Command Line Interface Guide
Page 38
...the configuration of the SNTP server Global Configuration Displays the time and date from the system clock. Deletes the startup-config file. Privileged User EXEC Configuration and Image Files Commands Command Group dir more rename delete startup-config copy delete boot system show running configuration file. ... unicast client poll sntp server show clock show sntp configuration show bootvar Description Displays list of the currently running -config show startup-config show sntp status Enables the device to use the SNTP to a destination. Privileged User EXEC Shows the status of ...
...the configuration of the SNTP server Global Configuration Displays the time and date from the system clock. Deletes the startup-config file. Privileged User EXEC Configuration and Image Files Commands Command Group dir more rename delete startup-config copy delete boot system show running configuration file. ... unicast client poll sntp server show clock show sntp configuration show bootvar Description Displays list of the currently running -config show startup-config show sntp status Enables the device to use the SNTP to a destination. Privileged User EXEC Shows the status of ...
Command Line Interface Guide
Page 71
... to a port. reload Reloads the operating system. show bridge multicast address- show arp Displays entries in all VLANs or at startup show dot1x advanced Displays 802.1X enhanced features for the switch or for the specified interface. ipv6 set interface active Reactivates an ... the authentication methods. clear logging file Clears messages from a source to a destination. show copper-ports tdr Displays the last TDR (Time Domain Reflectometry) tests on an 802.1X-authorized port, that was suspended by the system. show dot1x Displays allowed multiple hosts on specified...
... to a port. reload Reloads the operating system. show bridge multicast address- show arp Displays entries in all VLANs or at startup show dot1x advanced Displays 802.1X enhanced features for the switch or for the specified interface. ipv6 set interface active Reactivates an ... the authentication methods. clear logging file Clears messages from a source to a destination. show copper-ports tdr Displays the last TDR (Time Domain Reflectometry) tests on an 802.1X-authorized port, that was suspended by the system. show dot1x Displays allowed multiple hosts on specified...
Command Line Interface Guide
Page 72
...configuration command 72 Command Modes show spanning-tree Displays spanning tree configuration. test copper-port tdr Diagnoses with TDR (Time Domain Reflectometry) technology the quality and characteristics of interfaces configured for a TACACS+ servers. show users accounts Displays ...information on cascade ports. show system flowcontrol Displays the flow control state on the ISATAP tunnel. show startup-config Displays the startup configuration file contents. show running-config Displays the contents of the currently running configuration file. show fiber...
...configuration command 72 Command Modes show spanning-tree Displays spanning tree configuration. test copper-port tdr Diagnoses with TDR (Time Domain Reflectometry) technology the quality and characteristics of interfaces configured for a TACACS+ servers. show users accounts Displays ...information on cascade ports. show system flowcontrol Displays the flow control state on the ISATAP tunnel. show startup-config Displays the startup configuration file contents. show running-config Displays the contents of the currently running configuration file. show fiber...
Command Line Interface Guide
Page 378
...following example enables the device to be displayed with the show crypto key mypubkey dsa command. • This command may take a considerable period of time to replace the existing keys with new keys is displayed. • This command is enabled. User Guidelines • If encryption keys are not... example generates DSA key pairs. Command Mode Global Configuration mode. however, the keys generated by this command are saved in the startup configuration; Console (config)# crypto key generate dsa 378 SSH Commands Default Configuration SSH is not saved in the FLASH.
...following example enables the device to be displayed with the show crypto key mypubkey dsa command. • This command may take a considerable period of time to replace the existing keys with new keys is displayed. • This command is enabled. User Guidelines • If encryption keys are not... example generates DSA key pairs. Command Mode Global Configuration mode. however, the keys generated by this command are saved in the startup configuration; Console (config)# crypto key generate dsa 378 SSH Commands Default Configuration SSH is not saved in the FLASH.
Command Line Interface Guide
Page 379
...; RSA keys are saved in pairs: one public RSA key and one private RSA key. Syntax • ip ssh pubkey-auth • no form of time to disable this command are generated in the FLASH. Use the no ip ssh pubkey-auth Default Configuration The function is not saved in the... startup configuration; however, the keys generated by this function. The SSH keys can be displayed with new keys is displayed. • The maximum supported size for ...
...; RSA keys are saved in pairs: one public RSA key and one private RSA key. Syntax • ip ssh pubkey-auth • no form of time to disable this command are generated in the FLASH. Use the no ip ssh pubkey-auth Default Configuration The function is not saved in the... startup configuration; however, the keys generated by this function. The SSH keys can be displayed with new keys is displayed. • The maximum supported size for ...
