Security Guide
Page 8
... defined as follows: • Data input and output are the packets that is entered into logical interfaces defined by using the SSH secured management session. © Copyright 2005, 2006, 2007 Nokia Page 8 of 43 This document may be done locally by using the console port or remotely by FIPS 140-2, as required...
... defined as follows: • Data input and output are the packets that is entered into logical interfaces defined by using the SSH secured management session. © Copyright 2005, 2006, 2007 Nokia Page 8 of 43 This document may be done locally by using the console port or remotely by FIPS 140-2, as required...
Security Guide
Page 14
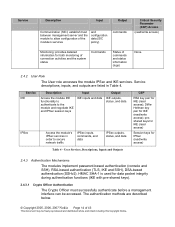
The authentication methods are listed in order to secure network traffic IPSec inputs, commands, and data ... Descriptions, Inputs and Outputs 2.4.3 Authentication Mechanisms The modules implement password-based authentication (console and SSH), RSA-based authentication (TLS, IKE and SSH), DSA-based authentication (SSHv2). HMAC SHA-1 is used for both monitoring of ...to allow configuration of the module's services and configuration data (SIC policy) commands Critical Security Parameter (CSP) Access (read /write access) Table 4 - Service descriptions, inputs, and outputs are described below...
The authentication methods are listed in order to secure network traffic IPSec inputs, commands, and data ... Descriptions, Inputs and Outputs 2.4.3 Authentication Mechanisms The modules implement password-based authentication (console and SSH), RSA-based authentication (TLS, IKE and SSH), DSA-based authentication (SSHv2). HMAC SHA-1 is used for both monitoring of ...to allow configuration of the module's services and configuration data (SIC policy) commands Critical Security Parameter (CSP) Access (read /write access) Table 4 - Service descriptions, inputs, and outputs are described below...
Security Guide
Page 15
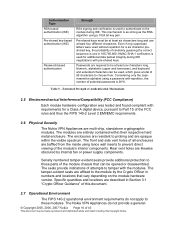
... a digital certificate issued by a trusted Certification Authority (CA). 2.4.3.2 User Authentication User authentication to access the CLI. RSA-based authentication (SSHv1, SSHv2 and TLS handshake) RSA encryption and decryption is described in Table 5. during the SSH session establishment....handshake. • CLI (local) - Authentication Type Strength DSA-based authentication (SSHv2) DSA signing and verification is performed during IKE using a 1024 bit key pair. © Copyright 2005, 2006, 2007 Nokia Page 15 of each authentication mechanism implemented by using a 1024 ...
... a digital certificate issued by a trusted Certification Authority (CA). 2.4.3.2 User Authentication User authentication to access the CLI. RSA-based authentication (SSHv1, SSHv2 and TLS handshake) RSA encryption and decryption is described in Table 5. during the SSH session establishment....handshake. • CLI (local) - Authentication Type Strength DSA-based authentication (SSHv2) DSA signing and verification is performed during IKE using a 1024 bit key pair. © Copyright 2005, 2006, 2007 Nokia Page 15 of each authentication mechanism implemented by using a 1024 ...
Security Guide
Page 16
...FCC Compliance) Each module hardware configuration was tested and found compliant with pre-shared keys. Authentication Type RSA-based authentication (IKE) Pre-shared key-based authentication (IKE) Password-based authentication Strength RSA signing and verification is used to authenticate to tamper with the modules. Specific quantities and... with repetition, the number of the FCC rules and thus the FIPS 140-2 Level 2 EMI/EMC requirements. 2.6 Physical Security The Nokia VPN Appliances are opaque within their respective hard metal enclosure. This mechanism is 26^6. Table 5 -
...FCC Compliance) Each module hardware configuration was tested and found compliant with pre-shared keys. Authentication Type RSA-based authentication (IKE) Pre-shared key-based authentication (IKE) Password-based authentication Strength RSA signing and verification is used to authenticate to tamper with the modules. Specific quantities and... with repetition, the number of the FCC rules and thus the FIPS 140-2 Level 2 EMI/EMC requirements. 2.6 Physical Security The Nokia VPN Appliances are opaque within their respective hard metal enclosure. This mechanism is 26^6. Table 5 -
Security Guide
Page 17
...chip as well as the VPN encryption algorithm. © Copyright 2005, 2006, 2007 Nokia Page 17 of 43 This document may be chosen as self-tests for all firmware-based cryptographic functions. Accelerator chips differ only in IKE is performed by the encryption accelerators. The...and quick, using RSA key wrapping. Key establishment is electrically bypassed. Check Point provides the capability to use SSHv1 or SSHv2 to secure management sessions. Note that accelerated DES and 1 key Triple DES are non-compliant with the module through customized interfaces that are implemented ...
...chip as well as the VPN encryption algorithm. © Copyright 2005, 2006, 2007 Nokia Page 17 of 43 This document may be chosen as self-tests for all firmware-based cryptographic functions. Accelerator chips differ only in IKE is performed by the encryption accelerators. The...and quick, using RSA key wrapping. Key establishment is electrically bypassed. Check Point provides the capability to use SSHv1 or SSHv2 to secure management sessions. Note that accelerated DES and 1 key Triple DES are non-compliant with the module through customized interfaces that are implemented ...
Security Guide
Page 20
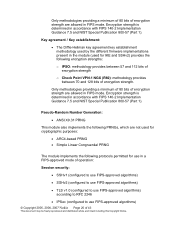
... different firmware implementations present in the module (used for cryptographic purposes: • ARC4-based PRNG • Simple Linear Congruential PRNG The module implements the following protocols permitted for...following PRNGs, which are not used for use in a FIPS-approved mode of operation: Session security: • SSHv1 (configured to use FIPS-approved algorithms) • SSHv2 (configured to use...; IPSec (configured to use FIPS-approved algorithms) © Copyright 2005, 2006, 2007 Nokia Page 20 of encryption strength. Only methodologies providing a minimum of 80 bits of encryption ...
... different firmware implementations present in the module (used for cryptographic purposes: • ARC4-based PRNG • Simple Linear Congruential PRNG The module implements the following protocols permitted for...following PRNGs, which are not used for use in a FIPS-approved mode of operation: Session security: • SSHv1 (configured to use FIPS-approved algorithms) • SSHv2 (configured to use...; IPSec (configured to use FIPS-approved algorithms) © Copyright 2005, 2006, 2007 Nokia Page 20 of encryption strength. Only methodologies providing a minimum of 80 bits of encryption ...
Security Guide
Page 29
... below to install the NGX with Check Point VPN-1 version R55p running a FIPS 140-2 validated configuration. For older Nokia VPN Appliance modules, the Crypto Officer may need to upgrade the supplied IPSO and/or or the Check Point firmware so that ...may be followed: 3.1.2.1 SCENARIO 1 - The Crypto Officer must be freely reproduced and distributed whole and intact including this version and install NGX (R60): A. Access the device via Voyager, the web-based...
... below to install the NGX with Check Point VPN-1 version R55p running a FIPS 140-2 validated configuration. For older Nokia VPN Appliance modules, the Crypto Officer may need to upgrade the supplied IPSO and/or or the Check Point firmware so that ...may be followed: 3.1.2.1 SCENARIO 1 - The Crypto Officer must be freely reproduced and distributed whole and intact including this version and install NGX (R60): A. Access the device via Voyager, the web-based...