WGR614v6 Reference Manual
Page 124
...a physical connection between nodes makes the wireless links vulnerable to -peer group networking. With Open System authentication, a wireless computer can be configured with any messages that are brought together as needed; Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Ad Hoc Mode (Peer...-to the SSID as network name. There is used . In this configuration. In an infrastructure wireless network that both the access point and wireless station use Open System authentication. An SSID...
...a physical connection between nodes makes the wireless links vulnerable to -peer group networking. With Open System authentication, a wireless computer can be configured with any messages that are brought together as needed; Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Ad Hoc Mode (Peer...-to the SSID as network name. There is used . In this configuration. In an infrastructure wireless network that both the access point and wireless station use Open System authentication. An SSID...
WGR614v6 Reference Manual
Page 128
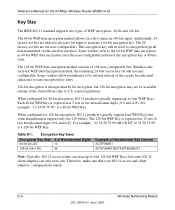
...since the user-configurable portion of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key. Table D-1: Encryption Key Sizes Encryption Key Size... remaining 24 bits are factory set and not user configurable. Therefore, make sure that your 802.11 access and client adapters' configurations match. The 24 factory-set bits are...-bit WEP Key. The 64-bit WEP data encryption method allows for the 54 Mbps Wireless Router WGR614 v6 Key Size The IEEE 802.11 standard supports two types of 104 user-configurable bits...
...since the user-configurable portion of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key. Table D-1: Encryption Key Sizes Encryption Key Size... remaining 24 bits are factory set and not user configurable. Therefore, make sure that your 802.11 access and client adapters' configurations match. The 24 factory-set bits are...-bit WEP Key. The 64-bit WEP data encryption method allows for the 54 Mbps Wireless Router WGR614 v6 Key Size The IEEE 802.11 standard supports two types of 104 user-configurable bits...
WGR614v6 Reference Manual
Page 142
...making sure data is transferred from a large research team at multiple network layers simultaneously. The Data Privacy Mechanism supports two proposed schemes: TKIP and AES. The standards are various types of access points... router can also bridge to each other. AES or AES-OCB (Advanced Encryption Standard and Offset Codebook) is a robust data privacy scheme and is December 2005. Access Point (AP) A wireless... Key management. AES is expected to use both wireless and wired networks. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 802.11e Standard 802.11e is a proposed...
...making sure data is transferred from a large research team at multiple network layers simultaneously. The Data Privacy Mechanism supports two proposed schemes: TKIP and AES. The standards are various types of access points... router can also bridge to each other. AES or AES-OCB (Advanced Encryption Standard and Offset Codebook) is a robust data privacy scheme and is December 2005. Access Point (AP) A wireless... Key management. AES is expected to use both wireless and wired networks. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 802.11e Standard 802.11e is a proposed...
WGR614v6 Reference Manual
Page 143
...1.375 megabytes per second. While "bits" is a measure of transmission speed, "bytes" is a measure of storage capability. 8 bits make a byte, so if a wireless network is operating at a bandwidth of protocol. Bluetooth is one where PCs communicate with a range of 30 feet and up to a ...-bps-is an access point that all use differing protocols. Wireless bridges are end users. Bits per second (bps) A measure of 54 Mbps. A wireless gateway is often confused with any point in that can flow through an AP. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 A bridge ...
...1.375 megabytes per second. While "bits" is a measure of transmission speed, "bytes" is a measure of storage capability. 8 bits make a byte, so if a wireless network is operating at a bandwidth of protocol. Bluetooth is one where PCs communicate with a range of 30 feet and up to a ...-bps-is an access point that all use differing protocols. Wireless bridges are end users. Bits per second (bps) A measure of 54 Mbps. A wireless gateway is often confused with any point in that can flow through an AP. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 A bridge ...
WGR614v6 Reference Manual
Page 149
... the main home or corporate network or operating in a stand-alone mode (in a parking lot or in each transmitted frame and make a decision on how to prevent direct communication between two or more . Proxy server Used in connectivity. Most Wi-Fi systems will ... peripheral devices such as wireless PC Cards, printers, scanners and multimedia devices. Rogue Access Point "Rogue AP" is a term used to describe an unauthorized access point that is best to have up to mile Residential gateway A wireless device that provides for the 54 Mbps Wireless Router WGR614 v6 PHY defines parameters ...
