Installation Guide
Page 1
... user interface: Use the main local browser user interface, abbreviated as a DHCP client. If you can use 169.254.100.201. • For access over the switch's default IP address. 1. Access the AV UI or main UI to configure the switch You can download by visiting netgear.com/support/download/. 1. Connect an Ethernet cable from an Ethernet port on your computer to the OOB port or an Ethernet network port on the same subnet as the service port), through the Type-C USB console port...
... user interface: Use the main local browser user interface, abbreviated as a DHCP client. If you can use 169.254.100.201. • For access over the switch's default IP address. 1. Access the AV UI or main UI to configure the switch You can download by visiting netgear.com/support/download/. 1. Connect an Ethernet cable from an Ethernet port on your computer to the OOB port or an Ethernet network port on the same subnet as the service port), through the Type-C USB console port...
Installation Guide
Page 2
... EXEC mode by typing enable, type the show serviceport command, and press Enter. • To find the assigned IP address of the switch's OOB port or management interface (which is connected to a DHCP server. 2. Access the CLI to configure the switch To use the following settings: baud rate, 115,200 bps; flow control, none. 5. Depending on the switch, start a terminal emulation program: • On a computer with a Windows operating system, you can use the Type-C USB port, you to a console port on...
... EXEC mode by typing enable, type the show serviceport command, and press Enter. • To find the assigned IP address of the switch's OOB port or management interface (which is connected to a DHCP server. 2. Access the CLI to configure the switch To use the following settings: baud rate, 115,200 bps; flow control, none. 5. Depending on the switch, start a terminal emulation program: • On a computer with a Windows operating system, you can use the Type-C USB port, you to a console port on...
Product Datasheet
Page 11
... Multicast Routes (the maximum number of IPv4 multicast forwarding table entries) • IPv6 Multicast Routes (the maximum number of IPv6 multicast forwarding table entries) Loopback interfaces management for routing protocols administration Private VLANs and local Proxy ARP help troubleshoot connectivity issues and restore various configurations to their corresponding MAC addresses that are supported for central software upgrades and configuration files management (HTTP, TFTP), including in highly secured versions (HTTPS, SFTP, SCP) Simple Network Time Protocol (SNTP) can be used to...
... Multicast Routes (the maximum number of IPv4 multicast forwarding table entries) • IPv6 Multicast Routes (the maximum number of IPv6 multicast forwarding table entries) Loopback interfaces management for routing protocols administration Private VLANs and local Proxy ARP help troubleshoot connectivity issues and restore various configurations to their corresponding MAC addresses that are supported for central software upgrades and configuration files management (HTTP, TFTP), including in highly secured versions (HTTPS, SFTP, SCP) Simple Network Time Protocol (SNTP) can be used to...
Product Datasheet
Page 12
... a router which switches IP packets transparently, a DHCP relay agent processes DHCP messages and generates new DHCP messages • Supports DHCP Relay Option 82 circuit-id and remote-id for VLANs Router Discovery Protocol is an extension to ICMP and enables hosts to dynamically discover the IP address of routers on local IP subnets • Multiple Helper IPs feature allows to configure a DHCP relay agent with multiple DHCP server addresses per routing interface and...
... a router which switches IP packets transparently, a DHCP relay agent processes DHCP messages and generates new DHCP messages • Supports DHCP Relay Option 82 circuit-id and remote-id for VLANs Router Discovery Protocol is an extension to ICMP and enables hosts to dynamically discover the IP address of routers on local IP subnets • Multiple Helper IPs feature allows to configure a DHCP relay agent with multiple DHCP server addresses per routing interface and...
Product Datasheet
Page 13
.../MAC addresses for malicious users traffic elimination Time-based Layer 2 / Layer 3-v4 / Layer 3-v6 / Layer 4 Access Control Lists (ACLs) can be binded to ports, Layer 2 interfaces, VLANs and LAGs (Link Aggregation Groups or Port channel) for fast unauthorized data prevention and right granularity For in-band switch management, management ACLs on the switch • MAB initiates after unsuccessful dot1x authentication process (configurable time out), when clients don't respond to any of EAPOL packets • When 802.1X unaware clients try to connect, the switch...
