MR814v2 Reference Manual
Page 13
... MR814v2 router provides the following features: • 802.11b Standards-based wireless networking • Easy, web-based setup for installation and management • Content Filtering and Site Blocking Security • Built in firewall protects you can establish restricted access policies based on time-of-day, Website addresses and address keywords, and share high-speed cable/DSL...
... MR814v2 router provides the following features: • 802.11b Standards-based wireless networking • Easy, web-based setup for installation and management • Content Filtering and Site Blocking Security • Built in firewall protects you can establish restricted access policies based on time-of-day, Website addresses and address keywords, and share high-speed cable/DSL...
MR814v2 Reference Manual
Page 14
...; Blocks unwanted traffic from the Internet to your LAN. • Blocks access from reaching your wireless and Ethernet devices. You can also configure the router to send immediate alert messages to access objectionable Internet sites. 1-2 Introduction A Powerful, True Firewall ...only devices that you to control access to Internet content by screening for the MR814v2 Cable/DSL Wireless Router 802.11b Standards-based Wireless Networking The MR814v2 router includes an 802.11b-compliant wireless access point, providing continuous, high-speed 11 Mbps access between your PCs. The access...
...; Blocks unwanted traffic from the Internet to your LAN. • Blocks access from reaching your wireless and Ethernet devices. You can also configure the router to send immediate alert messages to access objectionable Internet sites. 1-2 Introduction A Powerful, True Firewall ...only devices that you to control access to Internet content by screening for the MR814v2 Cable/DSL Wireless Router 802.11b Standards-based Wireless Networking The MR814v2 router includes an 802.11b-compliant wireless access point, providing continuous, high-speed 11 Mbps access between your PCs. The access...
MR814v2 Reference Manual
Page 38
...data encryption options of your wireless equipment. MR814 v2 Wireless Data Security Options Range: Up to 500 Feet 1) Open System: Easy but no security 2) MAC Access List: No data security 3) WEP: Security but the data broadcast over 802.11b wireless networks at a maximum ...range of the browser interface. Reference Manual for others outside of your immediate area to 500 feet. Such distances can allow for the MR814v2 Cable/DSL Wireless Router Implement Appropriate Wireless Security Note: Indoors, computers can connect over the wireless ...
...data encryption options of your wireless equipment. MR814 v2 Wireless Data Security Options Range: Up to 500 Feet 1) Open System: Easy but no security 2) MAC Access List: No data security 3) WEP: Security but the data broadcast over 802.11b wireless networks at a maximum ...range of the browser interface. Reference Manual for others outside of your immediate area to 500 feet. Such distances can allow for the MR814v2 Cable/DSL Wireless Router Implement Appropriate Wireless Security Note: Indoors, computers can connect over the wireless ...
MR814v2 Reference Manual
Page 42
...explanation of each of these options, as defined by the IEEE 802.11b wireless communication standard. Also, if you choose for the MR814v2 router. You can tell if a web site is separate from the...Cable/DSL Wireless Router Choosing Authentication and Security Encryption Methods Figure 3-7: Encryption Strength Restricting wireless access to your network prevents intruders from connecting to "Authentication and WEP" on page D-3 for a full explanation of each of these options, as defined by the IEEE 802.11b wireless communication standard. 3-6 Wireless Configuration However, the wireless...
...explanation of each of these options, as defined by the IEEE 802.11b wireless communication standard. Also, if you choose for the MR814v2 router. You can tell if a web site is separate from the...Cable/DSL Wireless Router Choosing Authentication and Security Encryption Methods Figure 3-7: Encryption Strength Restricting wireless access to your network prevents intruders from connecting to "Authentication and WEP" on page D-3 for a full explanation of each of these options, as defined by the IEEE 802.11b wireless communication standard. 3-6 Wireless Configuration However, the wireless...
