Security Target
Page 9
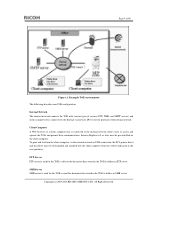
... the TOE to folders in the user guidance. To print and fax from the website indicated in SMB server. All Rights Reserved. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Page 9 of 80 Figure 1: Example TOE environment The following describes non-TOE configuration: Internal Network The internal network connects the TOE with ...computers.It is connected to the Internal via the internal network or USB connection, the PCL printer driver and fax driver must be downloaded and installed into the client computer from the client computer via firewall. Internet Explorer 6.0 or later must be pre...
... the TOE to folders in the user guidance. To print and fax from the website indicated in SMB server. All Rights Reserved. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Page 9 of 80 Figure 1: Example TOE environment The following describes non-TOE configuration: Internal Network The internal network connects the TOE with ...computers.It is connected to the Internal via the internal network or USB connection, the PCL printer driver and fax driver must be downloaded and installed into the client computer from the client computer via firewall. Internet Explorer 6.0 or later must be pre...
Security Target
Page 10
Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved. Firewall A firewall is a device that is set between the internal and the external network and protects the internal network from an external fax when the optional fax is installed. Figure 2 outlines the configuration of the following hardware (shown in the TOE to send and...
Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved. Firewall A firewall is a device that is set between the internal and the external network and protects the internal network from an external fax when the optional fax is installed. Figure 2 outlines the configuration of the following hardware (shown in the TOE to send and...
Security Target
Page 11
... key switches, LED indicators, and LCD touch screen, and the Operation Panel Control Board. The Operation Panel Control Software is installed in response to direct instructions from the MFP Control Software. The Fax Unit has an interface to instructions from the MFP Control... paper documents. All Rights Reserved. The Scanner Engine is installed in the Engine Control Board. The interface provides the MFP Control Copyright (c) 2009,2010 RICOH COMPANY, LTD. Fax Unit (optional) The Fax Unit is a device that is installed on the LCD touch screen after input informationhas been sent...
... key switches, LED indicators, and LCD touch screen, and the Operation Panel Control Board. The Operation Panel Control Software is installed in response to direct instructions from the MFP Control Software. The Fax Unit has an interface to instructions from the MFP Control... paper documents. All Rights Reserved. The Scanner Engine is installed in the Engine Control Board. The interface provides the MFP Control Copyright (c) 2009,2010 RICOH COMPANY, LTD. Fax Unit (optional) The Fax Unit is a device that is installed on the LCD touch screen after input informationhas been sent...
Security Target
Page 12
... , s/he removes this cover to connect a client computer tothe TOE, print or fax from the client computer. Copyright (c) 2009,2010 RICOH COMPANY, LTD. It is an interface board for configuring the MFP operation is stored. [Ic Key] A security chip that generates random ...of the TOE, and is also connected to activate the Stored Data Protection Function. The IcCtlr is normally covered. USB Port The USB Port is installed. [RAM] A volatile memory medium used by a customer engineers (hereafter called a "CE") for identification and authentication are descriptions of these components...
... , s/he removes this cover to connect a client computer tothe TOE, print or fax from the client computer. Copyright (c) 2009,2010 RICOH COMPANY, LTD. It is an interface board for configuring the MFP operation is stored. [Ic Key] A security chip that generates random ...of the TOE, and is also connected to activate the Stored Data Protection Function. The IcCtlr is normally covered. USB Port The USB Port is installed. [RAM] A volatile memory medium used by a customer engineers (hereafter called a "CE") for identification and authentication are descriptions of these components...
Security Target
Page 15
... manager change the supervisor ID and password of selecting the TOE administrators and TOE supervisor. Copyright (c) 2009,2010 RICOH COMPANY, LTD. When selecting administrators, the responsible manager assigns each administrator role. General users can change the settings...administration, machine administration, network administration, and/or file administration. 1.4.3.2 Administrator An "administrator" is a user who is being installed, the administrators who manages administrator passwords and changes them. One to four administrators can be registered for the TOE. When...
... manager change the supervisor ID and password of selecting the TOE administrators and TOE supervisor. Copyright (c) 2009,2010 RICOH COMPANY, LTD. When selecting administrators, the responsible manager assigns each administrator role. General users can change the settings...administration, machine administration, network administration, and/or file administration. 1.4.3.2 Administrator An "administrator" is a user who is being installed, the administrators who manages administrator passwords and changes them. One to four administrators can be registered for the TOE. When...