.../MAC addresses for malicious users traffic elimination Time-based Layer 2 / Layer 3-v4 / Layer 3-v6 / Layer 4 Access Control Lists (ACLs) can be binded to ports, Layer 2 interfaces, VLANs and LAGs (Link Aggregation Groups or Port channel) for fast unauthorized data prevention and right granularity For in-band switch management, management ACLs on the switch • MAB initiates after unsuccessful dot1x authentication process (configurable time out), when clients don't respond to any of EAPOL packets • When 802.1X unaware clients try to connect, the switch...
Product Datasheet
Page 14
... configured time-outs • By default, configuration authentication methods are supported for the switch configuration, based on latest industry standards: exec authorization using TACACS+ or RADIUS; command authorization using TACACS+ or RADIUS; and authentication based on user domain in addition to user ID and password Superior quality of service Advanced classifier-based hardware implementation for Layer 2 (MAC), Layer 3 (IP) and Layer 4 (UDP/TCP transport ports) prioritization 8 queues (7 in a stack) for priorities and various QoS...
... configured time-outs • By default, configuration authentication methods are supported for the switch configuration, based on latest industry standards: exec authorization using TACACS+ or RADIUS; command authorization using TACACS+ or RADIUS; and authentication based on user domain in addition to user ID and password Superior quality of service Advanced classifier-based hardware implementation for Layer 2 (MAC), Layer 3 (IP) and Layer 4 (UDP/TCP transport ports) prioritization 8 queues (7 in a stack) for priorities and various QoS...
Product Datasheet
Page 42
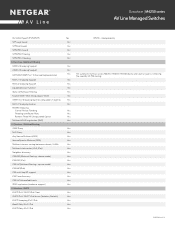
...(Multicast Routing - dense mode) PIM-DM (IPv6) PIM-SM (Multicast Routing - Multicast Filtering IGMPv2 Snooping Support IGMPv3 Snooping Support NETGEAR IGMP Plus™ Enhanced Implementation MLDv1 Snooping Support MLDv2 Snooping Support Expedited Leave function Static L2 Multicast Filtering Enable IGMP / MLD Snooping per VLAN IGMPv1/v2 Snooping Querier, compatible v3 queries MLDv1 Snooping Querier MGMD Snooping Control Packet Flooding Flooding to mRouter Ports Remove Flood-All-Unregistered Option Multicast VLAN registration (MVR) L3 Services - Datasheet | M4250 series AV Line Managed...
...(Multicast Routing - dense mode) PIM-DM (IPv6) PIM-SM (Multicast Routing - Multicast Filtering IGMPv2 Snooping Support IGMPv3 Snooping Support NETGEAR IGMP Plus™ Enhanced Implementation MLDv1 Snooping Support MLDv2 Snooping Support Expedited Leave function Static L2 Multicast Filtering Enable IGMP / MLD Snooping per VLAN IGMPv1/v2 Snooping Querier, compatible v3 queries MLDv1 Snooping Querier MGMD Snooping Control Packet Flooding Flooding to mRouter Ports Remove Flood-All-Unregistered Option Multicast VLAN registration (MVR) L3 Services - Datasheet | M4250 series AV Line Managed...
