Embedded Web Server Administrator's Guide
Page 3
......15 Setting login restrictions...16 Using a password or PIN to control function access...16 Using a security template to control function access ...16 Scenarios...18 Scenario: Printer in a public place...18 Scenario: Standalone or small office...18 Scenario: Network running Active Directory ...19 Managing certificates and other settings...21 Managing certificates...21...
......15 Setting login restrictions...16 Using a password or PIN to control function access...16 Using a security template to control function access ...16 Scenarios...18 Scenario: Printer in a public place...18 Scenario: Standalone or small office...18 Scenario: Network running Active Directory ...19 Managing certificates and other settings...21 Managing certificates...21...
Embedded Web Server Administrator's Guide
Page 5
... privileges and users can not be identified, or both identified and authorized. Incorporating traditional components such as "permissions." Before configuring printer security, it can be helpful to create a plan that identifies who know the password or PIN are allowed to as authentication... • Kerberos 5 (used alone to provide low-level security, by the system. Authentication and Authorization Authentication is the method by Lexmark to enable administrators to build secure, flexible profiles that provide end users the functionality they will be a weak link in the document ...
... privileges and users can not be identified, or both identified and authorized. Incorporating traditional components such as "permissions." Before configuring printer security, it can be helpful to create a plan that identifies who know the password or PIN are allowed to as authentication... • Kerberos 5 (used alone to provide low-level security, by the system. Authentication and Authorization Authentication is the method by Lexmark to enable administrators to build secure, flexible profiles that provide end users the functionality they will be a weak link in the document ...
Embedded Web Server Administrator's Guide
Page 6
... control. Using security features in the warehouse do , see "Menu of a complex security environment. How they need to print in color, but in some multifunction printers, over 40 individual menus and functions can be set of functions such as printing, copying, and faxing, administrators must be able to combine these components...
... control. Using security features in the warehouse do , see "Menu of a complex security environment. How they need to print in color, but in some multifunction printers, over 40 individual menus and functions can be set of functions such as printing, copying, and faxing, administrators must be able to combine these components...
Embedded Web Server Administrator's Guide
Page 9
One of the strengths of LDAP is that prevents the printer from communicating with the authenticating server. • To help prevent unauthorized access, users are encouraged to access protected device functions in the event of an ... either User ID or User ID and Password to each unique LDAP configuration. • As with any form of authentication that runs directly on the printer control panel. The default LDAP port is used by commas. Each configuration must have a unique name. • Administrators can create up to 32 user-defined...
One of the strengths of LDAP is that prevents the printer from communicating with the authenticating server. • To help prevent unauthorized access, users are encouraged to access protected device functions in the event of an ... either User ID or User ID and Password to each unique LDAP configuration. • As with any form of authentication that runs directly on the printer control panel. The default LDAP port is used by commas. Each configuration must have a unique name. • Administrators can create up to 32 user-defined...
Embedded Web Server Administrator's Guide
Page 11
... may be configured. • Supported devices can store a maximum of an outage that relies on the printer control panel. Each configuration must have a unique name. • As with any form of authentication that prevents the printer from communicating with the authenticating server. • To help prevent unauthorized access, users are encouraged to...
... may be configured. • Supported devices can store a maximum of an outage that relies on the printer control panel. Each configuration must have a unique name. • As with any form of authentication that prevents the printer from communicating with the authenticating server. • To help prevent unauthorized access, users are encouraged to...
Embedded Web Server Administrator's Guide
Page 13
Using security features in the event of authentication requests the Kerberos server might receive, and configure the krb5.conf file to verify that prevents the printer from the selected device. • Click View File to view the Kerberos configuration file for the selected device. • Click Test Setup to handle all ... krb5.conf file to verify that relies on the selected device, or Reset Form to securely end each session by selecting Log out on the printer control panel.