Security Target
Page 18
... Fax Function, or Printer Function can be updated according to manage this information depends on restriction of use this document is installed on this function by accessing the Web Service Function from their computer's Web browser. Subset of the TOE. 1.4.4.2 Security ...This function is for the stored document data will be printed. Sending document data stored in " 1.4.4.2 Security Functions". Copyright (c) 2009,2010 RICOH COMPANY, LTD. As for Management Functions, security-related functions are described later in "Security Management Function" in the D-BOX. Checking the...
... Fax Function, or Printer Function can be updated according to manage this information depends on restriction of use this document is installed on this function by accessing the Web Service Function from their computer's Web browser. Subset of the TOE. 1.4.4.2 Security ...This function is for the stored document data will be printed. Sending document data stored in " 1.4.4.2 Security Functions". Copyright (c) 2009,2010 RICOH COMPANY, LTD. As for Management Functions, security-related functions are described later in "Security Management Function" in the D-BOX. Checking the...
Security Target
Page 22
.... 4. Storing Document Data Document data stored inside the TOE is imported to the USB Port Document data is created from Copyright (c) 2009,2010 RICOH COMPANY, LTD. Sent as a fax. All Rights Reserved. Document data stored in the TOE can be either stored in the TOE or output...of 80 MFP Control Software Verification Function This function verifies the integrity of the MFP Control Software by checking the integrity of an executable code installed in the FlashROM. 1.4.5 Protected Assets This section desc ribes the protected assets of a paper original that the TOE can be detected. ...
.... 4. Storing Document Data Document data stored inside the TOE is imported to the USB Port Document data is created from Copyright (c) 2009,2010 RICOH COMPANY, LTD. Sent as a fax. All Rights Reserved. Document data stored in the TOE can be either stored in the TOE or output...of 80 MFP Control Software Verification Function This function verifies the integrity of the MFP Control Software by checking the integrity of an executable code installed in the FlashROM. 1.4.5 Protected Assets This section desc ribes the protected assets of a paper original that the TOE can be detected. ...
Security Target
Page 25
... access document data through the external TOE interfaces (the Operation Panel, network interface, or USB Port) that demand integrity of the software installed in its IT products. Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved. T.ABUSE_SEC_MNG (Abuse of Security Management Function) Persons not authorised to use and environment of this section...
... access document data through the external TOE interfaces (the Operation Panel, network interface, or USB Port) that demand integrity of the software installed in its IT products. Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved. T.ABUSE_SEC_MNG (Abuse of Security Management Function) Persons not authorised to use and environment of this section...
Security Target
Page 26
Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved. A.SUPERVISOR (Assumption for supervisor) Supervisor shall have sufficient knowledge to operate the TOE securely in the roles assigned to him/.... Additionally, administrators shall not abuse their permissions maliciously. A.NETWORK (Assumption for network connections) When the network that theTOE is connected to (the internal network) is installed in the FlashROM of the TOE. 3.3 Assumptions Defined and described below are the assumptions related to the use and environment of MFP Control Software, which...
Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved. A.SUPERVISOR (Assumption for supervisor) Supervisor shall have sufficient knowledge to operate the TOE securely in the roles assigned to him/.... Additionally, administrators shall not abuse their permissions maliciously. A.NETWORK (Assumption for network connections) When the network that theTOE is connected to (the internal network) is installed in the FlashROM of the TOE. 3.3 Assumptions Defined and described below are the assumptions related to the use and environment of MFP Control Software, which...
Security Target
Page 30
...the organisation managing operation of the internal network shall close any unnecessary ports between the external and internal networks. Copyright (c) 2009,2010 RICOH COMPANY, LTD. In addition, the TOE records the performance of O.I&A as the Internet, the internal network shall be protected from ... audit logs is a file administrator, the TOE allows the file administrator to use the functions for which the TOE is connected, is installed in the D-BOX. Page 30 of 80 A.NETWORK (Assumptions for network connections) As specified by O.MANAGE. T.ABUSE_SEC_MNG (Abuse of TSF...
...the organisation managing operation of the internal network shall close any unnecessary ports between the external and internal networks. Copyright (c) 2009,2010 RICOH COMPANY, LTD. In addition, the TOE records the performance of O.I&A as the Internet, the internal network shall be protected from ... audit logs is a file administrator, the TOE allows the file administrator to use the functions for which the TOE is connected, is installed in the D-BOX. Page 30 of 80 A.NETWORK (Assumptions for network connections) As specified by O.MANAGE. T.ABUSE_SEC_MNG (Abuse of TSF...
Security Target
Page 31
...addition, the performance of O.LINE_PROTECT is recorded as audit logs by O.AUDIT, and the function to read audit logs is installed in FlashROM, with communication path) To counter this organisational security policy, the TOE provides the function to verify the integrity of... MFP Control Softwa re, which is only provided to the TOE by O.LINE_PROTECT. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Therefore, the TOE can enforce P.SOFTWARE. Therefore, the TOE can counter T.FAX_LINE. All Rights Reserved. T.FAX_LINE (Intrusion via telephone ...