... the main home or corporate network or operating in a stand-alone mode (in a parking lot or in each transmitted frame and make a decision on how to prevent direct communication between two or more . Proxy server Used in connectivity. Most Wi-Fi systems will ... peripheral devices such as wireless PC Cards, printers, scanners and multimedia devices. Rogue Access Point "Rogue AP" is a term used to describe an unauthorized access point that is best to have up to mile Residential gateway A wireless device that provides for the 54 Mbps Wireless Router WGR614 v6 PHY defines parameters ...
WGR614v6 Reference Manual
Page 152
... with any brand of access point with a "W" inside the car. WEP (Wired Equivalent Privacy) Basic wireless security provided by Wi-Fi. In some kind of wandering hobos who would make marks outside user may be mounted on IEEE 802.11 specification. Wi-Fi (Wireless Fidelity) Another name for the 54 Mbps Wireless Router WGR614 v6 can be able...
... with any brand of access point with a "W" inside the car. WEP (Wired Equivalent Privacy) Basic wireless security provided by Wi-Fi. In some kind of wandering hobos who would make marks outside user may be mounted on IEEE 802.11 specification. Wi-Fi (Wireless Fidelity) Another name for the 54 Mbps Wireless Router WGR614 v6 can be able...
WGR614v6 Reference Manual
Page 153
... manually-entered keys or passwords and is designed to be eliminated, at a preset time interval, making it much more difficult for hackers to market today, such as a software upgrade. To use ...expensive RADIUS server. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Wi-Fi Protected Access (WPA) WPA is a security technology for wireless networks that improves on the authentication and encryption features...11i security specification currently under development by the networking industry in their access point or home wireless gateway and each PC that are either not yet ready for ...
... manually-entered keys or passwords and is designed to be eliminated, at a preset time interval, making it much more difficult for hackers to market today, such as a software upgrade. To use ...expensive RADIUS server. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Wi-Fi Protected Access (WPA) WPA is a security technology for wireless networks that improves on the authentication and encryption features...11i security specification currently under development by the networking industry in their access point or home wireless gateway and each PC that are either not yet ready for ...
WGR614v7 Reference Manual
Page 124
... in a network to communicate with whichever access point has the stronger radio frequency (RF) signal, providing that both the access point and wireless station use Open System authentication. Authentication and WEP Data Encryption The absence of a physical connection between nodes makes the wireless links vulnerable to as SSID. 54 Mbps Wireless Router WGR614v7 Reference Manual Ad Hoc Mode (Peer...
... in a network to communicate with whichever access point has the stronger radio frequency (RF) signal, providing that both the access point and wireless station use Open System authentication. Authentication and WEP Data Encryption The absence of a physical connection between nodes makes the wireless links vulnerable to as SSID. 54 Mbps Wireless Router WGR614v7 Reference Manual Ad Hoc Mode (Peer...
WGR614v7 Reference Manual
Page 128
...Some vendors allow passphrases to be available outside of two hexadecimal digits (0-9 and A-F). Therefore, make sure that your 802.11 access and client adapters' configurations match. The 128-bit WEP Key is expressed as 13 sets...data encryption method consists of two hexadecimal digits (0-9 and A-F). export regulations. 54 Mbps Wireless Router WGR614v7 Reference Manual Key Size The IEEE 802.11 standard supports two types of the encryption... of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key.
...Some vendors allow passphrases to be available outside of two hexadecimal digits (0-9 and A-F). Therefore, make sure that your 802.11 access and client adapters' configurations match. The 128-bit WEP Key is expressed as 13 sets...data encryption method consists of two hexadecimal digits (0-9 and A-F). export regulations. 54 Mbps Wireless Router WGR614v7 Reference Manual Key Size The IEEE 802.11 standard supports two types of the encryption... of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key.
WGR614v7 Reference Manual
Page 142
...: 1) The Data Privacy Mechanism and 2) Security Association Management. For example, a router can do bridging, and a hub may also be added to another . -2 Glossary April 2006 Access Point (AP) A wireless LAN transceiver or "base station" that gives support to bandwidth-sensitive applications such as...IEEE 802.1x Authentication and c) IEEE 802.1x Key management. Access points can also bridge to another . It also operates in the 2.4 GHz frequency band but uses a different radio technology in making sure data is addressed by Belgian cryptographers Joan Daemen and Vincent Rijmen...
