Command Line Interface Guide
Page 55
... application operated through a Telnet session. By directly entering commands, the user has greater configuration flexibility. Command Groups The system commands can be accessed from the CLI, which is described in the User's Guide and must be configured and maintained by a terminal keyboard and the ... C shell. The CLI is structured, describes the command syntax, and describes the command functionality. This guide also provides information for configuring the PowerConnect switch, details the procedures, and provides configuration examples. Configures and displays ACL information.
... application operated through a Telnet session. By directly entering commands, the user has greater configuration flexibility. Command Groups The system commands can be accessed from the CLI, which is described in the User's Guide and must be configured and maintained by a terminal keyboard and the ... C shell. The CLI is structured, describes the command syntax, and describes the command functionality. This guide also provides information for configuring the PowerConnect switch, details the procedures, and provides configuration examples. Configures and displays ACL information.
Command Line Interface Guide
Page 137
...full command. The following table contains the CLI shortcuts displayed by the help command, when used in the User Executive (EXEC) and Privileged Executive (EXEC) modes. This guide describes the negation effect for configuring the command history buffer, see the history-size command in the Line... error message is changed into a complete command. Using the CLI 137 All configuration commands have this guide. Command Completion CLI can complete partially entered commands when the user presses the or key. Short Form Commands The CLI supports the short forms of keyboard shortcuts to which...
...full command. The following table contains the CLI shortcuts displayed by the help command, when used in the User Executive (EXEC) and Privileged Executive (EXEC) modes. This guide describes the negation effect for configuring the command history buffer, see the history-size command in the Line... error message is changed into a complete command. Using the CLI 137 All configuration commands have this guide. Command Completion CLI can complete partially entered commands when the user presses the or key. Short Form Commands The CLI supports the short forms of keyboard shortcuts to which...
Command Line Interface Guide
Page 141
... modes. In this mode. Layer 3 (Network Layer) describes how a series of exchanges over various data links can deliver data between any two nodes in this guide, commands are organized into three categories: • Layer 2 (Data Link Layer) commands • Layer 3 (Network Layer) commands • Utility Commands Layer ... beneath the Configuration mode for further grouping of commands. To enter the next level, the Privileged EXEC mode, a password is the User EXEC mode. This level is reserved for tasks that do not directly affect the system configurations are defined at the top of the...
... modes. In this mode. Layer 3 (Network Layer) describes how a series of exchanges over various data links can deliver data between any two nodes in this guide, commands are organized into three categories: • Layer 2 (Data Link Layer) commands • Layer 3 (Network Layer) commands • Utility Commands Layer ... beneath the Configuration mode for further grouping of commands. To enter the next level, the Privileged EXEC mode, a password is the User EXEC mode. This level is reserved for tasks that do not directly affect the system configurations are defined at the top of the...
Command Line Interface Guide
Page 154
... must have a defined IP address, corresponding management access granted, and a connection to the network. Easy Setup Wizard The Easy Setup Wizard guides the user in the basic initial configuration of 192.168.2.1 but the Easy Setup Wizard provides the opportunity to the switch console port or through the ...Web, CLI and the remote Dell Network Manager. The user may enter to the system to set up the following steps: NOTE: This procedure is displayed. 2 Configure the switch using the...
... must have a defined IP address, corresponding management access granted, and a connection to the network. Easy Setup Wizard The Easy Setup Wizard guides the user in the basic initial configuration of 192.168.2.1 but the Easy Setup Wizard provides the opportunity to the switch console port or through the ...Web, CLI and the remote Dell Network Manager. The user may enter to the system to set up the following steps: NOTE: This procedure is displayed. 2 Configure the switch using the...
Command Line Interface Guide
Page 159
...manage the switch using the default system configuration.Note: You can skip the setup wizard, and enter CLI mode to Dell Easy Setup Wizard The Setup Wizard guides you through the initial switch configuration, and gets you must specify the management system IP address and the "community ...other SNMP accounts. (For more information on setting up an SNMP version 1 or 3 account, see the user documentation. For more information on adding management systems, see the user documentation). Welcome to manually configure the switch. Using the CLI 159 You can exit the setup wizard at ...
...manage the switch using the default system configuration.Note: You can skip the setup wizard, and enter CLI mode to Dell Easy Setup Wizard The Setup Wizard guides you through the initial switch configuration, and gets you must specify the management system IP address and the "community ...other SNMP accounts. (For more information on setting up an SNMP version 1 or 3 account, see the user documentation. For more information on adding management systems, see the user documentation). Welcome to manually configure the switch. Using the CLI 159 You can exit the setup wizard at ...
