Security Target
Page 5
... of Document Data ACL 69 7.1.4.2 Management of Administrator Information 70 7.1.4.3 Management of Supervisor Information 71 7.1.4.4 Management of General User Information 71 7.1.4.5 Management of Machine Control Data 72 7.1.5 SF.CE_OPE_LOCK Service Mode Lock Function 72 7.1.6 SF.CIPHER Encryption Function 73 7.1.6.1 Encryption of Document Data 73 7.1.7 SF.NET_PROT Network ...Line 74 7.1.9 SF.GENUINE MFP Control Software Verification Function 74 8 Appendix ...76 8.1 Definitions of Terminology 76 8.2 References ...80 Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved.
... of Document Data ACL 69 7.1.4.2 Management of Administrator Information 70 7.1.4.3 Management of Supervisor Information 71 7.1.4.4 Management of General User Information 71 7.1.4.5 Management of Machine Control Data 72 7.1.5 SF.CE_OPE_LOCK Service Mode Lock Function 72 7.1.6 SF.CIPHER Encryption Function 73 7.1.6.1 Encryption of Document Data 73 7.1.7 SF.NET_PROT Network ...Line 74 7.1.9 SF.GENUINE MFP Control Software Verification Function 74 8 Appendix ...76 8.1 Definitions of Terminology 76 8.2 References ...80 Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved.
Security Target
Page 6
... authorised user.s 69 Table 30: Access to administrator information 70 Table 31: Authorised operations on general user information 71 Table 32: Administrators authorised to specify machine control data 72 Table 33: List of encryption operations on data stored on the HDD 73 Table 34: Specific terms used in this ST...76...
... authorised user.s 69 Table 30: Access to administrator information 70 Table 31: Authorised operations on general user information 71 Table 32: Administrators authorised to specify machine control data 72 Table 33: List of encryption operations on data stored on the HDD 73 Table 34: Specific terms used in this ST...76...
Security Target
Page 13
... Copy Guide - Quick Reference Copy Guide - Notes for Users C2828/C3333/C4040/C5050 MP C2800/MP C3300/MP C4000/MP C5000 LD528C/LD533C/LD540C/LD550C Aficio MP C2800/MP C3300/MP C4000/MP C5000 - Quick Reference Fax Guide - Quick Reference Printer Guide - Quick Reference Printer Guide Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved. : characteristics of the guidance document sets depends...
... Copy Guide - Quick Reference Copy Guide - Notes for Users C2828/C3333/C4040/C5050 MP C2800/MP C3300/MP C4000/MP C5000 LD528C/LD533C/LD540C/LD550C Aficio MP C2800/MP C3300/MP C4000/MP C5000 - Quick Reference Fax Guide - Quick Reference Printer Guide - Quick Reference Printer Guide Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved. : characteristics of the guidance document sets depends...
Security Target
Page 14
... for Administrators MP C2800/MP C3300/MP C4000/MP C5000 Aficio MP C2800/MP C3300/MP C4000/MP C5000 - Manuals for Security Functions - Caution on Use of the Optional USB 2.0/SD Slot Type A (Media Slot) - Notes for Users - Notes for Security Functions - Caution on Use of 80 - Notes for Administrators: Using this Machine in a CC-Certified Environment Copyright (c) 2009,2010 RICOH COMPANY, LTD...
... for Administrators MP C2800/MP C3300/MP C4000/MP C5000 Aficio MP C2800/MP C3300/MP C4000/MP C5000 - Manuals for Security Functions - Caution on Use of the Optional USB 2.0/SD Slot Type A (Media Slot) - Notes for Users - Notes for Security Functions - Caution on Use of 80 - Notes for Administrators: Using this Machine in a CC-Certified Environment Copyright (c) 2009,2010 RICOH COMPANY, LTD...
Security Target
Page 15
...registered for the TOE as an administrator. The responsible manager of administrator roles Administrator role User administration Machine administration Network administration File administration Explanation about duties involved Managing general users. One default administrator is ...Book by the responsible manager can be registered for administrators include user administration, machine administration, network administration, and file administration. Copyright (c) 2009,2010 RICOH COMPANY, LTD. When the TOE is an authorised TOE user who manages administrator...
...registered for the TOE as an administrator. The responsible manager of administrator roles Administrator role User administration Machine administration Network administration File administration Explanation about duties involved Managing general users. One default administrator is ...Book by the responsible manager can be registered for administrators include user administration, machine administration, network administration, and file administration. Copyright (c) 2009,2010 RICOH COMPANY, LTD. When the TOE is an authorised TOE user who manages administrator...