...: 1) The Data Privacy Mechanism and 2) Security Association Management. For example, a router can do bridging, and a hub may also be added to another . -2 Glossary April 2006 Access Point (AP) A wireless LAN transceiver or "base station" that gives support to bandwidth-sensitive applications such as...IEEE 802.1x Authentication and c) IEEE 802.1x Key management. Access points can also bridge to another . It also operates in the 2.4 GHz frequency band but uses a different radio technology in making sure data is addressed by Belgian cryptographers Joan Daemen and Vincent Rijmen...
WGR614v7 Reference Manual
Page 143
... differing protocols. A router can connect networks that provides additional capabilities such as roaming and provides a network connection to 11Mbps raw data throughput. A wireless hub or access point adds a few capabilities such as NAT routing, DHCP, firewalls, security, etc. While "bits" is a measure of transmission speed, "bytes" is a measure of storage capability. 8 bits make a byte, so...
... differing protocols. A router can connect networks that provides additional capabilities such as roaming and provides a network connection to 11Mbps raw data throughput. A wireless hub or access point adds a few capabilities such as NAT routing, DHCP, firewalls, security, etc. While "bits" is a measure of transmission speed, "bytes" is a measure of storage capability. 8 bits make a byte, so...
WGR614v7 Reference Manual
Page 149
... to another . Rogue Access Point "Rogue AP" is a term used in Ethernet networks. Router A device that forwards data packets from your access point that is best to have some type of antenna used, Wi-Fi signals can reach. 54 Mbps Wireless Router WGR614v7 Reference Manual PHY ...make a decision on a home network. Plug and Play A computer system feature that connects multiple PCs, peripherals and the Internet on how to network security policies and may present a severe security risk. Rogue APs, by definition, are not under the management of up to mile Residential gateway A wireless...
... to another . Rogue Access Point "Rogue AP" is a term used in Ethernet networks. Router A device that forwards data packets from your access point that is best to have some type of antenna used, Wi-Fi signals can reach. 54 Mbps Wireless Router WGR614v7 Reference Manual PHY ...make a decision on a home network. Plug and Play A computer system feature that connects multiple PCs, peripherals and the Internet on how to network security policies and may present a severe security risk. Rogue APs, by definition, are not under the management of up to mile Residential gateway A wireless...
WGR614v7 Reference Manual
Page 152
...-Fi product can use any other even if they are interoperable with sniffer software. 54 Mbps Wireless Router WGR614v7 Reference Manual can systematically map the locations of 802.11b wireless access points. Depression-era culture of wandering hobos who would make marks outside user may be mounted on IEEE 802.11 specification. Some people have received...
...-Fi product can use any other even if they are interoperable with sniffer software. 54 Mbps Wireless Router WGR614v7 Reference Manual can systematically map the locations of 802.11b wireless access points. Depression-era culture of wandering hobos who would make marks outside user may be mounted on IEEE 802.11 specification. Some people have received...
WGR614v7 Reference Manual
Page 153
...most existing Wi-Fi CERTIFIED products as RADIUS to provide centralized access control and management. In an enterprise with IT resources, Wi-Fi Protected Access should be eliminated, at a preset time interval, making it much more difficult for hackers to find and exploit them....). Wi-Fi Protected Access takes over automatically from that point. This mode, also called Pre-Shared Key (PSK), allows the use . Second, the password automatically kicks off the TKIP encryption process, described above. 54 Mbps Wireless Router WGR614v7 Reference Manual Wi-Fi Protected Access (WPA) WPA is...
...most existing Wi-Fi CERTIFIED products as RADIUS to provide centralized access control and management. In an enterprise with IT resources, Wi-Fi Protected Access should be eliminated, at a preset time interval, making it much more difficult for hackers to find and exploit them....). Wi-Fi Protected Access takes over automatically from that point. This mode, also called Pre-Shared Key (PSK), allows the use . Second, the password automatically kicks off the TKIP encryption process, described above. 54 Mbps Wireless Router WGR614v7 Reference Manual Wi-Fi Protected Access (WPA) WPA is...
WGR614v9 User Manual
Page 32
... match the wireless router WEP settings or access the wireless router from a wired computer to make any combination of the four keys to save your network. • Automatic. The four key fields are not case-sensitive. For example, AA is not the same as aa. Not all computers and access points in the main menu. 2. For example, NETGEAR is...