MR814v2 Reference Manual
Page 47
... MR814v2 router. 3. Be sure you will be automatically populated with its default LAN address of password, or using whatever LAN address and password you set up. 2. Wireless adapter configuration utilities such as defined by the IEEE 802.11b wireless communication standard. Wireless Configuration ... Automatic - You must be active. These values must then either configure your wireless connection when you click on page D-5 for the MR814v2 Cable/DSL Wireless Router 1. Note: When configuring the router from a wired PC to the MR814v2 firewall at its default user name of...
... MR814v2 router. 3. Be sure you will be automatically populated with its default LAN address of password, or using whatever LAN address and password you set up. 2. Wireless adapter configuration utilities such as defined by the IEEE 802.11b wireless communication standard. Wireless Configuration ... Automatic - You must be active. These values must then either configure your wireless connection when you click on page D-5 for the MR814v2 Cable/DSL Wireless Router 1. Note: When configuring the router from a wired PC to the MR814v2 firewall at its default user name of...
MR814v2 Reference Manual
Page 90
... (also called 64-bits), 128-bits WEP data encryption A-2 Technical Specifications Reference Manual for the MR814v2 Cable/DSL Wireless Router Interface Specifications LAN: WAN: Wireless Radio Data Rate Frequency Data Encoding: 802.11b Operating Range Maximum Computers Per Wireless Network: 802.11b Operating Frequency Ranges 802.11b Encryption VCCI Class B EN 55 022 (CISPR 22), Class B 10BASE-T or 100BASE-Tx, RJ-... (60 m) 561 ft (170 m) 264 ft (80 m) 890 ft (270 m) 430 ft (130 m) 1485 ft (450 m) 660 ft (200 m) Limited by the amount of wireless network traffic generated by each node.
... (also called 64-bits), 128-bits WEP data encryption A-2 Technical Specifications Reference Manual for the MR814v2 Cable/DSL Wireless Router Interface Specifications LAN: WAN: Wireless Radio Data Rate Frequency Data Encoding: 802.11b Operating Range Maximum Computers Per Wireless Network: 802.11b Operating Frequency Ranges 802.11b Encryption VCCI Class B EN 55 022 (CISPR 22), Class B 10BASE-T or 100BASE-Tx, RJ-... (60 m) 561 ft (170 m) 264 ft (80 m) 890 ft (270 m) 430 ft (130 m) 1485 ft (450 m) 660 ft (200 m) Limited by the amount of wireless network traffic generated by each node.
MR814v2 Reference Manual
Page 129
... point. 7. The station can join any network and receive any access points that govern how two 802.11b devices communicate. With Open System authentication, a wireless PC can now communicate with an Ethernet network through the access point. The station finds a message ... point or communicate with the station. 8. The access point associates with the network. Turn on the wireless station. 2. The station listens for the MR814v2 Cable/DSL Wireless Router Authentication and WEP The absence of authentication: Open System and Shared Key. • Open System Authentication...
... point. 7. The station can join any network and receive any access points that govern how two 802.11b devices communicate. With Open System authentication, a wireless PC can now communicate with an Ethernet network through the access point. The station finds a message ... point or communicate with the station. 8. The access point associates with the network. Turn on the wireless station. 2. The station listens for the MR814v2 Cable/DSL Wireless Router Authentication and WEP The absence of authentication: Open System and Shared Key. • Open System Authentication...
MR814v2 Reference Manual
Page 130
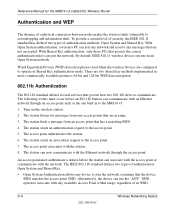
Reference Manual for the MR814v2 Cable/DSL Wireless Router • Shared Key Authentication requires that corresponds to the station's default key. The access point authenticates the station. 3. The access point compares the decrypted text ... WEP Key that the station and the access point have the same WEP Key to the access point. 4. These two authentication procedures are described below . 802.11b Authentication Open System Steps 1) Authentication request sent to AP 2) AP authenticates Client attempting to connect 3) Client connects to the station. 3. The station associates with the...
