Command Line Interface Guide
Page 18
show (mst 360 exit (mst 361 abort (mst 361 spanning-tree pathcost method 362 spanning-tree bpdu 362 clear spanning-tree detected-protocols 363 show spanning-tree 364 Spanning-tree guard root 376 29 SSH Commands 377 ip ssh port 377 ip ssh server 377 crypto key generate dsa 378 crypto key generate rsa 379 ip ssh pubkey-auth 379 crypto key pubkey-chain ssh 380 user-key 380 key-string 381 show ip ssh 382 show crypto key mypubkey 384 show crypto key pubkey-chain ssh 385 30 Syslog Commands 387 logging on 387 logging 387 logging console 389 logging buffered 389 18 Contents
show (mst 360 exit (mst 361 abort (mst 361 spanning-tree pathcost method 362 spanning-tree bpdu 362 clear spanning-tree detected-protocols 363 show spanning-tree 364 Spanning-tree guard root 376 29 SSH Commands 377 ip ssh port 377 ip ssh server 377 crypto key generate dsa 378 crypto key generate rsa 379 ip ssh pubkey-auth 379 crypto key pubkey-chain ssh 380 user-key 380 key-string 381 show ip ssh 382 show crypto key mypubkey 384 show crypto key pubkey-chain ssh 385 30 Syslog Commands 387 logging on 387 logging 387 logging console 389 logging buffered 389 18 Contents
Command Line Interface Guide
Page 25
... navigate from one command mode to assist in configuring devices, the CLI (Command Line Interface) is divided into different command modes. at the system prompt (console prompt) displays a list of specific commands. Using the CLI This chapter describes how to start using the CLI and describes implemented command editing features to...
... navigate from one command mode to assist in configuring devices, the CLI (Command Line Interface) is divided into different command modes. at the system prompt (console prompt) displays a list of specific commands. Using the CLI This chapter describes how to start using the CLI and describes implemented command editing features to...
Command Line Interface Guide
Page 26
The user-level prompt consists of the device "host name" followed by the angle bracket (>). console> The default host name is "Console" unless it has been changed using the hostname command in User EXEC Mode. The password is automatically in the device. Privileged users... system parameters: The password is defined as "*". In general, the User EXEC commands allow the user to commands that do not change the configuration. console# To return from the User EXEC mode, perform the following steps: 1 At the prompt enter the command enable and press . The Global Configuration...
The user-level prompt consists of the device "host name" followed by the angle bracket (>). console> The default host name is "Console" unless it has been changed using the hostname command in User EXEC Mode. The password is automatically in the device. Privileged users... system parameters: The password is defined as "*". In general, the User EXEC commands allow the user to commands that do not change the configuration. console# To return from the User EXEC mode, perform the following steps: 1 At the prompt enter the command enable and press . The Global Configuration...
Command Line Interface Guide
Page 27
...Configuration mode perform the following example illustrates how to access Global Configuration mode and returns to the Privileged EXEC mode: console# console#configure console(config)#exit console# Using the CLI 27 The following example illustrates how to access Privileged Exec mode and return back to the User ...EXEC mode: console>enable Enter Password: ****** console# console#disable console> The Exit command is used to return from any mode to the previous mode except when returning to ...
...Configuration mode perform the following example illustrates how to access Global Configuration mode and returns to the Privileged EXEC mode: console# console#configure console(config)#exit console# Using the CLI 27 The following example illustrates how to access Privileged Exec mode and return back to the User ...EXEC mode: console>enable Enter Password: ****** console# console#disable console> The Exit command is used to return from any mode to the previous mode except when returning to ...
Command Line Interface Guide
Page 28
...services configuration mode. The following steps are the Interface Configuration modes: • Line Interface - Contains commands to entering commands on the console line only. 28 Using the CLI Using the switch command-line interface (CLI) is used to manage the member ports as line... port configuration. Contains commands to a VLAN or port-channel. The Global Configuration mode command interface ethernet is used to the switch console port, or via a Telnet connection, ensure the device has an IP address defined, corresponding management access is connected to the device...
