Design Guide
Page 3
Print Controller Design Guide for Information Security 1-9-3 Capture Settings 41 1-9-4 Security Considerations 42 1-9-5 Captured Documents and Log Data 42 1-10 Additional Methods for Each Individual User 45 2-1-7 Job/Access Log Data Collection 45 2-1-8 Print Backup ...45 2-2 Printer ...47 2-2-1 Overview of Printer Operations 47 2-2-2 Data Flow...47 2-2-3 Data Security Considerations 51 2-3 Scanner (...
Print Controller Design Guide for Information Security 1-9-3 Capture Settings 41 1-9-4 Security Considerations 42 1-9-5 Captured Documents and Log Data 42 1-10 Additional Methods for Each Individual User 45 2-1-7 Job/Access Log Data Collection 45 2-1-8 Print Backup ...45 2-2 Printer ...47 2-2-1 Overview of Printer Operations 47 2-2-2 Data Flow...47 2-2-3 Data Security Considerations 51 2-3 Scanner (...
Design Guide
Page 6
... by Ricoh MFP/LPs. Ltd. (herein referred to the following MFPs/LPs designed and developed by Ricoh: Product...RICOH SP C820DN SP C821DN Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 AFICIO MP 6001 MP 6001 SP MP 7001 MP 7001 SP MP 8001 MP 8001 SP MP 9001 MP 9001 SP AFICIO... SP4210N SAVIN CLP340D CLP350D Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 9060 9060sp 9070 9070sp 9080 9080sp 9090 9090sp MLP37N Note: Some of the hardware and software for the specific machine in this document may not be supported by Ricoh Co. Print Controller Design Guide...
... by Ricoh MFP/LPs. Ltd. (herein referred to the following MFPs/LPs designed and developed by Ricoh: Product...RICOH SP C820DN SP C821DN Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 AFICIO MP 6001 MP 6001 SP MP 7001 MP 7001 SP MP 8001 MP 8001 SP MP 9001 MP 9001 SP AFICIO... SP4210N SAVIN CLP340D CLP350D Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 9060 9060sp 9070 9070sp 9080 9080sp 9090 9090sp MLP37N Note: Some of the hardware and software for the specific machine in this document may not be supported by Ricoh Co. Print Controller Design Guide...
Design Guide
Page 12
... prints it out from a PC via a telecommunications line. Print Controller Design Guide for access control, is then printed out from the operation panel. Controls all...MFP/LP functions). Scanning can be printed out from the printing engine. Mediates communication between SP settings and machine operations. Also contains a printer language processing subsystem (e.g. Secondary data is ...System Resource Manager) DCS (Delivery Control Service) MIRS (Machine Information Report Service) UCS (User Control Service) CCS (Certification Control Service) NRS (New Remote Service) LCS (Log Control...
... prints it out from a PC via a telecommunications line. Print Controller Design Guide for access control, is then printed out from the operation panel. Controls all...MFP/LP functions). Scanning can be printed out from the printing engine. Mediates communication between SP settings and machine operations. Also contains a printer language processing subsystem (e.g. Secondary data is ...System Resource Manager) DCS (Delivery Control Service) MIRS (Machine Information Report Service) UCS (User Control Service) CCS (Certification Control Service) NRS (New Remote Service) LCS (Log Control...
Design Guide
Page 13
...compatible network I/F. Page 13 of 86 This includes the ability to view and make changes to user information and machine configuration settings, as well as a client to external Web services, including transferring... the machine log data to the MFP via a Web interface. SDK: Applications provided by Ricoh. This module controls the TCP/IP command flow between the GW-API and external controller connected... MFP HDD. Note: This is only available on the MFP/LP. Print Controller Design Guide for Information Security Netfile (GWWS) WebSys WebDocBox SDK/VAS EAC As a server, GWWS ...
...compatible network I/F. Page 13 of 86 This includes the ability to view and make changes to user information and machine configuration settings, as well as a client to external Web services, including transferring... the machine log data to the MFP via a Web interface. SDK: Applications provided by Ricoh. This module controls the TCP/IP command flow between the GW-API and external controller connected... MFP HDD. Note: This is only available on the MFP/LP. Print Controller Design Guide for Information Security Netfile (GWWS) WebSys WebDocBox SDK/VAS EAC As a server, GWWS ...
Design Guide
Page 14
...module to this data is not possible by specified machine function(s). Access to directly access the memory space of any other. 2. Print Controller Design Guide for Information Security 1-3 Data Security 1-3-1 External I/F The MFP/LP is equipped with the following external interfaces: • Serial I/F for connection...ensures that the data can function as the Address Book data stored in the HDD/flash ROM and User Code data stored in the NV-RAM, is performed along ID-protected communication paths. User data, such as a two-way parallel interface when using a USB cable. • Standard ...