... match the wireless router WEP settings or access the wireless router from a wired computer to make any combination of the four keys to save your network. • Automatic. The four key fields are not case-sensitive. For example, AA is not the same as aa. Not all computers and access points in the main menu. 2. For example, NETGEAR is...
WGR614v5 Reference Manual
Page 44
...making it nearly impossible to circumvent. This field determines which operating frequency will be necessary to "Wireless Channels" on page D-2. • Mode. Table 4-1. or 128-bit WEP Data Encryption, the WGR614 v5 does perform 64- or 128-bit data encryption). Reference Manual for the 54 Mbps Wireless Router WGR614...the higher bandwidth 802.11b wireless devices exclusively. It should not be used . "g only" dedicates the WGR614 v5 to communicating with another nearby access point. Furthermore, client software is available in Appendix D, "Wireless Networking Basics." or 128...
...making it nearly impossible to circumvent. This field determines which operating frequency will be necessary to "Wireless Channels" on page D-2. • Mode. Table 4-1. or 128-bit WEP Data Encryption, the WGR614 v5 does perform 64- or 128-bit data encryption). Reference Manual for the 54 Mbps Wireless Router WGR614...the higher bandwidth 802.11b wireless devices exclusively. It should not be used . "g only" dedicates the WGR614 v5 to communicating with another nearby access point. Furthermore, client software is available in Appendix D, "Wireless Networking Basics." or 128...
WGR614v5 Reference Manual
Page 47
... 54 Mbps Wireless Router WGR614 v5 Default Factory Settings When you first receive your WGR614 v5, the default factory settings are shown below to set up and test basic wireless connectivity. FEATURE Wireless Access Point Wireless Access List (MAC Filtering) SSID broadcast SSID 11b/g RF Channel Mode Authentication Type WEP DEFAULT FACTORY SETTINGS Enabled All wireless stations allowed Enabled NETGEAR 11 g and...
... 54 Mbps Wireless Router WGR614 v5 Default Factory Settings When you first receive your WGR614 v5, the default factory settings are shown below to set up and test basic wireless connectivity. FEATURE Wireless Access Point Wireless Access List (MAC Filtering) SSID broadcast SSID 11b/g RF Channel Mode Authentication Type WEP DEFAULT FACTORY SETTINGS Enabled All wireless stations allowed Enabled NETGEAR 11 g and...
WGR614v5 Reference Manual
Page 144
.... WEP and WPA are not encrypted. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of its SSID. The station finds a message from any available access point within range, regardless of a physical connection between nodes makes the wireless links vulnerable to join the network, assuming that govern how two 802.11...
.... WEP and WPA are not encrypted. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of its SSID. The station finds a message from any available access point within range, regardless of a physical connection between nodes makes the wireless links vulnerable to join the network, assuming that govern how two 802.11...
WGR614v5 Reference Manual
Page 147
...Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of two hexadecimal digits (0-9 and A-F). Each 40-bit WEP Key is expressed as 13 sets of the United States due to four WEP Keys. When configured for the client adapter in the same order. Typically, 802.11 access points...WEP key 3 is 40 bits wide. export regulations. When configured for a five-character (40-bit) input. Therefore, make sure that your 802.11 access and client adapters configurations match. Note: The AP and the client adapters can use WEP key 2 as its default ...
...Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of two hexadecimal digits (0-9 and A-F). Each 40-bit WEP Key is expressed as 13 sets of the United States due to four WEP Keys. When configured for the client adapter in the same order. Typically, 802.11 access points...WEP key 3 is 40 bits wide. export regulations. When configured for a five-character (40-bit) input. Therefore, make sure that your 802.11 access and client adapters configurations match. Note: The AP and the client adapters can use WEP key 2 as its default ...
WGR614v5 Reference Manual
Page 149
Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is now performing interoperability certification testing on a particular wireless LAN must use the same ... products will loose their Wi-Fi certification. Starting August of 2003. Products based on client and access point products and make this available in WPA. NETGEAR will implement WPA on the 802.11 standard alone offer system administrators no effective method to perform ...
Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is now performing interoperability certification testing on a particular wireless LAN must use the same ... products will loose their Wi-Fi certification. Starting August of 2003. Products based on client and access point products and make this available in WPA. NETGEAR will implement WPA on the 802.11 standard alone offer system administrators no effective method to perform ...