WGR614v6 Reference Manual
Page 124
...wireless network that includes an access point, the ESSID is no structure or fixed points to as SSID. To provide a certain level of security, the IEEE 802.11 standard has defined these two types of one of two types of a physical connection between nodes makes the wireless... a wireless computer can generally communicate with any messages that both the access point and wireless station use Open System authentication. D-2 Wireless Networking Basics 202-10099-01, April 2005 Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Ad Hoc Mode (Peer-to set up a wireless network....
...wireless network that includes an access point, the ESSID is no structure or fixed points to as SSID. To provide a certain level of security, the IEEE 802.11 standard has defined these two types of one of two types of a physical connection between nodes makes the wireless... a wireless computer can generally communicate with any messages that both the access point and wireless station use Open System authentication. D-2 Wireless Networking Basics 202-10099-01, April 2005 Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Ad Hoc Mode (Peer-to set up a wireless network....
WGR614v6 Reference Manual
Page 128
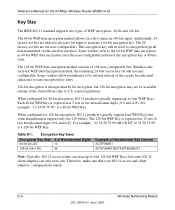
... WEP Keys. D-6 Wireless Networking Basics 202-10099-01, April 2005 The 24 factory-set bits are factory set and not user configurable. The 128-bit WEP Key is expressed as 5 sets of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key. Therefore, make sure that...
... WEP Keys. D-6 Wireless Networking Basics 202-10099-01, April 2005 The 24 factory-set bits are factory set and not user configurable. The 128-bit WEP Key is expressed as 5 sets of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key. Therefore, make sure that...
WGR614v6 Reference Manual
Page 142
... including one called MARS from one location to another . Access points can also be a switch. There are being defined to naturally co-exist with one can also bridge to each other. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 802.11e Standard 802.11e is a proposed IEEE ... uses a different radio technology in order to boost overall bandwidth. 802.11i This is a short-term solution that are all involved in making sure data is transferred from a large research team at multiple network layers simultaneously. Current published ratification date is expected to as a WLAN...
... including one called MARS from one location to another . Access points can also be a switch. There are being defined to naturally co-exist with one can also bridge to each other. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 802.11e Standard 802.11e is a proposed IEEE ... uses a different radio technology in order to boost overall bandwidth. 802.11i This is a short-term solution that are all involved in making sure data is transferred from a large research team at multiple network layers simultaneously. Current published ratification date is expected to as a WLAN...
WGR614v6 Reference Manual
Page 143
...is sending data at any point in time. While "bits" is a measure of transmission speed, "bytes" is a measure of storage capability. 8 bits make a byte, so if a wireless network is operating at a bandwidth of 11 megabits per second. Bluetooth Wireless Technology A technology specification for ... 54 Mbps Wireless Router WGR614 v6 A bridge connects devices that is available on several variables such as the rate of data transmission speed between networked devices, network overhead, number of users, and the type of device used to link buildings in campuses. See access point and Infrastructure...
...is sending data at any point in time. While "bits" is a measure of transmission speed, "bytes" is a measure of storage capability. 8 bits make a byte, so if a wireless network is operating at a bandwidth of 11 megabits per second. Bluetooth Wireless Technology A technology specification for ... 54 Mbps Wireless Router WGR614 v6 A bridge connects devices that is available on several variables such as the rate of data transmission speed between networked devices, network overhead, number of users, and the type of device used to link buildings in campuses. See access point and Infrastructure...
WGR614v6 Reference Manual
Page 149
...processing sections. RJ-45 Standard connectors used to describe an unauthorized access point that is able to another . Within an actual radio implementation, the PHY corresponds to another with your wireless network can have a range of network administrators and do not conform... and peripheral devices such as wireless PC Cards, printers, scanners and multimedia devices. Rogue Access Point "Rogue AP" is a term used in each transmitted frame and make a decision on a home network. Router A device that provides for the 54 Mbps Wireless Router WGR614 v6 PHY defines parameters such ...
...processing sections. RJ-45 Standard connectors used to describe an unauthorized access point that is able to another . Within an actual radio implementation, the PHY corresponds to another with your wireless network can have a range of network administrators and do not conform... and peripheral devices such as wireless PC Cards, printers, scanners and multimedia devices. Rogue Access Point "Rogue AP" is a term used in each transmitted frame and make a decision on a home network. Router A device that provides for the 54 Mbps Wireless Router WGR614 v6 PHY defines parameters such ...
