Design Guide
Page 6
... as the information security of image data and other information handled internally by Ricoh MFP/LPs. external I/F) and functions described in this document may not be supported by the end user's machine. Print Controller Design Guide for Information Security Overview This document describes the structural layout and functional operations of the hardware and software for the specific machine in question.
... as the information security of image data and other information handled internally by Ricoh MFP/LPs. external I/F) and functions described in this document may not be supported by the end user's machine. Print Controller Design Guide for Information Security Overview This document describes the structural layout and functional operations of the hardware and software for the specific machine in question.
Design Guide
Page 8
... the external charge device I/F and external coin/card-operated devices. • External controller I/F board: Acts as the interface between the MFP and external controller. • File Format Converter: Converts the file format of image files. • RC Gate: Intermediary device connected to the MFP/LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an...
... the external charge device I/F and external coin/card-operated devices. • External controller I/F board: Acts as the interface between the MFP and external controller. • File Format Converter: Converts the file format of image files. • RC Gate: Intermediary device connected to the MFP/LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an...
Design Guide
Page 12
Print Controller Design Guide for access control, is handled from the operation panel. Controls all internal operations performed on to the controller to a PC via a TWAIN driver. Controls the sending of 86 Address Book, Document Server, MFP/LP functions). Receives image data through the host interface, which reads the original and then sends the data to be printed out from the printing engine. Activates the scanning engine, which then...
Print Controller Design Guide for access control, is handled from the operation panel. Controls all internal operations performed on to the controller to a PC via a TWAIN driver. Controls the sending of 86 Address Book, Document Server, MFP/LP functions). Receives image data through the host interface, which reads the original and then sends the data to be printed out from the printing engine. Activates the scanning engine, which then...
Design Guide
Page 13
... Ricoh. Page 13 of 86 GWWS also acts as a client to external Web services, including transferring the machine log data to be viewed and changed via a Web interface. The EAC allows the external controller to initiate MFP operations such as print jobs and scan jobs, as well as to the MFP HDD. This includes the ability to view and make changes to user information and machine configuration settings...
... Ricoh. Page 13 of 86 GWWS also acts as a client to external Web services, including transferring the machine log data to be viewed and changed via a Web interface. The EAC allows the external controller to initiate MFP operations such as print jobs and scan jobs, as well as to the MFP HDD. This includes the ability to view and make changes to user information and machine configuration settings...
Design Guide
Page 14
... External Device 1. Print Controller Design Guide for Information Security 1-3 Data Security 1-3-1 External I/F The MFP/LP is equipped with the following external interfaces: • Serial I/F for connection of external coin/card-operated devices. • Serial I/F for all shared service layers, run on the HDD or stored temporarily in the NV-RAM, is performed along ID-protected communication paths. Access to perform FAX data operations. Memory space...
... External Device 1. Print Controller Design Guide for Information Security 1-3 Data Security 1-3-1 External I/F The MFP/LP is equipped with the following external interfaces: • Serial I/F for connection of external coin/card-operated devices. • Serial I/F for all shared service layers, run on the HDD or stored temporarily in the NV-RAM, is performed along ID-protected communication paths. Access to perform FAX data operations. Memory space...
Design Guide
Page 17
... is cancelled and new firmware is overwritten with new files Firmware Update Using an SD Card Page 17 of 86 Files are widely available for Information Security 1-4 Protection of MFP/LP Firmware 1-4-1 Firmware Installation/Update It is possible to update the firmware stored on the MFP/LP using the same SD card in the SD card has not been altered, and then resumes the update. 1. Generate digital signature Private key 4. Print Controller Design Guide...
... is cancelled and new firmware is overwritten with new files Firmware Update Using an SD Card Page 17 of 86 Files are widely available for Information Security 1-4 Protection of MFP/LP Firmware 1-4-1 Firmware Installation/Update It is possible to update the firmware stored on the MFP/LP using the same SD card in the SD card has not been altered, and then resumes the update. 1. Generate digital signature Private key 4. Print Controller Design Guide...
Design Guide
Page 24
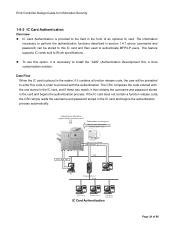
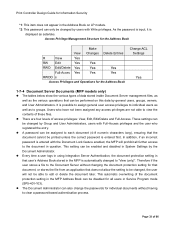
... PC Integration Server LAN LDAP Server Windows Server Customized Auth. Info. This feature supports IC cards built to Ricoh specifications. Authentication information (input from the operation panel) Information is encrypted Authentication information (stored in the form of 86 One server is necessary to install the "ADK" (Authentication Development Kit), a local customization solution. To use this code in the card and begins the authentication process. Print Controller Design Guide for Information...
... PC Integration Server LAN LDAP Server Windows Server Customized Auth. Info. This feature supports IC cards built to Ricoh specifications. Authentication information (input from the operation panel) Information is encrypted Authentication information (stored in the form of 86 One server is necessary to install the "ADK" (Authentication Development Kit), a local customization solution. To use this code in the card and begins the authentication process. Print Controller Design Guide for Information...