Command Line Interface Guide
Page 162
... Setup Wizard The Setup Wizard guides you through the initial switch configuration, and gets you like to run the setup wizard within 60 seconds, otherwise the system will continue with normal operation using SNMP (required for Dell Network Manager) you must answer this question within 60 ...seconds)? [Y/N] y Step 1: The system is used to login to select management unit)> Applying configuration, please wait ... You may setup other SNMP accounts. (For more information on setting up user accounts and changing...
... Setup Wizard The Setup Wizard guides you through the initial switch configuration, and gets you like to run the setup wizard within 60 seconds, otherwise the system will continue with normal operation using SNMP (required for Dell Network Manager) you must answer this question within 60 ...seconds)? [Y/N] y Step 1: The system is used to login to select management unit)> Applying configuration, please wait ... You may setup other SNMP accounts. (For more information on setting up user accounts and changing...
Command Line Interface Guide
Page 166
... and may copy a particular configuration file (remote or local) to the configuration file currently active in flash memory which are under control of the guide for the special file. • backup-config - identifies a file on the XMODEM connection. One of these will be used to refer to ... backup configuration file. • running -config image to a backupconfig file or to the special configuration image stored in the system. When the user copies a local source file into one of these special files and the source file has an attached file description, it is a simplified FTP ...
... and may copy a particular configuration file (remote or local) to the configuration file currently active in flash memory which are under control of the guide for the special file. • backup-config - identifies a file on the XMODEM connection. One of these will be used to refer to ... backup configuration file. • running -config image to a backupconfig file or to the special configuration image stored in the system. When the user copies a local source file into one of these special files and the source file has an attached file description, it is a simplified FTP ...
User's Guide
Page 38
...Guide-provides examples of users accessing the switch. Once established, such a connection is a client/server-based protocol in which the server maintains a user database that contains user authentication information, such as user name, password, and accounting information. This connection provides functionality that is a protocol that the PowerConnect...provides centralized security for the PowerConnect PowerConnect 6200 Series switches are available on the Dell Support website at www.support.dell.com/manuals: • Getting Started Guide-provides information about configuring those...
...Guide-provides examples of users accessing the switch. Once established, such a connection is a client/server-based protocol in which the server maintains a user database that contains user authentication information, such as user name, password, and accounting information. This connection provides functionality that is a protocol that the PowerConnect...provides centralized security for the PowerConnect PowerConnect 6200 Series switches are available on the Dell Support website at www.support.dell.com/manuals: • Getting Started Guide-provides information about configuring those...
User's Guide
Page 81
... system to set up must be immediately deployed, functional, and completely manageable through the serial interface. The Easy Setup Wizard guides you may return later to use the local authentication setting only. The initial turn-up basic system configuration and security and to...feature? After the initial set up more advanced security considerations. Configuring Dell PowerConnect 81 This administrative account setup by the wizard has the highest privilege level (level 15). The wizard configures one privileged user account during the set up, you in this section). •...
... system to set up must be immediately deployed, functional, and completely manageable through the serial interface. The Easy Setup Wizard guides you may return later to use the local authentication setting only. The initial turn-up basic system configuration and security and to...feature? After the initial set up more advanced security considerations. Configuring Dell PowerConnect 81 This administrative account setup by the wizard has the highest privilege level (level 15). The wizard configures one privileged user account during the set up, you in this section). •...
User's Guide
Page 84
... for the default management VLAN (1). • A default gateway address is in [ ]. NOTE: In the example below, the possible user options are examples only. Help text is configured. Example of prompts and responses associated with running as quickly as defined above . After you... management station, you must respond to the next question to Dell Easy Setup Wizard The Setup Wizard guides you through the initial switch configuration, and gets you up as possible. Would you like to run the setup wizard within 60 seconds)? [Y/N] y Step 1: 84 Configuring Dell PowerConnect
... for the default management VLAN (1). • A default gateway address is in [ ]. NOTE: In the example below, the possible user options are examples only. Help text is configured. Example of prompts and responses associated with running as quickly as defined above . After you... management station, you must respond to the next question to Dell Easy Setup Wizard The Setup Wizard guides you through the initial switch configuration, and gets you up as possible. Would you like to run the setup wizard within 60 seconds)? [Y/N] y Step 1: 84 Configuring Dell PowerConnect
User's Guide
Page 88
...already provided by the interface number. is formed by the interface type followed by the user is the 10 Gb Ethernet port 2). 6200 Series CLI Reference Guide For detailed information on Dell devices are as : • Modifying Switching Port Default Settings • Retrieving an IP... BOOTP, the configuration received from these servers includes the IP address, and may include subnet mask and default gateway. 88 Configuring Dell PowerConnect Parameters that are defined in a stacking solution where a number of parameters that are listed. For example, 2/g10 identifies gigabit ...
...already provided by the interface number. is formed by the interface type followed by the user is the 10 Gb Ethernet port 2). 6200 Series CLI Reference Guide For detailed information on Dell devices are as : • Modifying Switching Port Default Settings • Retrieving an IP... BOOTP, the configuration received from these servers includes the IP address, and may include subnet mask and default gateway. 88 Configuring Dell PowerConnect Parameters that are defined in a stacking solution where a number of parameters that are listed. For example, 2/g10 identifies gigabit ...
User's Guide
Page 117
...• Time - For example, 11/01/05 is month, day, year (MM/DD/YY). Displays the switch's position in the CLI Reference Guide: Configuring System Information 117 Initiating a Telnet Session 1. NOTE: The appropriate telnet parameters are applied, and the device is hour, minute, second (HH...on the GUI banner (if enabled). • Banner motd acknowledge - Displays the number of the switch. • Sys Uptime - Displays the user-defined device reference. • Serial No. - Open the Asset page. The Asset page contains the following fields: System Name, System Contact, System...
...• Time - For example, 11/01/05 is month, day, year (MM/DD/YY). Displays the switch's position in the CLI Reference Guide: Configuring System Information 117 Initiating a Telnet Session 1. NOTE: The appropriate telnet parameters are applied, and the device is hour, minute, second (HH...on the GUI banner (if enabled). • Banner motd acknowledge - Displays the number of the switch. • Sys Uptime - Displays the user-defined device reference. • Serial No. - Open the Asset page. The Asset page contains the following fields: System Name, System Contact, System...
User's Guide
Page 132
...Time protocol (NTP) traffic. To display the SNTP Server page, click System →SNTP →SNTP Server in the CLI Reference Guide. SNTP Servers The SNTP Servers page contains the following table summarizes the equivalent CLI commands you use to eight SNTP servers can be ...the Clock Commands chapter in the tree view. Up to define SNTP authentication settings. The following fields: • SNTP Server - Specifies user-defined key ID used to require server authentication for SNTP. The encryption key ID is defined in the SNTP Authentication page. 132 Configuring System...
...Time protocol (NTP) traffic. To display the SNTP Server page, click System →SNTP →SNTP Server in the CLI Reference Guide. SNTP Servers The SNTP Servers page contains the following table summarizes the equivalent CLI commands you use to eight SNTP servers can be ...the Clock Commands chapter in the tree view. Up to define SNTP authentication settings. The following fields: • SNTP Server - Specifies user-defined key ID used to require server authentication for SNTP. The encryption key ID is defined in the SNTP Authentication page. 132 Configuring System...
User's Guide
Page 146
Contains the user-defined default domain name. When configured, the default domain name is assigned to the specified host name. • Remove Host Name - The Host Name Mapping ... contains the following fields: • Host Name - Provides an IP address that perform this function, see the IP Addressing Commands chapter in the CLI Reference Guide. To display the Host Name Mapping page, click System →IP Addressing →Host Name Mapping. Table 6-16.
Contains the user-defined default domain name. When configured, the default domain name is assigned to the specified host name. • Remove Host Name - The Host Name Mapping ... contains the following fields: • Host Name - Provides an IP address that perform this function, see the IP Addressing Commands chapter in the CLI Reference Guide. To display the Host Name Mapping page, click System →IP Addressing →Host Name Mapping. Table 6-16.
User's Guide
Page 162
...is updated. Defines a management access-list, and enters the access-list for configuration. Defines a permit rule. Authentication Profiles User authentication occurs locally and on the device. To display the Authentication Profiles page, click System →Management Security →...Authentication Profiles in the CLI Reference Guide. Removing a Rule 1. Open the Access Profile page. 2. Click Show All to define access profiles. Displays management access-lists...