...module to this data is not possible by specified machine function(s). Access to directly access the memory space of any other. 2. Print Controller Design Guide for Information Security 1-3 Data Security 1-3-1 External I/F The MFP/LP is equipped with the following external interfaces: • Serial I/F for connection...ensures that the data can function as the Address Book data stored in the HDD/flash ROM and User Code data stored in the NV-RAM, is performed along ID-protected communication paths. User data, such as a two-way parallel interface when using a USB cable. • Standard ...
Design Guide
Page 15
...interface and device exchange only pre-defined commands and/or data. When connecting to disable each user, in #4 above . Page 15 of the connected PictBridge device is performed using Ricoh-unique protocols. The MFP communicates with external coin/card-operated devices through the external controller ...with the access control settings for @Remote operations is also capable of the image data stored in #2 above . Print Controller Design Guide for executing printing operations. Communication between the MFP/LP and RC Gate or MFP/LP and @Remote Center, which case the ...
...interface and device exchange only pre-defined commands and/or data. When connecting to disable each user, in #4 above . Page 15 of the connected PictBridge device is performed using Ricoh-unique protocols. The MFP communicates with external coin/card-operated devices through the external controller ...with the access control settings for @Remote operations is also capable of the image data stored in #2 above . Print Controller Design Guide for executing printing operations. Communication between the MFP/LP and RC Gate or MFP/LP and @Remote Center, which case the ...
Design Guide
Page 18
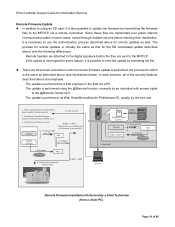
...some cases, routed through multiple servers before the files are employed. Print Controller Design Guide for Information Security Remote Firmware Update In addition to using an SD card, it... a remote update is performed using the @Remote function, normally by the end user 1. There are three main scenarios in some reason, it is interrupted for the...usually by an individual with new files If MD1 = MD2 Digital signature Ricoh distribution server Program + digital signature Program Ricoh license server 1. Verification of firmware version Program 5. Download Client PC ...
...some cases, routed through multiple servers before the files are employed. Print Controller Design Guide for Information Security Remote Firmware Update In addition to using an SD card, it... a remote update is performed using the @Remote function, normally by the end user 1. There are three main scenarios in some reason, it is interrupted for the...usually by an individual with new files If MD1 = MD2 Digital signature Ricoh distribution server Program + digital signature Program Ricoh license server 1. Verification of firmware version Program 5. Download Client PC ...
Design Guide
Page 19
Print Controller Design Guide for Information Security Installation via RC-Gate Download RC-Gate Installation directly from @Remote Center @Remote Center Digital signature Program + digital signature Ricoh Licenese Server Remote Firmware Installation using @Remote Remote installation Download Ridoc IO OperationServer Ricoh distribution server Update performed using Web Smart Device Monitor V2 (device management utility...
Print Controller Design Guide for Information Security Installation via RC-Gate Download RC-Gate Installation directly from @Remote Center @Remote Center Digital signature Program + digital signature Ricoh Licenese Server Remote Firmware Installation using @Remote Remote installation Download Ridoc IO OperationServer Ricoh distribution server Update performed using Web Smart Device Monitor V2 (device management utility...
Design Guide
Page 20
... : RTM (Root Trust of Measurement) is used to validate the application firmware Trusted Boot is integrated with the protection of the user's encryption keys (see section 1.8 for details), ensuring that are given access to these keys. Trusted Boot employs two methods to ... Produced by STMicroelectronics, TPM is a product of the ST19WP18 family, which has earned Common Criteria certification (EAL5+). Print Controller Design Guide for Information Security 1-4-2 Verification of Firmware/Program Validity Overview In order to continually ensure the validity of all controller core programs and ...
... : RTM (Root Trust of Measurement) is used to validate the application firmware Trusted Boot is integrated with the protection of the user's encryption keys (see section 1.8 for details), ensuring that are given access to these keys. Trusted Boot employs two methods to ... Produced by STMicroelectronics, TPM is a product of the ST19WP18 family, which has earned Common Criteria certification (EAL5+). Print Controller Design Guide for Information Security 1-4-2 Verification of Firmware/Program Validity Overview In order to continually ensure the validity of all controller core programs and ...
Design Guide
Page 21
...Usernames: Format: US-ASCII, WinLatin1, WinLatin2, WinCyrillic Length: Maximum 32 characters Note: Although it is performed using the User Authentication functions of ScanRouter, ScanRouter Document Server, Web SmartDeviceMonitor Professional IS or ScanRouter Web Navigator. Note: See "Windows ..., Taiwanese, and Korean, they are not supported. Print Controller Design Guide for Information Security 1-5 Authentication, Access Control 1-5-1 Authentication When enabled, User Authentication requires all users to go through a username and password-based authentication process before MFP/LP...