...services configuration mode. The following steps are the Interface Configuration modes: • Line Interface - Contains commands to entering commands on the console line only. 28 Using the CLI Using the switch command-line interface (CLI) is used to manage the member ports as line... port configuration. Contains commands to a VLAN or port-channel. The Global Configuration mode command interface ethernet is used to the switch console port, or via a Telnet connection, ensure the device has an IP address defined, corresponding management access is connected to the device...
Command Line Interface Guide
Page 29
... displayed. 2 Configure the device and enter the necessary commands to complete the command. The User Exec mode is entered, and the prompt "Console>" is incomplete and the character ? Keywords identify a command, and arguments specify configuration parameters. A list of keywords and arguments. is entered ...in the Privileged EXEC mode command mode the login command is entered. The matched parameters for the administrator, enter: Console(config)# username admin password smith When working with the quit or exit command. Editing Features Entering Commands A CLI command is a...
... displayed. 2 Configure the device and enter the necessary commands to complete the command. The User Exec mode is entered, and the prompt "Console>" is incomplete and the character ? Keywords identify a command, and arguments specify configuration parameters. A list of keywords and arguments. is entered ...in the Privileged EXEC mode command mode the login command is entered. The matched parameters for the administrator, enter: Console(config)# username admin password smith When working with the quit or exit command. Editing Features Entering Commands A CLI command is a...
Command Line Interface Guide
Page 32
... the keyboard. For example click . Italic font Indicates a parameter. The following table describes the command conventions. Ctrl+F4 Any combination keys pressed simultaneously on the console. CLI Command Conventions When entering commands there are defined.
... the keyboard. For example click . Italic font Indicates a parameter. The following table describes the command conventions. Ctrl+F4 Any combination keys pressed simultaneously on the console. CLI Command Conventions When entering commands there are defined.
Command Line Interface Guide
Page 33
... textual input and output with commands being entered from the console a Setup Wizard is a basic command-line interpreter similar to the Getting Started Guide and User Guide for configuring the Dell™ PowerConnect™ switch, details the procedures and provides configuration examples....Telnet connection from the Web Based Interface. Command Groups The system commands can be accessed from a VT100 terminal connected to the console port of a Graphic User Interface (GUI) driven software application. Configuration and Image Files Commands Manages the device Configuration files....
... textual input and output with commands being entered from the console a Setup Wizard is a basic command-line interpreter similar to the Getting Started Guide and User Guide for configuring the Dell™ PowerConnect™ switch, details the procedures and provides configuration examples....Telnet connection from the Web Based Interface. Command Groups The system commands can be accessed from a VT100 terminal connected to the console port of a Graphic User Interface (GUI) driven software application. Configuration and Image Files Commands Manages the device Configuration files....
Command Line Interface Guide
Page 34
.... Configures and displays QoS information. Configures IGMP snooping and displays IGMP configuration and IGMP information. Configures and manages IP addresses on the device. Configures the console and remote Telnet connection. Configures Voice VLANs and displays Voice VLAN information. Configures and manages IPv6 addresses on the device. Manages and displays syslog messages...
.... Configures and displays QoS information. Configures IGMP snooping and displays IGMP configuration and IGMP information. Configures and manages IP addresses on the device. Configures the console and remote Telnet connection. Configures Voice VLANs and displays Voice VLAN information. Configures and manages IPv6 addresses on the device. Manages and displays syslog messages...
Command Line Interface Guide
Page 35
... conditions defined in IPv4 Access List Configuration mode. Configuration Specifies the authentication method list when accessing Line Configuration a higher privilege level from a remote telnet or console. Global Configuration Specifies authentication methods for accessing higher Global privilege levels. MAC-Access List Configuration service-acl Applies an ACL to the input interface. Privileged...
