Security Guide
Page 4
Some highlighted security features of the Nokia VPN Appliances are: • Read/write and read-only access modes • Screening of all modules greatly accelerate the embedded Check Point VPN-1/FireWall-1 performance by this Security Policy: Model IP260 IP265 IP1220 IP1260 CPU Type Celeron Celeron Xeon Xeon Firewall Speed 272Mbps 272Mbps 2.2Gbps 3.9Gbps VPN Speed (AES, TDES...
Some highlighted security features of the Nokia VPN Appliances are: • Read/write and read-only access modes • Screening of all modules greatly accelerate the embedded Check Point VPN-1/FireWall-1 performance by this Security Policy: Model IP260 IP265 IP1220 IP1260 CPU Type Celeron Celeron Xeon Xeon Firewall Speed 272Mbps 272Mbps 2.2Gbps 3.9Gbps VPN Speed (AES, TDES...
Security Guide
Page 11
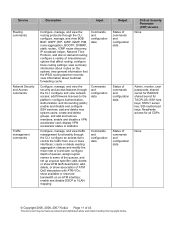
... or show ATM QoS descriptors; view summary information about multicast forwarding cache Commands and configuration data Configure, manage, and view the security and access features through the CLI: configure and view network access; add, delete, or show association of queues, assign logical names to the ...DSCP to control the traffic from one or more interfaces; shared secret for all CSPs None © Copyright 2005, 2006, 2007 Nokia Page 11 of miscellaneous options that the IPSO routing daemon records; SSH host keys; configure a variety of 43 This document may ...
... or show ATM QoS descriptors; view summary information about multicast forwarding cache Commands and configuration data Configure, manage, and view the security and access features through the CLI: configure and view network access; add, delete, or show association of queues, assign logical names to the ...DSCP to control the traffic from one or more interfaces; shared secret for all CSPs None © Copyright 2005, 2006, 2007 Nokia Page 11 of miscellaneous options that the IPSO routing daemon records; SSH host keys; configure a variety of 43 This document may ...
Security Guide
Page 32
...commands: set ssh server dsa-authentication 1 password-authentication 1 rhosts-authentication 0 rhosts-authentication 0 rsa-authentication 1 © Copyright 2005, 2006, 2007 Nokia Page 32 of operation to FIPS mode 1. Using the CLI through the console port, enter the following command: set fips on page 41. ...3.1.5 Initializing the Remote Management of disabled access and feature mechanisms, see Appendix A on restart command. To ensure that the device is in FIPS mode. FIPS mode can be enabled only ...
...commands: set ssh server dsa-authentication 1 password-authentication 1 rhosts-authentication 0 rhosts-authentication 0 rsa-authentication 1 © Copyright 2005, 2006, 2007 Nokia Page 32 of operation to FIPS mode 1. Using the CLI through the console port, enter the following command: set fips on page 41. ...3.1.5 Initializing the Remote Management of disabled access and feature mechanisms, see Appendix A on restart command. To ensure that the device is in FIPS mode. FIPS mode can be enabled only ...
Security Guide
Page 41
...a FIPS mode of operation, many of the existing and new features of Nokia IPSO are disabled when the module is in FIPS mode: • HTTP access • FTP access • Telnet access • TFTP access • Load Sharing (Nokia IPSO Clustering) and High Availability (VRRP) • NTP &#...8226; SSLv3 • Disabled algorithms: o CAST o DES (40 bits) o MD5 o HMAC MD5 o Arcfour o Twofish o Blowfish © Copyright 2005, 2006, 2007 Nokia Page 41 of 43 This document may be freely reproduced and distributed whole and intact including this Copyright Notice. The following list shows all the...
...a FIPS mode of operation, many of the existing and new features of Nokia IPSO are disabled when the module is in FIPS mode: • HTTP access • FTP access • Telnet access • TFTP access • Load Sharing (Nokia IPSO Clustering) and High Availability (VRRP) • NTP &#...8226; SSLv3 • Disabled algorithms: o CAST o DES (40 bits) o MD5 o HMAC MD5 o Arcfour o Twofish o Blowfish © Copyright 2005, 2006, 2007 Nokia Page 41 of 43 This document may be freely reproduced and distributed whole and intact including this Copyright Notice. The following list shows all the...
Security Guide
Page 43
...Error Detection Code Electromagnetic Compatibility Electromagnetic Interference Encapsulating Security Payload Federal Communication Commission Federal Information Processing Standard Feature Pack Inter-Gateway Routing Protocol Internet Key Exchange IP Security Known Answer Test Light Emitting Diode Message ... Protocol Rivest Shamir and Adleman Security Association Secure Hash Algorithm Secure Internal Communications Simple Network Management Protocol Secure Shell Secure Socket Layer Transport Layer Security Virtual Private Network © Copyright 2005, 2006, 2007 Nokia Page 43 of 43 This ...
...Error Detection Code Electromagnetic Compatibility Electromagnetic Interference Encapsulating Security Payload Federal Communication Commission Federal Information Processing Standard Feature Pack Inter-Gateway Routing Protocol Internet Key Exchange IP Security Known Answer Test Light Emitting Diode Message ... Protocol Rivest Shamir and Adleman Security Association Secure Hash Algorithm Secure Internal Communications Simple Network Management Protocol Secure Shell Secure Socket Layer Transport Layer Security Virtual Private Network © Copyright 2005, 2006, 2007 Nokia Page 43 of 43 This ...