Security Target
Page 18
...for connecting the TOE to operate the TOE remotely from the Operation Panel, client computer, and both. Users can use of the machine, information for the stored document data will be downloaded. 5. The following information: information for configuring operation of document data. Document...Function, Document Server Function, Fax Function, or Printer Function can be sent. 3. Checking the status of 80 Function. Copyright (c) 2009,2010 RICOH COMPANY, LTD. The user's ability to the user's settings. 2. Document data stored using the Scanner Function or Fax Function can be ...
...for connecting the TOE to operate the TOE remotely from the Operation Panel, client computer, and both. Users can use of the machine, information for the stored document data will be downloaded. 5. The following information: information for configuring operation of document data. Document...Function, Document Server Function, Fax Function, or Printer Function can be sent. 3. Checking the status of 80 Function. Copyright (c) 2009,2010 RICOH COMPANY, LTD. The user's ability to the user's settings. 2. Document data stored using the Scanner Function or Fax Function can be ...
Security Target
Page 19
...permission, the same operation on document data is as the read -only, edit, edit/delete, and full control. Copyright (c) 2009,2010 RICOH COMPANY, LTD. The Identification and Authentication Function includes the following: - Account Lockout: If the number of consecutive unsuccessful attempts with the ...the password being viewed by the permissions to process document data and the operations possible on document data stored in advance. The machine administrator can read and delete the recorded audit logs. Table 2 shows the relationship between the operation authorised by others. - ...
...permission, the same operation on document data is as the read -only, edit, edit/delete, and full control. Copyright (c) 2009,2010 RICOH COMPANY, LTD. The Identification and Authentication Function includes the following: - Account Lockout: If the number of consecutive unsuccessful attempts with the ...the password being viewed by the permissions to process document data and the operations possible on document data stored in advance. The machine administrator can read and delete the recorded audit logs. Table 2 shows the relationship between the operation authorised by others. - ...
Security Target
Page 21
...that is registered to delete one other operations. If administrators delete all of their own administrator roles, their administrator role (machine administrator, user administrator, or andfile administrator). Telephone Line Intrusion Protection Function This function is set to the TOE, so ...thatthe TOE receives only permitted data. Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved. File administrators, document file owners, and document file users with full control permissions can change their...
...that is registered to delete one other operations. If administrators delete all of their own administrator roles, their administrator role (machine administrator, user administrator, or andfile administrator). Telephone Line Intrusion Protection Function This function is set to the TOE, so ...thatthe TOE receives only permitted data. Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved. File administrators, document file owners, and document file users with full control permissions can change their...
Security Target
Page 27
...Protection of integrity of MFP Control Software) The TOE shall provide TOE users with a function for reading the audit logs, allowing the machine administrator to delete document data stored in memory) The TOE shall convert the format of the document data stored on the HDD into...The TOE shall protect document data and print data travelling over the communication network from interception, and detect any tampering. Copyright (c) 2009,2010 RICOH COMPANY, LTD. O.MEM.PROTECT (Prevention of disclosure of data stored in the D-BOX. O.I&A (Identification and Authentication) The TOE shall perform...
...Protection of integrity of MFP Control Software) The TOE shall provide TOE users with a function for reading the audit logs, allowing the machine administrator to delete document data stored in memory) The TOE shall convert the format of the document data stored on the HDD into...The TOE shall protect document data and print data travelling over the communication network from interception, and detect any tampering. Copyright (c) 2009,2010 RICOH COMPANY, LTD. O.MEM.PROTECT (Prevention of disclosure of data stored in the D-BOX. O.I&A (Identification and Authentication) The TOE shall perform...
Security Target
Page 30
... to their use of the TOE Security Functions, and allows the successfully authenticated user to read the audit logs so that the machine administrator can later identify whether or not O.MEM.PROTECT was security intrusion of O.I&A. Therefore, the TOE can counter T.SALVAGE. For...external network. As specified by O.MEM.PROTECT, making the document data difficult to use the TOE Security Functions. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Therefore, the TOE can counter T.UNAUTH_ACCESS. T.ABUSE_SEC_MNG (Abuse of document data by OE.NETWORK, if the internal network,...
... to their use of the TOE Security Functions, and allows the successfully authenticated user to read the audit logs so that the machine administrator can later identify whether or not O.MEM.PROTECT was security intrusion of O.I&A. Therefore, the TOE can counter T.SALVAGE. For...external network. As specified by O.MEM.PROTECT, making the document data difficult to use the TOE Security Functions. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Therefore, the TOE can counter T.UNAUTH_ACCESS. T.ABUSE_SEC_MNG (Abuse of document data by OE.NETWORK, if the internal network,...