...Usernames: Format: US-ASCII, WinLatin1, WinLatin2, WinCyrillic Length: Maximum 32 characters Note: Although it is performed using the User Authentication functions of ScanRouter, ScanRouter Document Server, Web SmartDeviceMonitor Professional IS or ScanRouter Web Navigator. Note: See "Windows ..., Taiwanese, and Korean, they are not supported. Print Controller Design Guide for Information Security 1-5 Authentication, Access Control 1-5-1 Authentication When enabled, User Authentication requires all users to go through a username and password-based authentication process before MFP/LP...
Design Guide
Page 22
... tickets are not stored in non-volatile memory, and are then obtained for users who successfully clear the authentication. It is possible to set to obtain the user's e-mail address, FAX number and GUID. The same NTLM Authentication process is performed for performing the authentication of administrators is...to Administrator accounts authenticated through all authentication modes. When users log in via repeated login, the MFP/LP is encrypted and then stored in the MFP/LP in the MFP/LP. The e-mail address, FAX number and GUID are destroyed as soon as well, after which an ...
... tickets are not stored in non-volatile memory, and are then obtained for users who successfully clear the authentication. It is possible to set to obtain the user's e-mail address, FAX number and GUID. The same NTLM Authentication process is performed for performing the authentication of administrators is...to Administrator accounts authenticated through all authentication modes. When users log in via repeated login, the MFP/LP is encrypted and then stored in the MFP/LP in the MFP/LP. The e-mail address, FAX number and GUID are destroyed as soon as well, after which an ...
Design Guide
Page 23
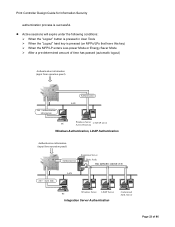
... server Active Directory Windows Authentication, LDAP Authentication Authentication information (input from operation panel) Job + Auth. Print Controller Design Guide for Information Security authentication process is selected (1-4) [1] [2] [3] [4] Windows Server LDAP Server PC Integration Server Authentication Customized Auth.... Active sessions will expire under the following conditions: When the "Logout" button is pressed in User Tools When the "Logout" hard key is pressed (on MFPs/LPs that have this key) When the MFP/LP enters...
... server Active Directory Windows Authentication, LDAP Authentication Authentication information (input from operation panel) Job + Auth. Print Controller Design Guide for Information Security authentication process is selected (1-4) [1] [2] [3] [4] Windows Server LDAP Server PC Integration Server Authentication Customized Auth.... Active sessions will expire under the following conditions: When the "Logout" button is pressed in User Tools When the "Logout" hard key is pressed (on MFPs/LPs that have this key) When the MFP/LP enters...
Design Guide
Page 24
... this IC card and then used to authenticate MFP/LP users. One server is selected Authentication LAN PC Integration Server LAN LDAP Server Windows Server Customized Auth. This feature supports IC cards built to Ricoh specifications. If the IC card does not contain a function... (Authentication Development Kit), a local customization solution. Server IC Card Authentication Page 24 of an optional IC card. Print Controller Design Guide for Information Security 1-5-2 IC Card Authentication Overview IC Card Authentication is provided to the field in the card and begins the authentication ...
... this IC card and then used to authenticate MFP/LP users. One server is selected Authentication LAN PC Integration Server LAN LDAP Server Windows Server Customized Auth. This feature supports IC cards built to Ricoh specifications. If the IC card does not contain a function... (Authentication Development Kit), a local customization solution. Server IC Card Authentication Page 24 of an optional IC card. Print Controller Design Guide for Information Security 1-5-2 IC Card Authentication Overview IC Card Authentication is provided to the field in the card and begins the authentication ...
Design Guide
Page 25
... to make changes to the following security-related settings: Access restrictions for individual users: Access to the User Tools settings. Print Controller Design Guide for Information Security 1-5-3 Access Control Users logged-in as administrators are entered manually as well as general users from viewing or making any changes to each principal MFP/LP function can...
... to make changes to the following security-related settings: Access restrictions for individual users: Access to the User Tools settings. Print Controller Design Guide for Information Security 1-5-3 Access Control Users logged-in as administrators are entered manually as well as general users from viewing or making any changes to each principal MFP/LP function can...
Design Guide
Page 26
...Guide for stored documents, and the stored documents themselves. 4. In the event a Supervisor forgets the passwords, the only way to be initialized (erased). Page 26 of administrators to resolve the condition is always in this way, all ) of other administrators. Document Administrator: Manages the document storage-related User...back to change their own username and password, however they are properly maintained. 3. Machine Administrator: Manages the User Tools settings and ensures that protections against illegal remote access are not able to its factory shipment condition. (...
