User Guide
Page 5
Table of Contents Table of Contents Contents Overview ...3 Table of Contents ...5 Part I: User's Guide 25 Chapter 1 Introducing the ISG50 ...27 1.1 Overview ...27 1.1.1 PBX ...27 1.1.2 Security and Routing ...28 1.1.3 Application Scenarios ...28 1.2 Rack-mounted Installation ...31 1.2.1 Rack-Mounted Installation Procedure 32 1.3 Connecting the Frame Ground ...32 1.4 Front Panel ...33 1.4.1 Front Panel ...
Table of Contents Table of Contents Contents Overview ...3 Table of Contents ...5 Part I: User's Guide 25 Chapter 1 Introducing the ISG50 ...27 1.1 Overview ...27 1.1.1 PBX ...27 1.1.2 Security and Routing ...28 1.1.3 Application Scenarios ...28 1.2 Rack-mounted Installation ...31 1.2.1 Rack-Mounted Installation Procedure 32 1.3 Connecting the Frame Ground ...32 1.4 Front Panel ...33 1.4.1 Front Panel ...
User Guide
Page 7
... WAN Trunk ...112 7.4 How to Set Up an IPSec VPN Tunnel 113 7.4.1 Set Up the VPN Gateway ...114 7.4.2 Set Up the VPN Connection 115 7.4.3 Configure Security Policies for the VPN Tunnel 116 7.5 How to Configure User-aware Access Control 116 7.5.1 Set Up User Accounts ...117...
... WAN Trunk ...112 7.4 How to Set Up an IPSec VPN Tunnel 113 7.4.1 Set Up the VPN Gateway ...114 7.4.2 Set Up the VPN Connection 115 7.4.3 Configure Security Policies for the VPN Tunnel 116 7.5 How to Configure User-aware Access Control 116 7.5.1 Set Up User Accounts ...117...
User Guide
Page 9
... 163 8.8 Using the Extension Portal ...164 8.8.1 Your Information ...164 8.8.2 Accessing the Extension Portal 164 8.8.3 Using the Web Phone (IP Phone Users Only 165 8.8.4 Changing Your Security Information 166 8.8.5 Personalizing Your Settings 167 8.8.6 Setting Up Voicemail ...170 8.9 Capturing Packets Using the Web Configurator 171 8.10 Creating an Automated Menu System 173 8.10... Screen 197 10.3 Interface Status Screen ...198 10.4 The Traffic Statistics Screen ...200 10.5 The Session Monitor Screen ...203 10.6 The DDNS Status Screen ...205 ISG50 User's Guide 9
... 163 8.8 Using the Extension Portal ...164 8.8.1 Your Information ...164 8.8.2 Accessing the Extension Portal 164 8.8.3 Using the Web Phone (IP Phone Users Only 165 8.8.4 Changing Your Security Information 166 8.8.5 Personalizing Your Settings 167 8.8.6 Setting Up Voicemail ...170 8.9 Capturing Packets Using the Web Configurator 171 8.10 Creating an Automated Menu System 173 8.10... Screen 197 10.3 Interface Status Screen ...198 10.4 The Traffic Statistics Screen ...200 10.5 The Session Monitor Screen ...203 10.6 The DDNS Status Screen ...205 ISG50 User's Guide 9
User Guide
Page 22
Table of Contents 52.8.4 Configuring SSH ...695 52.8.5 Secure Telnet Using SSH Examples 696 52.9 Telnet ...698 52.9.1 Configuring Telnet ...698 52.10 FTP ...699 52.10.1 Configuring FTP ...699 52.11 SNMP ...700 ... Know ...725 55.2 The Configuration File Screen ...727 55.3 The Firmware Package Screen ...731 55.4 The Shell Script Screen ...733 Chapter 56 Diagnostics ...737 22 ISG50 User's Guide
Table of Contents 52.8.4 Configuring SSH ...695 52.8.5 Secure Telnet Using SSH Examples 696 52.9 Telnet ...698 52.9.1 Configuring Telnet ...698 52.10 FTP ...699 52.10.1 Configuring FTP ...699 52.11 SNMP ...700 ... Know ...725 55.2 The Configuration File Screen ...727 55.3 The Firmware Package Screen ...731 55.4 The Shell Script Screen ...733 Chapter 56 Diagnostics ...737 22 ISG50 User's Guide
User Guide
Page 27
..., and PBX stands for reliable, secure voice and data service. 1.1.1 PBX An IP PBX is a unique telephone number within an organization typically consisting of the following networks: • A traditional Public Switched Telephone Network (PSTN): ISG50-PSTN • An Internet connection to an... Internet Telephony Service Provider (ITSP): all ISG50 models • An Integrated Services Digital Network/Basic Rate Interface Network (ISDN BRI): ISG50-ISDN Each telephone connected to an IP...