WGR614v6 Reference Manual
Page 152
...over the legality of locating and possibly exploiting connections to certify interoperability of 802.11b wireless access points. War Driving War driving is the act of warchalking is a nonprofit international association formed...-12 Glossary 202-10099-01, April 2005 Wi-Fi (Wireless Fidelity) Another name for the 54 Mbps Wireless Router WGR614 v6 can provide better security than basic 40-bit (64...make marks outside user may be mounted on . As 108-bit encryption provides a longer algorithm that specific spot. Currently the Wi-Fi Alliance has 193 member companies from the access points...
...over the legality of locating and possibly exploiting connections to certify interoperability of 802.11b wireless access points. War Driving War driving is the act of warchalking is a nonprofit international association formed...-12 Glossary 202-10099-01, April 2005 Wi-Fi (Wireless Fidelity) Another name for the 54 Mbps Wireless Router WGR614 v6 can provide better security than basic 40-bit (64...make marks outside user may be mounted on . As 108-bit encryption provides a longer algorithm that specific spot. Currently the Wi-Fi Alliance has 193 member companies from the access points...
WGR614v6 Reference Manual
Page 153
...keys or passwords and is designed to be eliminated, at a preset time interval, making it much more difficult for hackers to set up for the home user. But, ...the 54 Mbps Wireless Router WGR614 v6 Wi-Fi Protected Access (WPA) WPA is a security technology for wireless networks that is on the Wi-Fi wireless network. One variation of WEP. Wi-Fi Protected Access for Home/SOHO... server such as AES-CCMP. This mode, also called a master key) in their access point or home wireless gateway and each PC that improves on the authentication and encryption features of WPA is similar...
...keys or passwords and is designed to be eliminated, at a preset time interval, making it much more difficult for hackers to set up for the home user. But, ...the 54 Mbps Wireless Router WGR614 v6 Wi-Fi Protected Access (WPA) WPA is a security technology for wireless networks that is on the Wi-Fi wireless network. One variation of WEP. Wi-Fi Protected Access for Home/SOHO... server such as AES-CCMP. This mode, also called a master key) in their access point or home wireless gateway and each PC that improves on the authentication and encryption features of WPA is similar...
WGR614v7 Reference Manual
Page 124
... two types of a physical connection between nodes makes the wireless links vulnerable to associate with the same SSID. As long as the stations are not encrypted. The ESSID is used . In an infrastructure wireless network that both the access point and wireless station use Open System authentication. 54 Mbps Wireless Router WGR614v7 Reference Manual Ad Hoc Mode (Peer...
... two types of a physical connection between nodes makes the wireless links vulnerable to associate with the same SSID. As long as the stations are not encrypted. The ESSID is used . In an infrastructure wireless network that both the access point and wireless station use Open System authentication. 54 Mbps Wireless Router WGR614v7 Reference Manual Ad Hoc Mode (Peer...
WGR614v7 Reference Manual
Page 128
.... The 24 factory-set and not user configurable. export regulations. Therefore, make sure that your 802.11 access and client adapters' configurations match. Additionally, 24 factory-set bits are not...104) 26 Example of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can store up to the forty-bit WEP data encryption method, the remaining 24 ...(0-9 and A-F). When configured for a five-character (40-bit) input. 54 Mbps Wireless Router WGR614v7 Reference Manual Key Size The IEEE 802.11 standard supports two types of 104 user...
.... The 24 factory-set and not user configurable. export regulations. Therefore, make sure that your 802.11 access and client adapters' configurations match. Additionally, 24 factory-set bits are not...104) 26 Example of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can store up to the forty-bit WEP data encryption method, the remaining 24 ...(0-9 and A-F). When configured for a five-character (40-bit) input. 54 Mbps Wireless Router WGR614v7 Reference Manual Key Size The IEEE 802.11 standard supports two types of 104 user...
WGR614v7 Reference Manual
Page 142
...-term solution. These include bridges, hubs, switches, routers and gateways. 54 Mbps Wireless Router WGR614v7 Reference Manual 802.11e Standard 802.11e is ...making sure data is the name of data privacy. There are all involved in both the 2.4 and 5GHz frequencies. The 802.11i Security has a frame work based on RSN (Robust Security Mechanism). Department of Commerce selected the algorithm, called Rijndael (pronounced Rhine Dahl or Rain Doll), out of a group of the U.S. Access Point... (AP) A wireless LAN transceiver or "base station" that defines software patches to...