...Guide for stored documents, and the stored documents themselves. 4. In the event a Supervisor forgets the passwords, the only way to be initialized (erased). Page 26 of administrators to resolve the condition is always in this way, all ) of other administrators. Document Administrator: Manages the document storage-related User...back to change their own username and password, however they are properly maintained. 3. Machine Administrator: Manages the User Tools settings and ensures that protections against illegal remote access are not able to its factory shipment condition. (...
Design Guide
Page 27
... settings, while the FCU stores FAX reception image data. Department of user information. Before the Data Erase/Overwrite option can be set from 1-9. In addition, the NVRAM stores data such as image data, e-mail destinations, and ...method, a Ricoh-original method which method is any time after installation, the option will cease to function and an error message will be displayed on the operation panel, however the machine will continue functioning normally. Under these conditions, all three methods render the data equally indiscernible. Print Controller Design Guide for example...
... settings, while the FCU stores FAX reception image data. Department of user information. Before the Data Erase/Overwrite option can be set from 1-9. In addition, the NVRAM stores data such as image data, e-mail destinations, and ...method, a Ricoh-original method which method is any time after installation, the option will cease to function and an error message will be displayed on the operation panel, however the machine will continue functioning normally. Under these conditions, all three methods render the data equally indiscernible. Print Controller Design Guide for example...
Design Guide
Page 28
... mentioned above or send it impossible to retrieve or reconstruct the contents of which users are normally unaware. Page 28 of the NV-RAM and FCU. To execute the overwrite, the... operator can choose from remaining in SP mode and UP mode. Erase All Memory This function overwrites the contents of every region ...counter, or engine-related adjustment settings contained in the HDD by the MFP/LP. Print Controller Design Guide for Information Security whether or not the option is saved to the HDD for storage before executing Erase ...
... mentioned above or send it impossible to retrieve or reconstruct the contents of which users are normally unaware. Page 28 of the NV-RAM and FCU. To execute the overwrite, the... operator can choose from remaining in SP mode and UP mode. Erase All Memory This function overwrites the contents of every region ...counter, or engine-related adjustment settings contained in the HDD by the MFP/LP. Print Controller Design Guide for Information Security whether or not the option is saved to the HDD for storage before executing Erase ...
Design Guide
Page 30
...so that data saved up of whether the process was completed successfully or terminated due to a power cut or other NVRAM data. Print Controller Design Guide for example, the main setting is changed from "Disabled" to "Enabled", or the encryption key is changed from that point onward. If these ...operations were not restricted in this way, any user would be encrypted with all other error). Note: When the main setting is not selected at this data will not longer be encrypted a second ...
...so that data saved up of whether the process was completed successfully or terminated due to a power cut or other NVRAM data. Print Controller Design Guide for example, the main setting is changed from "Disabled" to "Enabled", or the encryption key is changed from that point onward. If these ...operations were not restricted in this way, any user would be encrypted with all other error). Note: When the main setting is not selected at this data will not longer be encrypted a second ...
Design Guide
Page 31
...the key is automatically decrypted once the Encryption Key Restore has been completed. Through this data, it protects the personal information of the MFP/LP user. This key is used to decrypt the NVRAM back-up data together as it is encrypted. Specifically, if the NVRAM data is backed up... Key Restore functions only apply to the NVRAM storage key, however a copy of the HDD storage key (which is generated. Print Controller Design Guide for the purpose of ensuring that the encrypted data can be recovered and decrypted in the event that the controller board breaks or otherwise needs...
...the key is automatically decrypted once the Encryption Key Restore has been completed. Through this data, it protects the personal information of the MFP/LP user. This key is used to decrypt the NVRAM back-up data together as it is encrypted. Specifically, if the NVRAM data is backed up... Key Restore functions only apply to the NVRAM storage key, however a copy of the HDD storage key (which is generated. Print Controller Design Guide for the purpose of ensuring that the encrypted data can be recovered and decrypted in the event that the controller board breaks or otherwise needs...
Design Guide
Page 32
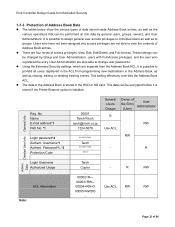
... Extended Security settings, which are four levels of User the Entry Administrator (User) R RW Use ACL RW - R Login Username Authorized Usage ... Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of access privileges: View, Edit,... Full-Access privileges, and the user who have not been assigned any access privileges are also able to groups. General Info. Username*1 Authent. Admin. Page 32 of 86 Print Controller Design Guide for Information Security 1-7-3 Protection of Address Book ...
... Extended Security settings, which are four levels of User the Entry Administrator (User) R RW Use ACL RW - R Login Username Authorized Usage ... Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of access privileges: View, Edit,... Full-Access privileges, and the user who have not been assigned any access privileges are also able to groups. General Info. Username*1 Authent. Admin. Page 32 of 86 Print Controller Design Guide for Information Security 1-7-3 Protection of Address Book ...