Security Guide
Page 1
Nokia VPN Appliance FIPS 140-2 Cryptographic Module Security Policy Level 2 Validation Version 1.7 Aug 2007 Module Hardware Versions: IP260, IP265, IP1220, and IP1260 Firmware Versions: IPSO v3.9 and v4.1 Check Point VPN-1 NGX (R60) [HFA-03] © Copyright 2005, 2006, 2007 Nokia This document may be freely reproduced and distributed whole and intact including this Copyright Notice.
Nokia VPN Appliance FIPS 140-2 Cryptographic Module Security Policy Level 2 Validation Version 1.7 Aug 2007 Module Hardware Versions: IP260, IP265, IP1220, and IP1260 Firmware Versions: IPSO v3.9 and v4.1 Check Point VPN-1 NGX (R60) [HFA-03] © Copyright 2005, 2006, 2007 Nokia This document may be freely reproduced and distributed whole and intact including this Copyright Notice.
Security Guide
Page 4
... for unicast traffic and DVMRP for IPSO The Nokia VPN Appliances are rack mounted devices that are : • Read/write and read-only access modes • Screening of 43 This document may be freely reproduced and distributed whole and intact including this Security Policy: Model IP260 IP265 IP1220 IP1260 CPU Type Celeron Celeron Xeon...
... for unicast traffic and DVMRP for IPSO The Nokia VPN Appliances are rack mounted devices that are : • Read/write and read-only access modes • Screening of 43 This document may be freely reproduced and distributed whole and intact including this Security Policy: Model IP260 IP265 IP1220 IP1260 CPU Type Celeron Celeron Xeon...
Security Guide
Page 5
...ƒ IP1220 / IP1260 - The following hardware versions: ƒ IP260 / IP265 - therefore the Check Point module binary image was packaged into each module. The Nokia VPN Appliances run the Nokia proprietary, security-hardened IPSO operating system along with Check Point VPN-1 NGX (R60) [HFA-... the cryptographic boundary of each of the Nokia VPN Appliance configurations and was performed and validation certificates obtained for all hardware and firmware configurations listed in this document. All FRU upgrades are secured with identical components). This includes separate algorithm...
...ƒ IP1220 / IP1260 - The following hardware versions: ƒ IP260 / IP265 - therefore the Check Point module binary image was packaged into each module. The Nokia VPN Appliances run the Nokia proprietary, security-hardened IPSO operating system along with Check Point VPN-1 NGX (R60) [HFA-... the cryptographic boundary of each of the Nokia VPN Appliance configurations and was performed and validation certificates obtained for all hardware and firmware configurations listed in this document. All FRU upgrades are secured with identical components). This includes separate algorithm...
Security Guide
Page 27
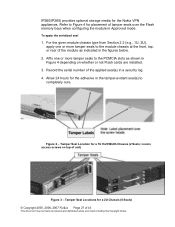
..., or rear of the module as shown in Approved mode. covers access screws on whether or not Flash cards are installed. 3. IP260/IP265) provides optional storage media for a 1U Half-Width Chassis (2 Seals; Record the serial number of tamper seals over the Flash memory bays... and distributed whole and intact including this Copyright Notice. Tamper Seal Location for the Nokia VPN appliances. Refer to completely cure. To apply the serialized seal 1. Allow 24 hours for the adhesive in a security log. 4. Tamper Seal Locations for placement of the applied seal(s) in the tamper...
..., or rear of the module as shown in Approved mode. covers access screws on whether or not Flash cards are installed. 3. IP260/IP265) provides optional storage media for a 1U Half-Width Chassis (2 Seals; Record the serial number of tamper seals over the Flash memory bays... and distributed whole and intact including this Copyright Notice. Tamper Seal Location for the Nokia VPN appliances. Refer to completely cure. To apply the serialized seal 1. Allow 24 hours for the adhesive in a security log. 4. Tamper Seal Locations for placement of the applied seal(s) in the tamper...