Reference Manual for the MR814v2 Cable/DSL Wireless Router • Shared Key Authentication requires that corresponds to the station's default key. The access point authenticates the station. 3. The access point compares the decrypted text ... WEP Key that the station and the access point have the same WEP Key to the access point. 4. These two authentication procedures are described below . 802.11b Authentication Open System Steps 1) Authentication request sent to AP 2) AP authenticates Client attempting to connect 3) Client connects to the station. 3. The station associates with the...
MR814v2 Reference Manual
Page 131
..., you want to use. For authentication purposes, the 802.11b network uses Open System Authentication. The station connects to communicate with either the 802.11b network or Ethernet network. Typically, there are three WEP Encryption options available for the MR814v2 Cable/DSL Wireless Router 5. This process is illustrated in below. 802.11b Authentication Shared Key Steps 1) Authentication request sent to...
..., you want to use. For authentication purposes, the 802.11b network uses Open System Authentication. The station connects to communicate with either the 802.11b network or Ethernet network. Typically, there are three WEP Encryption options available for the MR814v2 Cable/DSL Wireless Router 5. This process is illustrated in below. 802.11b Authentication Shared Key Steps 1) Authentication request sent to...
MR814v2 Reference Manual
Page 132
... method, allows for the MR814v2 Cable/DSL Wireless Router 3. Some vendors allow passphrases to be entered instead of two hexadecimal digits (0-9 and A-F). export regulations. Note: Typically, 802.11b access points can only store one 128-bit key. The receiving 802.11b device decrypts the data using a.... Use WEP for 128-bit encryption, 802.11b products typically support four WEP Keys but some manufacturers support only one . This encryption key will be available outside of two hexadecimal digits (0-9 and A-F). D-6 Wireless Networking Basics Some vendors refer to four...
... method, allows for the MR814v2 Cable/DSL Wireless Router 3. Some vendors allow passphrases to be entered instead of two hexadecimal digits (0-9 and A-F). export regulations. Note: Typically, 802.11b access points can only store one 128-bit key. The receiving 802.11b device decrypts the data using a.... Use WEP for 128-bit encryption, 802.11b products typically support four WEP Keys but some manufacturers support only one . This encryption key will be available outside of two hexadecimal digits (0-9 and A-F). D-6 Wireless Networking Basics Some vendors refer to four...
MR814v2 Reference Manual
Page 133
Reference Manual for the MR814v2 Cable/DSL Wireless Router WEP Configuration Options The WEP settings must match on all of the 802.11b client adapters on the client adapter, etc. Note: The AP and the client adapters can use WEP key 2 as its default key to ...keys for example, channel 1 and channel 2) in the ISM (Industrial, Scientific, and Medical) band between access points, then all of the 802.11b access points and all 802.11b devices that allow the maximum channel separation will decrease the amount of the signals, a node sending signals using neighboring channels (for the client...
Reference Manual for the MR814v2 Cable/DSL Wireless Router WEP Configuration Options The WEP settings must match on all of the 802.11b client adapters on the client adapter, etc. Note: The AP and the client adapters can use WEP key 2 as its default key to ...keys for example, channel 1 and channel 2) in the ISM (Industrial, Scientific, and Medical) band between access points, then all of the 802.11b access points and all 802.11b devices that allow the maximum channel separation will decrease the amount of the signals, a node sending signals using neighboring channels (for the client...
MR814v2 Reference Manual
Page 137
... part of the 400+ vendors that forwards data between sources and destinations. See netmask. UPnP. The cable used to -Point Protocol RFC RIP router Routing Information Protocol subnet mask UPnP Universal Plug and Play UTP WAN WEP wide area network Windows Internet...For Comment. Unshielded twisted pair. WEP is a data encryption protocol for 802.11b wireless networks. This allows your Windows PCs can determine minimum distance paths between networks. Reference Manual for the MR814v2 Cable/DSL Wireless Router Point-to extend or connect remotely located local area networks. RFCs can ...
