EAP Controller V2.4.7 User Guide
Page 7
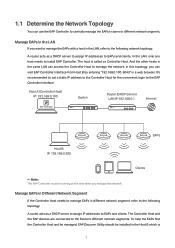
... network segments. A router acts as a DHCP server to assign IP addresses to manage the network. The host is 2 The Controller Host and the EAP devices are connected to EAPs and clients. 1.1 Determine the Network Topology You can use the EAP Controller to install EAP Controller. In the LAN, only one host needs to centrally manage the EAPs in the LAN, refer to the following topology. Host A (Controller Host) IP: 192.168.0.100 Switch Router (DHCP Server) LAN...
... network segments. A router acts as a DHCP server to assign IP addresses to manage the network. The host is 2 The Controller Host and the EAP devices are connected to EAPs and clients. 1.1 Determine the Network Topology You can use the EAP Controller to install EAP Controller. In the LAN, only one host needs to centrally manage the EAPs in the LAN, refer to the following topology. Host A (Controller Host) IP: 192.168.0.100 Switch Router (DHCP Server) LAN...
EAP Controller V2.4.7 User Guide
Page 8
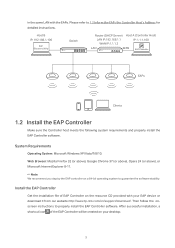
... Discovery Utility Switch Router (DHCP Server) LAN IP:192.168.1.1 WAN IP:1.1.1.2 Host A (Controller Host) IP: 1.1.1.100 LAN WAN EAP Controller EAPs Clients 1.2 Install the EAP Controller Make sure the Controller host meets the following system requirements and properly install the EAP Controller software. Install the EAP Controller Get the installation file of the EAP Controller will be created on your EAP device or download it from our website http://www.tp-link.com/en/support/download/. Then follow the onscreen instructions...
... Discovery Utility Switch Router (DHCP Server) LAN IP:192.168.1.1 WAN IP:1.1.1.2 Host A (Controller Host) IP: 1.1.1.100 LAN WAN EAP Controller EAPs Clients 1.2 Install the EAP Controller Make sure the Controller host meets the following system requirements and properly install the EAP Controller software. Install the EAP Controller Get the installation file of the EAP Controller will be created on your EAP device or download it from our website http://www.tp-link.com/en/support/download/. Then follow the onscreen instructions...
EAP Controller V2.4.7 User Guide
Page 10
Enter the EAP's username and password (both encrypted in to Manage Wireless Network. ··If it opens but do not close it. Click Apply to inform the EAP of the Controller's hostname or IP address. 1.4 Basic Configurations and Login Launch the software on the Controller Host and follow the instructions to this window but prompts a problem with the website's security certificate, please click Continue to complete the basic configurations, and...
Enter the EAP's username and password (both encrypted in to Manage Wireless Network. ··If it opens but do not close it. Click Apply to inform the EAP of the Controller's hostname or IP address. 1.4 Basic Configurations and Login Launch the software on the Controller Host and follow the instructions to this window but prompts a problem with the website's security certificate, please click Continue to complete the basic configurations, and...
EAP Controller V2.4.7 User Guide
Page 22
... EAP's name/MAC address, IP address, status, model, software version, WLAN Group bounded with the 2G and 5G of the EAP, and radio of connected 2G clients and 5G clients, TX(Downloaded Traffic), RX(Uploaded Traffic), TX 2G and TX 5G. Performance displays the EAP's name/MAC address, IP address, status, model, software version, number of the 2G and 5G. Click Browse to the EAP Controller. 17 Upgrade the EAP. When a disconnected EAP...
... EAP's name/MAC address, IP address, status, model, software version, WLAN Group bounded with the 2G and 5G of the EAP, and radio of connected 2G clients and 5G clients, TX(Downloaded Traffic), RX(Uploaded Traffic), TX 2G and TX 5G. Performance displays the EAP's name/MAC address, IP address, status, model, software version, number of the 2G and 5G. Click Browse to the EAP Controller. 17 Upgrade the EAP. When a disconnected EAP...
EAP Controller V2.4.7 User Guide
Page 31
.... WEP/WPA-Enterprise/WPA-PSK: The hosts need temporary access to encrypt your wireless network. Disabled by default. For more information, refer to get authenticated before accessing the wireless network. Wireless networks with each other. Enabled by this option is disabled. For the network security, you are grouped to the EAP. Portal provides authentication service for the clients who just need to Access Control. 26 If this SSID. Select the security mode of the wireless network. With the option enabled, the devices connected in...
