Product Manual
Page 3
Package Contents Contents of the above , with the DI-808HV will cause damage and void the warranty for this product. System Requirements For Configuration: Ethernet-based Cable or DSL Modem Computer with Windows-, Macintosh-, or ... version 6.x or Netscape Navigator version 6.x and above items are missing, please contact your reseller. If any of Package: D-Link DI-808HV Broadband VPN Router 5V DC Power Adapter Ethernet (CAT5-UTP/Straight-Through) Cable Manual on CD Quick Installation Guide Note: Using a power supply with a different voltage rating than the one included with JavaScript...
Package Contents Contents of the above , with the DI-808HV will cause damage and void the warranty for this product. System Requirements For Configuration: Ethernet-based Cable or DSL Modem Computer with Windows-, Macintosh-, or ... version 6.x or Netscape Navigator version 6.x and above items are missing, please contact your reseller. If any of Package: D-Link DI-808HV Broadband VPN Router 5V DC Power Adapter Ethernet (CAT5-UTP/Straight-Through) Cable Manual on CD Quick Installation Guide Note: Using a power supply with a different voltage rating than the one included with JavaScript...
Product Manual
Page 16
... section is optional and is the section where you input the name of the network adapter in . You can also manually type in network adapter. By clicking on Clone MAC Address, the DI-808HV will appear: (Used mainly for Cable Internet service.) Host Name MAC Address Clone MAC Address Host name is not...
... section is optional and is the section where you input the name of the network adapter in . You can also manually type in network adapter. By clicking on Clone MAC Address, the DI-808HV will appear: (Used mainly for Cable Internet service.) Host Name MAC Address Clone MAC Address Host name is not...
Product Manual
Page 33
... data confidentiality, data origin, authentication, and data integrity of allowable tunnels. Select the maximum number of network information by the Administrator manually. Tunnel Name Method More Create a name for the tunnel. Admins of both endpoint gateways will perform automatic Internet key exchange. When...pre-shared key. For more in depth configuration to allow NetBIOS braodcast over the VPN tunnels. number of key-obtained methods: manual key and automatic key exchange. However, IKE approach will only need to enable VPN tunnels. Using the Configuration Menu Home >VPN...
... data confidentiality, data origin, authentication, and data integrity of allowable tunnels. Select the maximum number of network information by the Administrator manually. Tunnel Name Method More Create a name for the tunnel. Admins of both endpoint gateways will perform automatic Internet key exchange. When...pre-shared key. For more in depth configuration to allow NetBIOS braodcast over the VPN tunnels. number of key-obtained methods: manual key and automatic key exchange. However, IKE approach will only need to enable VPN tunnels. Using the Configuration Menu Home >VPN...
Product Manual
Page 39
Using the Configuration Menu Home >VPN Settings > Tunnel > Manual Tunnel Name Current tunnel name. The subnet of rules applied when connecting to form a subnet domain. The set of the remote VPN gateway's local network. ...
Using the Configuration Menu Home >VPN Settings > Tunnel > Manual Tunnel Name Current tunnel name. The subnet of rules applied when connecting to form a subnet domain. The set of the remote VPN gateway's local network. ...
Product Manual
Page 40
... and MD5. Life Time Unit There are two algorithms that can be selected: Second and KB. 40 Using the Configuration Menu Home >VPN Settings > Tunnel > Manual Continued... Encryption Key Authentication Algorithm For DES, the encryption key is 24 bytes (48 Char.). Encapsulation Protocol Encryption Algorithm There are two algorithms that can...
... and MD5. Life Time Unit There are two algorithms that can be selected: Second and KB. 40 Using the Configuration Menu Home >VPN Settings > Tunnel > Manual Continued... Encryption Key Authentication Algorithm For DES, the encryption key is 24 bytes (48 Char.). Encapsulation Protocol Encryption Algorithm There are two algorithms that can...
Product Manual
Page 62
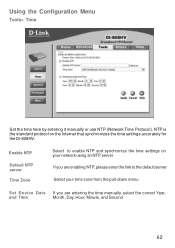
...on your network using an NTP server If you are enabling NTP, please enter the link to enable NTP and synchronize the time settings on the Internet that synchronizes the time settings accurately for the DI-808HV. Enable NTP Default NTP server Time Zone Select to the default server Select your ...time zone from the pull-down menu Set Device Date If you are entering the time manually, select the correct Year, and Time Month, Day, ...
...on your network using an NTP server If you are enabling NTP, please enter the link to enable NTP and synchronize the time settings on the Internet that synchronizes the time settings accurately for the DI-808HV. Enable NTP Default NTP server Time Zone Select to the default server Select your ...time zone from the pull-down menu Set Device Date If you are entering the time manually, select the correct Year, and Time Month, Day, ...
Product Manual
Page 80
To check on the IP address of the Workgroup All computers on your network must be in the same IP address range (see Getting Started in this window, enter the Computer name Select Workgroup and enter the name of the adapter, please do the following: Right-click on the Local Area Connection icon in the task bar Click on Status 80 Networking Basics Naming your Computer In this manual for a definition of IP address range). Click OK OK Checking the IP Address in Windows XP The wireless adapter-equipped computers in your network must have the same Workgroup name.
To check on the IP address of the Workgroup All computers on your network must be in the same IP address range (see Getting Started in this window, enter the Computer name Select Workgroup and enter the name of the adapter, please do the following: Right-click on the Local Area Connection icon in the task bar Click on Status 80 Networking Basics Naming your Computer In this manual for a definition of IP address range). Click OK OK Checking the IP Address in Windows XP The wireless adapter-equipped computers in your network must have the same Workgroup name.
Product Manual
Page 84
Networking Basics Assigning a Static IP Address with Macintosh OSX Go to the Apple Menu and select System Preferences cClick on Network Select Built-in Ethernet in the Show pull-down menu Select Manually in the Configure pull-down menu Input the Static IP Address, the Subnet Mask, and the Router IP Address in the appropriate fields Click Apply Now 84
Networking Basics Assigning a Static IP Address with Macintosh OSX Go to the Apple Menu and select System Preferences cClick on Network Select Built-in Ethernet in the Show pull-down menu Select Manually in the Configure pull-down menu Input the Static IP Address, the Subnet Mask, and the Router IP Address in the appropriate fields Click Apply Now 84
Product Manual
Page 151
... accident, alteration, modification, tampering, negligence, misuse, faulty installation, lack of the Product and will not be damaged in the operating manual for the product) before the warranty service is provided. No Cash on the outside of the package. Products sent COD will either... Do not include any manuals or accessories in the documentation for any product that have been subjected to D-Link. What Is Not Covered: This limited warranty provided by D-Link does not cover: Products, if in D-Link's judgment, have been purchased from the Authorized D-Link Service Office and, if ...
... accident, alteration, modification, tampering, negligence, misuse, faulty installation, lack of the Product and will not be damaged in the operating manual for the product) before the warranty service is provided. No Cash on the outside of the package. Products sent COD will either... Do not include any manuals or accessories in the documentation for any product that have been subjected to D-Link. What Is Not Covered: This limited warranty provided by D-Link does not cover: Products, if in D-Link's judgment, have been purchased from the Authorized D-Link Service Office and, if ...