Security Guide
Page 2
... 2.8 CRYPTOGRAPHIC KEY MANAGEMENT 17 2.8.1 Key Generation 23 2.8.2 Key Establishment 23 2.8.3 Key Entry and Output 23 2.8.4 Key Storage 23 2.8.5 Key Zeroization 23 2.9 SELF-TESTS...24 2.10 DESIGN ASSURANCE 25 2.11 MITIGATION OF OTHER ATTACKS 25 3 SECURE OPERATION (APPROVED MODE 26 3.1 CRYPTO OFFICER GUIDANCE 26 3.1.1 Hardware Setup 26 3.1.2 Installing, Upgrading or Downgrading the Module Firmware 28 3.1.3 Initializing Check Point Modules 31 3.1.4 Setting the Module to FIPS Mode 32 3.1.5 Initializing the Remote Management of 43 This document may...
... 2.8 CRYPTOGRAPHIC KEY MANAGEMENT 17 2.8.1 Key Generation 23 2.8.2 Key Establishment 23 2.8.3 Key Entry and Output 23 2.8.4 Key Storage 23 2.8.5 Key Zeroization 23 2.9 SELF-TESTS...24 2.10 DESIGN ASSURANCE 25 2.11 MITIGATION OF OTHER ATTACKS 25 3 SECURE OPERATION (APPROVED MODE 26 3.1 CRYPTO OFFICER GUIDANCE 26 3.1.1 Hardware Setup 26 3.1.2 Installing, Upgrading or Downgrading the Module Firmware 28 3.1.3 Initializing Check Point Modules 31 3.1.4 Setting the Module to FIPS Mode 32 3.1.5 Initializing the Remote Management of 43 This document may...
Security Guide
Page 3
... 2 validation of Nokia's IPSO firmware version 4.1. The Nokia Web site (http://www.nokia.com/) contains information on the full line of a FIPS 140-2 cryptographic module security policy. This Security Policy adds additional hardware versions to run the module in the technical terms of products from Nokia. The additional hardware platforms included in this document simply support different numbers of Nokia FIPS 140-2 tested cryptographic modules. Additional information regarding the Check Point VPN-1 firmware that require retesting...
... 2 validation of Nokia's IPSO firmware version 4.1. The Nokia Web site (http://www.nokia.com/) contains information on the full line of a FIPS 140-2 cryptographic module security policy. This Security Policy adds additional hardware versions to run the module in the technical terms of products from Nokia. The additional hardware platforms included in this document simply support different numbers of Nokia FIPS 140-2 tested cryptographic modules. Additional information regarding the Check Point VPN-1 firmware that require retesting...
Security Guide
Page 4
... devices that are differentiated through the use of all modules greatly accelerate the embedded Check Point VPN-1/FireWall-1 performance by using the Nokia Firewall Flows. As VPN platforms, all incoming communications to ensure authorized user access • SSH-secured remote management of the modules (IPSO) • SSHv1 and SSHv2 supported • TLS-secured remote management of Check Point applications • Secure VPN between subsystems • Multiple layers of authentication required when accessing the remote management interface for multicast traffic. 2 NOKIA VPN APPLIANCE...
... devices that are differentiated through the use of all modules greatly accelerate the embedded Check Point VPN-1/FireWall-1 performance by using the Nokia Firewall Flows. As VPN platforms, all incoming communications to ensure authorized user access • SSH-secured remote management of the modules (IPSO) • SSHv1 and SSHv2 supported • TLS-secured remote management of Check Point applications • Secure VPN between subsystems • Multiple layers of authentication required when accessing the remote management interface for multicast traffic. 2 NOKIA VPN APPLIANCE...
Security Guide
Page 5
...document. The following hardware versions: ƒ IP260 / IP265 - therefore the Check Point module binary image was performed and validation certificates obtained for Field Replaceable Unit (FRU) upgrades to internal network interface cards, hard drives, FLASH memory, and other components (e.g., fans and power supplies replaced with Check Point VPN-1 NGX (R60) [HFA-03] The cryptographic modules implement the same version of the module to service or install these internal components. 2.2 Cryptographic Module The Nokia VPN Appliances were tested as part of the complete Nokia VPN Appliance...