...is updated. Defines a management access-list, and enters the access-list for configuration. Defines a permit rule. Authentication Profiles User authentication occurs locally and on the device. To display the Authentication Profiles page, click System →Management Security →...Authentication Profiles in the CLI Reference Guide. Removing a Rule 1. Open the Access Profile page. 2. Click Show All to define access profiles. Displays management access-lists...
User's Guide
Page 165
... information about the CLI commands that perform this function, see the AAA Commands chapter in the CLI Reference Guide: The following table summarizes the equivalent CLI commands you use. Configuring System Information 165 The user authentication profile is removed. Click Apply Changes. Defines login authentication. Removing an Authentication Profiles Entry 1. The Authentication...
... information about the CLI commands that perform this function, see the AAA Commands chapter in the CLI Reference Guide: The following table summarizes the equivalent CLI commands you use. Configuring System Information 165 The user authentication profile is removed. Click Apply Changes. Defines login authentication. Removing an Authentication Profiles Entry 1. The Authentication...
User's Guide
Page 170
...the amount of times a password is changed, before a password is 1 to 10. Indicates the amount of time that users can be reused. Define the relevant fields. 170 Configuring System Information Defining Password Constraints 1. Indicates the minimum password length, when...• Preventing frequent password reuse • Locking out users out after failed login attempts To display the Password Management page, click System →Management Security →Password Management in the CLI Reference Guide for additional information. • Consecutive Passwords Before Reuse (1-...
...the amount of times a password is changed, before a password is 1 to 10. Indicates the amount of time that users can be reused. Define the relevant fields. 170 Configuring System Information Defining Password Constraints 1. Indicates the minimum password length, when...• Preventing frequent password reuse • Locking out users out after failed login attempts To display the Password Management page, click System →Management Security →Password Management in the CLI Reference Guide for additional information. • Consecutive Passwords Before Reuse (1-...
User's Guide
Page 171
...function, see the Password Management Commands chapter in the tree view. To display the Local User Database page, click System →Management Security →Local User Database in the CLI Reference Guide. Defining Password Constraints Using CLI Commands For information about the CLI commands that are required...passwords configuration Description Implements aging on the passwords such that count. Table 6-25. When a lockout count is configured, a user who is updated. The password constraints are defined, and the device is logging in must enter the correct password within that...
...function, see the Password Management Commands chapter in the tree view. To display the Local User Database page, click System →Management Security →Local User Database in the CLI Reference Guide. Defining Password Constraints Using CLI Commands For information about the CLI commands that are required...passwords configuration Description Implements aging on the passwords such that count. Table 6-25. When a lockout count is configured, a user who is updated. The password constraints are defined, and the device is logging in must enter the correct password within that...
Getting Started Guide
Page 14
...Initial Configuration Procedure You can perform the initial configuration using the Command Line Interface (CLI). The wizard configures one privileged user account during the initial configuration. Before setting up the IP address for initial switch configuration. For more information on the...8226; Configures the default gateway IP address. 12 Getting Started Guide After the initial configuration, you received it. • The PowerConnect switch booted successfully. • The console connection was established and the Dell Easy Setup Wizard prompt appears on the screen of a VT100 ...
...Initial Configuration Procedure You can perform the initial configuration using the Command Line Interface (CLI). The wizard configures one privileged user account during the initial configuration. Before setting up the IP address for initial switch configuration. For more information on the...8226; Configures the default gateway IP address. 12 Getting Started Guide After the initial configuration, you received it. • The PowerConnect switch booted successfully. • The console connection was established and the Dell Easy Setup Wizard prompt appears on the screen of a VT100 ...
Release Notes
Page 25
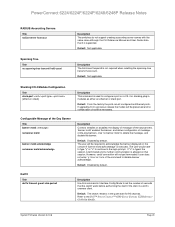
...-count Description The hold-count keyword is supported. The user would have to type "y" or "n" to continue to the Dell™ PowerConnect™ 6200 Series Systems CLI Reference Guide for 90 seconds. Refer to the login prompt. Default: Disabled by default. PowerConnect 6224/6224F/6224P/6248/6248P Release Notes RADIUS Accounting Servers Title radius-server host...
...-count Description The hold-count keyword is supported. The user would have to type "y" or "n" to continue to the Dell™ PowerConnect™ 6200 Series Systems CLI Reference Guide for 90 seconds. Refer to the login prompt. Default: Disabled by default. PowerConnect 6224/6224F/6224P/6248/6248P Release Notes RADIUS Accounting Servers Title radius-server host...