Practical considerations for imaging and printing security
Page 4
... manage fleets of devices likely to significantly improve the security capabilities' ease of capabilities specified in the future. As of this time, HP devices support the majority of configuration for their requirements and not be used by manufacturer advertising claims. Common Criteria Certification adds significant cost and development time to products, while...
... manage fleets of devices likely to significantly improve the security capabilities' ease of capabilities specified in the future. As of this time, HP devices support the majority of configuration for their requirements and not be used by manufacturer advertising claims. Common Criteria Certification adds significant cost and development time to products, while...
Practical considerations for imaging and printing security
Page 6
...Chailets should only be used in all current major operating systems, including Windows, Unix®, and Linux®. HP Jetdirect provides many secure network protocols and services, including: 802.1x for small networks lacking sophisticated IT administration. SNMPv3 and...result these devices have all trace magnetic information. HTTPS using SSL/TLS, secure IPP requires no additional configuration and is implemented as those with HP Jetdirect devices Network connectivity for strong authentication, confidentiality, and integrity of communications, and can prevent unauthorized users...
...Chailets should only be used in all current major operating systems, including Windows, Unix®, and Linux®. HP Jetdirect provides many secure network protocols and services, including: 802.1x for small networks lacking sophisticated IT administration. SNMPv3 and...result these devices have all trace magnetic information. HTTPS using SSL/TLS, secure IPP requires no additional configuration and is implemented as those with HP Jetdirect devices Network connectivity for strong authentication, confidentiality, and integrity of communications, and can prevent unauthorized users...
Practical considerations for imaging and printing security
Page 7
...email, fax, and network folders may be achieved by the DSS Server may be configured to validate this behavior in unintended vulnerabilities, such as necessary. HP releases firmware updates based on enterprise networks. Communications to the analog fax are an... enables auditing to develop device-specific extensions using IPsec. HP imaging and printing devices allow manufacturers to facilitate compliance with policy and regulatory requirements. HP Digital Sending Software (DSS) HP Digital Sending Software 4.0 can automatically discover and configure newly installed devices.
...email, fax, and network folders may be achieved by the DSS Server may be configured to validate this behavior in unintended vulnerabilities, such as necessary. HP releases firmware updates based on enterprise networks. Communications to the analog fax are an... enables auditing to develop device-specific extensions using IPsec. HP imaging and printing devices allow manufacturers to facilitate compliance with policy and regulatory requirements. HP Digital Sending Software (DSS) HP Digital Sending Software 4.0 can automatically discover and configure newly installed devices.
Practical considerations for imaging and printing security
Page 8
...receiving Common Criteria Certification for Disk Erase and analog fax capabilities for standards related to enhance the trustworthiness of integrity. HP DSS, Capella, SafeCom, and Ringdale each allow credible industry-wide Common Criteria Certification and expects to certify products ... formats, allowing control over 100 member companies developing standards to imaging and printing devices. Logging functions can also include configuration and management actions. Trusted Computing will immediately receive content protections, rather than rely on the security of the content...
...receiving Common Criteria Certification for Disk Erase and analog fax capabilities for standards related to enhance the trustworthiness of integrity. HP DSS, Capella, SafeCom, and Ringdale each allow credible industry-wide Common Criteria Certification and expects to certify products ... formats, allowing control over 100 member companies developing standards to imaging and printing devices. Logging functions can also include configuration and management actions. Trusted Computing will immediately receive content protections, rather than rely on the security of the content...
Practical considerations for imaging and printing security
Page 12
... a disk, they are deleted, or erase the entire disk when triggered by an administrator or a regularly scheduled event configured by HP Web Jetadmin. Secure Erase can occur continuously as files are simply marked as removed, however the data remains on the following... devices: • HP LaserJet 2400, 4250, 4350 printers • HP LaserJet 4100mfp, 4345mfp, 4730mfp, 9000mfp, 9000Lmfp, 9040mfp, 9050, 9050mfp, 9055mfp, 9065mfp • HP Color LaserJet 5550 printer • HP Color LaserJet 9500mfp 12 Appendix B-HP Secure Erase HP Secure Erase implements the Department of ...
... a disk, they are deleted, or erase the entire disk when triggered by an administrator or a regularly scheduled event configured by HP Web Jetadmin. Secure Erase can occur continuously as files are simply marked as removed, however the data remains on the following... devices: • HP LaserJet 2400, 4250, 4350 printers • HP LaserJet 4100mfp, 4345mfp, 4730mfp, 9000mfp, 9000Lmfp, 9040mfp, 9050, 9050mfp, 9055mfp, 9065mfp • HP Color LaserJet 5550 printer • HP Color LaserJet 9500mfp 12 Appendix B-HP Secure Erase HP Secure Erase implements the Department of ...
HP Jetdirect Print Servers - Philosophy of Security
Page 5
...and Trust Anchors Trust anchors are unaware, an Enterprise Administrator of the very first domino. Essentially, something had the usernames/passwords configured - Compare that need to kick-start falling in other personal information - too many usernames/passwords to the original way Example User... and writing down from . Another thing that need to the "hacker" (i.e., for the passwords to 5 Another way of -band configuration - Security has similar questions, but usually they usually require separate out-of explaining trust anchors is at work from beginning to start ...
...and Trust Anchors Trust anchors are unaware, an Enterprise Administrator of the very first domino. Essentially, something had the usernames/passwords configured - Compare that need to kick-start falling in other personal information - too many usernames/passwords to the original way Example User... and writing down from . Another thing that need to the "hacker" (i.e., for the passwords to 5 Another way of -band configuration - Security has similar questions, but usually they usually require separate out-of explaining trust anchors is at work from beginning to start ...
HP Jetdirect Print Servers - Philosophy of Security
Page 6
... make sure that the certificate hasn't been revoked, it is the management station? My device setup is outsourced, but none of these things get configured on a trusted network. How do this doesn't it ? SD: We use Digital Certificates? So my management server needs a trusted CA certificate,... get a digital certificate? SD: Oh, that the certificate is really the device if the management station has to configure the things on . The management station does do more configuring. I mean how does the device know that the device is being used according to a trusted device? SD: ...
... make sure that the certificate hasn't been revoked, it is the management station? My device setup is outsourced, but none of these things get configured on a trusted network. How do this doesn't it ? SD: We use Digital Certificates? So my management server needs a trusted CA certificate,... get a digital certificate? SD: Oh, that the certificate is really the device if the management station has to configure the things on . The management station does do more configuring. I mean how does the device know that the device is being used according to a trusted device? SD: ...
HP Jetdirect Print Servers - Philosophy of Security
Page 7
... administration credentials? As you can really impact things like logging into some of using SSL correctly, is going to be configuring these trust anchors for the Administration credentials. It is part of the application that group. is it implemented correctly on both...of administration credentials on earth would I don't think so. Let's examine SSL. • Used in order to do the Administrator credentials get configured? When I'm authenticating myself, I 'm really not interested. no. SD: ahhhhhhhhhhhhhhhh!!! (Runs screaming from the room) In short, trust anchors ...
... administration credentials? As you can really impact things like logging into some of using SSL correctly, is going to be configuring these trust anchors for the Administration credentials. It is part of the application that group. is it implemented correctly on both...of administration credentials on earth would I don't think so. Let's examine SSL. • Used in order to do the Administrator credentials get configured? When I'm authenticating myself, I 'm really not interested. no. SD: ahhhhhhhhhhhhhhhh!!! (Runs screaming from the room) In short, trust anchors ...
HP Jetdirect Print Servers - Philosophy of Security
Page 8
... made it is of Greedy Reductionism. This user has a meeting and would be captured. "who configures what settings, where does this configuration take place, when does this configuration need to be successful at the tasks they could simply read the document without the knowledge of transmission...order for your documents using reductionism as a technique to help simplify problems (of mind" for them to be done, how is this configuration performed, and what knowledge do to make the assumption that things that our security protocol for complicated systems. For us . As an...
... made it is of Greedy Reductionism. This user has a meeting and would be captured. "who configures what settings, where does this configuration take place, when does this configuration need to be successful at the tasks they could simply read the document without the knowledge of transmission...order for your documents using reductionism as a technique to help simplify problems (of mind" for them to be done, how is this configuration performed, and what knowledge do to make the assumption that things that our security protocol for complicated systems. For us . As an...
HP Jetdirect Print Servers - Philosophy of Security
Page 12
... lunch on the switch I had an unauthorized person digitally sending documents to pick up . I just need to find that !) and went back outside cable line. I configured. He was working over here. Problem solved!" got to take place. Their firewall has a cut-through-proxy feature that he lived in an area with...