... conditions defined in IPv4 Access List Configuration mode. Configuration Specifies the authentication method list when accessing Line Configuration a higher privilege level from a remote telnet or console. Global Configuration Specifies authentication methods for accessing higher Global privilege levels. MAC-Access List Configuration service-acl Applies an ACL to the input interface. Privileged...
Command Line Interface Guide
Page 53
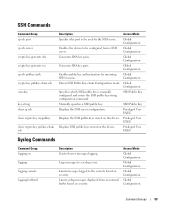
... a syslog server. Access Mode Global Configuration Global Configuration Global Configuration Global Configuration Command Groups 53 Logs messages to the console based on severity. SSH Commands Command Group ip ssh port ip ssh server crypto key generate dsa crypto key generate rsa... Generates DSA key pairs. Global Configuration Enables the device to be configured from an internal buffer based on logging logging console logging buffered Description Controls error messages logging. Privileged User EXEC Displays the SSH public keys stored on the device. Privileged...
... a syslog server. Access Mode Global Configuration Global Configuration Global Configuration Global Configuration Command Groups 53 Logs messages to the console based on severity. SSH Commands Command Group ip ssh port ip ssh server crypto key generate dsa crypto key generate rsa... Generates DSA key pairs. Global Configuration Enables the device to be configured from an internal buffer based on logging logging console logging buffered Description Controls error messages logging. Privileged User EXEC Displays the SSH public keys stored on the device. Privileged...
Command Line Interface Guide
Page 65
... system-priority line logging logging buffered logging buffered size logging console The following example clears messages from a SSH server. logging on severity. Identifies a specific line for a remote telnet or console. Limits messages logged to the logging file based on severity.... Limits syslog messages sent to the console based on severity. Controls error messages logging. Specifies the login authentication method ...
... system-priority line logging logging buffered logging buffered size logging console The following example clears messages from a SSH server. logging on severity. Identifies a specific line for a remote telnet or console. Limits messages logged to the logging file based on severity.... Limits syslog messages sent to the console based on severity. Controls error messages logging. Specifies the login authentication method ...
Command Line Interface Guide
Page 70
... history history size login-banner motd-banner password autobaud speed Description Specifies the authentication method list when accessing a higher privilege level from a remote telnet or console. Enables the display of -the-day banners. Enables the display of exec banners. Configures the interval that the device loads at startup. Sets the line...
... history history size login-banner motd-banner password autobaud speed Description Specifies the authentication method list when accessing a higher privilege level from a remote telnet or console. Enables the display of -the-day banners. Enables the display of exec banners. Configures the interval that the device loads at startup. Sets the line...
Command Line Interface Guide
Page 75
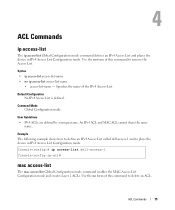
... the Access List. Specifies the name of this command to place the device in IPv4 Access List Configuration mode. Console(config)# ip access-list dell-access-1 Console(config-ip-al)# mac access-list The mac access-list Global Configuration mode command enables the MAC-Access List Configuration... mode and creates Layer 2 ACLs. Example The following example shows how to define an IPv4 Access List called dell-access-1 and to...
... the Access List. Specifies the name of this command to place the device in IPv4 Access List Configuration mode. Console(config)# ip access-list dell-access-1 Console(config-ip-al)# mac access-list The mac access-list Global Configuration mode command enables the MAC-Access List Configuration... mode and creates Layer 2 ACLs. Example The following example shows how to define an IPv4 Access List called dell-access-1 and to...
Command Line Interface Guide
Page 76
...}} {any|{destination destination-wildcard}} [dscp number | ip-precedence number] • permit-icmp {any|{source source-wildcard}} {any|{destination destination-wildcard}} {any |igmp- Console(config)# mac access-list macl-acl1 Console(config-mac-al)# permit (ip) The permit IP-Access List Configuration mode command permits traffic if the conditions defined in the permit...
