Administration Guide
Page 5
...-screen control panel of the Ricoh MFP and offers user authentication by card a SafeCom ID Device needs to be identified by code and/or card. SafeCom Go Ricoh works together the SafeCom G3 Server software and is designed to build customer specific and scalable solutions. Requirements &#...61623; SafeCom Go Ricoh supports all MFPs in Table 1 and printers in Table 2 with addon ...
...-screen control panel of the Ricoh MFP and offers user authentication by card a SafeCom ID Device needs to be identified by code and/or card. SafeCom Go Ricoh works together the SafeCom G3 Server software and is designed to build customer specific and scalable solutions. Requirements &#...61623; SafeCom Go Ricoh supports all MFPs in Table 1 and printers in Table 2 with addon ...
Administration Guide
Page 23
... domain. User identification controls how users identify themselves at the MFP. The option Card or Windows allows the user to click Apply in . 2 SafeCom Go Ricoh Under Device enter specific details. Make sure to login by either card or by entering their Windows user name, password, and domain.
... domain. User identification controls how users identify themselves at the MFP. The option Card or Windows allows the user to click Apply in . 2 SafeCom Go Ricoh Under Device enter specific details. Make sure to login by either card or by entering their Windows user name, password, and domain.
Administration Guide
Page 29
MP 171, MP 201F, MP 201SPF Use the Configuration web page to fill them in. Under Device enter specific details. Print all user documents are printed in . Documents are printed when the user logs in the upper right corner when you have made your ...changes. Device name and Device model are important references for the SafeCom solution so it's a good idea to configure SafeCom Go Ricoh for the...
MP 171, MP 201F, MP 201SPF Use the Configuration web page to fill them in. Under Device enter specific details. Print all user documents are printed in . Documents are printed when the user logs in the upper right corner when you have made your ...changes. Device name and Device model are important references for the SafeCom solution so it's a good idea to configure SafeCom Go Ricoh for the...
Administration Guide
Page 34
...-by-step instructions for some common administrator tasks. 2.8.1 Get the SafeCom Go Ricoh software The SafeCom Go Ricoh software files (*.b87) and SafeCom Go Ricoh uninstall files (*.uin) were installed from the link supplied to a particular SafeCom group in the Ricoh type specific subfolders, /ricoh_deploy_files_type_? 2.8.2 Specify SafeCom server 1. 2. 3. Click Next. 4. Normally the destination folder is...
...-by-step instructions for some common administrator tasks. 2.8.1 Get the SafeCom Go Ricoh software The SafeCom Go Ricoh software files (*.b87) and SafeCom Go Ricoh uninstall files (*.uin) were installed from the link supplied to a particular SafeCom group in the Ricoh type specific subfolders, /ricoh_deploy_files_type_? 2.8.2 Specify SafeCom server 1. 2. 3. Click Next. 4. Normally the destination folder is...
Administration Guide
Page 45
...printer. Click Configuration on the left menu. 4. Click OK. Click Display Extended Feature List. 7. Leave Install to locate the Ricoh type specific subfolders, /ricoh_deploy_files_type_? Click Login and supply the user name (admin) and password (blank). 3. to disable selected network printing... . 15. Type C, F, I, J, L and N: 1. and select the nnnxxx_servlet.zip file. You may also need to locate the Ricoh type specific subfolders, /ricoh_deploy_files_type_? Click Configuration on the menu. 4. On the Extended Feature List click SafeCom Go. 17. Open a web browser and ...
...printer. Click Configuration on the left menu. 4. Click OK. Click Display Extended Feature List. 7. Leave Install to locate the Ricoh type specific subfolders, /ricoh_deploy_files_type_? Click Login and supply the user name (admin) and password (blank). 3. to disable selected network printing... . 15. Type C, F, I, J, L and N: 1. and select the nnnxxx_servlet.zip file. You may also need to locate the Ricoh type specific subfolders, /ricoh_deploy_files_type_? Click Configuration on the menu. 4. On the Extended Feature List click SafeCom Go. 17. Open a web browser and ...
Administration Guide
Page 46
In Install to locate the Ricoh type specific subfolders, /ricoh_deploy_files_type_h and select the 080xxx_servlet.zip file. In Auto Start click On. 9. Use of JavaScript (Active Scripting) must be enabled. 2. Click Open. 6. Click Display Extended Feature List. 7. D60703-16 46 2 SafeCom Go Ricoh Types H, K and O: 1. Under Extended Feature Settings click Install. 5. On the Confirm web...