..., and PBX stands for reliable, secure voice and data service. 1.1.1 PBX An IP PBX is a unique telephone number within an organization typically consisting of the following networks: • A traditional Public Switched Telephone Network (PSTN): ISG50-PSTN • An Internet connection to an... Internet Telephony Service Provider (ITSP): all ISG50 models • An Integrated Services Digital Network/Basic Rate Interface Network (ISDN BRI): ISG50-ISDN Each telephone connected to an IP...
User Guide
Page 28
...an existing network with the reliability of the ISG50's features. 1.1.2 Security and Routing The ISG50's security features include VPN, firewall, ADP (Anomaly Detection and Protection), and certificates. See Chapter 2 on page 37 for a small organization. The ISG50 lets you can deploy the ISG50 as a stand alone telephone switchboard for ...ports for a more detailed overview of the LAN1, or DMZ. Flexible configuration helps you set ports to the PSTN, ITSP, or ISDN. The ISG50 also provides two separate LAN networks. Calls to the outside world go through the IP PBX to be part ...
...an existing network with the reliability of the ISG50's features. 1.1.2 Security and Routing The ISG50's security features include VPN, firewall, ADP (Anomaly Detection and Protection), and certificates. See Chapter 2 on page 37 for a small organization. The ISG50 lets you can deploy the ISG50 as a stand alone telephone switchboard for ...ports for a more detailed overview of the LAN1, or DMZ. Flexible configuration helps you set ports to the PSTN, ITSP, or ISDN. The ISG50 also provides two separate LAN networks. Calls to the outside world go through the IP PBX to be part ...
User Guide
Page 29
... access and DMZ network for publicly accessible servers. • IPSec VPN-secured VoIP services and internal server access for VPN connections and VoIP. 1.1.3.2 DMZ Installation Use the ISG50 with a USG, ZyXEL's Unified Threat Management (UTM) firewall to add more security services like B) use PSTN or ISDN. • Auto attendant menu systems act as automatic switchboard...
... access and DMZ network for publicly accessible servers. • IPSec VPN-secured VoIP services and internal server access for VPN connections and VoIP. 1.1.3.2 DMZ Installation Use the ISG50 with a USG, ZyXEL's Unified Threat Management (UTM) firewall to add more security services like B) use PSTN or ISDN. • Auto attendant menu systems act as automatic switchboard...
User Guide
Page 30
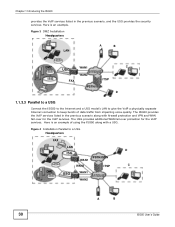
... with a USG. Here is an example of data traffic from impacting voice quality. The ISG50 provides the VoIP services listed in the previous scenario, and the USG provides the security services. The USG provides additional WAN fail-over for the VoIP services. Here is an example. ...Figure 3 DMZ Installation Headquarters LAN A B DMZ USG WAN1 C ISG WAN2 FAX ITSP PSTN/ISDN D 1.1.3.3 Parallel to a USG Connect the ISG50 to the Internet and a...