... part of the 400+ vendors that forwards data between sources and destinations. See netmask. UPnP. The cable used to -Point Protocol RFC RIP router Routing Information Protocol subnet mask UPnP Universal Plug and Play UTP WAN WEP wide area network Windows Internet...For Comment. Unshielded twisted pair. WEP is a data encryption protocol for 802.11b wireless networks. This allows your Windows PCs can determine minimum distance paths between networks. Reference Manual for the MR814v2 Cable/DSL Wireless Router Point-to extend or connect remotely located local area networks. RFCs can ...
MR814v3 Reference Manual
Page 15
...of the Router The MR814 v3 Cable/DSL Wireless Router with multiple Web content filtering options, plus browsing activity reporting and instant alerts -- both via e-mail. The MR814 v3 router provides the following features: • 802.11b Standards-based wireless networking • WPA-PSK wireless security. &#...Parents and network administrators can install and use the router within minutes. The MR814 v3 router provides you can establish restricted access policies based on time-of the NETGEAR MR814 v3 Cable/DSL Wireless Router. With minimum setup, you with 4-port switch connects...
...of the Router The MR814 v3 Cable/DSL Wireless Router with multiple Web content filtering options, plus browsing activity reporting and instant alerts -- both via e-mail. The MR814 v3 router provides the following features: • 802.11b Standards-based wireless networking • WPA-PSK wireless security. &#...Parents and network administrators can install and use the router within minutes. The MR814 v3 router provides you can establish restricted access policies based on time-of the NETGEAR MR814 v3 Cable/DSL Wireless Router. With minimum setup, you with 4-port switch connects...
MR814v3 Reference Manual
Page 16
... E-mail pager whenever a significant event occurs. • With its content filtering feature, the MR814 v3 prevents objectionable content from your LAN to Internet content by screening for the MR814 v3 Cable/DSL Wireless Router 802.11b Standards-based Wireless Networking The MR814 v3 router includes an 802.11b-compliant wireless access point, providing continuous, high-speed 11 Mbps access between your PCs. You can...
... E-mail pager whenever a significant event occurs. • With its content filtering feature, the MR814 v3 prevents objectionable content from your LAN to Internet content by screening for the MR814 v3 Cable/DSL Wireless Router 802.11b Standards-based Wireless Networking The MR814 v3 router includes an 802.11b-compliant wireless access point, providing continuous, high-speed 11 Mbps access between your PCs. You can...
MR814v3 Reference Manual
Page 96
...-bits), 128-bits WEP data encryption A-2 Technical Specifications 202-10039-01 Reference Manual for the MR814 v3 Cable/DSL Wireless Router Interface Specifications LAN: WAN: Wireless Radio Data Rate Frequency Data Encoding: 802.11b Operating Range Maximum Computers Per Wireless Network: 802.11b Operating Frequency Ranges 802.11b Encryption VCCI Class B EN 55 022 (CISPR 22), Class B 10BASE-T or 100BASE-Tx, RJ-...ft (60 m) 561 ft (170 m) 264 ft (80 m) 890 ft (270 m) 430 ft (130 m) 1485 ft (450 m) 660 ft (200 m) Limited by the amount of wireless network traffic generated by each node.
...-bits), 128-bits WEP data encryption A-2 Technical Specifications 202-10039-01 Reference Manual for the MR814 v3 Cable/DSL Wireless Router Interface Specifications LAN: WAN: Wireless Radio Data Rate Frequency Data Encoding: 802.11b Operating Range Maximum Computers Per Wireless Network: 802.11b Operating Frequency Ranges 802.11b Encryption VCCI Class B EN 55 022 (CISPR 22), Class B 10BASE-T or 100BASE-Tx, RJ-...ft (60 m) 561 ft (170 m) 264 ft (80 m) 890 ft (270 m) 430 ft (130 m) 1485 ft (450 m) 660 ft (200 m) Limited by the amount of wireless network traffic generated by each node.