Product Datasheet
Page 44
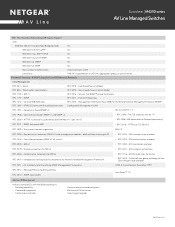
... Protection CPU Rate Limiting ICMP throttling Management Management ACL (MACAL) Max Rules Out of band Management Radius accounting TACACS+ Malicious Code Detection Network Traffic Access Control Lists (ACLs) Time-based ACLs Protocol-based ACLs ACL over VLANs Dynamic ACLs IEEE 802.1x Radius Port Access Authentication 802.1x MAC Address Authentication Bypass (MAB) Network Authentication Successive Tiering Port Security IP Source Guard DHCP Snooping Dynamic ARP Inspection IPv6 RA Guard Stateless Mode MAC Filtering Port MAC Locking Private Edge VLAN Private VLANs Quality of Service (QoS) -
... Protection CPU Rate Limiting ICMP throttling Management Management ACL (MACAL) Max Rules Out of band Management Radius accounting TACACS+ Malicious Code Detection Network Traffic Access Control Lists (ACLs) Time-based ACLs Protocol-based ACLs ACL over VLANs Dynamic ACLs IEEE 802.1x Radius Port Access Authentication 802.1x MAC Address Authentication Bypass (MAB) Network Authentication Successive Tiering Port Security IP Source Guard DHCP Snooping Dynamic ARP Inspection IPv6 RA Guard Stateless Mode MAC Filtering Port MAC Locking Private Edge VLAN Private VLANs Quality of Service (QoS) -
Product Datasheet
Page 48
...-state-mgmt-05 - SSH transport layer protocol RFC 2576 - An Architecture for Transport layer security RFC 2271 - SECSH public key file format - RFC 4252 - Conformance statements for SMI v2 RFC 3410 - RFC 4251 - Scripting capability - Context-sensitive help Optional user password encryption Multisession Telnet server Auto Image Upgrade PAGE 48 of SNMP Protocol Operations RFC 1157 - Time Sensitive Networking AVB Feature Support AVB IEEE 802...
...-state-mgmt-05 - SSH transport layer protocol RFC 2576 - An Architecture for Transport layer security RFC 2271 - SECSH public key file format - RFC 4252 - Conformance statements for SMI v2 RFC 3410 - RFC 4251 - Scripting capability - Context-sensitive help Optional user password encryption Multisession Telnet server Auto Image Upgrade PAGE 48 of SNMP Protocol Operations RFC 1157 - Time Sensitive Networking AVB Feature Support AVB IEEE 802...
Product Datasheet
Page 50
... and DHCP Power Source Equipment (PSE) IEEE 802.af Powered Ethernet (DTE Power via the TCP MD5 Signature Option RFC 2453 - Assign matching traffic flow to implement transparent subnet gateways (Proxy ARP) RFC 1256 - Access Control Lists (ACLs) Permit/deny actions for IPv4 routers RFC 2082 - TCP/UDP destination port - Minimum and maximum bandwidth per queue - Using ARP to a specific queue - IPv6 flow label - IP precedence to -Point Links RFC...
... and DHCP Power Source Equipment (PSE) IEEE 802.af Powered Ethernet (DTE Power via the TCP MD5 Signature Option RFC 2453 - Assign matching traffic flow to implement transparent subnet gateways (Proxy ARP) RFC 1256 - Access Control Lists (ACLs) Permit/deny actions for IPv4 routers RFC 2082 - TCP/UDP destination port - Minimum and maximum bandwidth per queue - Using ARP to a specific queue - IPv6 flow label - IP precedence to -Point Links RFC...
User Manual
Page 9
AV Line of Fully Managed Switches M4250 Series Main User Manual Configure the CST settings and display the CST status..........229 Configure the CST interface settings 231 Display the CST interface status 234 Manage MST instances 236 Add an MST instance and display the MST status 236 Change an MST instance 238 Delete an MST instance 238 Configure and display the interface settings for an MST instance 239 Display the STP interface statistics 242 Configure the...
AV Line of Fully Managed Switches M4250 Series Main User Manual Configure the CST settings and display the CST status..........229 Configure the CST interface settings 231 Display the CST interface status 234 Manage MST instances 236 Add an MST instance and display the MST status 236 Change an MST instance 238 Delete an MST instance 238 Configure and display the interface settings for an MST instance 239 Display the STP interface statistics 242 Configure the...