... with a USG. Here is an example of data traffic from impacting voice quality. The ISG50 provides the VoIP services listed in the previous scenario, and the USG provides the security services. The USG provides additional WAN fail-over for the VoIP services. Here is an example. ...Figure 3 DMZ Installation Headquarters LAN A B DMZ USG WAN1 C ISG WAN2 FAX ITSP PSTN/ISDN D 1.1.3.3 Parallel to a USG Connect the ISG50 to the Internet and a...
User Guide
Page 31
... In addition to one of the application scenarios already described, you can also use site-to-site VPNs to connect ISG50s at offices in the US and Germany, if someone in the US office needs to call someone in Germany, you can be mounted on a standard ... make the rack unstable or top-heavy. Take all the equipment it gets billed as a local German call. This allows peer to anchor the rack securely before installing the unit. Note: Leave 10 cm of all necessary precautions to peer VoIP calling and faxes over IP without using a rackmounting kit. Make...
... In addition to one of the application scenarios already described, you can also use site-to-site VPNs to connect ISG50s at offices in the US and Germany, if someone in the US office needs to call someone in Germany, you can be mounted on a standard ... make the rack unstable or top-heavy. Take all the equipment it gets billed as a local German call. This allows peer to anchor the rack securely before installing the unit. Note: Leave 10 cm of all necessary precautions to peer VoIP calling and faxes over IP without using a rackmounting kit. Make...
User Guide
Page 32
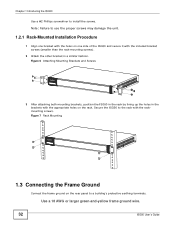
... the rack by lining up the holes in a similar fashion. Use a 18 AWG or larger green-and-yellow frame ground wire. 32 ISG50 User's Guide Note: Failure to the rack with the included bracket screws (smaller than the rack-mounting screws). 2 Attach the other bracket ...the brackets with the appropriate holes on one bracket with the holes on the rack. Secure the ISG50 to use the proper screws may damage the unit. 1.2.1 Rack-Mounted Installation Procedure 1 Align one side of the ISG50 and secure it with the rackmounting screws. Figure 7 Rack Mounting 1.3 Connecting the Frame Ground ...
... the rack by lining up the holes in a similar fashion. Use a 18 AWG or larger green-and-yellow frame ground wire. 32 ISG50 User's Guide Note: Failure to the rack with the included bracket screws (smaller than the rack-mounting screws). 2 Attach the other bracket ...the brackets with the appropriate holes on one bracket with the holes on the rack. Secure the ISG50 to use the proper screws may damage the unit. 1.2.1 Rack-Mounted Installation Procedure 1 Align one side of the ISG50 and secure it with the rackmounting screws. Figure 7 Rack Mounting 1.3 Connecting the Frame Ground ...
User Guide
Page 39
...-Based Routing (SBR). Click-To-Talk The Click-To-Talk (CTT) feature allows you to manage a larger telephone network. High Availability To ensure the ISG50 provides reliable, secure Internet access, set of rules that the end user can then be on the move and still receive calls sent to groups of the...
...-Based Routing (SBR). Click-To-Talk The Click-To-Talk (CTT) feature allows you to manage a larger telephone network. High Availability To ensure the ISG50 provides reliable, secure Internet access, set of rules that the end user can then be on the move and still receive calls sent to groups of the...
User Guide
Page 40
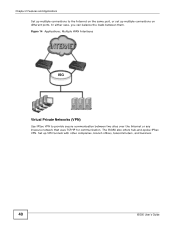
Chapter 2 Features and Applications Set up multiple connections to provide secure communication between them. Figure 14 Applications: Multiple WAN Interfaces ISG Virtual Private Networks (VPN) Use IPSec VPN to the Internet on different ports. The ISG50 also offers hub-and-spoke IPSec VPN. Set up multiple connections... on the same port, or set up VPN tunnels with other companies, branch offices, telecommuters, and business 40 ISG50 User's Guide In either case, you can balance the loads between two sites over the Internet or any insecure network that uses TCP...