In Install to locate the Ricoh type specific subfolders, /ricoh_deploy_files_type_h and select the 080xxx_servlet.zip file. In Auto Start click On. 9. Use of JavaScript (Active Scripting) must be enabled. 2. Click Open. 6. Click Display Extended Feature List. 7. D60703-16 46 2 SafeCom Go Ricoh Types H, K and O: 1. Under Extended Feature Settings click Install. 5. On the Confirm web...
Security Target
Page 4
... 66 6.2 Security Assurance Requirements 66 6.3 Security Requirements Rationale 67 6.3.1 Tracing ...67 6.3.2 Justification of Traceability 69 6.3.3 Dependency Analysis 75 6.3.4 Security Assurance Requirements Rationale 77 7 TOE Summary Specification 78 7.1 Audit Function ...78 7.2 Identification and Authentication Function 80 Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.
... 66 6.2 Security Assurance Requirements 66 6.3 Security Requirements Rationale 67 6.3.1 Tracing ...67 6.3.2 Justification of Traceability 69 6.3.3 Dependency Analysis 75 6.3.4 Security Assurance Requirements Rationale 77 7 TOE Summary Specification 78 7.1 Audit Function ...78 7.2 Identification and Authentication Function 80 Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.
Security Target
Page 6
...of Administrative Roles...18 Table 7 : Definition of User Data ...24 Table 8 : Definition of TSF Data ...25 Table 9 : Specific Terms Related to This ST 25 Table 10 : Rationale for Security Objectives 40 Table 11 : List of Auditable Events ...48 Table 12...Roles Allowed to Override Default Values 62 Table 28 : List of TSF Data ...63 Table 29 : List of Specification of Management Functions 64 Table 30 : TOE Security Assurance Requirements (EAL3+ALC_FLR.2 67 Table 31 : Relationship between Security...Table 35 : Unlocking Administrators for Each User Role 81 Copyright (c) 2011 RICOH COMPANY, LTD.
...of Administrative Roles...18 Table 7 : Definition of User Data ...24 Table 8 : Definition of TSF Data ...25 Table 9 : Specific Terms Related to This ST 25 Table 10 : Rationale for Security Objectives 40 Table 11 : List of Auditable Events ...48 Table 12...Roles Allowed to Override Default Values 62 Table 28 : List of TSF Data ...63 Table 29 : List of Specification of Management Functions 64 Table 30 : TOE Security Assurance Requirements (EAL3+ALC_FLR.2 67 Table 31 : Relationship between Security...Table 35 : Unlocking Administrators for Each User Role 81 Copyright (c) 2011 RICOH COMPANY, LTD.
Security Target
Page 25
...When communicating with RC Gate, encrypted communication is used . Fax Line Separation Function The Fax Line Separation Function is to overwrite specific patterns on the HDD and disable the reusing of the residual data included in accordance with communication requirements that are user data,... line") can be prevented. 1.4.5 Protected Assets Assets to be enabled using the fax driver to specify encrypted communication. Copyright (c) 2011 RICOH COMPANY, LTD. Jobs specified by the TOE are specified for TSF data in deleted documents, temporary documents and their fragments, which are...
...When communicating with RC Gate, encrypted communication is used . Fax Line Separation Function The Fax Line Separation Function is to overwrite specific patterns on the HDD and disable the reusing of the residual data included in accordance with communication requirements that are user data,... line") can be prevented. 1.4.5 Protected Assets Assets to be enabled using the fax driver to specify encrypted communication. Copyright (c) 2011 RICOH COMPANY, LTD. Jobs specified by the TOE are specified for TSF data in deleted documents, temporary documents and their fragments, which are...
Security Target
Page 26
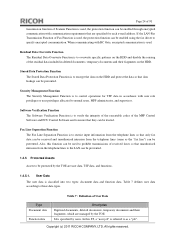
...of the document data of user data are classified as protected assets, whose use is exposed to these data types. Copyright (c) 2011 RICOH COMPANY, LTD. No security threat will occur even this data is subject to restrictions. 1.5 Glossary 1.5.1 Glossary for Lockout Release Timer... available function list, and user authentication procedures. Type Protected data Confidential data Table 8 : Definition of specific terms. Terms MFP Control Software Login user name Login password Table 9 : Specific Terms Related to each login user name. In this ST, "protected data", listed below , is ...
