 7 Configuration Menu Screens Summary ...
User Guide
Page 69
See Section 5.2 on page 70. • VPN SETUP Use VPN SETUP to configure a VPN (Virtual Private Network) tunnel for background information. CHAPTER 5 Quick Setup 5.1 Quick Setup Overview The Web Configurator's quick setup wizards help you use PPPoE or PPTP.... connection to set up a WAN (Internet) connection. This wizard creates matching ISP account settings in the ISG50 if you configure Internet and VPN connection settings. This chapter provides information on page 77. ISG50 User's Guide 69 In the Web Configurator, click Configuration > Quick Setup to open a wizard to another...
See Section 5.2 on page 70. • VPN SETUP Use VPN SETUP to configure a VPN (Virtual Private Network) tunnel for background information. CHAPTER 5 Quick Setup 5.1 Quick Setup Overview The Web Configurator's quick setup wizards help you use PPPoE or PPTP.... connection to set up a WAN (Internet) connection. This wizard creates matching ISP account settings in the ISG50 if you configure Internet and VPN connection settings. This chapter provides information on page 77. ISG50 User's Guide 69 In the Web Configurator, click Configuration > Quick Setup to open a wizard to another...
User Guide
Page 77
...-shared key and default security settings. The VPN connection can be to another computer, smartphone, or network. Chapter 5 Quick Setup 5.4 VPN Setup Wizard: Wizard Type A VPN (Virtual Private Network) tunnel is a secure connection to another ISG50 or other IPSec device. Advanced: Use this wizard to configure. Use this screen to select which type...
...-shared key and default security settings. The VPN connection can be to another computer, smartphone, or network. Chapter 5 Quick Setup 5.4 VPN Setup Wizard: Wizard Type A VPN (Virtual Private Network) tunnel is a secure connection to another ISG50 or other IPSec device. Advanced: Use this wizard to configure. Use this screen to select which type...
User Guide
Page 79
... of the remote IPSec device (secure gateway) to 31 pairs of the VPN tunnel must match the local IP address configured on your network. You can also specify a subnet. ISG50 User's Guide 79 5.5.1 VPN Express Wizard - Configuration Figure 54 VPN Express Wizard: Step 3 Chapter 5 Quick Setup • Secure Gateway: If Any displays...
... of the remote IPSec device (secure gateway) to 31 pairs of the VPN tunnel must match the local IP address configured on your network. You can also specify a subnet. ISG50 User's Guide 79 5.5.1 VPN Express Wizard - Configuration Figure 54 VPN Express Wizard: Step 3 Chapter 5 Quick Setup • Secure Gateway: If Any displays...
User Guide
Page 80
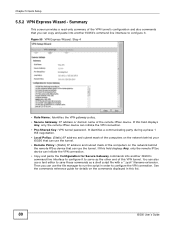
...identifies a communicating party during a phase 1 IKE negotiation. • Local Policy: (Static) IP address and subnet mask of the computers on the network behind your ISG50 that can use the tunnel. • Remote Policy: (Static) IP address and subnet mask of the VPN tunnel's configuration and also commands that...field displays Any, only the remote IPSec device can initiate the VPN connection. • Copy and paste the Configuration for details on the network behind the remote IPSec device that you can also use a text editor to configure the VPN connection. You can use the tunnel. ...
...identifies a communicating party during a phase 1 IKE negotiation. • Local Policy: (Static) IP address and subnet mask of the computers on the network behind your ISG50 that can use the tunnel. • Remote Policy: (Static) IP address and subnet mask of the VPN tunnel's configuration and also commands that...field displays Any, only the remote IPSec device can initiate the VPN connection. • Copy and paste the Configuration for details on the network behind the remote IPSec device that you can also use a text editor to configure the VPN connection. You can use the tunnel. ...
User Guide
Page 85
... on the remote IPSec device. • Remote Policy (IP/Mask): Type the IP address of a computer behind your network. Select DH1, DH2 or DH5 to have the ISG50 automatically renegotiate the IPSec SA when the SA life time expires. 5.5.7 VPN Advanced Wizard - You can also specify a ...VPN rule. Summary This is less secure. Select this to enable PFS. This must match the remote IP address configured on the network behind the remote IPSec device. ISG50 User's Guide 85 Chapter 5 Quick Setup • Perfect Forward Secrecy (PFS): Disabling PFS allows faster IPSec setup, but is...
... on the remote IPSec device. • Remote Policy (IP/Mask): Type the IP address of a computer behind your network. Select DH1, DH2 or DH5 to have the ISG50 automatically renegotiate the IPSec SA when the SA life time expires. 5.5.7 VPN Advanced Wizard - You can also specify a ...VPN rule. Summary This is less secure. Select this to enable PFS. This must match the remote IP address configured on the network behind the remote IPSec device. ISG50 User's Guide 85 Chapter 5 Quick Setup • Perfect Forward Secrecy (PFS): Disabling PFS allows faster IPSec setup, but is...