Chapter 2 Features and Applications Set up multiple connections to provide secure communication between them. Figure 14 Applications: Multiple WAN Interfaces ISG Virtual Private Networks (VPN) Use IPSec VPN to the Internet on different ports. The ISG50 also offers hub-and-spoke IPSec VPN. Set up multiple connections... on the same port, or set up VPN tunnels with other companies, branch offices, telecommuters, and business 40 ISG50 User's Guide In either case, you can balance the loads between two sites over the Internet or any insecure network that uses TCP...
User Guide
Page 41
Figure 15 Applications: VPN Connectivity ISG Flexible Security Zones Many security settings are made by zone, not by interface, port, or network. ISG50 User's Guide 41 You can also set up additional connections to the Internet to provide better service. You can create your network. You can add interfaces and VPN tunnels to change security settings in the ISG50. Chapter 2 Features and Applications travelers to provide secure access to your own custom zones. As a result, it is much simpler to set up and to zones.
Figure 15 Applications: VPN Connectivity ISG Flexible Security Zones Many security settings are made by zone, not by interface, port, or network. ISG50 User's Guide 41 You can also set up additional connections to the Internet to provide better service. You can create your network. You can add interfaces and VPN tunnels to change security settings in the ISG50. Chapter 2 Features and Applications travelers to provide secure access to your own custom zones. As a result, it is much simpler to set up and to zones.
User Guide
Page 42
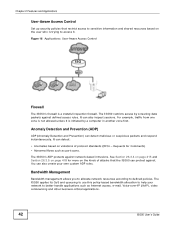
... User-Aware Access Control Set up security policies that the ISG50 can protect against network-based intrusions. For example, traffic from one zone is not allowed unless it . Figure 16 Applications: User-Aware Access Control ISG Firewall The ISG50's firewall is trying to access it...information and shared resources based on violations of attacks that restrict access to better handle applications such as port scans. The ISG50 restricts access by a computer in another zone first. Bandwidth Management Bandwidth management allows you to allocate network resources according to...
... User-Aware Access Control Set up security policies that the ISG50 can protect against network-based intrusions. For example, traffic from one zone is not allowed unless it . Figure 16 Applications: User-Aware Access Control ISG Firewall The ISG50's firewall is trying to access it...information and shared resources based on violations of attacks that restrict access to better handle applications such as port scans. The ISG50 restricts access by a computer in another zone first. Bandwidth Management Bandwidth management allows you to allocate network resources according to...
User Guide
Page 60
... to Auto. This option appears when you are configuring the first WAN interface. • Encapsulation: Choose the Ethernet option when the WAN port is the security zone to configure two Internet connections. Use this option to which this interface and Internet connection belong. • IP Address Assignment: Select Auto if your...
... to Auto. This option appears when you are configuring the first WAN interface. • Encapsulation: Choose the Ethernet option when the WAN port is the security zone to configure two Internet connections. Use this option to which this interface and Internet connection belong. • IP Address Assignment: Select Auto if your...
User Guide
Page 61
...First WAN Interface: This is the number of the interface that will connect with your (static) public IP address. The DNS server is the security zone to which this interface and Internet connection will send traffic (the default gateway). • First / Second DNS Server: These fields display if... you selected static IP address assignment. • IP Subnet Mask: Enter the subnet mask for VPN, DDNS and the time server. The ISG50 uses these (in the previous screen. Figure 37 Internet Access: Ethernet Encapsulation • Encapsulation: This displays the type of Internet connection you ...
...First WAN Interface: This is the number of the interface that will connect with your (static) public IP address. The DNS server is the security zone to which this interface and Internet connection will send traffic (the default gateway). • First / Second DNS Server: These fields display if... you selected static IP address assignment. • IP Subnet Mask: Enter the subnet mask for VPN, DDNS and the time server. The ISG50 uses these (in the previous screen. Figure 37 Internet Access: Ethernet Encapsulation • Encapsulation: This displays the type of Internet connection you ...