...document. The following hardware versions: ƒ IP260 / IP265 - therefore the Check Point module binary image was performed and validation certificates obtained for Field Replaceable Unit (FRU) upgrades to internal network interface cards, hard drives, FLASH memory, and other components (e.g., fans and power supplies replaced with Check Point VPN-1 NGX (R60) [HFA-03] The cryptographic modules implement the same version of the module to service or install these internal components. 2.2 Cryptographic Module The Nokia VPN Appliances were tested as part of the complete Nokia VPN Appliance...
Security Guide
Page 7
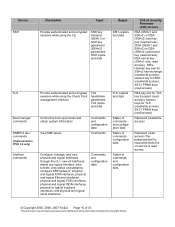
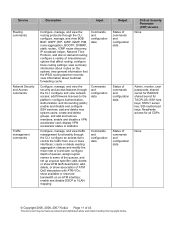
... Mbps fiber Ethernet, V.35, or X.21 protocol options) PCMCIA Slots (secured with Tamper Seals) Power Switch Reset Switch Status LEDs Power Fault Ethernet Port status (green indicates connection, yellow blinking indicates data being transmitted) IP260/IP265 4 1 1 N/A 2 (enabled) 1 1 1 1 1 IP1220/IP1260 4 1 1 3 2 (disabled) 1 1 1 built in, 1 per optional PMC NIC card) 1 1 built in, additional depending on number of I/O option cards installed Descriptions of the status LEDs © Copyright 2005, 2006, 2007 Nokia Page 7 of 43 This document...
... Mbps fiber Ethernet, V.35, or X.21 protocol options) PCMCIA Slots (secured with Tamper Seals) Power Switch Reset Switch Status LEDs Power Fault Ethernet Port status (green indicates connection, yellow blinking indicates data being transmitted) IP260/IP265 4 1 1 N/A 2 (enabled) 1 1 1 1 1 IP1220/IP1260 4 1 1 3 2 (disabled) 1 1 1 built in, 1 per optional PMC NIC card) 1 1 built in, additional depending on number of I/O option cards installed Descriptions of the status LEDs © Copyright 2005, 2006, 2007 Nokia Page 7 of 43 This document...
Security Guide
Page 8
... and contents. 2.4 Roles and Services The modules support role-based authentication. Module Physical Port Network ports Network ports Network ports, console port, power switch, reset switch Network ports, console port, LEDs Power plug, Power switch FIPS 140-2 Logical Interface Data input interface Data output interface Control input interface Status output interface Power interface Table 2 - Three management interfaces can be used for power and reset through the LEDs and the status data that use the CLI to configure and monitor IPSO systems. This can configure, manage, and...
... and contents. 2.4 Roles and Services The modules support role-based authentication. Module Physical Port Network ports Network ports Network ports, console port, power switch, reset switch Network ports, console port, LEDs Power plug, Power switch FIPS 140-2 Logical Interface Data input interface Data output interface Control input interface Status output interface Power interface Table 2 - Three management interfaces can be used for power and reset through the LEDs and the status data that use the CLI to configure and monitor IPSO systems. This can configure, manage, and...
Security Guide
Page 9
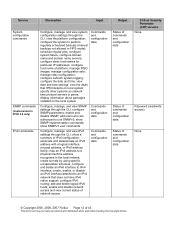
... Provide network connectivity and set a password for the admin account Commands and configuration data(via local console) Status of commands and configuration data Critical Security Parameter (CSP) Access Admin password (read/write access) © Copyright 2005, 2006, 2007 Nokia Page 9 of 43 This document may be freely reproduced and distributed whole and intact including this interface after the initial configuration of the services available to Use Check Point Management Tools Descriptions of the Check Point module through the CLI. SNMP support...
... Provide network connectivity and set a password for the admin account Commands and configuration data(via local console) Status of commands and configuration data Critical Security Parameter (CSP) Access Admin password (read/write access) © Copyright 2005, 2006, 2007 Nokia Page 9 of 43 This document may be freely reproduced and distributed whole and intact including this interface after the initial configuration of the services available to Use Check Point Management Tools Descriptions of the Check Point module through the CLI. SNMP support...