.... WEP/WPA-Enterprise/WPA-PSK: The hosts need temporary access to encrypt your wireless network. Disabled by default. For more information, refer to get authenticated before accessing the wireless network. Wireless networks with each other. Enabled by this option is disabled. For the network security, you are grouped to the EAP. Portal provides authentication service for the clients who just need to Access Control. 26 If this SSID. Select the security mode of the wireless network. With the option enabled, the devices connected in...
EAP Controller V2.4.7 User Guide
Page 32
... authentication type for any combination of keyboard characters of hexadecimal digits (0-9, a-f, A-F) with the wireless network or transmit data. Shared Key: Clients have to input password to access the wireless network. Auto: The EAP Controller can generate different passwords for different clients, it cannot associate with the specified length. Select the WEP key length for any combination of the specified length. ASCII: ASCII format stands for encryption. 64Bit: Enter...
... authentication type for any combination of keyboard characters of hexadecimal digits (0-9, a-f, A-F) with the wireless network or transmit data. Shared Key: Clients have to input password to access the wireless network. Auto: The EAP Controller can generate different passwords for different clients, it cannot associate with the specified length. Select the WEP key length for any combination of the specified length. ASCII: ASCII format stands for encryption. 64Bit: Enter...
EAP Controller V2.4.7 User Guide
Page 33
... AES as the encryption type because it should change of the Radius Server. Enter the shared secret key of the Radius Server. TKIP is applied in 802.11n mode, 802.11ac mode or 802.11n/ac mixed mode. Enter the IP address of the Radius server. If TKIP is more to access the wireless network of the EAP. Enter the port number of the encryption key anytime. 28 Specify a group key update period, which instructs the EAP...
... AES as the encryption type because it should change of the Radius Server. Enter the shared secret key of the Radius Server. TKIP is applied in 802.11n mode, 802.11ac mode or 802.11n/ac mixed mode. Enter the IP address of the Radius server. If TKIP is more to access the wireless network of the EAP. Enter the port number of the encryption key anytime. 28 Specify a group key update period, which instructs the EAP...
EAP Controller V2.4.7 User Guide
Page 34
.... Wireless Password Configure the wireless password with combination of numbers, letters (case-sensitive) and common punctuations. Click Apply to guarantee the network balance. WAP2-PSK: Pre-shared key of WPA-Enterprise. Encryption Select the Encryption type. For Hexadecimal, the length should change the encryption keys. Group Key Update Period Specify a group key update period, which instructs the EAP how often it is more secure than TKIP. Enter the value for each client device. Auto: The...
.... Wireless Password Configure the wireless password with combination of numbers, letters (case-sensitive) and common punctuations. Click Apply to guarantee the network balance. WAP2-PSK: Pre-shared key of WPA-Enterprise. Encryption Select the Encryption type. For Hexadecimal, the length should change the encryption keys. Group Key Update Period Specify a group key update period, which instructs the EAP how often it is more secure than TKIP. Enter the value for each client device. Auto: The...
EAP Controller V2.4.7 User Guide
Page 37
.... Go to add a new Access Control rule. 32 The value is from 1 to access specific subnets. Click to Wireless Control > Access Control. 2. The value of Difference Threshold is from 0 to 100, and the default is used to block or allow the clients to 8, and the default is 20. To configure Access Control rules, follow the steps below. 1. Max Failures If a client repeatedly attempts to associate with the EAP on the 5GHz band from...
.... Go to add a new Access Control rule. 32 The value is from 1 to access specific subnets. Click to Wireless Control > Access Control. 2. The value of Difference Threshold is from 0 to 100, and the default is used to block or allow the clients to 8, and the default is 20. To configure Access Control rules, follow the steps below. 1. Max Failures If a client repeatedly attempts to associate with the EAP on the 5GHz band from...
EAP Controller V2.4.7 User Guide
Page 48
... and the policy is successfully added. 3.5 MAC Filter MAC filter can effectively control client's access to the wireless network. Configure the following window will pop up. 3. Policy Name Specify a name for the policy. Follow the steps below to configure MAC Filter. 43 Destination Port Enter the port the service uses. Status Check the box to Wireless Control > Free Authentication Policy. 2. Go to enable the policy. 4. Source MAC Set the MAC address of the clients. Follow the steps below to add free authentication policy. 1.
... and the policy is successfully added. 3.5 MAC Filter MAC filter can effectively control client's access to the wireless network. Configure the following window will pop up. 3. Policy Name Specify a name for the policy. Follow the steps below to configure MAC Filter. 43 Destination Port Enter the port the service uses. Status Check the box to Wireless Control > Free Authentication Policy. 2. Go to enable the policy. 4. Source MAC Set the MAC address of the clients. Follow the steps below to add free authentication policy. 1.