...of the document data of user data are classified as protected assets, whose use is exposed to these data types. Copyright (c) 2011 RICOH COMPANY, LTD. No security threat will occur even this data is subject to restrictions. 1.5 Glossary 1.5.1 Glossary for Lockout Release Timer... available function list, and user authentication procedures. Type Protected data Confidential data Table 8 : Definition of specific terms. Terms MFP Control Software Login user name Login password Table 9 : Specific Terms Related to each login user name. In this ST, "protected data", listed below , is ...
Security Target
Page 46
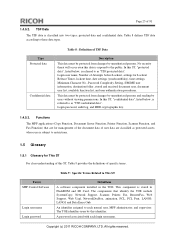
...allowed by an administrative role c) Revocation of data received over defined external interfaces before it is supposed to perform specific checks and process data received on one requires explicit allowance by an authorized administrative role. Component levelling: FPT_FDI_EXP:...) data are connected to specify this information before these data are allowed to another external interface. Examples Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. 5 Extended Components Definition This section describes Extended Components Definition. Management: FPT_FDI_EXP.1 The ...
...allowed by an administrative role c) Revocation of data received over defined external interfaces before it is supposed to perform specific checks and process data received on one requires explicit allowance by an authorized administrative role. Component levelling: FPT_FDI_EXP:...) data are connected to specify this information before these data are allowed to another external interface. Examples Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. 5 Extended Components Definition This section describes Extended Components Definition. Management: FPT_FDI_EXP.1 The ...
Security Target
Page 47
...therefore be placed in this . It did not fit well in any of the existing families in a Security Target. Copyright (c) 2011 RICOH COMPANY, LTD. However, in either the FDP or the FPT class. Therefore, the authors decided to define an extended component to disallow...FDP_IFF and FDP_IFC for this functionality. All rights reserved. Page 46 of 91 are firewall systems but also other components Dependencies: FMT_SMF.1 Specification of Management Functions FMT_SMR.1 Security roles FPT_FDI_EXP.1.1 The TSF shall provide the capability to restrict data received on [assignment: the Operation ...
...therefore be placed in this . It did not fit well in any of the existing families in a Security Target. Copyright (c) 2011 RICOH COMPANY, LTD. However, in either the FDP or the FPT class. Therefore, the authors decided to define an extended component to disallow...FDP_IFF and FDP_IFC for this functionality. All rights reserved. Page 46 of 91 are firewall systems but also other components Dependencies: FMT_SMF.1 Specification of Management Functions FMT_SMR.1 Security roles FPT_FDI_EXP.1.1 The TSF shall provide the capability to restrict data received on [assignment: the Operation ...
Security Target
Page 49
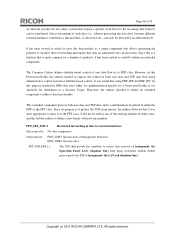
...use of the authentication mechanism; a) Minimal: Unsuccessful use of login operation Copyright (c) 2011 RICOH COMPANY, LTD. Start and end operation of downloading document data. - c) Detailed: The specific security attributes used in making an access check. Start and end operation of 91 Functional...Auditable Auditable Events a) Minimal: Successful requests to perform an operation on an object covered by the SFP. c) Detailed: The specific security attributes used in making an access check. Table 11 : List of Auditable Events Page 48 of printing document data. ...
...use of the authentication mechanism; a) Minimal: Unsuccessful use of login operation Copyright (c) 2011 RICOH COMPANY, LTD. Start and end operation of downloading document data. - c) Detailed: The specific security attributes used in making an access check. Start and end operation of 91 Functional...Auditable Auditable Events a) Minimal: Successful requests to perform an operation on an object covered by the SFP. c) Detailed: The specific security attributes used in making an access check. Table 11 : List of Auditable Events Page 48 of printing document data. ...