Security Guide
Page 10
... commands and configuration data Critical Security Parameter (CSP) Access RSA (SSHv1 and SSHv2) or DSA (SSHv2) host key pair (read access) ;RSA (SSHv1 and SSHv2) or DSA (SSHv2) authorized key (read access); view tunnels; X9.31 PRNG keys (read access) RSA key pair for SSHv2 key exchange (read access); Service SSH TLS Boot manager commands SNMPv3 Get commands (Implemented in IPSO 3.9 only) Interface commands Description Input Provide authenticated and encrypted sessions while using the CLI...
... commands and configuration data Critical Security Parameter (CSP) Access RSA (SSHv1 and SSHv2) or DSA (SSHv2) host key pair (read access) ;RSA (SSHv1 and SSHv2) or DSA (SSHv2) authorized key (read access); view tunnels; X9.31 PRNG keys (read access) RSA key pair for SSHv2 key exchange (read access); Service SSH TLS Boot manager commands SNMPv3 Get commands (Implemented in IPSO 3.9 only) Interface commands Description Input Provide authenticated and encrypted sessions while using the CLI...
Security Guide
Page 11
... routing; enable and disable and configure SSH services; create and delete groups, and add and remove members; show available or reserved bandwidth on demand routing; Service Routing commands Network Security and Access commands Traffic management commands Description Input Configure, manage, and view the routing protocols through the CLI: configure, manage, and view BGB BGP, OSPF, RIP, IGRP, IGMP, PIM, route aggregation, BOOTP, DVMRP, static routes,, ICMP router discovery, IP broadcast helper, Network Time Protocol, and dial on an ATM interface; add and delete new system users...
... routing; enable and disable and configure SSH services; create and delete groups, and add and remove members; show available or reserved bandwidth on demand routing; Service Routing commands Network Security and Access commands Traffic management commands Description Input Configure, manage, and view the routing protocols through the CLI: configure, manage, and view BGB BGP, OSPF, RIP, IGRP, IGMP, PIM, route aggregation, BOOTP, DVMRP, static routes,, ICMP router discovery, IP broadcast helper, Network Time Protocol, and dial on an ATM interface; add and delete new system users...
Security Guide
Page 12
... backups not allowed in FIPS mode); create tunnels by using specific encapsulation schemes; configure IPv6 routing; configure static host names for particular IP addresses; configure the date and time; enable and disable SNMP; show a summary of IPv6 configuration; show SNMPv3 user commands Commands and configuration data Configure, manage, and view IPv6 settings through the CLI: show SNMP implementation commands; enable and disable network access and view current status of network access Commands and configuration data Output Status of commands and configuration data Status of...
... backups not allowed in FIPS mode); create tunnels by using specific encapsulation schemes; configure IPv6 routing; configure static host names for particular IP addresses; configure the date and time; enable and disable SNMP; show a summary of IPv6 configuration; show SNMPv3 user commands Commands and configuration data Configure, manage, and view IPv6 settings through the CLI: show SNMP implementation commands; enable and disable network access and view current status of network access Commands and configuration data Output Status of commands and configuration data Status of...
Security Guide
Page 13
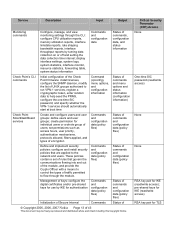
... types of UNIX groups authorized to run VPN-1 services, register a cryptographic token, enter random data to the network and users. Critical Security Parameter (CSP) Access None One-time SIC password (read/write access) None None RSA key pair for IKE (read /write access) RSA key pair for TLS display interface settings, system logs, system statistics, interface monitor, resource statistics, forwarding table, system status information Commands and configuration data Status of commands, configuration data, and status information Check Point's CLI commands Initial configuration...
... types of UNIX groups authorized to run VPN-1 services, register a cryptographic token, enter random data to the network and users. Critical Security Parameter (CSP) Access None One-time SIC password (read/write access) None None RSA key pair for IKE (read /write access) RSA key pair for TLS display interface settings, system logs, system statistics, interface monitor, resource statistics, forwarding table, system status information Commands and configuration data Status of commands, configuration data, and status information Check Point's CLI commands Initial configuration...