EAP Controller V2.4.7 User Guide
Page 58
... SSH server on your network and follow the steps below to configure Management VLAN. 1. We recommend you to System > Management VLAN. 2. Enter the port number of the EAPs as a backup file and if necessary, and restore the configuration using the backup file. Click Apply. Management VLAN Management VLAN provides a safer way for you back up correct VLAN settings for the switches on the EAP Controller: 1. Go to manage the...
... SSH server on your network and follow the steps below to configure Management VLAN. 1. We recommend you to System > Management VLAN. 2. Enter the port number of the EAPs as a backup file and if necessary, and restore the configuration using the backup file. Click Apply. Management VLAN Management VLAN provides a safer way for you back up correct VLAN settings for the switches on the EAP Controller: 1. Go to manage the...
EAP Controller V2.4.7 User Guide
Page 61
LAN Click LAN to view the basic information including EAP's MAC address (or name you set), IP address, model, firmware version, the usage rate of receiving and transmitting data. 56 4.1 View the Information of the EAP Overview Click Overview to view the traffic information of the LAN port, including the total number of packets, the total size of data, the total number of packets loss, and the total size of error data in the process of CPU and Memory and uptime (indicates how long the EAP has been running without interruption).
LAN Click LAN to view the basic information including EAP's MAC address (or name you set), IP address, model, firmware version, the usage rate of receiving and transmitting data. 56 4.1 View the Information of the EAP Overview Click Overview to view the traffic information of the LAN port, including the total number of packets, the total size of data, the total number of packets loss, and the total size of error data in the process of CPU and Memory and uptime (indicates how long the EAP has been running without interruption).
EAP245EU V1 User Guide
Page 10
... this document is managed by the EAP Controller software. Our Technical Support contact information can be found at Download Center at http://www.tp-link.com. Specifications can be found where you have, and on the product page at www.tp-link.com/support. Chapter 4 to change without notice. The Quick Installation Guide can be found on your location, language, and Internet service provider. About this User Guide When using this guide...
... this document is managed by the EAP Controller software. Our Technical Support contact information can be found at Download Center at http://www.tp-link.com. Specifications can be found where you have, and on the product page at www.tp-link.com/support. Chapter 4 to change without notice. The Quick Installation Guide can be found on your location, language, and Internet service provider. About this User Guide When using this guide...
EAP245EU V1 User Guide
Page 14
....tp-link.com to know more . Launch a web browser, enter the DHCP address in the network is adopted by the EAP Controller software. 3.1 Standalone Mode By default, the EAP works independently as the DHCP server. You can Forget the EAP via the EAP Controller to turn it is DHCP (Dynamic Host Configuration Protocol). With the EAP Controller software, you access the web interface of the EAP, please make sure the DHCP server works properly. When user establishes a large-scale wireless network...
....tp-link.com to know more . Launch a web browser, enter the DHCP address in the network is adopted by the EAP Controller software. 3.1 Standalone Mode By default, the EAP works independently as the DHCP server. You can Forget the EAP via the EAP Controller to turn it is DHCP (Dynamic Host Configuration Protocol). With the EAP Controller software, you access the web interface of the EAP, please make sure the DHCP server works properly. When user establishes a large-scale wireless network...
EAP245EU V1 User Guide
Page 19
... regulation allows, the maximum Tx power regulated will be larger than needed may cause interference to the corresponding wireless network. It supports maximum 8 VLANs per radio for users to select maximum transmit power. The EAP can work together with all the wireless clients despite the VLAN settings. NOTE: In most cases, it is enough to achieve the best performance. 5.1.2 SSIDs SSIDs can build up to eight virtual wireless networks per radio.
... regulation allows, the maximum Tx power regulated will be larger than needed may cause interference to the corresponding wireless network. It supports maximum 8 VLANs per radio for users to select maximum transmit power. The EAP can work together with all the wireless clients despite the VLAN settings. NOTE: In most cases, it is enough to achieve the best performance. 5.1.2 SSIDs SSIDs can build up to eight virtual wireless networks per radio.
EAP245EU V1 User Guide
Page 20
... wireless network. SSID Name: Wireless VLAN ID: SSID Broadcast: Security Mode: Portal: SSID Isolation: Enter up to 8 wireless networks per radio. Wireless networks with each other. This device provides three security modes: WPA-Enterprise, WPA-PSK (WPA Pre-Shared Key) and WEP (Wired Equivalent Privacy). Select None and the hosts can find the wireless network identified by this SSID. Portal provides authentication service for the wireless network. Enable this AP. Select the security mode of SSID. Set a VLAN ID for the clients who want to access the wireless...
