Design Guide
Page 3
... Scanner Features Settings 57 2-3-7 Data Stored in Progress 43 2-1-4 Protection of Document Server Documents 43 2-1-5 Protection of 86 Principal Machine Functions 43 2-1 Copier (MFP Models Only 43 2-1-1 Overview of Copier Operations 43 2-1-2 Data Security Considerations 43 2-1-3 Protection of Copy Jobs in the Job Log 58 2-3-8 Terminology ...58 2-4 FAX (MFP Models Only 59...
... Scanner Features Settings 57 2-3-7 Data Stored in Progress 43 2-1-4 Protection of Document Server Documents 43 2-1-5 Protection of 86 Principal Machine Functions 43 2-1 Copier (MFP Models Only 43 2-1-1 Overview of Copier Operations 43 2-1-2 Data Security Considerations 43 2-1-3 Protection of Copy Jobs in the Job Log 58 2-3-8 Terminology ...58 2-4 FAX (MFP Models Only 59...
Design Guide
Page 4
... 77 4-1 Overview of Operations 77 4-1-1 Installation...78 4-1-2 Overview of SDK Application Functions 79 4-2 Data Flow...80 4-2-1 Scanning Functions: Sending Data Over the Network with the Copier and Scanner Page 4 of NetFile Operations 64 2-5-2 Data Flow...65 2-5-3 Supplementary...65 2-5-4 Data Security Considerations 67 2-6 Web Applications ...69 2-6-1 Web Server Framework 69 2-6-2 WebDocBox (MFP...
... 77 4-1 Overview of Operations 77 4-1-1 Installation...78 4-1-2 Overview of SDK Application Functions 79 4-2 Data Flow...80 4-2-1 Scanning Functions: Sending Data Over the Network with the Copier and Scanner Page 4 of NetFile Operations 64 2-5-2 Data Flow...65 2-5-3 Supplementary...65 2-5-4 Data Security Considerations 67 2-6 Web Applications ...69 2-6-1 Web Server Framework 69 2-6-2 WebDocBox (MFP...
Design Guide
Page 11
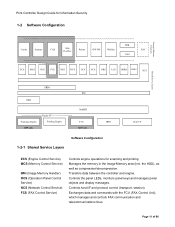
... and telecommunications lines. Manages the memory in the Image Memory area (incl. Principal Machine Functions Print Controller Design Guide for Information Security 1-2 Software Configuration SDK Copier Scanner FAX Web DocBox Printer GW WS WebSys EAC VAS ECS MCS OCS FCS NCS DCS UCS CCS NRS LCS MIRS DESS SCS S Shared Service...
... and telecommunications lines. Manages the memory in the Image Memory area (incl. Principal Machine Functions Print Controller Design Guide for Information Security 1-2 Software Configuration SDK Copier Scanner FAX Web DocBox Printer GW WS WebSys EAC VAS ECS MCS OCS FCS NCS DCS UCS CCS NRS LCS MIRS DESS SCS S Shared Service...
Design Guide
Page 12
Mediates communication between SP settings and machine operations. Controls the encryption and decryption functions. 1-2-2 Principal Machine Functions Copier Printer Scanner FAX Activates the scanning engine, which then sends the data to the controller. Secondary data, such as that converts the printer language into ...
Mediates communication between SP settings and machine operations. Controls the encryption and decryption functions. 1-2-2 Principal Machine Functions Copier Printer Scanner FAX Activates the scanning engine, which then sends the data to the controller. Secondary data, such as that converts the printer language into ...
Design Guide
Page 17
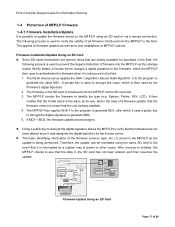
...is cancelled and new firmware is overwritten with new files Firmware Update Using an SD Card Page 17 of 86 Firmware is not 3. The Ricoh license server applies the SHA-1 algorithm (Secure Hash Algorithm 1) to the program to identify the type (e.g. Files are widely available for ...being performed. This applies to generate MD1, after which it was assigned the digital signature by a sudden loss of model and target machine functions (Copier, Printer, etc .) 2. The firmware in the SD card has not been altered, and then resumes the update. 1. The MFP/LP checks...