User Guide
Page 62
..., and it can be up to 31 characters long. • Type the Password associated with your ISP. • Zone: This is the security zone to identify and reach the PPPoE server. Auto displays if you selected Auto as given to 64 characters long. • Authentication Type - Your... ISG50 accepts either CHAP or PAP when requested by your service provider. Figure 38 Internet Access: PPPoE Encapsulation 4.1.3.1 ISP Parameters • Type the ...
..., and it can be up to 31 characters long. • Type the Password associated with your ISP. • Zone: This is the security zone to identify and reach the PPPoE server. Auto displays if you selected Auto as given to 64 characters long. • Authentication Type - Your... ISG50 accepts either CHAP or PAP when requested by your service provider. Figure 38 Internet Access: PPPoE Encapsulation 4.1.3.1 ISP Parameters • Type the ...
User Guide
Page 64
... the Idle Timeout in the order you specify here) to resolve domain names for VPN, DDNS and the time server. This field is the security zone to which this interface and Internet connection will belong. • IP Address: Enter your broadband modem or router. The Domain Name System (...8226; Type a Connection ID or connection name. Auto displays if you selected Auto as 0.0.0.0 if you do not want to configure DNS servers. 64 ISG50 User's Guide Leave the field as the IP Address Assignment in the previous screen. • First / Second DNS Server: These fields display if you...
... the Idle Timeout in the order you specify here) to resolve domain names for VPN, DDNS and the time server. This field is the security zone to which this interface and Internet connection will belong. • IP Address: Enter your broadband modem or router. The Domain Name System (...8226; Type a Connection ID or connection name. Auto displays if you selected Auto as 0.0.0.0 if you do not want to configure DNS servers. 64 ISG50 User's Guide Leave the field as the IP Address Assignment in the previous screen. • First / Second DNS Server: These fields display if you...
User Guide
Page 66
..., close the window to exit the wizard. 4.2 Device Registration Use this screen displays your ISG50 with myZXEL.com and activate trial periods of subscription security features if you have not already done so. If the ISG50 is already registered this screen to access the Internet. If you can still activate any ... on page 66). After configuring the WAN interface(s), a screen displays with myZyXEL.com. Click Next and use the following screen to register. 66 ISG50 User's Guide Finish You have not already done so, you want to do a more detailed registration or manage your...
..., close the window to exit the wizard. 4.2 Device Registration Use this screen displays your ISG50 with myZXEL.com and activate trial periods of subscription security features if you have not already done so. If the ISG50 is already registered this screen to access the Internet. If you can still activate any ... on page 66). After configuring the WAN interface(s), a screen displays with myZyXEL.com. Click Next and use the following screen to register. 66 ISG50 User's Guide Finish You have not already done so, you want to do a more detailed registration or manage your...
User Guide
Page 69
...up a WAN (Internet) connection. ISG50 User's Guide 69 This chapter provides information on configuring the quick setup screens in this link to open the first Quick Setup screen. Figure 44 Quick Setup • WAN Interface Click this User's Guide for a secure connection to open a wizard to..., smartphone, or network. See the feature-specific chapters in the Web Configurator. This wizard creates matching ISP account settings in the ISG50 if you configure Internet and VPN connection settings. CHAPTER 5 Quick Setup 5.1 Quick Setup Overview The Web Configurator's quick setup wizards ...
...up a WAN (Internet) connection. ISG50 User's Guide 69 This chapter provides information on configuring the quick setup screens in this link to open the first Quick Setup screen. Figure 44 Quick Setup • WAN Interface Click this User's Guide for a secure connection to open a wizard to..., smartphone, or network. See the feature-specific chapters in the Web Configurator. This wizard creates matching ISP account settings in the ISG50 if you configure Internet and VPN connection settings. CHAPTER 5 Quick Setup 5.1 Quick Setup Overview The Web Configurator's quick setup wizards ...