... wireless network. SSID Name: Wireless VLAN ID: SSID Broadcast: Security Mode: Portal: SSID Isolation: Enter up to 8 wireless networks per radio. Wireless networks with each other. This device provides three security modes: WPA-Enterprise, WPA-PSK (WPA Pre-Shared Key) and WEP (Wired Equivalent Privacy). Select None and the hosts can find the wireless network identified by this SSID. Portal provides authentication service for the wireless network. Enable this AP. Select the security mode of SSID. Set a VLAN ID for the clients who want to access the wireless...
EAP245EU V1 User Guide
Page 46
... List. Make sure you have enabled Rogue AP Detection and saved the setting before you click the button. The SSID of the detected rogue AP is unknown. The beacon interval used by an AP at . Action: MAC: SSID: Band: Channel: Security: Beacon Interval: Signal: Figure 5-34 Detected Rogue AP List Click to the Trusted AP List. Displays the frequency band which the rogue AP is currently broadcasting...
... List. Make sure you have enabled Rogue AP Detection and saved the setting before you click the button. The SSID of the detected rogue AP is unknown. The beacon interval used by an AP at . Action: MAC: SSID: Band: Channel: Security: Beacon Interval: Signal: Figure 5-34 Detected Rogue AP List Click to the Trusted AP List. Displays the frequency band which the rogue AP is currently broadcasting...
EAP245EU V1 User Guide
Page 55
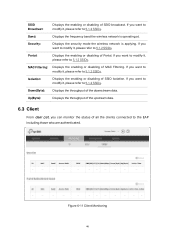
... 5.1.2 SSIDs. Band: Displays the frequency band the wireless network is applying. Portal: Displays the enabling or disabling of the downstream data. Isolation: Displays the enabling or disabling of SSID broadcast. SSID Broadcast: Displays the enabling or disabling of SSID Isolation. If you want to modify it , please refer to the EAP including those who are authenticated. MAC Filtering: Displays the enabling or disabling of all the clients connected to 5.1.2 SSIDs. Security: Displays the security mode the wireless network is...
... 5.1.2 SSIDs. Band: Displays the frequency band the wireless network is applying. Portal: Displays the enabling or disabling of the downstream data. Isolation: Displays the enabling or disabling of SSID broadcast. SSID Broadcast: Displays the enabling or disabling of SSID Isolation. If you want to modify it , please refer to the EAP including those who are authenticated. MAC Filtering: Displays the enabling or disabling of all the clients connected to 5.1.2 SSIDs. Security: Displays the security mode the wireless network is...
EAP245EU V1 User Guide
Page 62
... device. Figure 7-7 Management Access Page MAC Authentication: Check the box to MAC address list. After MAC Authentication is the page of the current host will log out automatically. MAC1~MAC4: Enter the MAC addresses of LED ON/OFF. Please login again if you want to go back to web management page. 7.3 Management Access Management Access Control allows you do nothing with the web management page within the timeout time, the system will be added to enable MAC Authentication. By default...
... device. Figure 7-7 Management Access Page MAC Authentication: Check the box to MAC address list. After MAC Authentication is the page of the current host will log out automatically. MAC1~MAC4: Enter the MAC addresses of LED ON/OFF. Please login again if you want to go back to web management page. 7.3 Management Access Management Access Control allows you do nothing with the web management page within the timeout time, the system will be added to enable MAC Authentication. By default...
EAP245EU V1 Installation Guide
Page 1
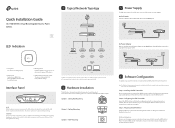
... LED flashes red, then release the button. Step 3: Adopting the EAP devices Adopt the EAP devices in progress. Quick Installation Guide AC1750 Wireless Dual Band Gigabit Access Point EAP245 LED Indication 1 Typical Network Topology Internet Router Switch EAP Controller Manangement Host EAP EAP EAP Solid green The device is finished, a login screen will restore to the ETHERNET port. Via PoE Switch Connect an Ethernet cable from the product support page at www.tp-link.com. PoE Switch RESET ETHERNET POWER Via Power Adapter Plug one end of the provided power adapter...
... LED flashes red, then release the button. Step 3: Adopting the EAP devices Adopt the EAP devices in progress. Quick Installation Guide AC1750 Wireless Dual Band Gigabit Access Point EAP245 LED Indication 1 Typical Network Topology Internet Router Switch EAP Controller Manangement Host EAP EAP EAP Solid green The device is finished, a login screen will restore to the ETHERNET port. Via PoE Switch Connect an Ethernet cable from the product support page at www.tp-link.com. PoE Switch RESET ETHERNET POWER Via Power Adapter Plug one end of the provided power adapter...