User Manual
Page 25
... Series Main User Manual By default, no IP address is set for the OOB port, but its DHCP client is enabled so that the port can change the password again.) Log in to the main UI using the OOB port, reboot the switch so that the IP address for your network. The login page displays. 6. The System Information page displays. Connect an Ethernet cable from an Ethernet port on your computer with a static IP address: • For access...
... Series Main User Manual By default, no IP address is set for the OOB port, but its DHCP client is enabled so that the port can change the password again.) Log in to the main UI using the OOB port, reboot the switch so that the IP address for your network. The login page displays. 6. The System Information page displays. Connect an Ethernet cable from an Ethernet port on your computer with a static IP address: • For access...
User Manual
Page 65
... the Delete button. Launch a web browser. 2. To remove an IPv6 default route address, in the IPv6 Default Route Configuration section, do the following : a. Click the Add button. To save the settings to use each subsequent time that you log in , no password is added to remove. The first time that you log in . The IPv6 Management Interface Configuration page displays. 6. AV Line of the switch. Configure the time setting manually To configure the time setting manually 1. Select the Change IPv6 Default Route check box. Enter admin as the user name...
... the Delete button. Launch a web browser. 2. To remove an IPv6 default route address, in the IPv6 Default Route Configuration section, do the following : a. Click the Add button. To save the settings to use each subsequent time that you log in , no password is added to remove. The first time that you log in . The IPv6 Management Interface Configuration page displays. 6. AV Line of the switch. Configure the time setting manually To configure the time setting manually 1. Select the Change IPv6 Default Route check box. Enter admin as the user name...
User Manual
Page 190
... VLAN membership table. AV Line of Fully Managed Switches M4250 Series Main User Manual VLANs Adding virtual LAN (VLAN) support to the end user. Configure Switching Information 190 Main User Manual Each switch can be assigned to 1024 VLANs. In the address field of your local device password, and click the Login button. By default, all ports are members. Launch a web browser. 2. Enter admin as the user name, enter your web browser, enter the IP address of multicast traffic. Add a VLAN You can add multiple VLANs...
... VLAN membership table. AV Line of Fully Managed Switches M4250 Series Main User Manual VLANs Adding virtual LAN (VLAN) support to the end user. Configure Switching Information 190 Main User Manual Each switch can be assigned to 1024 VLANs. In the address field of your local device password, and click the Login button. By default, all ports are members. Launch a web browser. 2. Enter admin as the user name, enter your web browser, enter the IP address of multicast traffic. Add a VLAN You can add multiple VLANs...
User Manual
Page 194
... routing interface. Click the Apply button. Auto-Trunk overview Auto-trunk is a feature that you log in , no password is enabled on capable physical links and LAG interfaces between partner devices. A trunk can carry all VLANs on the switch and on the switch become part of the trunk, allowing automatic configuration of Fully Managed Switches M4250 Series Main User Manual To change the internal VLAN allocation settings: 1. Enter admin as a trunk (that you log in . The first time that lets the switch automatically enable Trunk mode...
... routing interface. Click the Apply button. Auto-Trunk overview Auto-trunk is a feature that you log in , no password is enabled on capable physical links and LAG interfaces between partner devices. A trunk can carry all VLANs on the switch and on the switch become part of the trunk, allowing automatic configuration of Fully Managed Switches M4250 Series Main User Manual To change the internal VLAN allocation settings: 1. Enter admin as a trunk (that you log in . The first time that lets the switch automatically enable Trunk mode...
User Manual
Page 207
... access control (MAC) addresses. • IPX: The internetwork packet exchange (IPX) is a network layer protocol that forwards data over a network. Click the Main UI Login button. A group ID is required. Select Switching > VLAN > Advanced > Protocol Based VLAN Group Configuration. The Protocol Based VLAN Group Configuration page displays. 6. For example, to specify all three protocols, enter the following protocols to 16 characters. 8. You can include multiple interfaces. AV Line of your local device password...
