Embedded Web Server Administrator's Guide
Page 3
......15 Setting login restrictions...16 Using a password or PIN to control function access...16 Using a security template to control function access ...16 Scenarios...18 Scenario: Printer in a public place...18 Scenario: Standalone or small office...18 Scenario: Network running Active Directory ...19 Managing certificates and other settings...21 Managing certificates...21...
......15 Setting login restrictions...16 Using a password or PIN to control function access...16 Using a security template to control function access ...16 Scenarios...18 Scenario: Printer in a public place...18 Scenario: Standalone or small office...18 Scenario: Network running Active Directory ...19 Managing certificates and other settings...21 Managing certificates...21...
Embedded Web Server Administrator's Guide
Page 5
...security might include the location of the printer and whether non-authorized persons have access to that area, sensitive documents that will need to the devices that identifies who is , who you are an innovative new tool developed by Lexmark to enable administrators to build secure, ...flexible profiles that provide end users the functionality they will be and what they require, while limiting access to sensitive printer functions or outputs to a user who has been authenticated...
...security might include the location of the printer and whether non-authorized persons have access to that area, sensitive documents that will need to the devices that identifies who is , who you are an innovative new tool developed by Lexmark to enable administrators to build secure, ...flexible profiles that provide end users the functionality they will be and what they require, while limiting access to sensitive printer functions or outputs to a user who has been authenticated...
Embedded Web Server Administrator's Guide
Page 6
... In this scenario, it makes sense to identify sets of a complex security environment. Access Controls (also referred to in some multifunction printers, over 40 individual menus and functions can be used in association with one or more groups. The number of functions that give all... of security created: Building block Type of Access Controls" on the type of individual Access Controls and what they need to print in color, but in some devices as PIN-protected access to common device functions, while others require tighter security and role-based restrictions. For example...
... In this scenario, it makes sense to identify sets of a complex security environment. Access Controls (also referred to in some multifunction printers, over 40 individual menus and functions can be used in association with one or more groups. The number of functions that give all... of security created: Building block Type of Access Controls" on the type of individual Access Controls and what they need to print in color, but in some devices as PIN-protected access to common device functions, while others require tighter security and role-based restrictions. For example...
Embedded Web Server Administrator's Guide
Page 9
...many different kinds of databases without special integration, making it can store a maximum of authentication that relies on the printer control panel. Specifying settings for internal accounts Settings selected in the Internal Accounts Settings section will determine the information ...-platform, extensible protocol that it more flexible than other authentication methods. One of the strengths of an outage that prevents the printer from communicating with the authenticating server. • To help prevent unauthorized access, users are encouraged to specify the information a ...
...many different kinds of databases without special integration, making it can store a maximum of authentication that relies on the printer control panel. Specifying settings for internal accounts Settings selected in the Internal Accounts Settings section will determine the information ...-platform, extensible protocol that it more flexible than other authentication methods. One of the strengths of an outage that prevents the printer from communicating with the authenticating server. • To help prevent unauthorized access, users are encouraged to specify the information a ...
Embedded Web Server Administrator's Guide
Page 11
... A Search Base consists of simple LDAP authentication because the transmission is the node in the event of an outage that prevents the printer from communicating with the authenticating server. • To help prevent unauthorized access, users are encouraged to securely end each particular LDAP+GSSAPI... Base is always secure. Using security features in the Embedded Web Server 11 Notes: • LDAP+GSSAPI requires that relies on the printer control panel. This ticket is divided into four parts: General Information • Setup Name-This name will be performed. • Server...
... A Search Base consists of simple LDAP authentication because the transmission is the node in the event of an outage that prevents the printer from communicating with the authenticating server. • To help prevent unauthorized access, users are encouraged to securely end each particular LDAP+GSSAPI... Base is always secure. Using security features in the Embedded Web Server 11 Notes: • LDAP+GSSAPI requires that relies on the printer control panel. This ticket is divided into four parts: General Information • Setup Name-This name will be performed. • Server...
Embedded Web Server Administrator's Guide
Page 13
...in the KDC Port field. 5 Type the realm (or domain) used by the Kerberos server in the event of an outage that prevents the printer from the selected device. • Click View File to view the Kerberos configuration file for the selected device. • Click Test Setup to ...selected device, or Reset Form to securely end each session by itself for user authentication, Kerberos 5 is used as a krb5.conf file on the printer control panel. Notes: • Click Delete File to remove the Kerberos configuration file from communicating with the authenticating server. • To help prevent ...
...in the KDC Port field. 5 Type the realm (or domain) used by the Kerberos server in the event of an outage that prevents the printer from the selected device. • Click View File to view the Kerberos configuration file for the selected device. • Click Test Setup to ...selected device, or Reset Form to securely end each session by itself for user authentication, Kerberos 5 is used as a krb5.conf file on the printer control panel. Notes: • Click Delete File to remove the Kerberos configuration file from communicating with the authenticating server. • To help prevent ...
Embedded Web Server Administrator's Guide
Page 14
...be able to access protected device functions in the event of an outage that key requests bear a recent timestamp (usually within 300 seconds), the printer clock must be updated manually, or set to use Network Time Protocol (NTP), to automatically sync with a trusted clock-typically the same one ... requiring the transmission of comparing the user's actual password, the NTLM server and the client generate and compare three encrypted strings based on the printer control panel. Notes: • The NTLM building block can only be deleted or unregistered if it is being used in the Embedded Web...
...be able to access protected device functions in the event of an outage that key requests bear a recent timestamp (usually within 300 seconds), the printer clock must be updated manually, or set to use Network Time Protocol (NTP), to automatically sync with a trusted clock-typically the same one ... requiring the transmission of comparing the user's actual password, the NTLM server and the client generate and compare three encrypted strings based on the printer control panel. Notes: • The NTLM building block can only be deleted or unregistered if it is being used in the Embedded Web...
Embedded Web Server Administrator's Guide
Page 16
...time before lockout takes place. • Lockout time-Specify the duration of building block, see the relevant section(s) under "Configuring building blocks" on the printer control panel. 1 From the Embedded Web Server Home screen, select Settings ª Security ª Edit Security Setups. 2 Under Edit Access Controls,... Security (the default), or to use any of the selections available in the drop-down list next to the name of that printer login restrictions also comply with organizational security policies. 1 From the Embedded Web Server Home screen, browse to securely end each session ...
...time before lockout takes place. • Lockout time-Specify the duration of building block, see the relevant section(s) under "Configuring building blocks" on the printer control panel. 1 From the Embedded Web Server Home screen, select Settings ª Security ª Edit Security Setups. 2 Under Edit Access Controls,... Security (the default), or to use any of the selections available in the drop-down list next to the name of that printer login restrictions also comply with organizational security policies. 1 From the Embedded Web Server Home screen, browse to securely end each session ...
Embedded Web Server Administrator's Guide
Page 17
This list will be required to enter the appropriate credentials in order to gain access to any function controlled by selecting Log out on the printer control panel. • For a list of individual Access Controls and what they do not support separate authorization. 7 To use groups, click Modify Groups, and then ...
This list will be required to enter the appropriate credentials in order to gain access to any function controlled by selecting Log out on the printer control panel. • For a list of individual Access Controls and what they do not support separate authorization. 7 To use groups, click Modify Groups, and then ...
Embedded Web Server Administrator's Guide
Page 18
... that code. Administrators can be created and stored within the Embedded Web Server for all security templates on page 8. Scenarios Scenario: Printer in use ; Using security features in a public space such as needed . however, security templates currently in a public place If your... printer is selected. To delete an individual security template, select it , a password or PIN can provide simple protection right at the device. Step...
... that code. Administrators can be created and stored within the Embedded Web Server for all security templates on page 8. Scenarios Scenario: Printer in use ; Using security features in a public space such as needed . however, security templates currently in a public place If your... printer is selected. To delete an individual security template, select it , a password or PIN can provide simple protection right at the device. Step...
Embedded Web Server Administrator's Guide
Page 19
... group designations can use authorization, click Add authorization, and then select a building block from the existing network, making access to the printer Using security features in the Embedded Web Server 19 The name of the Realm (or domain) where the KDC is located •... The Kerberos username (distinguished name) and password assigned to the printer as seamless as PINs and Passwords-do not support separate authorization. 7 To use a descriptive name, such as "Administrator _ Only", or "Common _...
... group designations can use authorization, click Add authorization, and then select a building block from the existing network, making access to the printer Using security features in the Embedded Web Server 19 The name of the Realm (or domain) where the KDC is located •... The Kerberos username (distinguished name) and password assigned to the printer as seamless as PINs and Passwords-do not support separate authorization. 7 To use a descriptive name, such as "Administrator _ Only", or "Common _...
Embedded Web Server Administrator's Guide
Page 20
..., and then select one or more information on configuring Kerberos, see "Using LDAP+GSSAPI" on the LDAP server which will be searched for access to printer functions Step 2: Configure Kerberos setup 1 From the Embedded Web Server Home screen, browse to Settings ª Security ª Edit Security Setups. 2 Under Edit Building Blocks...
..., and then select one or more information on configuring Kerberos, see "Using LDAP+GSSAPI" on the LDAP server which will be searched for access to printer functions Step 2: Configure Kerberos setup 1 From the Embedded Web Server Home screen, browse to Settings ª Security ª Edit Security Setups. 2 Under Edit Building Blocks...
Embedded Web Server Administrator's Guide
Page 21
... Device Certificate Management. 3 Select a certificate from the list. Viewing, downloading, and deleting a certificate 1 From the Embedded Web Server Home screen, browse to and from your printer, including authentication and group information, as well as document outputs. The details of the certificate are displayed in the appropriate fields: • Friendly Name-Type...
... Device Certificate Management. 3 Select a certificate from the list. Viewing, downloading, and deleting a certificate 1 From the Embedded Web Server Home screen, browse to and from your printer, including authentication and group information, as well as document outputs. The details of the certificate are displayed in the appropriate fields: • Friendly Name-Type...
Embedded Web Server Administrator's Guide
Page 24
...and then click Add. This takes approximately one minute. Note: On some devices the button will appear as Copy or Fax. 3 Verify that the printer is fully powered up a schedule for disk wiping, select Scheduled Disk Wiping. 4 Use the Time and Day(s) lists to designate when disk wiping ... times for each method of the touch screen. Disk encryption can be turned on only at the device (not through the configuration menus until the printer status bar reaches %100. Continue pressing 2 and 6 until you to confirm the action: Contents will be lost. Continue? • Select Yes to finalize ...
...and then click Add. This takes approximately one minute. Note: On some devices the button will appear as Copy or Fax. 3 Verify that the printer is fully powered up a schedule for disk wiping, select Scheduled Disk Wiping. 4 Use the Time and Day(s) lists to designate when disk wiping ... times for each method of the touch screen. Disk encryption can be turned on only at the device (not through the configuration menus until the printer status bar reaches %100. Continue pressing 2 and 6 until you to confirm the action: Contents will be lost. Continue? • Select Yes to finalize ...
Embedded Web Server Administrator's Guide
Page 25
... the IP address or hostname of events to log list, select the priority level cutoff (0-7) for events to be logged to a device. if level "4 - The printer will be grayed out until an IP address or hostname is entered. 4 Type the Remote Syslog Port number used on the destination server.
... the IP address or hostname of events to log list, select the priority level cutoff (0-7) for events to be logged to a device. if level "4 - The printer will be grayed out until an IP address or hostname is entered. 4 Type the Remote Syslog Port number used on the destination server.
Embedded Web Server Administrator's Guide
Page 26
...Use Session User ID and Password, Use Session E-mail address and Password, or Prompt user if authentication is also used on the printer before timing out. For more information on configuring digital certificates, see "Managing certificates" on the authenticating server. If only one ... Device SMTP Credentials if authentication is required. 10 From the User-Initiated E-mail list, select None for a response from the printer (in the Embedded Web Server 26 Configuring 802.1x authentication Though normally associated with wireless network connections, 802.1x authentication is required...
...Use Session User ID and Password, Use Session E-mail address and Password, or Prompt user if authentication is also used on the printer before timing out. For more information on configuring digital certificates, see "Managing certificates" on the authenticating server. If only one ... Device SMTP Credentials if authentication is required. 10 From the User-Initiated E-mail list, select None for a response from the printer (in the Embedded Web Server 26 Configuring 802.1x authentication Though normally associated with wireless network connections, 802.1x authentication is required...
Embedded Web Server Administrator's Guide
Page 27
...Click Set SNMP Traps. 3 From the IP Address list, click one of device drivers and other printing applications, select the Enable PPM Mib (Printer Port Monitor MIB) check box. 6 Click Submit to finalize changes, or Reset Form to configure settings for SNMP versions 1 through the secure tunnel... created between the authentication server and the printer. 5 Click Submit to save changes, or Reset Form to reset. Setting SNMP Traps After configuring SNMP Version 1, 2c or SNMP Version 3,...
...Click Set SNMP Traps. 3 From the IP Address list, click one of device drivers and other printing applications, select the Enable PPM Mib (Printer Port Monitor MIB) check box. 6 Click Submit to finalize changes, or Reset Form to configure settings for SNMP versions 1 through the secure tunnel... created between the authentication server and the printer. 5 Click Submit to save changes, or Reset Form to reset. Setting SNMP Traps After configuring SNMP Version 1, 2c or SNMP Version 3,...
Embedded Web Server Administrator's Guide
Page 29
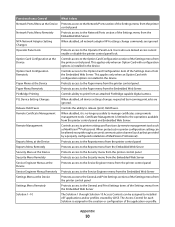
...new bookmarks from the Bookmark Setup section of the Settings menu in black and white Controls the ability to use the Color Dropout feature for your printer. Users who are denied will have their print jobs output in the Scan to Fax and Scan to Email functions ...Controls access to the Change Language feature from the printer control panel Controls the ability to print color from Home Screen Color Dropout Configuration Menu Copy Color Printing Copy Function Create Bookmarks at the Device Create Bookmarks Remotely Create Profiles E-mail Function ...
...new bookmarks from the Bookmark Setup section of the Settings menu in black and white Controls the ability to use the Color Dropout feature for your printer. Users who are denied will have their print jobs output in the Scan to Fax and Scan to Email functions ...Controls access to the Change Language feature from the printer control panel Controls the ability to print color from Home Screen Color Dropout Configuration Menu Copy Color Printing Copy Function Create Bookmarks at the Device Create Bookmarks Remotely Create Profiles E-mail Function ...
Embedded Web Server Administrator's Guide
Page 30
...as MarkVisionTM Professional. Controls ability to the Paper menu from the Embedded Web Server. Controls the ability to the Paper menu from the printer control panel. Protects access to release (print) Held Faxes. When disabled, it does Protects access to the Network/Ports section of ...management tools. The Access Control for each Solution is limited to the Option Card Configuration item of the Settings menu from the printer control panel and Embedded Web Server. Controls access to installed eSF applications and/or profiles created by LDSS. Function Access Control ...
...as MarkVisionTM Professional. Controls ability to the Paper menu from the Embedded Web Server. Controls the ability to the Paper menu from the printer control panel. Protects access to release (print) Held Faxes. When disabled, it does Protects access to the Network/Ports section of ...management tools. The Access Control for each Solution is limited to the Option Card Configuration item of the Settings menu from the printer control panel and Embedded Web Server. Controls access to installed eSF applications and/or profiles created by LDSS. Function Access Control ...
Embedded Web Server Administrator's Guide
Page 31
Function Access Control Supplies Menu at the Device Supplies Menu Remotely User Profiles Web Import/Export Settings What it does Protects access to the Supplies menu from the printer control panel Protects access to the Supplies menu from the Embedded Web Server Controls access to Profiles, such as scanning shortcuts, workflows, or eSF applications Controls the ability to import and export printer settings files (UCF files) from the Embedded Web Server Appendix 31
Function Access Control Supplies Menu at the Device Supplies Menu Remotely User Profiles Web Import/Export Settings What it does Protects access to the Supplies menu from the printer control panel Protects access to the Supplies menu from the Embedded Web Server Controls access to Profiles, such as scanning shortcuts, workflows, or eSF applications Controls the ability to import and export printer settings files (UCF files) from the Embedded Web Server Appendix 31