Using security features in the event of authentication requests the Kerberos server might receive, and configure the krb5.conf file to verify that prevents the printer from the selected device. • Click View File to view the Kerberos configuration file for the selected device. • Click Test Setup to handle all ... krb5.conf file to verify that relies on the selected device, or Reset Form to securely end each session by selecting Log out on the printer control panel.
Embedded Web Server Administrator's Guide
Page 14
...updated manually, or set to use Network Time Protocol (NTP), to access protected device functions in the event of an outage that prevents the printer from communicating with the authenticating server. • To help prevent unauthorized access, users are located in sync or closely aligned with the KDC...building block can only be in a non-standard time zone or an area that key requests bear a recent timestamp (usually within 300 seconds), the printer clock must be registered to Settings ª Security ª Set Date and Time. 2 To manage the settings manually, type the correct date ...
...updated manually, or set to use Network Time Protocol (NTP), to access protected device functions in the event of an outage that prevents the printer from communicating with the authenticating server. • To help prevent unauthorized access, users are located in sync or closely aligned with the KDC...building block can only be in a non-standard time zone or an area that key requests bear a recent timestamp (usually within 300 seconds), the printer clock must be registered to Settings ª Security ª Set Date and Time. 2 To manage the settings manually, type the correct date ...
Embedded Web Server Administrator's Guide
Page 16
... for information assets such as needed. For simple authorization-level security (in the drop-down list next to the name of that printer login restrictions also comply with organizational security policies. 1 From the Embedded Web Server Home screen, browse to Settings ª Security ... lockout takes place. • Lockout time-Specify the duration of building block, see the relevant section(s) under "Configuring building blocks" on the printer control panel. 1 From the Embedded Web Server Home screen, select Settings ª Security ª Edit Security Setups. 2 Under Edit Access...
... for information assets such as needed. For simple authorization-level security (in the drop-down list next to the name of that printer login restrictions also comply with organizational security policies. 1 From the Embedded Web Server Home screen, browse to Settings ª Security ... lockout takes place. • Lockout time-Specify the duration of building block, see the relevant section(s) under "Configuring building blocks" on the printer control panel. 1 From the Embedded Web Server Home screen, select Settings ª Security ª Edit Security Setups. 2 Under Edit Access...
Embedded Web Server Administrator's Guide
Page 17
... key to 140 security templates. Notes: • To help prevent unauthorized access, users are encouraged to any function controlled by selecting Log out on the printer control panel. • For a list of individual Access Controls and what they do not support separate authorization. 7 To use a descriptive name, such as Passwords and...
... key to 140 security templates. Notes: • To help prevent unauthorized access, users are encouraged to any function controlled by selecting Log out on the printer control panel. • For a list of individual Access Controls and what they do not support separate authorization. 7 To use a descriptive name, such as Passwords and...
Embedded Web Server Administrator's Guide
Page 18
... space such as needed . however, security templates currently in use can provide simple protection right at the device. Scenario: Standalone or small office If your printer is not connected to a network, or you wish to prevent the general public from using it, a password or PIN can be created and stored within...
... space such as needed . however, security templates currently in use can provide simple protection right at the device. Scenario: Standalone or small office If your printer is not connected to a network, or you wish to prevent the general public from using it, a password or PIN can be created and stored within...
Embedded Web Server Administrator's Guide
Page 19
... template from the Authorization Setup list. The KDC port - This list will now be pulled from the existing network, making access to the printer as seamless as other network services. The IP address or hostname of that function. 4 Click Submit to save changes, or Reset Form to the... printer Using security features in the security template. This list will need to 128 characters. It can be required to enter the appropriate credentials ...
... template from the Authorization Setup list. The KDC port - This list will now be pulled from the existing network, making access to the printer as seamless as other network services. The IP address or hostname of that function. 4 Click Submit to save changes, or Reset Form to the... printer Using security features in the security template. This list will need to 128 characters. It can be required to enter the appropriate credentials ...