...}} {any|{destination destination-wildcard}} [dscp number | ip-precedence number] • permit-icmp {any|{source source-wildcard}} {any|{destination destination-wildcard}} {any |igmp- Console(config)# mac access-list macl-acl1 Console(config-mac-al)# permit (ip) The permit IP-Access List Configuration mode command permits traffic if the conditions defined in the permit...
Command Line Interface Guide
Page 78
... exists at the end of the list and those packets that do not match the conditions defined in the deny statement match. Console(config)# ip access-list ip-acl1 Console(config-ip-al)# permit rsvp 192.1.1.1 0.0.0.0 any dscp 56 deny (IP) The deny IP-Access List Configuration mode command denies traffic if...
... exists at the end of the list and those packets that do not match the conditions defined in the deny statement match. Console(config)# ip access-list ip-acl1 Console(config-ip-al)# permit rsvp 192.1.1.1 0.0.0.0 any dscp 56 deny (IP) The deny IP-Access List Configuration mode command denies traffic if...
Command Line Interface Guide
Page 80
...:10:XX use the Mac address 00:00:00:00:10:00 and mask 00:00:00:00:00:FF. • destination - Console(config)# ip access-list ip-acl1 Console(config-ip-al)# deny rsvp 192.1.1.1 0.0.0.255 any | {destination destination-wildcard}} [vlan vlan-id] [cos cos cos-wildcard] [ethtype eth-type] [inner...
...:10:XX use the Mac address 00:00:00:00:10:00 and mask 00:00:00:00:00:FF. • destination - Console(config)# ip access-list ip-acl1 Console(config-ip-al)# deny rsvp 192.1.1.1 0.0.0.255 any | {destination destination-wildcard}} [vlan vlan-id] [cos cos cos-wildcard] [ethtype eth-type] [inner...
Command Line Interface Guide
Page 81
... - Specifies the MAC address of the host from which the packet is specified, the policy map cannot be ignored. • vlan-id - Console(config)# mac access-list macl-acl1 Console(config-mac-al)# permit 6:6:6:6:6:6 0:0:0:0:0:0 any - Specifies wildcard bits to an ACL, all packets are denied. • If the VLAN ID is being...
... - Specifies the MAC address of the host from which the packet is specified, the policy map cannot be ignored. • vlan-id - Console(config)# mac access-list macl-acl1 Console(config-mac-al)# permit 6:6:6:6:6:6 0:0:0:0:0:0 any - Specifies wildcard bits to an ACL, all packets are denied. • If the VLAN ID is being...
Command Line Interface Guide
Page 82
... service-acl The service-acl Interface Configuration (Ethernet, port-channel) mode command applies an ACL to detach an ACL from an input interface. Console(config)# mac access-list macl1 Console (config-mac-acl)# deny 6:6:6:6:6:6:0:0:0:0:0:0 any condition exists at the end of Service (CoS). (Range: 0 - 7) • cos-wildcard - Applies the specified ACL to...
... service-acl The service-acl Interface Configuration (Ethernet, port-channel) mode command applies an ACL to detach an ACL from an input interface. Console(config)# mac access-list macl1 Console (config-mac-acl)# deny 6:6:6:6:6:6:0:0:0:0:0:0 any condition exists at the end of Service (CoS). (Range: 0 - 7) • cos-wildcard - Applies the specified ACL to...
Command Line Interface Guide
Page 83
... access-lists Privileged EXEC mode command displays access control lists (ACLs) defined on a device. Console(config)# interface eth g1 Console(config-if)# service-acl input macl1 show access-lists The show access-lists IP access list ACL1 permit 234 172.30.40.1 0.0.0.0 any permit 234 ...
... access-lists Privileged EXEC mode command displays access control lists (ACLs) defined on a device. Console(config)# interface eth g1 Console(config-if)# service-acl input macl1 show access-lists The show access-lists IP access list ACL1 permit 234 172.30.40.1 0.0.0.0 any permit 234 ...