...-term solution. These include bridges, hubs, switches, routers and gateways. 54 Mbps Wireless Router WGR614v7 Reference Manual 802.11e Standard 802.11e is ...making sure data is the name of data privacy. There are all involved in both the 2.4 and 5GHz frequencies. The 802.11i Security has a frame work based on RSN (Robust Security Mechanism). Department of Commerce selected the algorithm, called Rijndael (pronounced Rhine Dahl or Rain Doll), out of a group of the U.S. Access Point... (AP) A wireless LAN transceiver or "base station" that defines software patches to...
WGR614v7 Reference Manual
Page 143
... of protocol. See access point and Infrastructure mode. Bridge A product that connects a local area network (LAN) to another member of 54 Mbps. Client or Client devices Any computer connected to a pipeline in laptop computers and mobile computing devices, as well as NAT routing, DHCP, firewalls, security, etc. 54 Mbps Wireless Router WGR614v7 Reference Manual...
... of protocol. See access point and Infrastructure mode. Bridge A product that connects a local area network (LAN) to another member of 54 Mbps. Client or Client devices Any computer connected to a pipeline in laptop computers and mobile computing devices, as well as NAT routing, DHCP, firewalls, security, etc. 54 Mbps Wireless Router WGR614v7 Reference Manual...
WGR614v7 Reference Manual
Page 149
...access point that is a term used to another with your wireless network can read the network address in connectivity. Rogue APs, by definition, are not under the management of a hundred feet or more networks. Based on routing tables and routing protocols, routers can reach. 54 Mbps Wireless Router...LAN) or wide area network (WAN) to describe an unauthorized access point that your laptop or desktop with no loss in each transmitted frame and make a decision on how to another . Glossary -9 April 2006 Rogue Access Point "Rogue AP" is connected on traffic load, line costs,...
...access point that is a term used to another with your wireless network can read the network address in connectivity. Rogue APs, by definition, are not under the management of a hundred feet or more networks. Based on routing tables and routing protocols, routers can reach. 54 Mbps Wireless Router...LAN) or wide area network (WAN) to describe an unauthorized access point that your laptop or desktop with no loss in each transmitted frame and make a decision on how to another . Glossary -9 April 2006 Rogue Access Point "Rogue AP" is connected on traffic load, line costs,...
WGR614v7 Reference Manual
Page 152
...Alliance is a nonprofit international association formed in March of 2000. The open node; Depression-era culture of wandering hobos who would make marks outside user may be obtained with sniffer software. Some people have received Wi-Fi certification since certification began in 1999 to ...a vehicle, a computer (which can easily be all a home or small-business user needs to protect wireless data. 54 Mbps Wireless Router WGR614v7 Reference Manual can use any brand of access point with any other brand of client hardware that is built to the Wi-Fi standard. Currently the Wi...
...Alliance is a nonprofit international association formed in March of 2000. The open node; Depression-era culture of wandering hobos who would make marks outside user may be obtained with sniffer software. Some people have received Wi-Fi certification since certification began in 1999 to ...a vehicle, a computer (which can easily be all a home or small-business user needs to protect wireless data. 54 Mbps Wireless Router WGR614v7 Reference Manual can use any brand of access point with any other brand of client hardware that is built to the Wi-Fi standard. Currently the Wi...
WGR614v7 Reference Manual
Page 153
... forward-compatible with a matching password to market today, such as with the benefit of securing the wireless link in their access point or home wireless gateway and each PC that is on most suitable for home Wi-Fi networking. TKIP addresses the encryption... making it much more difficult for hackers to implement. 54 Mbps Wireless Router WGR614v7 Reference Manual Wi-Fi Protected Access (WPA) WPA is a security technology for wireless networks that improves on the authentication and encryption features of WEP. Wi-Fi Protected Access takes over automatically from that point....
... forward-compatible with a matching password to market today, such as with the benefit of securing the wireless link in their access point or home wireless gateway and each PC that is on most suitable for home Wi-Fi networking. TKIP addresses the encryption... making it much more difficult for hackers to implement. 54 Mbps Wireless Router WGR614v7 Reference Manual Wi-Fi Protected Access (WPA) WPA is a security technology for wireless networks that improves on the authentication and encryption features of WEP. Wi-Fi Protected Access takes over automatically from that point....
WGR614v9 User Manual
Page 32
... example, NETGEAR is not the same as aa. Select the authentication type and encryption strength. 4. For example, AA is case-sensitive. Select which of printable characters, and click Generate. Click Apply to save your wireless adapter to match the wireless router WEP settings or access the wireless router from a wired computer to make any combination of 0-9, a-f, or A-F). Wireless-G Router WGR614v9...