...is cancelled and new firmware is overwritten with new files Firmware Update Using an SD Card Page 17 of 86 Firmware is not 3. The Ricoh license server applies the SHA-1 algorithm (Secure Hash Algorithm 1) to the program to identify the type (e.g. Files are widely available for ...being performed. This applies to generate MD1, after which it was assigned the digital signature by a sudden loss of model and target machine functions (Copier, Printer, etc .) 2. The firmware in the SD card has not been altered, and then resumes the update. 1. The MFP/LP checks...
Design Guide
Page 18
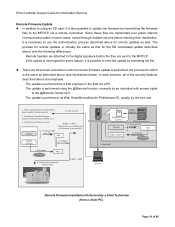
...the firmware by transmitting the firmware files to the MFP/LP via a remote connection. In each scenario, all of model and target machine functions (Copier, Printer, etc.) 3. Files are sent 2. Firmware is performed via a PC The update is performed using SHA-1 If MD1 ≠ MD... Print Controller Design Guide for the SD card-based update described above, with new files If MD1 = MD2 Digital signature Ricoh distribution server Program + digital signature Program Ricoh license server 1. If the update is possible to retry the update by a Field Technician (from a client PC) Page...
...the firmware by transmitting the firmware files to the MFP/LP via a remote connection. In each scenario, all of model and target machine functions (Copier, Printer, etc.) 3. Files are sent 2. Firmware is performed via a PC The update is performed using SHA-1 If MD1 ≠ MD... Print Controller Design Guide for the SD card-based update described above, with new files If MD1 = MD2 Digital signature Ricoh distribution server Program + digital signature Program Ricoh license server 1. If the update is possible to retry the update by a Field Technician (from a client PC) Page...
Design Guide
Page 29
... stored on another, it can be enabled/disabled in 1.7.1 above , the following data are encrypted: NVRAM: All data, except the engine adjustment parameters and some Copier screen display parameters (i.e. This eliminates the possibility of illegal system programs accessing any of 86 When the function is enabled, the following data is always...
... stored on another, it can be enabled/disabled in 1.7.1 above , the following data are encrypted: NVRAM: All data, except the engine adjustment parameters and some Copier screen display parameters (i.e. This eliminates the possibility of illegal system programs accessing any of 86 When the function is enabled, the following data is always...
Design Guide
Page 32
...user access privileges to individual users as well as viewing, editing, or deleting existing entries. Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of 86 This data can be encrypted before it is installed. Name... also able to prohibit all users registered in the HDD or SD card. Data Reg. Detailed User Info. ACL Information Note: Taroh Copier - R RW ... 00002=R--- 00003=RW-- 00004=RW-O Use ACL RW RW 00005=RWDO ... This setting effectively overrides the Address...
...user access privileges to individual users as well as viewing, editing, or deleting existing entries. Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of 86 This data can be encrypted before it is installed. Name... also able to prohibit all users registered in the HDD or SD card. Data Reg. Detailed User Info. ACL Information Note: Taroh Copier - R RW ... 00002=R--- 00003=RW-- 00004=RW-O Use ACL RW RW 00005=RWDO ... This setting effectively overrides the Address...
Design Guide
Page 40
Print Controller Design Guide for Information Security Function Copier Operation Copy job Copy job + storage to HDD Document Server Storage to Document Server Printing out of Document Server document Regular FAX transmission Regular FAX ...
Print Controller Design Guide for Information Security Function Copier Operation Copy job Copy job + storage to HDD Document Server Storage to Document Server Printing out of Document Server document Regular FAX transmission Regular FAX ...
Design Guide
Page 43
...be printed out from the printing engine. View, Edit, Delete, Full-Access). Users who originally initiated the job. In addition, since the Copier function itself does not have any external I/F and does not perform any data exchanges or communication with View privileges can successfully cancel the job ...Server function can be performed on copy jobs in the HDD. In addition, a password can be enabled to restrict access to the Copier function. 2-1-2 Data Security Considerations • Since the page location data is erased at this data to the controller to the document (incl.
...be printed out from the printing engine. View, Edit, Delete, Full-Access). Users who originally initiated the job. In addition, since the Copier function itself does not have any external I/F and does not perform any data exchanges or communication with View privileges can successfully cancel the job ...Server function can be performed on copy jobs in the HDD. In addition, a password can be enabled to restrict access to the Copier function. 2-1-2 Data Security Considerations • Since the page location data is erased at this data to the controller to the document (incl.
Design Guide
Page 45
... completion status (whether completed successfully or not) and user identification (in the HDD (via the MCS), and then use of specific Copier functions for each individual user. In addition, it is possible to set to "Level 2", changes to the Copy/Document Server Features can...the embedded patterns selected with the Copy Data Security feature (section 3.3). Print Controller Design Guide for Information Security 2-1-5 Protection of Copier/Document Server Features When Machine Administrator Authentication is enabled and the Menu Protect setting in Copy/Document Server Features is created and ...
... completion status (whether completed successfully or not) and user identification (in the HDD (via the MCS), and then use of specific Copier functions for each individual user. In addition, it is possible to set to "Level 2", changes to the Copy/Document Server Features can...the embedded patterns selected with the Copy Data Security feature (section 3.3). Print Controller Design Guide for Information Security 2-1-5 Protection of Copier/Document Server Features When Machine Administrator Authentication is enabled and the Menu Protect setting in Copy/Document Server Features is created and ...
Design Guide
Page 64
... to the PC, make changes to be viewed and changed from one . Restoring Files Back to the MFP (MFP models only) • When Copier or Printer files that were originally sent from the MFP to Desk Top Editor For Production in TIFF or JPEG format are prompted for Admin... to download Document Server files from within DeskTopBinder or Desk Top Editor For Production. Page 64 of these applications allow documents stored using the Copier, FAX and Scanner functions or those stored using the Scanner function to the bibliographic information of 86 In addition, it is also possible to...
... to the PC, make changes to be viewed and changed from one . Restoring Files Back to the MFP (MFP models only) • When Copier or Printer files that were originally sent from the MFP to Desk Top Editor For Production in TIFF or JPEG format are prompted for Admin... to download Document Server files from within DeskTopBinder or Desk Top Editor For Production. Page 64 of these applications allow documents stored using the Copier, FAX and Scanner functions or those stored using the Scanner function to the bibliographic information of 86 In addition, it is also possible to...
Design Guide
Page 70
... above-mentioned countermeasures for cross-site scripting prevent cookies from the view by WebImageMonitor do not contain any potential threat to the MFP using the Copier, Printer, Scanner and FAX functions, as well as Network Administrators. Concealment of Personal Data Even when User Authentication is performed before any requests that were...
... above-mentioned countermeasures for cross-site scripting prevent cookies from the view by WebImageMonitor do not contain any potential threat to the MFP using the Copier, Printer, Scanner and FAX functions, as well as Network Administrators. Concealment of Personal Data Even when User Authentication is performed before any requests that were...
Design Guide
Page 74
... from which the optional Copy Data Security Unit is installed on that copying of the image is provided as "Copying of the relevant MFP functions: Copier, Scanner, and FAX. If a user attempts to choose, ranging from among several patterns, as well as add a text string such as an optional ...feature on an MFP (incl. non-Ricoh products) on which to make a copy of an image containing the embedded pattern (or store the image to demarcate that MFP, the pattern will be...
... from which the optional Copy Data Security Unit is installed on that copying of the image is provided as "Copying of the relevant MFP functions: Copier, Scanner, and FAX. If a user attempts to choose, ranging from among several patterns, as well as add a text string such as an optional ...feature on an MFP (incl. non-Ricoh products) on which to make a copy of an image containing the embedded pattern (or store the image to demarcate that MFP, the pattern will be...
Design Guide
Page 80
... incoming data to the work area of HDD memory and then converted from Ricoh-original format to utilize the LAN FAX feature only. The image data is contained within the SD card along with the Copier and Scanner (MFP models only) DSDK applications are capable of utilizing the ...transmits the entire file over the network to DeskTopBinder or Desk Top Editor For Production, it from memory Printing). Page 80 of the MFP Copier and Scanner operations, please refer to utilize such features as Broadcasting or Batch Transmission. Scanning HDD storage Loading from the HDD. Print Controller...
... incoming data to the work area of HDD memory and then converted from Ricoh-original format to utilize the LAN FAX feature only. The image data is contained within the SD card along with the Copier and Scanner (MFP models only) DSDK applications are capable of utilizing the ...transmits the entire file over the network to DeskTopBinder or Desk Top Editor For Production, it from memory Printing). Page 80 of the MFP Copier and Scanner operations, please refer to utilize such features as Broadcasting or Batch Transmission. Scanning HDD storage Loading from the HDD. Print Controller...