Design Guide
Page 27
Print Controller Design Guide for example, although the MFP/LP completely erases the page location data (the storage location information necessary to function and an error message will continue functioning normally. In addition, the NVRAM stores data such as image data, e-mail destinations, and Address Book data containing various types of the HDD. Data stored on the magnetic media of data is performed once). In rare cases, performing the...
Print Controller Design Guide for example, although the MFP/LP completely erases the page location data (the storage location information necessary to function and an error message will continue functioning normally. In addition, the NVRAM stores data such as image data, e-mail destinations, and Address Book data containing various types of the HDD. Data stored on the magnetic media of data is performed once). In rare cases, performing the...
Design Guide
Page 32
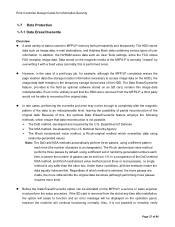
... entries. Admin. Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of 86 Page 32 of User the Entry Administrator (User) R RW Use ACL RW - R Login Username Authorized Usage ... Data Reg. The data in the HDD or SD card. Print Controller Design Guide for Information Security 1-7-3 Protection of Address Book Data The tables below show the various types of data stored inside Address Book...
... entries. Admin. Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of 86 Page 32 of User the Entry Administrator (User) R RW Use ACL RW - R Login Username Authorized Usage ... Data Reg. The data in the HDD or SD card. Print Controller Design Guide for Information Security 1-7-3 Protection of Address Book Data The tables below show the various types of data stored inside Address Book...
Design Guide
Page 33
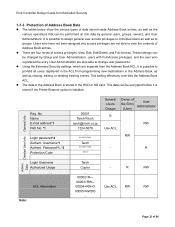
... Settings Yes 1-7-4 Document Server Documents (MFP models only) The tables below show the various types of the document protection setting in the MFP Address Book can be changed to groups. This setting can be able to clear a password-based authentication process. Print Controller Design Guide for Information Security *1: This item does not appear in System Settings by the Document Administrator. Therefore if the user stores a file...
... Settings Yes 1-7-4 Document Server Documents (MFP models only) The tables below show the various types of the document protection setting in the MFP Address Book can be changed to groups. This setting can be able to clear a password-based authentication process. Print Controller Design Guide for Information Security *1: This item does not appear in System Settings by the Document Administrator. Therefore if the user stores a file...
Design Guide
Page 45
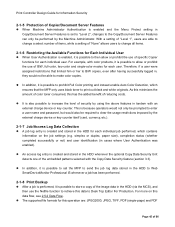
... set to "Level 2", changes to the Copy/Document Server Features can only be able to Desk Top Editor For Production. The supported file formats for each individual user. With a setting of "Level 1", users are : JPEG2000, JPEG, TIFF, PDF (single-page) and PDF Page 45 of the image data in the HDD (via the MCS), and then use the Netfile function to print out black and white originals. An access...
... set to "Level 2", changes to the Copy/Document Server Features can only be able to Desk Top Editor For Production. The supported file formats for each individual user. With a setting of "Level 1", users are : JPEG2000, JPEG, TIFF, PDF (single-page) and PDF Page 45 of the image data in the HDD (via the MCS), and then use the Netfile function to print out black and white originals. An access...
Design Guide
Page 49
.... The information stored includes the username, number of pages, the time the print job was performed, and job status/results. The password is registered in volatile memory and is therefore deleted when the MFP/LP main power is converted to image data, stored to print out an encrypted PDF file. the Function Pallet). After this, the decrypted data is turned off . • The user ID can be erased.
.... The information stored includes the username, number of pages, the time the print job was performed, and job status/results. The password is registered in volatile memory and is therefore deleted when the MFP/LP main power is converted to image data, stored to print out an encrypted PDF file. the Function Pallet). After this, the decrypted data is turned off . • The user ID can be erased.
Design Guide
Page 54
... data from a network-connected client PC, after the MFP main power is possible to pre-programmed e-mail addresses, folders and forwarding servers only. When sending the file in non-volatile memory, i.e. Print Controller Design Guide for Information Security 2-3 Scanner (MFP Models Only) 2-3-1 Overview of Scanner Operations • Depending on the settings selected, the Scanner function does one of the following: 1) Saves the scanned image...
... data from a network-connected client PC, after the MFP main power is possible to pre-programmed e-mail addresses, folders and forwarding servers only. When sending the file in non-volatile memory, i.e. Print Controller Design Guide for Information Security 2-3 Scanner (MFP Models Only) 2-3-1 Overview of Scanner Operations • Depending on the settings selected, the Scanner function does one of the following: 1) Saves the scanned image...
Design Guide
Page 55
... to retrieve e-mail addresses from a list of pre-registered senders and then enter a protection code, it is not possible to send the e-mail. - Print Controller Design Guide for Information Security password necessary to open the encrypted PDF data at the MFP and the forwarding server software must first set the MFP or related software to perform the following operations: - This makes it is forwarded to...