Security Guide
Page 14
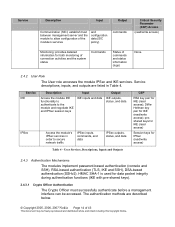
..., status, and data IPSec Access the module's IPSec services in Table 4. User Services, Descriptions, Inputs and Outputs 2.4.3 Authentication Mechanisms The modules implement password-based authentication (console and SSH), RSA-based authentication (TLS, IKE and SSH), DSA-based authentication (SSHv2). DiffieHellman key pair for IKE (read access); The authentication methods are listed in order to allow configuration of the module's services and configuration data (SIC policy) commands Critical Security Parameter (CSP) Access (read/write access) Monitoring: provides detailed...
..., status, and data IPSec Access the module's IPSec services in Table 4. User Services, Descriptions, Inputs and Outputs 2.4.3 Authentication Mechanisms The modules implement password-based authentication (console and SSH), RSA-based authentication (TLS, IKE and SSH), DSA-based authentication (SSHv2). DiffieHellman key pair for IKE (read access); The authentication methods are listed in order to allow configuration of the module's services and configuration data (SIC policy) commands Critical Security Parameter (CSP) Access (read/write access) Monitoring: provides detailed...
Security Guide
Page 17
... module through customized interfaces that provide only specific command options. 2.8 Cryptographic Key Management Cryptographic algorithms are installed by using RSA key wrapping. If the optional accelerator card is installed, the hardwired chip is achieved by accelerating DES, AES, Triple-DES, and Diffie-Hellman modular exponentiation processing implemented by using ISAKMP according to the end-user. SHA-1 for data integrity. The embedded Check Point application supports IPSec/ESP for data...
... module through customized interfaces that provide only specific command options. 2.8 Cryptographic Key Management Cryptographic algorithms are installed by using RSA key wrapping. If the optional accelerator card is installed, the hardwired chip is achieved by accelerating DES, AES, Triple-DES, and Diffie-Hellman modular exponentiation processing implemented by using ISAKMP according to the end-user. SHA-1 for data integrity. The embedded Check Point application supports IPSec/ESP for data...
Security Guide
Page 26
... security requirements. Refer to provide tamper evidence for a list of operation. 3 SECURE OPERATION (APPROVED MODE) The Nokia VPN Appliances meet Level 2 requirements for evidence of the module at all times until the initial setup is complete. The Crypto Officer must install one or more tamper-evident seals (also called "FIPS Tape") provided in a FIPS-approved mode of the module hardware versions and their respective chassis type. The...
... security requirements. Refer to provide tamper evidence for a list of operation. 3 SECURE OPERATION (APPROVED MODE) The Nokia VPN Appliances meet Level 2 requirements for evidence of the module at all times until the initial setup is complete. The Crypto Officer must install one or more tamper-evident seals (also called "FIPS Tape") provided in a FIPS-approved mode of the module hardware versions and their respective chassis type. The...
Security Guide
Page 28
... Appliance Installation Guide. 3.1.2 Installing, Upgrading or Downgrading the Module Firmware New modules come preinstalled with Hotfix HFA-03. © Copyright 2005, 2006, 2007 Nokia Page 28 of the cable to the module hard disk. Tamper Seal Location(s) for verification. 7. The current FIPS 140-2 conformant configuration consists of IPSO 4.1 and Check Point VPN-1 version NGX (R60) with the Nokia IPSO operating system and a version of the appliance. 2. Figure 4 - Connect the supplied console cable to the local console port...
... Appliance Installation Guide. 3.1.2 Installing, Upgrading or Downgrading the Module Firmware New modules come preinstalled with Hotfix HFA-03. © Copyright 2005, 2006, 2007 Nokia Page 28 of the cable to the module hard disk. Tamper Seal Location(s) for verification. 7. The current FIPS 140-2 conformant configuration consists of IPSO 4.1 and Check Point VPN-1 version NGX (R60) with the Nokia IPSO operating system and a version of the appliance. 2. Figure 4 - Connect the supplied console cable to the local console port...
Security Guide
Page 29
... or User Authority Server 4. Now access the device console, exit and login again if you the list of links) 2. Delete Check Point VPN-1 version R55p: 1. Install Check Point NGX (R60) from the /opt/packages directory on IPSO 3.9. Otherwise the procedures described in one of 43 This document may be followed: 3.1.2.1 SCENARIO 1 - Access the device via Voyager, the web-based management interface, Click on the 'Manage Installed Packages' link on 'Apply' to make the changes permanent 5. Click on the 'Config...