Security Target
Page 61
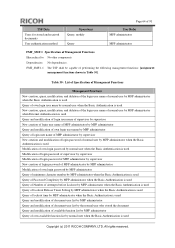
Dependencies: [FDP_ACC.1 Subset access control, or FDP_IFC.1 Subset information flow control] FMT_SMR.1 Security roles FMT_SMF.1 Specification of Management Function FMT_MSA.1.1(a) The TSF shall enforce the [assignment: document access control SFP] to restrict the ability to [selection: query, modify, delete, [assignment: newly ... login user name MFP administrator Supervisor MFP administrator MFP administrator who owns the applicable login user name Supervisor None No operation permitted None Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.
Dependencies: [FDP_ACC.1 Subset access control, or FDP_IFC.1 Subset information flow control] FMT_SMR.1 Security roles FMT_SMF.1 Specification of Management Function FMT_MSA.1.1(a) The TSF shall enforce the [assignment: document access control SFP] to restrict the ability to [selection: query, modify, delete, [assignment: newly ... login user name MFP administrator Supervisor MFP administrator MFP administrator who owns the applicable login user name Supervisor None No operation permitted None Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.
Security Target
Page 62
... [when document data attribute is not allowed in Table 27]. Dependencies: [FDP_ACC.1 Subset access control, or FDP_IFC.1 Subset information flow control] FMT_SMR.1 Security roles FMT_SMF.1 Specification of Management Function FMT_MSA.1.1(b)The TSF shall enforce the [assignment: TOE function access control SFP] to restrict the ability to [selection: query, modify, delete, [assignment... of 91 MFP administrator, applicable normal user who owns the applicable login user name MFP administrator MFP administrator Applicable normal user None None Copyright (c) 2011 RICOH COMPANY, LTD.
... [when document data attribute is not allowed in Table 27]. Dependencies: [FDP_ACC.1 Subset access control, or FDP_IFC.1 Subset information flow control] FMT_SMR.1 Security roles FMT_SMF.1 Specification of Management Function FMT_MSA.1.1(b)The TSF shall enforce the [assignment: TOE function access control SFP] to restrict the ability to [selection: query, modify, delete, [assignment... of 91 MFP administrator, applicable normal user who owns the applicable login user name MFP administrator MFP administrator Applicable normal user None None Copyright (c) 2011 RICOH COMPANY, LTD.
Security Target
Page 63
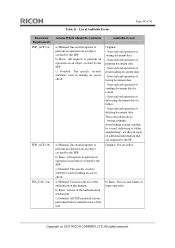
...User job Security Attributes Document data attribute Document user list Document user list Login user name of Management Functions Copyright (c) 2011 RICOH COMPANY, LTD. Table 28 : Authorised Identified Roles Allowed to enforce the SFP. Normal user who stored the applicable document ... of TSF data Hierarchical to : No other components. No authorised identified roles - Dependencies: FMT_SMR.1 Security roles FMT_SMF.1 Specification of normal user Authorised Identified Roles - Page 62 of 91 FMT_MSA.3(a)Static attribute initialisation Hierarchical to override the default values ...
...User job Security Attributes Document data attribute Document user list Document user list Login user name of Management Functions Copyright (c) 2011 RICOH COMPANY, LTD. Table 28 : Authorised Identified Roles Allowed to enforce the SFP. Normal user who stored the applicable document ... of TSF data Hierarchical to : No other components. No authorised identified roles - Dependencies: FMT_SMR.1 Security roles FMT_SMF.1 Specification of normal user Authorised Identified Roles - Page 62 of 91 FMT_MSA.3(a)Static attribute initialisation Hierarchical to override the default values ...
Security Target
Page 65
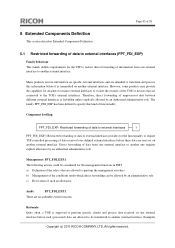
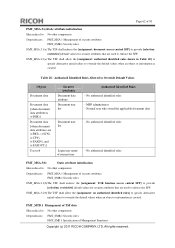
... Query of lockout time by MFP administrator Query of Management Functions Hierarchical to: No other components. Table 30 : List of Specification of Management Functions Management Functions New creation, query, modification, and deletion of the login user name of normal user by MFP...the Basic Authentication is used Query of Lockout Release Timer Setting by MFP administrator when the Basic Authentication is used Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. FMT_SMF.1.1 The TSF shall be capable of performing the following management functions: [assignment: management ...