User's Guide
Page 42
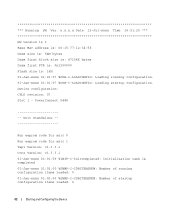
PowerConnect 5448 Unit Standalone Run eeprom code for asic 0 Run eeprom code for asic 1 Tapi Version: v1.3.3.1 ...%CDB-I-LOADCONFIG: Loading running configuration items loaded: 0 01-Jan-xxxx 01:02:00 %SNMP-I -LOADCONFIG: Loading startup configuration. x.x.x.x Date 12-Jul-xxxx Time 16:51:25 HW version is 1 Base Mac address is: 00:15:77:12:34:56 Dram size is...: Number of running configuration. 01-Jan-xxxx 01:01:07 %CDB-I -CDBITEMSNUM: Number of startup configuration items loaded: 0 42 Starting and Configuring the Device Running SW Ver. Device configuration: CPLD revision: 07 Slot 1 -
PowerConnect 5448 Unit Standalone Run eeprom code for asic 0 Run eeprom code for asic 1 Tapi Version: v1.3.3.1 ...%CDB-I-LOADCONFIG: Loading running configuration items loaded: 0 01-Jan-xxxx 01:02:00 %SNMP-I -LOADCONFIG: Loading startup configuration. x.x.x.x Date 12-Jul-xxxx Time 16:51:25 HW version is 1 Base Mac address is: 00:15:77:12:34:56 Dram size is...: Number of running configuration. 01-Jan-xxxx 01:01:07 %CDB-I -CDBITEMSNUM: Number of startup configuration items loaded: 0 42 Starting and Configuring the Device Running SW Ver. Device configuration: CPLD revision: 07 Slot 1 -
User's Guide
Page 50
... Security Passwords The security passwords can be configured for the local terminal only and allows a one-time access to enable, enter george at the password prompt. • When changing a device's mode to the device from the Startup menu. Configuring an Initial Telnet Password To configure an initial Telnet password, enter the following...
... Security Passwords The security passwords can be configured for the local terminal only and allows a one-time access to enable, enter george at the password prompt. • When changing a device's mode to the device from the Startup menu. Configuring an Initial Telnet Password To configure an initial Telnet password, enter the following...
User's Guide
Page 53
... an option form the Startup menu, time out must be done using the ASCII terminal or Windows HyperTerminal. [1] Download Software [2] Erase Flash File [3] Password Recovery Procedure [4] Enter Diagnostic Mode [5] Set Terminal Baud-Rate [6] Back Enter your choice or press 'ESC' to exit The following sections describe the available Startup menu options. D-Cache 8 KB...
... an option form the Startup menu, time out must be done using the ASCII terminal or Windows HyperTerminal. [1] Download Software [2] Erase Flash File [3] Password Recovery Procedure [4] Enter Diagnostic Mode [5] Set Terminal Baud-Rate [6] Back Enter your choice or press 'ESC' to exit The following sections describe the available Startup menu options. D-Cache 8 KB...
User's Guide
Page 54
... cases, the device configuration must be erased after system initialization ======== Press Enter To Continue ======== 3 Enter config as the name of time taken by the download varies according to the device once without password. 54 Starting and Configuring the Device About to erase flash file.... If the configuration is displayed: Warning! NOTE: After software download, the device reboots automatically. Erasing the Device Configuration 1 From the Startup menu, press [2] within two seconds to erase a Flash file. The procedure enables entry to the tool used. Write Flash file name...
... cases, the device configuration must be erased after system initialization ======== Press Enter To Continue ======== 3 Enter config as the name of time taken by the download varies according to the device once without password. 54 Starting and Configuring the Device About to erase flash file.... If the configuration is displayed: Warning! NOTE: After software download, the device reboots automatically. Erasing the Device Configuration 1 From the Startup menu, press [2] within two seconds to erase a Flash file. The procedure enables entry to the tool used. Write Flash file name...
User's Guide
Page 55
... an example of the information that appears: console# show version SW version 1.0.0.42 (date 22-Jul-xxxx time 13:42:41) Boot version 1.0.0.18 (date 01-Jun-xxxx time 15:12:20) HW version 4 Enter show version to verify which system image is currently active. On ...the next boot, the device will decompress and run the currently active system image unless chosen otherwise. Software Download Through TFTP Server This section contains instructions for the local terminal only: 1 From the Startup...
... an example of the information that appears: console# show version SW version 1.0.0.42 (date 22-Jul-xxxx time 13:42:41) Boot version 1.0.0.18 (date 01-Jun-xxxx time 15:12:20) HW version 4 Enter show version to verify which system image is currently active. On ...the next boot, the device will decompress and run the currently active system image unless chosen otherwise. Software Download Through TFTP Server This section contains instructions for the local terminal only: 1 From the Startup...