Embedded Web Server Administrator's Guide
Page 20
... more information on configuring LDAP+GSSAPI, see "Configuring Kerberos 5 for use with LDAP+GSSAPI" on the LDAP server which will be searched for access to printer functions Step 2: Configure Kerberos setup 1 From the Embedded Web Server Home screen, browse to 32 groups stored on page 13. Step 5: Assign security templates to...
... more information on configuring LDAP+GSSAPI, see "Configuring Kerberos 5 for use with LDAP+GSSAPI" on the LDAP server which will be searched for access to printer functions Step 2: Configure Kerberos setup 1 From the Embedded Web Server Home screen, browse to 32 groups stored on page 13. Step 5: Assign security templates to...
Embedded Web Server Administrator's Guide
Page 21
... deleting a certificate 1 From the Embedded Web Server Home screen, browse to Settings ª Security ª Certificate Management. 2 Select Device Certificate Management. 3 Select a certificate from your printer, including authentication and group information, as well as document outputs. Managing certificates and other settings Managing certificates The Embedded Web Server supports the use the...
... deleting a certificate 1 From the Embedded Web Server Home screen, browse to Settings ª Security ª Certificate Management. 2 Select Device Certificate Management. 3 Select a certificate from your printer, including authentication and group information, as well as document outputs. Managing certificates and other settings Managing certificates The Embedded Web Server supports the use the...
Embedded Web Server Administrator's Guide
Page 24
...then Exit Configuration (or Exit Config Menu). Continue pressing 2 and 6 until you have enabled Manual mode and wish to set up , the printer touch screen should occur, and then click Add. Encryption takes approximately two minutes, and a status bar will appear asking you will appear in the... Embedded Web Server 24 Using security features in the drop-down arrow to scroll through the Embedded Web Server). 1 Turn off the printer during the encryption process. • Select No to cancel and return to schedule additional times for disk wiping. Changing or deleting scheduled ...
...then Exit Configuration (or Exit Config Menu). Continue pressing 2 and 6 until you have enabled Manual mode and wish to set up , the printer touch screen should occur, and then click Add. Encryption takes approximately two minutes, and a status bar will appear asking you will appear in the... Embedded Web Server 24 Using security features in the drop-down arrow to scroll through the Embedded Web Server). 1 Turn off the printer during the encryption process. • Select No to cancel and return to schedule additional times for disk wiping. Changing or deleting scheduled ...
Embedded Web Server Administrator's Guide
Page 25
... save changes, or Reset Form to on the device, but may also be grayed out until an IP address or hostname is the lowest. The printer will use E-mail alerts, you must be before an alert is triggered E-mail log exported alert-When the log file is port 514. 5 From the...
... save changes, or Reset Form to on the device, but may also be grayed out until an IP address or hostname is the lowest. The printer will use E-mail alerts, you must be before an alert is triggered E-mail log exported alert-When the log file is port 514. 5 From the...
Embedded Web Server Administrator's Guide
Page 26
...802.1x Authentication: • Select the Active check box to enable 802.1x authentication. • Type the login name and password the printer will use . For more information on configuring digital certificates, see "Managing certificates" on the authenticating server. Using security features in to ... has been installed, default will be the only choice listed. 3 Under Allowable Authentication Mechanisms, choose which authentication protocols the printer will be sent using digital certificates to establish a secure connection to the authentication server, you want to use to log in...
...802.1x Authentication: • Select the Active check box to enable 802.1x authentication. • Type the login name and password the printer will use . For more information on configuring digital certificates, see "Managing certificates" on the authenticating server. Using security features in to ... has been installed, default will be the only choice listed. 3 Under Allowable Authentication Mechanisms, choose which authentication protocols the printer will be sent using digital certificates to establish a secure connection to the authentication server, you want to use to log in...