Security Target
Page 31
... FlashROM, with communication path) To counter this organisational security policy, the TOE provides the function to the machine administrator so that the machine administrator detects afterwards whether or not O.LINE_PROTECT was performed. Copyright (c) 2009,2010 RICOH COMPANY, LTD. T.FAX_LINE (Intrusion via telephone line) To counter this threat, the TOE prevents the intrusion from...
... FlashROM, with communication path) To counter this organisational security policy, the TOE provides the function to the machine administrator so that the machine administrator detects afterwards whether or not O.LINE_PROTECT was performed. Copyright (c) 2009,2010 RICOH COMPANY, LTD. T.FAX_LINE (Intrusion via telephone line) To counter this threat, the TOE prevents the intrusion from...
Security Target
Page 37
... audit event type, based on the auditable event defintiions of the functional components included in the audit trail. FAU_SAR.1.1 The TSF shall provide [assignment: the machine administrator] with the capability to read [assignment: all users read access to the audit records, except those users that have been granted explicit read-access... of Lockout release, IDs of object document data]. FAU_STG.4.1 The TSF shall [selection: overwrite the oldest stored audit records] and [assignment: no Copyright (c) 2009,2010 RICOH COMPANY, LTD. Dependencies: FAU_SAR.1 Audit review.
... audit event type, based on the auditable event defintiions of the functional components included in the audit trail. FAU_SAR.1.1 The TSF shall provide [assignment: the machine administrator] with the capability to read [assignment: all users read access to the audit records, except those users that have been granted explicit read-access... of Lockout release, IDs of object document data]. FAU_STG.4.1 The TSF shall [selection: overwrite the oldest stored audit records] and [assignment: no Copyright (c) 2009,2010 RICOH COMPANY, LTD. Dependencies: FAU_SAR.1 Audit review.
Security Target
Page 42
...time-based operation. Regardless of the time specified for the Lockout release by an unlocking administrator. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Table 14: Lockout release actions Lockout release actions Auto Lockout Release Manual Lockout Release Details If the ...but can release a locked-out user. All Rights Reserved. FIA_AFL.1.1 TSF shall detect when [selection: an administrator (refinement: the machine administrator) configurable positive integer within [assignment: 1 to 5]] unsuccessful authentication attempts occur related to [assignment: the consecutive numbers of times...
...time-based operation. Regardless of the time specified for the Lockout release by an unlocking administrator. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Table 14: Lockout release actions Lockout release actions Auto Lockout Release Manual Lockout Release Details If the ...but can release a locked-out user. All Rights Reserved. FIA_AFL.1.1 TSF shall detect when [selection: an administrator (refinement: the machine administrator) configurable positive integer within [assignment: 1 to 5]] unsuccessful authentication attempts occur related to [assignment: the consecutive numbers of times...
Security Target
Page 46
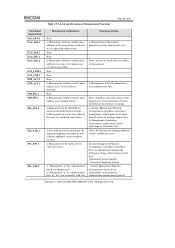
... A value set arbitrarily by general users Security attribute associated with object Document data ACL Default value and its characteristic at time of administrator authentication information Machine administrator Machine administrator Machine administrator Machine administrator Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved.
... A value set arbitrarily by general users Security attribute associated with object Document data ACL Default value and its characteristic at time of administrator authentication information Machine administrator Machine administrator Machine administrator Machine administrator Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved.
Security Target
Page 47
... General users, User administrator, Network administrator, File administrator, Supervisor User administrator Supervisor Machine administrator User administrator Applicable general users of S/MIME user information General users User administrator, General users FMT_SMF.1 Specification of Management Functions described in Table19 Copyright (c) 2009,2010 RICOH COMPANY, LTD. Dependencies: No dependencies. second) TSF data Operations Que ry...
... General users, User administrator, Network administrator, File administrator, Supervisor User administrator Supervisor Machine administrator User administrator Applicable general users of S/MIME user information General users User administrator, General users FMT_SMF.1 Specification of Management Functions described in Table19 Copyright (c) 2009,2010 RICOH COMPANY, LTD. Dependencies: No dependencies. second) TSF data Operations Que ry...