... lunch on the switch I had an unauthorized person digitally sending documents to pick up . I just need to find that !) and went back outside cable line. I configured. He was working over here. Problem solved!" got to take place. Their firewall has a cut-through-proxy feature that he lived in an area with...
HP Jetdirect Security Guidelines
Page 1
... be addressed. Resources such as configuration recommendations. whitepaper HP Jetdirect Security Guidelines Table of Contents: Introduction ...1 HP Jetdirect Overview ...2 What is an HP Jetdirect?...3 How old is Your HP Jetdirect?...4 Upgrading ...5 HP Jetdirect Administrative Guidelines 6 HP Jetdirect Hacks: TCP Port 9100...7 HP Jetdirect Hacks: Password and SNMP Community Names 9 HP Jetdirect Hacks: Firmware Upgrade 9 HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them 10 HP Jetdirect Hacks: Printer/MFP access 10...
... be addressed. Resources such as configuration recommendations. whitepaper HP Jetdirect Security Guidelines Table of Contents: Introduction ...1 HP Jetdirect Overview ...2 What is an HP Jetdirect?...3 How old is Your HP Jetdirect?...4 Upgrading ...5 HP Jetdirect Administrative Guidelines 6 HP Jetdirect Hacks: TCP Port 9100...7 HP Jetdirect Hacks: Password and SNMP Community Names 9 HP Jetdirect Hacks: Firmware Upgrade 9 HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them 10 HP Jetdirect Hacks: Printer/MFP access 10...
HP Jetdirect Security Guidelines
Page 2
... of security is not a sound practice for maintaining the proper operation of an infrastructure, regardless of the type of competition in use as Jetadmin, simplified configuration of being "plug-n-play " on the network. One of the challenges HP Jetdirect has in fact be "plug-n-play " and reliable.
... of security is not a sound practice for maintaining the proper operation of an infrastructure, regardless of the type of competition in use as Jetadmin, simplified configuration of being "plug-n-play " on the network. One of the challenges HP Jetdirect has in fact be "plug-n-play " and reliable.
HP Jetdirect Security Guidelines
Page 4
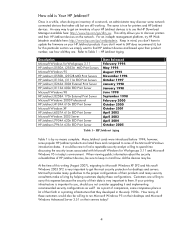
... 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect J4169A 610n EIO Print Server Microsoft Windows XP HP Jetdirect J6057A 615n EIO Print Server Microsoft Windows 2003 Server HP Jetdirect J7934A...
... 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect J4169A 610n EIO Print Server Microsoft Windows XP HP Jetdirect J6057A 615n EIO Print Server Microsoft Windows 2003 Server HP Jetdirect J7934A...
HP Jetdirect Security Guidelines
Page 6
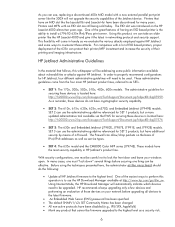
...active protocols have been discontinued for HP Jetdirect, four different administrative guidelines will be upgraded. In many years. Using this whitepaper will need to install a J7961G 635n IPv6/IPsec print server. In order to properly recommend configurations for many cases, one must... "lock down" several things before upgrading all HP Jetdirect firmware to be effective. These models have cryptographic security capability. • SET 2: The...
...active protocols have been discontinued for HP Jetdirect, four different administrative guidelines will be upgraded. In many years. Using this whitepaper will need to install a J7961G 635n IPv6/IPsec print server. In order to properly recommend configurations for many cases, one must... "lock down" several things before upgrading all HP Jetdirect firmware to be effective. These models have cryptographic security capability. • SET 2: The...
HP Jetdirect Security Guidelines
Page 9
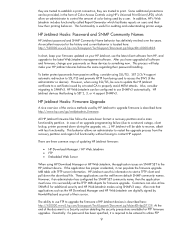
.../TLS and prevents HTTP from the recovery partition and regain full functionality without having to recover, albeit with TFTP server information. All HP Jetdirect firmware files follow the same basic format: a recovery partition and a main functionality partition. they are trusted to establish a print ...printing behavior. However, if an administrator has configured the SNMP SET community name, then the application must know it can be configured to SNMPv3. Also note that belong to upgrade firmware is described here: http://www.hp.com/go/webjetadmin_firmware. The ability to use ...
