Security Guide
Page 4
... differences of the modules covered by using the Nokia Firewall Flows. As network devices, the Nokia VPN Appliances support a comprehensive suite of 43 This document may be freely reproduced and distributed whole and intact including this Security Policy: Model IP260 IP265 IP1220 IP1260 CPU Type Celeron Celeron Xeon Xeon Firewall Speed 272Mbps 272Mbps 2.2Gbps 3.9Gbps VPN Speed...
... differences of the modules covered by using the Nokia Firewall Flows. As network devices, the Nokia VPN Appliances support a comprehensive suite of 43 This document may be freely reproduced and distributed whole and intact including this Security Policy: Model IP260 IP265 IP1220 IP1260 CPU Type Celeron Celeron Xeon Xeon Firewall Speed 272Mbps 272Mbps 2.2Gbps 3.9Gbps VPN Speed...
Security Guide
Page 5
...firewall functionalities. FIPS Algorithm validation testing was retested as multi-chip standalone cryptographic modules. All component slots are performed by both Check Point and Nokia. The following hardware versions: ƒ IP260 / IP265 - half-width 1U rack mount ƒ IP1220 / IP1260 - All FRU upgrades are secured...the cryptographic boundary of each of the Nokia VPN Appliance configurations and was performed and validation certificates obtained for FIPS mode. The Nokia VPN Appliances run the Nokia proprietary, security-hardened IPSO operating system along with ...
...firewall functionalities. FIPS Algorithm validation testing was retested as multi-chip standalone cryptographic modules. All component slots are performed by both Check Point and Nokia. The following hardware versions: ƒ IP260 / IP265 - half-width 1U rack mount ƒ IP1220 / IP1260 - All FRU upgrades are secured...the cryptographic boundary of each of the Nokia VPN Appliance configurations and was performed and validation certificates obtained for FIPS mode. The Nokia VPN Appliances run the Nokia proprietary, security-hardened IPSO operating system along with ...
Security Guide
Page 8
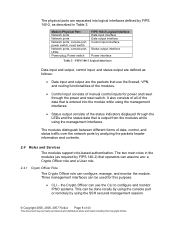
... authentication. The two main roles in Table 2. The physical ports are separated into the module while using the SSH secured management session. © Copyright 2005, 2006, 2007 Nokia Page 8 of 43 This document may be freely reproduced and distributed whole and intact including this purpose: • ...CLI - It also consists of all of the data that is output from the modules while using the management interfaces. the Crypto Officer can use the firewall, ...
... authentication. The two main roles in Table 2. The physical ports are separated into the module while using the SSH secured management session. © Copyright 2005, 2006, 2007 Nokia Page 8 of 43 This document may be freely reproduced and distributed whole and intact including this purpose: • ...CLI - It also consists of all of the data that is output from the modules while using the management interfaces. the Crypto Officer can use the firewall, ...
Security Guide
Page 33
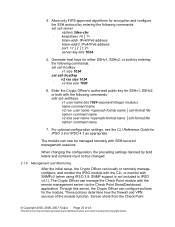
...IPv6 address listen-addr2 IPv4/IPv6 address port server-key-bits 1024 5. These policies determine how the firewall and VPN services of 43 This document may be freely reproduced and distributed whole and intact including this ... Management and Monitoring After the initial setup, the Crypto Officer can manage the Check Point module with SSH-secured management sessions. SNMP support is not included in IPSO v4.1). The Crypto Officer can locally or remotely manage,...appropriate. Screen shots from the Check Point © Copyright 2005, 2006, 2007 Nokia Page 33 of the module function. 4.
...IPv6 address listen-addr2 IPv4/IPv6 address port server-key-bits 1024 5. These policies determine how the firewall and VPN services of 43 This document may be freely reproduced and distributed whole and intact including this ... Management and Monitoring After the initial setup, the Crypto Officer can manage the Check Point module with SSH-secured management sessions. SNMP support is not included in IPSO v4.1). The Crypto Officer can locally or remotely manage,...appropriate. Screen shots from the Check Point © Copyright 2005, 2006, 2007 Nokia Page 33 of the module function. 4.