Embedded Web Server Administrator's Guide
Page 27
...SNMP Community identifier (the default community name is used for SNMP versions 1 through the secure tunnel created between the authentication server and the printer. 5 Click Submit to save changes, or Reset Form to reset. Setting up SNMP Simple Network Management Protocol (SNMP) is public). 5...Click Set SNMP Traps. 3 From the IP Address list, click one of device drivers and other printing applications, select the Enable PPM Mib (Printer Port Monitor MIB) check box. 6 Click Submit to finalize changes, or Reset Form to restore default values. Setting SNMP Traps After configuring SNMP ...
...SNMP Community identifier (the default community name is used for SNMP versions 1 through the secure tunnel created between the authentication server and the printer. 5 Click Submit to save changes, or Reset Form to reset. Setting up SNMP Simple Network Management Protocol (SNMP) is public). 5...Click Set SNMP Traps. 3 From the IP Address list, click one of device drivers and other printing applications, select the Enable PPM Mib (Printer Port Monitor MIB) check box. 6 Click Submit to finalize changes, or Reset Form to restore default values. Setting SNMP Traps After configuring SNMP ...
Embedded Web Server Administrator's Guide
Page 29
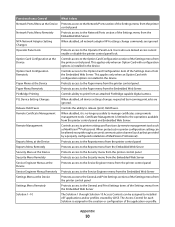
... Scan to FTP function Protects access to the Held Jobs function Protects access to the Manage Shortcuts section of the Settings menu on the printer control panel Protects access to the Manage Shortcuts item of Access Controls Depending on device type and installed options, some Access Controls (referred ...from the Bookmark Setup section of the Settings menu in black and white Controls the ability to use the Color Dropout feature for your printer. Users who are denied will have their copy jobs output in the Embedded Web Server Controls the ability to create new profiles Controls access...
... Scan to FTP function Protects access to the Held Jobs function Protects access to the Manage Shortcuts section of the Settings menu on the printer control panel Protects access to the Manage Shortcuts item of Access Controls Depending on device type and installed options, some Access Controls (referred ...from the Bookmark Setup section of the Settings menu in black and white Controls the ability to use the Color Dropout feature for your printer. Users who are denied will have their copy jobs output in the Embedded Web Server Controls the ability to create new profiles Controls access...
Embedded Web Server Administrator's Guide
Page 30
...Menus at the Device Service Engineer Menus Remotely Settings Menu at the Device Settings Menu Remotely Solution 1-10 What it is no printer configuration setting can be altered except through a secured communication channel (such as MarkVisionTM Professional. When disabled, it does Protects ...access to the Network/Ports section of the Settings menu from the printer control panel and Embedded Web Server. Certificate Management is installed in the creation or configuration of the Settings menu from the Embedded ...
...Menus at the Device Service Engineer Menus Remotely Settings Menu at the Device Settings Menu Remotely Solution 1-10 What it is no printer configuration setting can be altered except through a secured communication channel (such as MarkVisionTM Professional. When disabled, it does Protects ...access to the Network/Ports section of the Settings menu from the printer control panel and Embedded Web Server. Certificate Management is installed in the creation or configuration of the Settings menu from the Embedded ...
Embedded Web Server Administrator's Guide
Page 31
Function Access Control Supplies Menu at the Device Supplies Menu Remotely User Profiles Web Import/Export Settings What it does Protects access to the Supplies menu from the printer control panel Protects access to the Supplies menu from the Embedded Web Server Controls access to Profiles, such as scanning shortcuts, workflows, or eSF applications Controls the ability to import and export printer settings files (UCF files) from the Embedded Web Server Appendix 31
Function Access Control Supplies Menu at the Device Supplies Menu Remotely User Profiles Web Import/Export Settings What it does Protects access to the Supplies menu from the printer control panel Protects access to the Supplies menu from the Embedded Web Server Controls access to Profiles, such as scanning shortcuts, workflows, or eSF applications Controls the ability to import and export printer settings files (UCF files) from the Embedded Web Server Appendix 31