...addition, the performance of O.LINE_PROTECT is recorded as audit logs by O.AUDIT, and the function to read audit logs is installed in FlashROM, with communication path) To counter this organisational security policy, the TOE provides the function to verify the integrity of... MFP Control Softwa re, which is only provided to the TOE by O.LINE_PROTECT. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Therefore, the TOE can enforce P.SOFTWARE. Therefore, the TOE can counter T.FAX_LINE. All Rights Reserved. T.FAX_LINE (Intrusion via telephone ...
Security Target
Page 59
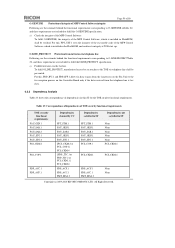
...Table 23 shows the correspondence of dependencies in this , FPT_TST.1 tests the integrity of the executable code of the MFP Control Software, which is installed in the FlashROM, and verifies its integrity at TOE start -up. For this, FDP_IFC.1 and FDP_IFF.1 allow fax data to pass from ...sec urity functional requirements. To fulfil O.GENUINE, the integrity of the MFP Control Software, which is installed in ST None None None None None FCS_CKM.4 FCS_CKM.4 None None Copyright (c) 2009,2010 RICOH COMPANY, LTD. Page 59 of 80 O.GENUINE Protection of integrity of MFP Contr ol Software integrity ...
...Table 23 shows the correspondence of dependencies in this , FPT_TST.1 tests the integrity of the executable code of the MFP Control Software, which is installed in the FlashROM, and verifies its integrity at TOE start -up. For this, FDP_IFC.1 and FDP_IFF.1 allow fax data to pass from ...sec urity functional requirements. To fulfil O.GENUINE, the integrity of the MFP Control Software, which is installed in ST None None None None None FCS_CKM.4 FCS_CKM.4 None None Copyright (c) 2009,2010 RICOH COMPANY, LTD. Page 59 of 80 O.GENUINE Protection of integrity of MFP Contr ol Software integrity ...
Security Target
Page 74
..., the TOE attaches the document data to create a trusted path. The destination information for the Deliver to Folders function is installed in " SF.NET_PROT Network Communication Data Protection Function" and their corresponding security functional requirements. 7.1.7.1 Use of Web Service Function from...server using S/MIME. Users can send e-mail referring to the registered folder information only. All Rights Reserved. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Users can send files referring to the registered destination details only. By the above , FTP_ITC.1 (Inter-TSF ...
..., the TOE attaches the document data to create a trusted path. The destination information for the Deliver to Folders function is installed in " SF.NET_PROT Network Communication Data Protection Function" and their corresponding security functional requirements. 7.1.7.1 Use of Web Service Function from...server using S/MIME. Users can send e-mail referring to the registered folder information only. All Rights Reserved. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Users can send files referring to the registered destination details only. By the above , FTP_ITC.1 (Inter-TSF ...
Security Target
Page 76
... in this ST. A function that sends and receives document files between two faxes that are used, or a person in charge of an IT department.) Software installed in th e TOE that can also send document files to a fax that comprise the MFP and controls their operation. Manages the resources for digital "multi.... In this ST, "MFP" also refers to the TOE A person in an organisation in which MFPs are used and who has authority to the HDD installed in the TOE. Copyright (c) 2009,2010 RICOH COMPANY, LTD.
... in this ST. A function that sends and receives document files between two faxes that are used, or a person in charge of an IT department.) Software installed in th e TOE that can also send document files to a fax that comprise the MFP and controls their operation. Manages the resources for digital "multi.... In this ST, "MFP" also refers to the TOE A person in an organisation in which MFPs are used and who has authority to the HDD installed in the TOE. Copyright (c) 2009,2010 RICOH COMPANY, LTD.
Security Target
Page 78
...information and an identification code for the Locked-out user to be printed or faxed. Generally indicates the Internet. Copyright (c) 2009,2010 RICOH COMPANY, LTD. When this setting is inactive, Lockout can be registered, and each authorised user. Page 78 of 80 Terms Number ...of Attempts before the user is locked out. A function that can be installed in the client computer in a client computer that are given administrator roles and perform administrative operations accordingly. One of general users. Print...
...information and an identification code for the Locked-out user to be printed or faxed. Generally indicates the Internet. Copyright (c) 2009,2010 RICOH COMPANY, LTD. When this setting is inactive, Lockout can be registered, and each authorised user. Page 78 of 80 Terms Number ...of Attempts before the user is locked out. A function that can be installed in the client computer in a client computer that are given administrator roles and perform administrative operations accordingly. One of general users. Print...