MR814v3 Reference Manual
Page 113
... C Preparing Your Network This appendix describes how to prepare your network to connect to the Internet through the MR814 v3 Cable/DSL Wireless Router and how to verify the readiness of your firewall. Note: If an ISP technician configured your computer during the...21 or "Obtaining ISP Configuration Information for Macintosh Computers" on your router. The cable or DSL broadband modem must have an 802.11g or 802.11b wireless adapter or an installed Ethernet Network Interface Card (NIC) and an Ethernet cable. Write down this information before you must use in web Configuration ...
... C Preparing Your Network This appendix describes how to prepare your network to connect to the Internet through the MR814 v3 Cable/DSL Wireless Router and how to verify the readiness of your firewall. Note: If an ISP technician configured your computer during the...21 or "Obtaining ISP Configuration Information for Macintosh Computers" on your router. The cable or DSL broadband modem must have an 802.11g or 802.11b wireless adapter or an installed Ethernet Network Interface Card (NIC) and an Ethernet cable. Write down this information before you must use in web Configuration ...
MR814v3 Reference Manual
Page 140
... two types of its SSID. The following events must authenticate a station before an 802.11b Station can join any network and receive any device to join the network, assuming that are not encrypted. The station listens for the MR814 v3 Cable/DSL Wireless Router Authentication and WEP The absence of authentication: Open System and Shared Key. •...
... two types of its SSID. The following events must authenticate a station before an 802.11b Station can join any network and receive any device to join the network, assuming that are not encrypted. The station listens for the MR814 v3 Cable/DSL Wireless Router Authentication and WEP The absence of authentication: Open System and Shared Key. •...
MR814v3 Reference Manual
Page 141
... connect 3) Client connects to network Access Point Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA N LO CA L MODEL FVM318 100 ACT Enable LNK/ACT 1 2 3 4 5 6 7 8 Cable or DLS modem Figure 8-1: 802.11b open system authentication Shared Key Authentication The following ...share the same WEP Key and the access point authenticates the station. Reference Manual for the MR814 v3 Cable/DSL Wireless Router • Shared Key Authentication requires that corresponds to the station's default key. The station associates with the original ...
... connect 3) Client connects to network Access Point Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA N LO CA L MODEL FVM318 100 ACT Enable LNK/ACT 1 2 3 4 5 6 7 8 Cable or DLS modem Figure 8-1: 802.11b open system authentication Shared Key Authentication The following ...share the same WEP Key and the access point authenticates the station. Reference Manual for the MR814 v3 Cable/DSL Wireless Router • Shared Key Authentication requires that corresponds to the station's default key. The station associates with the original ...
MR814v3 Reference Manual
Page 142
... Parameters Before enabling WEP on an 802.11b network, you want to use. The receiving 802.11b device decrypts the data using a configured WEP Key. Reference Manual for 802.11b products: 1. D-6 Wireless Networking Basics 202-10039-01 Typically, there are three WEP Encryption options available for the MR814 v3 Cable/DSL Wireless Router 5. For authentication purposes, the 802.11b network uses Open System Authentication...
... Parameters Before enabling WEP on an 802.11b network, you want to use. The receiving 802.11b device decrypts the data using a configured WEP Key. Reference Manual for 802.11b products: 1. D-6 Wireless Networking Basics 202-10039-01 Typically, there are three WEP Encryption options available for the MR814 v3 Cable/DSL Wireless Router 5. For authentication purposes, the 802.11b network uses Open System Authentication...
MR814v3 Reference Manual
Page 143
... sends using the same WEP Key. This encryption key will be available outside of two hexadecimal digits (0-9 and A-F). When configured for the MR814 v3 Cable/DSL Wireless Router 3. Reference Manual for 40-bit encryption, 802.11b products typically support up to four 128-bit WEP Keys but some manufacturers support only one . Therefore, make sure that your...
... sends using the same WEP Key. This encryption key will be available outside of two hexadecimal digits (0-9 and A-F). When configured for the MR814 v3 Cable/DSL Wireless Router 3. Reference Manual for 40-bit encryption, 802.11b products typically support up to four 128-bit WEP Keys but some manufacturers support only one . Therefore, make sure that your...