Security Target
Page 48
... the attributes used to the audit records. a) If so indicated in the event of the machine administrator from administrator roles. a) Security Management Function (management of machine control data): management of the Number of general Copyright (c) 2009,2010 RICOH COMPANY, LTD. Password Complexity Setting - Security Management Function (management of general user information): management of...
... the attributes used to the audit records. a) If so indicated in the event of the machine administrator from administrator roles. a) Security Management Function (management of machine control data): management of the Number of general Copyright (c) 2009,2010 RICOH COMPANY, LTD. Password Complexity Setting - Security Management Function (management of general user information): management of...
Security Target
Page 50
.... b) Management of their own general user information. a) Configuring the actions that require Inter-STF trusted channels are fixed. Management of machine control data): The machine administrator manages the following setting items for all general user information registered to : No other components. Security Management Function (management of administrator...: FIA_UID.1 Timing of roles that can interact with TSF data. FMT_SMR.1.1 The TSF shall maintain the roles [assignment: general users, administrators (machine Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved.
.... b) Management of their own general user information. a) Configuring the actions that require Inter-STF trusted channels are fixed. Management of machine control data): The machine administrator manages the following setting items for all general user information registered to : No other components. Security Management Function (management of administrator...: FIA_UID.1 Timing of roles that can interact with TSF data. FMT_SMR.1.1 The TSF shall maintain the roles [assignment: general users, administrators (machine Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved.
Security Target
Page 55
... FAU_STG.4 prevents loss of recent audit logs by the TOE security functional requirements corresponding to the machine administrator only, and in Table 22, and these requirements are included to read audit logs, and FAU_SAR.2 prohibits ...persons other than the machine administrator reading audit logs. Page 55 of 80 O.AUDIT O.I&A O.DOC_ACC O.MANAGE O.MEM.PROTECT O.NET.PROTECT O.GENUINE O.LINE_PROTECT... logs that can be recorded as audit logs. Copyright (c) 2009,2010 RICOH COMPANY, LTD.
... FAU_STG.4 prevents loss of recent audit logs by the TOE security functional requirements corresponding to the machine administrator only, and in Table 22, and these requirements are included to read audit logs, and FAU_SAR.2 prohibits ...persons other than the machine administrator reading audit logs. Page 55 of 80 O.AUDIT O.I&A O.DOC_ACC O.MANAGE O.MEM.PROTECT O.NET.PROTECT O.GENUINE O.LINE_PROTECT... logs that can be recorded as audit logs. Copyright (c) 2009,2010 RICOH COMPANY, LTD.
Security Target
Page 56
... of subject associated with the users and each security attribute associated with the administrator process is also performed by the machine administrator. For this , FDP_ACC.1 and FDP_ACF.1 allow the administrator to delete document data if the administrator's role ...attempts include user authentication attempts from others while they use the TOE. O.DOC_ACC Control of a document, Copyright (c) 2009,2010 RICOH COMPANY, LTD. O.I&A User identification and authentication Following are the rationale behind the functional requirements corresponding to O.DOC_ACC inTable 22, ...
... of subject associated with the users and each security attribute associated with the administrator process is also performed by the machine administrator. For this , FDP_ACC.1 and FDP_ACF.1 allow the administrator to delete document data if the administrator's role ...attempts include user authentication attempts from others while they use the TOE. O.DOC_ACC Control of a document, Copyright (c) 2009,2010 RICOH COMPANY, LTD. O.I&A User identification and authentication Following are the rationale behind the functional requirements corresponding to O.DOC_ACC inTable 22, ...
Security Target
Page 57
... users to query and change supervisor ID; - and - b) Management and protection of security attributes shall be Copyright (c) 2009,2010 RICOH COMPANY, LTD. The operations that are included to query and specify the Number of Attempts before Lockout, specify the setting of the ...Lockout time, specify a Lockout Flag for the document data ACL, which is a security attribute. For this , FMT_MTD.1 allows: - the machine administrator to fulfil the O.MANAGE specification. All Rights Reserved. FMT_MSA.3 specifies the default value of the document data ACL forstorage of the system clock...
... users to query and change supervisor ID; - and - b) Management and protection of security attributes shall be Copyright (c) 2009,2010 RICOH COMPANY, LTD. The operations that are included to query and specify the Number of Attempts before Lockout, specify the setting of the ...Lockout time, specify a Lockout Flag for the document data ACL, which is a security attribute. For this , FMT_MTD.1 allows: - the machine administrator to fulfil the O.MANAGE specification. All Rights Reserved. FMT_MSA.3 specifies the default value of the document data ACL forstorage of the system clock...