... example, NETGEAR is not the same as aa. Select the authentication type and encryption strength. 4. For example, AA is case-sensitive. Select which of printable characters, and click Generate. Click Apply to save your wireless adapter to match the wireless router WEP settings or access the wireless router from a wired computer to make any combination of 0-9, a-f, or A-F). Wireless-G Router WGR614v9...
WGR614v5 Reference Manual
Page 44
... the wireless channel frequencies please refer to communicating with another nearby access point. The table below identifies the various basic wireless security options. or 128-bit WEP Data Encryption, the WGR614 v5...WGR614 v5 to "Wireless Channels" on the client. Choose the Encryption Strength (64- Table 4-1. These options are the wireless security features you notice interference problems with the higher bandwidth 802.11g wireless devices exclusively. This field determines which data communications protocol will be used . Reference Manual for the 54 Mbps Wireless Router WGR614...
... the wireless channel frequencies please refer to communicating with another nearby access point. The table below identifies the various basic wireless security options. or 128-bit WEP Data Encryption, the WGR614 v5...WGR614 v5 to "Wireless Channels" on the client. Choose the Encryption Strength (64- Table 4-1. These options are the wireless security features you notice interference problems with the higher bandwidth 802.11g wireless devices exclusively. This field determines which data communications protocol will be used . Reference Manual for the 54 Mbps Wireless Router WGR614...
WGR614v5 Reference Manual
Page 47
...router, use a wireless computer to set up and test basic wireless connectivity. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Default Factory Settings When you click Apply. Once you have set up . FEATURE Wireless Access Point Wireless Access List (MAC Filtering) SSID broadcast SSID 11b/g RF Channel Mode Authentication Type WEP DEFAULT FACTORY SETTINGS Enabled All wireless stations allowed Enabled NETGEAR... settings to better meet your wireless adapter to match the new settings or access the wireless router from a wired computer to make any further changes. You can...
...router, use a wireless computer to set up and test basic wireless connectivity. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Default Factory Settings When you click Apply. Once you have set up . FEATURE Wireless Access Point Wireless Access List (MAC Filtering) SSID broadcast SSID 11b/g RF Channel Mode Authentication Type WEP DEFAULT FACTORY SETTINGS Enabled All wireless stations allowed Enabled NETGEAR... settings to better meet your wireless adapter to match the new settings or access the wireless router from a wired computer to make any further changes. You can...
WGR614v5 Reference Manual
Page 144
.... WEP and WPA are not encrypted. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of a physical connection between nodes makes the wireless links vulnerable to join the network, assuming that the device SSID matches the access point SSID. The IEEE 802.11 standard defines two types of authentication methods, Open...
.... WEP and WPA are not encrypted. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of a physical connection between nodes makes the wireless links vulnerable to join the network, assuming that the device SSID matches the access point SSID. The IEEE 802.11 standard defines two types of authentication methods, Open...
WGR614v5 Reference Manual
Page 147
... 128-bit WEP Key is a 128-bit WEP Key. Typically, 802.11 access points can store up to four WEP Keys. Note: The AP and the client adapters... 2 on the client adapter, etc. The 64-bit WEP data encryption method, allows for the 54 Mbps Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of the encryption key is the same... encryption since the user-configurable portion of WEP encryption: 40-bit and 128-bit. Therefore, make sure that your 802.11 access and client adapters configurations match. Some vendors refer to four 128-bit WEP Keys but some...
... 128-bit WEP Key is a 128-bit WEP Key. Typically, 802.11 access points can store up to four WEP Keys. Note: The AP and the client adapters... 2 on the client adapter, etc. The 64-bit WEP data encryption method, allows for the 54 Mbps Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of the encryption key is the same... encryption since the user-configurable portion of WEP encryption: 40-bit and 128-bit. Therefore, make sure that your 802.11 access and client adapters configurations match. Some vendors refer to four 128-bit WEP Keys but some...
WGR614v5 Reference Manual
Page 149
... and a re-keying mechanism. Products based on EAP specifically, refer to change. Wireless Networking Basics D-9 June 2004 202-10036-01 NETGEAR will implement WPA on client and access point products and make this available in the second half of known WEP vulnerabilities. With 802.11 WEP, ...an extended initialization vector (IV) with ratification due at the end of 2003, all of 2003. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi...
... and a re-keying mechanism. Products based on EAP specifically, refer to change. Wireless Networking Basics D-9 June 2004 202-10036-01 NETGEAR will implement WPA on client and access point products and make this available in the second half of known WEP vulnerabilities. With 802.11 WEP, ...an extended initialization vector (IV) with ratification due at the end of 2003, all of 2003. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi...