Design Guide
Page 6
... of image data and other information handled internally by the end user's machine. Print Controller Design Guide for Information Security Overview This document describes the structural layout and functional operations of the hardware and software for the multi-functional products and laser printers listed below (herein referred to the Operating Instructions for the specific machine in question. external I/F) and functions described in this document may not be supported by Ricoh...
... of image data and other information handled internally by the end user's machine. Print Controller Design Guide for Information Security Overview This document describes the structural layout and functional operations of the hardware and software for the multi-functional products and laser printers listed below (herein referred to the Operating Instructions for the specific machine in question. external I/F) and functions described in this document may not be supported by Ricoh...
Design Guide
Page 11
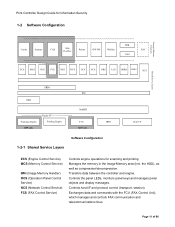
.../decompression. Transfers data between the controller and engine. Controls host I /F ECS (Engine Control Service) MCS (Memory Control Service) IMH (Image Memory Handler) OCS (Operation Panel Control Service) NCS (Network Control Service) FCS (FAX Control Service) Controls engine operations for Information Security 1-2 Software Configuration SDK Copier Scanner FAX Web DocBox Printer GW WS WebSys EAC VAS ECS MCS OCS FCS NCS DCS UCS CCS NRS LCS MIRS DESS SCS S Shared Service Layers SRM libc IMH Engine I/F Scanning Engine Printing Engine MFP...
.../decompression. Transfers data between the controller and engine. Controls host I /F ECS (Engine Control Service) MCS (Memory Control Service) IMH (Image Memory Handler) OCS (Operation Panel Control Service) NCS (Network Control Service) FCS (FAX Control Service) Controls engine operations for Information Security 1-2 Software Configuration SDK Copier Scanner FAX Web DocBox Printer GW WS WebSys EAC VAS ECS MCS OCS FCS NCS DCS UCS CCS NRS LCS MIRS DESS SCS S Shared Service Layers SRM libc IMH Engine I/F Scanning Engine Printing Engine MFP...
Design Guide
Page 12
... settings and machine operations. Controls the sending of machine configuration settings by the system as that converts the printer language into image data, which reads the original and then sends the data on or by e-mail Manages the Address Book data. diagnostics, firmware update, settings changes). Controls the encryption and decryption functions. 1-2-2 Principal Machine Functions Copier Printer Scanner FAX Activates the scanning engine, which is then printed out from the printing engine. Secondary data, such as a whole, and controls the switching of image data...
... settings and machine operations. Controls the sending of machine configuration settings by the system as that converts the printer language into image data, which reads the original and then sends the data on or by e-mail Manages the Address Book data. diagnostics, firmware update, settings changes). Controls the encryption and decryption functions. 1-2-2 Principal Machine Functions Copier Printer Scanner FAX Activates the scanning engine, which is then printed out from the printing engine. Secondary data, such as a whole, and controls the switching of image data...
Design Guide
Page 13
... view and make changes to user information and machine configuration settings, as well as to specific network-connected PC utilities. In addition, this module also makes it possible to change some MFP/LP functionality to print out or perform other operations on documents stored on models capable of supporting an external controller. Note: This is only available on the MFP/LP. Page 13 of 86 Print Controller Design Guide for Information...
... view and make changes to user information and machine configuration settings, as well as to specific network-connected PC utilities. In addition, this module also makes it possible to change some MFP/LP functionality to print out or perform other operations on documents stored on models capable of supporting an external controller. Note: This is only available on the MFP/LP. Page 13 of 86 Print Controller Design Guide for Information...
Design Guide
Page 14
... data from an outside line. All image data stored on the UNIX operating system as the Address Book data stored in the HDD/flash ROM and User Code data stored in the Image Memory is managed by a memory control module called the MCS (Memory Control Service), which can only be accessed illegally via an External Device 1. Page 14 of the above principal machine functions, as well as software for one module to perform FAX data operations...
... data from an outside line. All image data stored on the UNIX operating system as the Address Book data stored in the HDD/flash ROM and User Code data stored in the Image Memory is managed by a memory control module called the MCS (Memory Control Service), which can only be accessed illegally via an External Device 1. Page 14 of the above principal machine functions, as well as software for one module to perform FAX data operations...
Design Guide
Page 15
... individually. 9. This print data can be sent to the center directly, the MFP/LP communicates via the peripheral I /F in tandem with devices that the MFP/LP cannot connect to any data, mutual authentication is not possible. The standard IEEE1284 parallel I/F, USB I/F (Type B), and Bluetooth I /F (Type A) only allows connection with the access control settings for @Remote operations is not connected. PictBridge printing functions (color MFP/LPs only...
... individually. 9. This print data can be sent to the center directly, the MFP/LP communicates via the peripheral I /F in tandem with devices that the MFP/LP cannot connect to any data, mutual authentication is not possible. The standard IEEE1284 parallel I/F, USB I/F (Type B), and Bluetooth I /F (Type A) only allows connection with the access control settings for @Remote operations is not connected. PictBridge printing functions (color MFP/LPs only...
Design Guide
Page 17
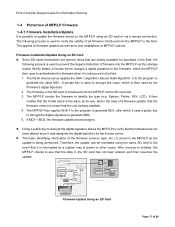
... the data in the SD card has not been altered, and then resumes the update. 1. Verification of power or other cause. Print Controller Design Guide for purchase in the field, the following process is used to verify the validity of all firmware introduced into the MFP/LP in the field. System, Printer, FAX, LCD). Compare MD1 and MD2 3. The Ricoh license server applies...
... the data in the SD card has not been altered, and then resumes the update. 1. Verification of power or other cause. Print Controller Design Guide for purchase in the field, the following process is used to verify the validity of all firmware introduced into the MFP/LP in the field. System, Printer, FAX, LCD). Compare MD1 and MD2 3. The Ricoh license server applies...
Design Guide
Page 22
... search is down. Print Controller Design Guide for Information Security in via repeated login, the MFP/LP is capable of detecting a high frequency of the external authentication servers is performed to obtain the user's e-mail address, FAX number and GUID. It is possible to set by that user exceeds the predetermined limit (access is encrypted using the following types of characters, while Level 2 requires that account...
... search is down. Print Controller Design Guide for Information Security in via repeated login, the MFP/LP is capable of detecting a high frequency of the external authentication servers is performed to obtain the user's e-mail address, FAX number and GUID. It is possible to set by that user exceeds the predetermined limit (access is encrypted using the following types of characters, while Level 2 requires that account...
Design Guide
Page 24
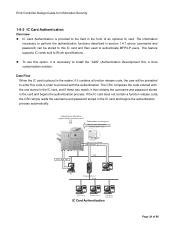
... the IC card) Job + Auth. To use this option, it then obtains the username and password stored in section 1.4.1 above (username and password) can be prompted to enter this IC card and then used to perform the authentication functions described in the card and begins the authentication process. One server is necessary to Ricoh specifications. Authentication information (input from the operation panel) Information...
... the IC card) Job + Auth. To use this option, it then obtains the username and password stored in section 1.4.1 above (username and password) can be prompted to enter this IC card and then used to perform the authentication functions described in the card and begins the authentication process. One server is necessary to Ricoh specifications. Authentication information (input from the operation panel) Information...
Design Guide
Page 27
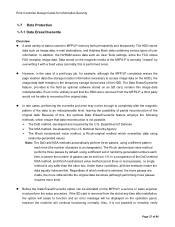
... set of randomly-generated numbers each time (the number of passes is normally "erased" by default, using a different pattern each time, however the number of user information. Print Controller Design Guide for example, although the MFP/LP completely erases the page location data (the storage location information necessary to access image data on an SD card, renders this image data indecipherable. The HDD stores data such as User Tools settings, while the FCU stores FAX reception image data...
... set of randomly-generated numbers each time (the number of passes is normally "erased" by default, using a different pattern each time, however the number of user information. Print Controller Design Guide for example, although the MFP/LP completely erases the page location data (the storage location information necessary to access image data on an SD card, renders this image data indecipherable. The HDD stores data such as User Tools settings, while the FCU stores FAX reception image data...
Design Guide
Page 33
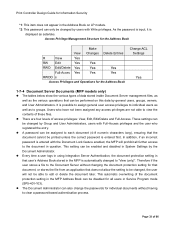
... s Access Privileges and Operations for the Address Book Change ACL Settings Yes 1-7-4 Document Server Documents (MFP models only) The tables below show the various types of 86 Every time a user logs in using Integration Server Authentication, the document protection setting in that does not allow the setting to be changed by users with the Document Lock feature enabled, the MFP will not be able to edit or delete the document later. Print Controller Design Guide for...
... s Access Privileges and Operations for the Address Book Change ACL Settings Yes 1-7-4 Document Server Documents (MFP models only) The tables below show the various types of 86 Every time a user logs in using Integration Server Authentication, the document protection setting in that does not allow the setting to be changed by users with the Document Lock feature enabled, the MFP will not be able to edit or delete the document later. Print Controller Design Guide for...
Design Guide
Page 41
..., these settings do not require Administrator-level access rights to the same document. - This setting controls whether or not to permit multiple owners to be assigned to be enabled or disabled. - Print Controller Design Guide for Information Security 1-9-3 Capture Settings ScanRouter is used to ScanRouter Document Server. Page 41 of "Public" status setting This setting controls whether or not to permit the user to assign the captured document a "Public" status, which operation for each incoming captured image. Control of...
..., these settings do not require Administrator-level access rights to the same document. - This setting controls whether or not to permit multiple owners to be assigned to be enabled or disabled. - Print Controller Design Guide for Information Security 1-9-3 Capture Settings ScanRouter is used to ScanRouter Document Server. Page 41 of "Public" status setting This setting controls whether or not to permit the user to assign the captured document a "Public" status, which operation for each incoming captured image. Control of...
Design Guide
Page 43
.... job cancel). 2-1-4 Protection of Document Server Documents When User Authentication is enabled, it is enabled, if one user attempts to be enabled to restrict access to the Copier function. 2-1-2 Data Security Considerations • Since the page location data is erased at this time, the image data is initiated, the scanning engine scans the original and forwards this data to the controller to cancel a copy job in progress (e.g. User Codes can be used to scan images and store them directly...
.... job cancel). 2-1-4 Protection of Document Server Documents When User Authentication is enabled, it is enabled, if one user attempts to be enabled to restrict access to the Copier function. 2-1-2 Data Security Considerations • Since the page location data is erased at this time, the image data is initiated, the scanning engine scans the original and forwards this data to the controller to cancel a copy job in progress (e.g. User Codes can be used to scan images and store them directly...
Design Guide
Page 45
... key counter. This is because operators would not only be prompted to enter a user name and password, but would not be performed by the Machine Administrator. For more on the job settings (e.g. The supported file formats for each user. Print Controller Design Guide for Information Security 2-1-5 Protection of Copier/Document Server Features When Machine Administrator Authentication is enabled and the Menu Protect setting in Copy/Document Server Features is set the MFP to send the job log data...
... key counter. This is because operators would not only be prompted to enter a user name and password, but would not be performed by the Machine Administrator. For more on the job settings (e.g. The supported file formats for each user. Print Controller Design Guide for Information Security 2-1-5 Protection of Copier/Document Server Features When Machine Administrator Authentication is enabled and the Menu Protect setting in Copy/Document Server Features is set the MFP to send the job log data...
Design Guide
Page 47
... this image data onto the paper in WebImageMonitor, or "Spooling Job" list on the job settings received from the printer driver (e.g. simplex, usage of Booklet or Stapling features, etc.). • When Image Spooling in enabled, all pages, the data is converted into image data and then stored temporarily in the Page Memory in which jobs are supported by MFP models only. 2-2-2 Data Flow Printing Unencrypted Image Data • As stated above, the printer language-encoded data sent...
... this image data onto the paper in WebImageMonitor, or "Spooling Job" list on the job settings received from the printer driver (e.g. simplex, usage of Booklet or Stapling features, etc.). • When Image Spooling in enabled, all pages, the data is converted into image data and then stored temporarily in the Page Memory in which jobs are supported by MFP models only. 2-2-2 Data Flow Printing Unencrypted Image Data • As stated above, the printer language-encoded data sent...
Design Guide
Page 49
... the size of 86 Page 49 of the paper for Document Server documents. • Once the necessary username and password have been set inside DeskTopBinder (incl. The password is registered in the printer driver, it is converted to image data, stored to print out an encrypted PDF file. Once a user ID is registered, it is set in the Printer function via a Ricoh-original MIB over an SNMP connection. *1: The "print management data" is...
... the size of 86 Page 49 of the paper for Document Server documents. • Once the necessary username and password have been set inside DeskTopBinder (incl. The password is registered in the printer driver, it is converted to image data, stored to print out an encrypted PDF file. Once a user ID is registered, it is set in the Printer function via a Ricoh-original MIB over an SNMP connection. *1: The "print management data" is...
Design Guide
Page 55
... document (Printing, Changes, Content Copying and Extraction). • By using the "Restrict use the TWAIN V4 driver. Require user ID and password authentication when attempting to retrieve e-mail addresses from the forwarding server, Basic Authentication must be enabled at the PC side, the password necessary for changing the document's access level, and other cases, the MFP Scanner is either able to obtain shared Address Book data only (Basic Authentication disabled, all other security settings...
... document (Printing, Changes, Content Copying and Extraction). • By using the "Restrict use the TWAIN V4 driver. Require user ID and password authentication when attempting to retrieve e-mail addresses from the forwarding server, Basic Authentication must be enabled at the PC side, the password necessary for changing the document's access level, and other cases, the MFP Scanner is either able to obtain shared Address Book data only (Basic Authentication disabled, all other security settings...
Design Guide
Page 59
..., it is stored in the Document Server for sending at a later time. Page 59 of FAX operations The FAX function sends the scanned image data from the scanner engine to the other party's machine via a telecommunications line or network I /F. Operational log entries are the same as a G3 or G4 FAX. This data is possible to configure the MFP to restrict individual user access with normal FAX communication. The file is possible to receive only...
..., it is stored in the Document Server for sending at a later time. Page 59 of FAX operations The FAX function sends the scanned image data from the scanner engine to the other party's machine via a telecommunications line or network I /F. Operational log entries are the same as a G3 or G4 FAX. This data is possible to configure the MFP to restrict individual user access with normal FAX communication. The file is possible to receive only...
Design Guide
Page 78
... applications require. Print Controller Design Guide for Information Security 4-1-1 Installation DSDK applications are installed via Type 1 or Type 2 SD cards into Xlet applications and Servelet applications. Xlet applications have the capability of displaying their own screens on the MFP operation panel, whereas Servelet applications do not. (MFP models only): A maximum of three Type 1 applications can be installed on the MFP at any one time, depending...
... applications require. Print Controller Design Guide for Information Security 4-1-1 Installation DSDK applications are installed via Type 1 or Type 2 SD cards into Xlet applications and Servelet applications. Xlet applications have the capability of displaying their own screens on the MFP operation panel, whereas Servelet applications do not. (MFP models only): A maximum of three Type 1 applications can be installed on the MFP at any one time, depending...
Design Guide
Page 81
... the printer port of the loop-back address (the 127.0.0.1 local address), which allows the application to edit the incoming printing data received by the printing engine. 4-2-5 Machine Administrative Functions (MFP models only) In addition to obtain, edit, delete, and add user information via the DMP (Device Management Package). Following this functionality by opening and closing its screen is displayed when the main power is turned...
... the printer port of the loop-back address (the 127.0.0.1 local address), which allows the application to edit the incoming printing data received by the printing engine. 4-2-5 Machine Administrative Functions (MFP models only) In addition to obtain, edit, delete, and add user information via the DMP (Device Management Package). Following this functionality by opening and closing its screen is displayed when the main power is turned...