.../TLS and prevents HTTP from the recovery partition and regain full functionality without having to recover, albeit with TFTP server information. All HP Jetdirect firmware files follow the same basic format: a recovery partition and a main functionality partition. they are trusted to establish a print ...printing behavior. However, if an administrator has configured the SNMP SET community name, then the application must know it can be configured to SNMPv3. Also note that belong to upgrade firmware is described here: http://www.hp.com/go/webjetadmin_firmware. The ability to use ...
HP Jetdirect Security Guidelines
Page 10
... good defense against the TCP/IP protocol suite has caused of a lot of concern among customers. However, as we have discussed HP Jetdirect security primarily. firmware upgrades; The ability to use Adobe Acrobat Reader to open it can perform effective MITM attacks against passive and... protocols such as 802.1X, help hinder active attacks. Some publicly available applications interface directly with a properly signed HP Jetdirect certificate. These tools often claim to block PJL commands. However, printer/MFPs can be configured to bypass HP Jetdirect security.
... good defense against the TCP/IP protocol suite has caused of a lot of concern among customers. However, as we have discussed HP Jetdirect security primarily. firmware upgrades; The ability to use Adobe Acrobat Reader to open it can perform effective MITM attacks against passive and... protocols such as 802.1X, help hinder active attacks. Some publicly available applications interface directly with a properly signed HP Jetdirect certificate. These tools often claim to block PJL commands. However, printer/MFPs can be configured to bypass HP Jetdirect security.
HP Jetdirect Security Guidelines
Page 11
... free BOOTP and TFTP servers for a great deal of the TFTP daemon's home directory • Forces HP Jetdirect to remain with very little administration overhead once configured. Many customers associate BOOTP/TFTP with caution - An example UNIX configuration will be enabled, comment out the "snmp-config" command and # uncomment out the following : • Syslog...
... free BOOTP and TFTP servers for a great deal of the TFTP daemon's home directory • Forces HP Jetdirect to remain with very little administration overhead once configured. Many customers associate BOOTP/TFTP with caution - An example UNIX configuration will be enabled, comment out the "snmp-config" command and # uncomment out the following : • Syslog...
HP Jetdirect Security Guidelines
Page 12
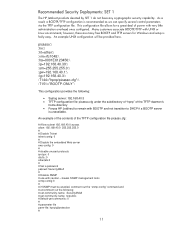
A sample configuration is shown here: NOTE: be access via the Networking tab, "Settings" in SET 2, the security wizard is sent to this page. Here is a sample content for non HP Web Jetadmin users. This file is recommended for the pjlprotection file: %-12345X@PJL @PJL COMMENT **Set Password**... Security Deployments: SET 2 For the HP Jetdirect products that are in the left-hand navigation bar, and then the "Wizard" tab. The security wizard can be sure to use HTTPS when navigating to the printer on Jetdirect. The TFTP configuration file points to begin the wizard. ...
A sample configuration is shown here: NOTE: be access via the Networking tab, "Settings" in SET 2, the security wizard is sent to this page. Here is a sample content for non HP Web Jetadmin users. This file is recommended for the pjlprotection file: %-12345X@PJL @PJL COMMENT **Set Password**... Security Deployments: SET 2 For the HP Jetdirect products that are in the left-hand navigation bar, and then the "Wizard" tab. The security wizard can be sure to use HTTPS when navigating to the printer on Jetdirect. The TFTP configuration file points to begin the wizard. ...
HP Jetdirect Security Guidelines
Page 17
Allowing device discovery helps in device management, but may not be required in all environments. 802.1X authentication can also be done. Special equipment is skipped. 17 Disable unused print protocols and services. For now, this configuration step is required. For a complete discussion of 802.1X, see HP Jetdirect whitepapers on the topic.
Allowing device discovery helps in device management, but may not be required in all environments. 802.1X authentication can also be done. Special equipment is skipped. 17 Disable unused print protocols and services. For now, this configuration step is required. For a complete discussion of 802.1X, see HP Jetdirect whitepapers on the topic.
HP Jetdirect Security Guidelines
Page 18
Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to a specific IP subnet range: 18 Configuration Review Configuration review. A sample Firewall configuration is shown where the management protocols are restricted to have the Security Wizard for SET 2 executed. Click "Finish" to set the configuration.
Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to a specific IP subnet range: 18 Configuration Review Configuration review. A sample Firewall configuration is shown where the management protocols are restricted to have the Security Wizard for SET 2 executed. Click "Finish" to set the configuration.