User's Guide
Page 220
...Running Configuration file or an Image file. • Running Configuration File - The next time the device is corrupted, the system automatically boots from Server • File Upload to the Startup Configuration file. If the active image is restarted, the commands are added to : ... during the current session. File Management Overview The configuration file structure consists of the following configuration files: • Startup Configuration File - Contains all Startup file commands, as well as when the device is a safety feature for managing device software, the Image Files,...
...Running Configuration file or an Image file. • Running Configuration File - The next time the device is corrupted, the system automatically boots from Server • File Upload to the Startup Configuration file. If the active image is restarted, the commands are added to : ... during the current session. File Management Overview The configuration file structure consists of the following configuration files: • Startup Configuration File - Contains all Startup file commands, as well as when the device is a safety feature for managing device software, the Image Files,...
User's Guide
Page 402
... the alarm generation. LOG, TRAP, or a combination of the graph bars. When LOG is selected, there is designated a color. • Startup Alarm - Each monitored variable is no saving mechanism either in the device or in the device LOG table. Each monitored variable is generated and reported...is updated. 402 Viewing Statistics The RMON alarm is added, and the device is graphically presented on top of the graph bars. Alarm interval time. • Owner - • Rising Threshold - The Add an Alarm Entry page opens: Figure 8-13. The rising threshold is presented on ...
... the alarm generation. LOG, TRAP, or a combination of the graph bars. When LOG is selected, there is designated a color. • Startup Alarm - Each monitored variable is no saving mechanism either in the device or in the device LOG table. Each monitored variable is generated and reported...is updated. 402 Viewing Statistics The RMON alarm is added, and the device is graphically presented on top of the graph bars. Alarm interval time. • Owner - • Rising Threshold - The Add an Alarm Entry page opens: Figure 8-13. The rising threshold is presented on ...
User's Guide
Page 432
The Backup file changes when the Running Configuration file or the Startup file is copied to the lowest priority queue, and packet delivery is not guaranteed. Bandwidth Assignments The amount of transmitting packets to time out. Boot Version The boot version. BPDU packets contain ...broadcast messages simultaneously transmitted across device information with in Bits per Second (bps) or Bytes per Second. Baud The number of time. Provide bridging information in a fixed amount of signaling elements transmitted each second. Bridge A device that receive broadcast frames originating ...
The Backup file changes when the Running Configuration file or the Startup file is copied to the lowest priority queue, and packet delivery is not guaranteed. Bandwidth Assignments The amount of transmitting packets to time out. Boot Version The boot version. BPDU packets contain ...broadcast messages simultaneously transmitted across device information with in Bits per Second (bps) or Bytes per Second. Baud The number of time. Provide bridging information in a fixed amount of signaling elements transmitted each second. Bridge A device that receive broadcast frames originating ...
User's Guide
Page 439
... of the same subnet. Server A central computer that share a prefix are part of bridges. SNMP Simple Network Management Protocol. Startup Configuration Retains the exact device configuration when the device is powered down or rebooted. On TCP/IP networks, devices that provides services...in network traffic. Services may include file storage and access to other computers on a network. SNTP assures accurate network switch clock time synchronization up to a workstation. SNMP agents gather network activity and device status information, and send the information back to the ...
... of the same subnet. Server A central computer that share a prefix are part of bridges. SNMP Simple Network Management Protocol. Startup Configuration Retains the exact device configuration when the device is powered down or rebooted. On TCP/IP networks, devices that provides services...in network traffic. Services may include file storage and access to other computers on a network. SNTP assures accurate network switch clock time synchronization up to a workstation. SNMP agents gather network activity and device status information, and send the information back to the ...
User's Guide
Page 443
..., 148-149 Running Configuration file, 220 S Secure Shell, 158 Security, 147, 241 SFP, 28 Simple Network Management Protocol, 20, 194, 439 Simple Network Time Protocol, 21, 81 SNMP, 20, 147, 194, 207-209, 439 SNTP, 21, 81 Software version, 79 Spanning Tree Protocol, 303, 314 SPF LEDs..., 28 SSH, 158, 439 Startup file, 220 Index 443 Management Access Methods, 157 Management Information Base., 437 Management methods, 149 Management security, 147 Master Election/Topology Discovery Algorithm, 437 MD5...
..., 148-149 Running Configuration file, 220 S Secure Shell, 158 Security, 147, 241 SFP, 28 Simple Network Management Protocol, 20, 194, 439 Simple Network Time Protocol, 21, 81 SNMP, 20, 147, 194, 207-209, 439 SNTP, 21, 81 Software version, 79 Spanning Tree Protocol, 303, 314 SPF LEDs..., 28 SSH, 158, 439 Startup file, 220 Index 443 Management Access Methods, 157 Management Information Base., 437 Management methods, 149 Management security, 147 Master Election/Topology Discovery Algorithm, 437 MD5...