... or User Authority Server 4. Now access the device console, exit and login again if you the list of links) 2. Delete Check Point VPN-1 version R55p: 1. Install Check Point NGX (R60) from the /opt/packages directory on IPSO 3.9. Otherwise the procedures described in one of 43 This document may be followed: 3.1.2.1 SCENARIO 1 - Access the device via Voyager, the web-based management interface, Click on the 'Manage Installed Packages' link on 'Apply' to make the changes permanent 5. Click on the 'Config...
Security Guide
Page 32
... enabled, the Crypto Officer's authorized SSH public key must set ssh server enable 1 2. Using the CLI through the console port, enter the following command: set the mode of 43 This document may be managed from the console port to FIPS mode. For the list of disabled access and feature mechanisms, see Appendix A on restart command. set the mode of operation to enter the set ssh server protocol 2,1 b. FIPS mode can log in FIPS mode 2. To ensure that the server will reboot the device...
... enabled, the Crypto Officer's authorized SSH public key must set ssh server enable 1 2. Using the CLI through the console port, enter the following command: set the mode of 43 This document may be managed from the console port to FIPS mode. For the list of disabled access and feature mechanisms, see Appendix A on restart command. set the mode of operation to enter the set ssh server protocol 2,1 b. FIPS mode can log in FIPS mode 2. To ensure that the server will reboot the device...
Security Guide
Page 33
... address port server-key-bits 1024 5. Screen shots from the Check Point © Copyright 2005, 2006, 2007 Nokia Page 33 of the module function. The module can now be changed. 3.1.6 Management and Monitoring After the initial setup, the Crypto Officer can manage the Check Point module with SNMPv3 (when using IPSO 3.9; For optional configuration settings, see the CLI Reference Guide for encryption and configure the SSH protocol by bold letters and numbers must not be managed remotely...
... address port server-key-bits 1024 5. Screen shots from the Check Point © Copyright 2005, 2006, 2007 Nokia Page 33 of the module function. The module can now be changed. 3.1.6 Management and Monitoring After the initial setup, the Crypto Officer can manage the Check Point module with SNMPv3 (when using IPSO 3.9; For optional configuration settings, see the CLI Reference Guide for encryption and configure the SSH protocol by bold letters and numbers must not be managed remotely...
Security Guide
Page 34
... VPN functionality must be configured to use only the following pages denote sample screen shots of the various Check Point configuration screens. IPSec and IKE can use only FIPS-approved algorithms. The following FIPS-approved algorithms: Data encryption • Triple DES • AES Data packet integrity • HMAC with the SSH-secured management session. • The AUX port must not be enabled. • The module logs...
... VPN functionality must be configured to use only the following pages denote sample screen shots of the various Check Point configuration screens. IPSec and IKE can use only FIPS-approved algorithms. The following FIPS-approved algorithms: Data encryption • Triple DES • AES Data packet integrity • HMAC with the SSH-secured management session. • The AUX port must not be enabled. • The module logs...
Security Guide
Page 43
... FCC FIPS FP IGRP IKE IPSec KAT LED MAC NIST OSPF PRNG RAM RIP RSA SA SHA SIC SNMP SSH SSL TLS VPN Authentication Header Application Intelligence American National Standards Institute Border Gateway Protocol Cipher Block Chaining Command-Line Interface Cryptographic Module Validation Program Cyclical Redundancy Check Critical Security Parameter Digital Signature Standard Distance Vector Multicast Routing Protocol Error Detection Code Electromagnetic Compatibility Electromagnetic Interference Encapsulating...
... FCC FIPS FP IGRP IKE IPSec KAT LED MAC NIST OSPF PRNG RAM RIP RSA SA SHA SIC SNMP SSH SSL TLS VPN Authentication Header Application Intelligence American National Standards Institute Border Gateway Protocol Cipher Block Chaining Command-Line Interface Cryptographic Module Validation Program Cyclical Redundancy Check Critical Security Parameter Digital Signature Standard Distance Vector Multicast Routing Protocol Error Detection Code Electromagnetic Compatibility Electromagnetic Interference Encapsulating...