... to retrieve e-mail addresses from a list of pre-registered senders and then enter a protection code, it is not possible to send the e-mail. - Print Controller Design Guide for Information Security password necessary to open the encrypted PDF data at the MFP and the forwarding server software must first set the MFP or related software to perform the following operations: - This makes it is forwarded to...
Design Guide
Page 58
... (in cases where User Authentication was enabled). Note: The Ricoh MFP(s) to the job log stored in the HDD. The entry contains information on job and access logs, please refer to 1.9 Job/Access Logs. 2-3-8 Terminology • SMTP (Simple Mail Transfer Protocol) [RFC2822]: A protocol used for the transmission of e-mail over a TCP/IP network. Page 58 of 86 Print Controller Design Guide for Information Security MFP...
... (in cases where User Authentication was enabled). Note: The Ricoh MFP(s) to the job log stored in the HDD. The entry contains information on job and access logs, please refer to 1.9 Job/Access Logs. 2-3-8 Terminology • SMTP (Simple Mail Transfer Protocol) [RFC2822]: A protocol used for the transmission of e-mail over a TCP/IP network. Page 58 of 86 Print Controller Design Guide for Information Security MFP...
Design Guide
Page 70
... the job history and other personal data from being illegally accessed Cookies created by WebImageMonitor do not contain any requests that malicious data cannot be changed by limiting the length of 86 Print Controller Design Guide for Information Security Protection Against URL Buffer Overflows URL buffer overflow attacks occur when intentionally oversized URL strings are sent to a Web server with...
... the job history and other personal data from being illegally accessed Cookies created by WebImageMonitor do not contain any requests that malicious data cannot be changed by limiting the length of 86 Print Controller Design Guide for Information Security Protection Against URL Buffer Overflows URL buffer overflow attacks occur when intentionally oversized URL strings are sent to a Web server with...
Design Guide
Page 71
... list of 86 Users who do not provide an authorized IP address are able to perform operations that each registered user is capable of the data in as attach a digital signature. In addition, it is possible to place limits on Document Server files. Print Controller Design Guide for Information Security Data Flow WebDocBox supports HTTP, a protocol used by allowing connection only with users who provide a specific...
... list of 86 Users who do not provide an authorized IP address are able to perform operations that each registered user is capable of the data in as attach a digital signature. In addition, it is possible to place limits on Document Server files. Print Controller Design Guide for Information Security Data Flow WebDocBox supports HTTP, a protocol used by allowing connection only with users who provide a specific...
Design Guide
Page 76
Print Controller Design Guide for Information Security Special pattern embedded when image is printed out MFP with optional Copy Data Security Unit installed and enabled Contract When pattern is detected, buzzer sounds and image is replaced with Copy Data Security setting disabled, ・ MFP without Copy Data Security Unit, or ・ Non-Ricoh product Buzzer Contract ‥J‥a‥n‥. ‥1‥'05 ‥‥‥ Previous deterrent feature still used Pattern cannot...
Print Controller Design Guide for Information Security Special pattern embedded when image is printed out MFP with optional Copy Data Security Unit installed and enabled Contract When pattern is detected, buzzer sounds and image is replaced with Copy Data Security setting disabled, ・ MFP without Copy Data Security Unit, or ・ Non-Ricoh product Buzzer Contract ‥J‥a‥n‥. ‥1‥'05 ‥‥‥ Previous deterrent feature still used Pattern cannot...
Design Guide
Page 78
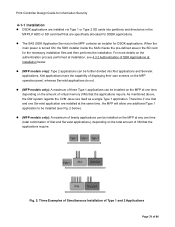
... Examples of Simultaneous Installation of Type 1 and 2 Applications Page 78 of virtual memory (VM) that the applications require. Print Controller Design Guide for Information Security 4-1-1 Installation DSDK applications are specifically allocated for DSDK applications. When the main power is turned ON, the SDK installer inside the SAS checks the pre-defined area in the MPF contains an installer for the necessary installation files and then performs...
... Examples of Simultaneous Installation of Type 1 and 2 Applications Page 78 of virtual memory (VM) that the applications require. Print Controller Design Guide for Information Security 4-1-1 Installation DSDK applications are specifically allocated for DSDK applications. When the main power is turned ON, the SDK installer inside the SAS checks the pre-defined area in the MPF contains an installer for the necessary installation files and then performs...
Design Guide
Page 81
Print Controller Design Guide for Information Security 4-2-3 Network Functions As mentioned above, a Type 1 SDK application is able to perform network communication either by using the GWWS function as the paper tray selection or printing mode. The data then follows the normal flow described in section 1.5.2. The user interface can be customized for communication with the IC Card Authentication explained in section 2.2 and is installed on the PC are...
Print Controller Design Guide for Information Security 4-2-3 Network Functions As mentioned above, a Type 1 SDK application is able to perform network communication either by using the GWWS function as the paper tray selection or printing mode. The data then follows the normal flow described in section 1.5.2. The user interface can be customized for communication with the IC Card Authentication explained in section 2.2 and is installed on the PC are...