... Query of lockout time by MFP administrator Query of Management Functions Hierarchical to: No other components. Table 30 : List of Specification of Management Functions Management Functions New creation, query, modification, and deletion of the login user name of normal user by MFP...the Basic Authentication is used Query of Lockout Release Timer Setting by MFP administrator when the Basic Authentication is used Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. FMT_SMF.1.1 The TSF shall be capable of performing the following management functions: [assignment: management ...
Security Target
Page 67
...dependencies. FTP_ITC.1.2 The TSF shall permit [selection: the TSF, another trusted IT product that is EAL3+ALC_FLR.2. Dependencies: FMT_SMF.1 Specification of Management Functions FMT_SMR.1 Security roles FPT_FDI_EXP.1.1 The TSF shall provide the capability to restrict data received on [assignment: the Operation ...and telephone line]. 6.1.7 Class FTA: TOE access FTA_SSL.3 TSF-initiated termination Hierarchical to: No other components. Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. ALC_FLR.2 was added to the set of the TOE. FTP_ITC.1.3 The TSF shall initiate ...
...dependencies. FTP_ITC.1.2 The TSF shall permit [selection: the TSF, another trusted IT product that is EAL3+ALC_FLR.2. Dependencies: FMT_SMF.1 Specification of Management Functions FMT_SMR.1 Security roles FPT_FDI_EXP.1.1 The TSF shall provide the capability to restrict data received on [assignment: the Operation ...and telephone line]. 6.1.7 Class FTA: TOE access FTA_SSL.3 TSF-initiated termination Hierarchical to: No other components. Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. ALC_FLR.2 was added to the set of the TOE. FTP_ITC.1.3 The TSF shall initiate ...
Security Target
Page 68
...32 shows the relationship between the TOE security functional requirements and TOE security objectives. Copyright (c) 2011 RICOH COMPANY, LTD. Table 32 shows that each TOE security functional requirement fulfils at least one TOE security...ASE_OBJ.2 ASE_REQ.2 ASE_SPD.1 ASE_TSS.1 ATE_COV.2 ATE_DPT.1 ATE_FUN.1 ATE_IND.2 AVA_VAN.2 Assurance Components Security architecture description Functional specification with complete summary Architectural design Operational user guidance Preparative procedures Authorisation controls Implementation representation CM coverage Delivery procedures Identification ...
...32 shows the relationship between the TOE security functional requirements and TOE security objectives. Copyright (c) 2011 RICOH COMPANY, LTD. Table 32 shows that each TOE security functional requirement fulfils at least one TOE security...ASE_OBJ.2 ASE_REQ.2 ASE_SPD.1 ASE_TSS.1 ATE_COV.2 ATE_DPT.1 ATE_FUN.1 ATE_IND.2 AVA_VAN.2 Assurance Components Security architecture description Functional specification with complete summary Architectural design Operational user guidance Preparative procedures Authorisation controls Implementation representation CM coverage Delivery procedures Identification ...
Security Target
Page 72
...for sending or receiving the TSF protected data. The supervisor and applicable MFP administrator are protected by FTP_ITC.1. Copyright (c) 2011 RICOH COMPANY, LTD. By satisfying FMT_MTD.1, FMT_SMF.1, FMT_SMR.1 and FTP_ITC.1, which are generated. FMT_MSA.1(a) restricts each available operation (newly... of user jobs (object) when the user jobs are the security functional requirements for stored and received documents. (2) Specification of supervisor. The MFP administrator is fulfilled. By satisfying FDP_ACC.1(a), FDP_ACF.1(a), FTP_ITC.1, FMT_MSA.1(a) and FMT_MSA.3(a), which are ...
...for sending or receiving the TSF protected data. The supervisor and applicable MFP administrator are protected by FTP_ITC.1. Copyright (c) 2011 RICOH COMPANY, LTD. By satisfying FMT_MTD.1, FMT_SMF.1, FMT_SMR.1 and FTP_ITC.1, which are generated. FMT_MSA.1(a) restricts each available operation (newly... of user jobs (object) when the user jobs are the security functional requirements for stored and received documents. (2) Specification of supervisor. The MFP administrator is fulfilled. By satisfying FDP_ACC.1(a), FDP_ACF.1(a), FTP_ITC.1, FMT_MSA.1(a) and FMT_MSA.3(a), which are ...