... access control (MAC) addresses. • IPX: The internetwork packet exchange (IPX) is a network layer protocol that forwards data over a network. Click the Main UI Login button. A group ID is required. Select Switching > VLAN > Advanced > Protocol Based VLAN Group Configuration. The Protocol Based VLAN Group Configuration page displays. 6. For example, to specify all three protocols, enter the following protocols to 16 characters. 8. You can include multiple interfaces. AV Line of your local device password...
User Manual
Page 256
... default is Enable. 8. This selection enables or disables the administrative mode for IGMP snooping for the switch. The default is Disable. 7. Note: For information about IGMP Plus mode, see Configure IGMP snooping automatically with source IP address 0.0.0.0 is not sent in , no password is forwarded to an upstream mrouter interface. AV Line of Fully Managed Switches M4250 Series Main User Manual The first time that you log in the associated VLAN. Select the Admin Mode Enable or Disable radio button. In addition, the switch forwards a multicast data...
... default is Enable. 8. This selection enables or disables the administrative mode for IGMP snooping for the switch. The default is Disable. 7. Note: For information about IGMP Plus mode, see Configure IGMP snooping automatically with source IP address 0.0.0.0 is not sent in , no password is forwarded to an upstream mrouter interface. AV Line of Fully Managed Switches M4250 Series Main User Manual The first time that you log in the associated VLAN. Select the Admin Mode Enable or Disable radio button. In addition, the switch forwards a multicast data...
User Manual
Page 527
... device UI, your Mac user name and password and click the Update Setting button. • Mozilla Firefox: Click the ADVANCED button. Then, click the Add Exception button. Click the Apply button. If a warning pop-up window display to let you are saved. Manage Switch Security 527 Main User Manual The default value is the default version for the security warning. AV Line of Fully Managed Switches M4250 Series Main User Manual The value must be...
... device UI, your Mac user name and password and click the Update Setting button. • Mozilla Firefox: Click the ADVANCED button. Then, click the Add Exception button. Click the Apply button. If a warning pop-up window display to let you are saved. Manage Switch Security 527 Main User Manual The default value is the default version for the security warning. AV Line of Fully Managed Switches M4250 Series Main User Manual The value must be...
User Manual
Page 552
... setting of the login authentication list (see RADIUS servers on page 500). • Primary authentication method: Set the primary authentication method to RADIUS, that is, RADIUS must be method 1 for example, the RADIUS server that apply to the switch and to specific users. The login page displays. 3. In the address field of your web browser, enter the IP address of the switch. AV Line of Fully Managed Switches M4250 Series Main User Manual Port authentication With port...
... setting of the login authentication list (see RADIUS servers on page 500). • Primary authentication method: Set the primary authentication method to RADIUS, that is, RADIUS must be method 1 for example, the RADIUS server that apply to the switch and to specific users. The login page displays. 3. In the address field of your web browser, enter the IP address of the switch. AV Line of Fully Managed Switches M4250 Series Main User Manual Port authentication With port...
User Manual
Page 646
.... Access control lists Access control lists (ACLs) ensure that passed since the client was authorized. To view ACL configuration examples, see Access control lists (ACLs) on page 768. The IP address of traffic are used to reach network resources. The interface the client is using. AV Line of the connected client. The user name (or guest ID) of Fully Managed Switches M4250 Series Main User Manual Table 160. The total number of bytes the client transmitted. Captive portal client statistics Field MAC Address...
.... Access control lists Access control lists (ACLs) ensure that passed since the client was authorized. To view ACL configuration examples, see Access control lists (ACLs) on page 768. The IP address of traffic are used to reach network resources. The interface the client is using. AV Line of the connected client. The user name (or guest ID) of Fully Managed Switches M4250 Series Main User Manual Table 160. The total number of bytes the client transmitted. Captive portal client statistics Field MAC Address...