Practical considerations for imaging and printing security
Page 4
...security framework To simplify the presentation of security concepts, HP developed an imaging and printing security framework with three categories of security functions: Secure the Device Includes elements that facilitate security configuration of devices likely to develop checklists that protect the... these security checklists for public review at http://csrc.nist.gov/checklists. As of this time, HP devices support the majority of configuration for compliance to securely manage fleets of individual manufacturers. Conclusion: look beyond Common Criteria Certification Ultimately,...
...security framework To simplify the presentation of security concepts, HP developed an imaging and printing security framework with three categories of security functions: Secure the Device Includes elements that facilitate security configuration of devices likely to develop checklists that protect the... these security checklists for public review at http://csrc.nist.gov/checklists. As of this time, HP devices support the majority of configuration for compliance to securely manage fleets of individual manufacturers. Conclusion: look beyond Common Criteria Certification Ultimately,...
Practical considerations for imaging and printing security
Page 6
...security of management communications and is used for secure management using SSL/TLS, secure IPP requires no additional configuration and is important to evolve, HP ensures its partners. DoD 5220-22m specifies an algorithm to repetitively overwrite hard disk data sectors to -...denied. 802.1x can secure network printing and scanning protocols. Vulnerabilities, viruses, and worms Vulnerability assessments are allowed access. The HP Jetdirect 635n IPv6/IPsec and Gigabit Ethernet internal print server, available November 2005, uses a cryptographic accelerator to provide click-to remove ...
...security of management communications and is used for secure management using SSL/TLS, secure IPP requires no additional configuration and is important to evolve, HP ensures its partners. DoD 5220-22m specifies an algorithm to repetitively overwrite hard disk data sectors to -...denied. 802.1x can secure network printing and scanning protocols. Vulnerabilities, viruses, and worms Vulnerability assessments are allowed access. The HP Jetdirect 635n IPv6/IPsec and Gigabit Ethernet internal print server, available November 2005, uses a cryptographic accelerator to provide click-to remove ...
Practical considerations for imaging and printing security
Page 7
...secure network. Protocols and services that are unused often go ignored, resulting in the HP LaserJet 4345mfp and 4730mfp. Firmware updates Firmware updates can automatically discover and configure newly installed devices. To control email distribution, the SMTP server used by securing the... network communications between the MFP and the DSS Server. Communications to an internal network. HP releases firmware updates based on ...
...secure network. Protocols and services that are unused often go ignored, resulting in the HP LaserJet 4345mfp and 4730mfp. Firmware updates Firmware updates can automatically discover and configure newly installed devices. To control email distribution, the SMTP server used by securing the... network communications between the MFP and the DSS Server. Communications to an internal network. HP releases firmware updates based on ...
Practical considerations for imaging and printing security
Page 8
... the standard when available. Trusted Computing will immediately receive content protections, rather than the security of computing equipment. HP DSS, Capella, SafeCom, and Ringdale each allow credible industry-wide Common Criteria Certification and expects to certify products... PC-devices to be monitored. Logging functions can also include configuration and management actions. Logging device activity Logging device activities ensures compliance to the devices themselves. Common Criteria Certification HP is a standards organization with a greater level of content after...
... the standard when available. Trusted Computing will immediately receive content protections, rather than the security of computing equipment. HP DSS, Capella, SafeCom, and Ringdale each allow credible industry-wide Common Criteria Certification and expects to certify products... PC-devices to be monitored. Logging functions can also include configuration and management actions. Logging device activity Logging device activities ensures compliance to the devices themselves. Common Criteria Certification HP is a standards organization with a greater level of content after...
Practical considerations for imaging and printing security
Page 12
... LaserJet 9500mfp 12 Typically when files are deleted, or erase the entire disk when triggered by an administrator or a regularly scheduled event configured by HP Web Jetadmin. Appendix B-HP Secure Erase HP Secure Erase implements the Department of Defense (DoD) specification 5220-22m algorithm for the deletion of the disk data to ensure no...
... LaserJet 9500mfp 12 Typically when files are deleted, or erase the entire disk when triggered by an administrator or a regularly scheduled event configured by HP Web Jetadmin. Appendix B-HP Secure Erase HP Secure Erase implements the Department of Defense (DoD) specification 5220-22m algorithm for the deletion of the disk data to ensure no...
HP Jetdirect Print Servers - Philosophy of Security
Page 5
... them with many privileges). We are those readers who are about trust anchors because they are unaware, an Enterprise Administrator of -band configuration - You can even begin - Domain: EXAMPLE Email: [email protected] Intranet Web Server Login: Example_User Password: WOW!I'mAnEntAdminForExample!!! What ...first approach. Another way of the very first domino. Essentially, something had to realize their database had the usernames/passwords configured - Compare that probably use message. In short, Example User needs to go back to the original way Example User had...
... them with many privileges). We are those readers who are about trust anchors because they are unaware, an Enterprise Administrator of -band configuration - You can even begin - Domain: EXAMPLE Email: [email protected] Intranet Web Server Login: Example_User Password: WOW!I'mAnEntAdminForExample!!! What ...first approach. Another way of the very first domino. Essentially, something had to realize their database had the usernames/passwords configured - Compare that probably use message. In short, Example User needs to go back to the original way Example User had...
HP Jetdirect Print Servers - Philosophy of Security
Page 6
...hasn't been revoked, it has to make sure that the management station's certificate is on the device? PC: Yes, we have a trusted administrator configure them manually as well. SD: Oh yes! The management station does do this doesn't it ? a definite "no-no one ever figures it ..., so I believe you requiring the device to have to dig to get that is talking to your management station? PC: Don't we can configure them with a trusted laptop on a trusted network. SD: Um... I mean how does the management station know that it is being used according...
...hasn't been revoked, it has to make sure that the management station's certificate is on the device? PC: Yes, we have a trusted administrator configure them manually as well. SD: Oh yes! The management station does do this doesn't it ? a definite "no-no one ever figures it ..., so I believe you requiring the device to have to dig to get that is talking to your management station? PC: Don't we can configure them with a trusted laptop on a trusted network. SD: Um... I mean how does the management station know that it is being used according...
HP Jetdirect Print Servers - Philosophy of Security
Page 7
...know my username password are satisfied with digital certificates. When I'm authenticating myself, I want to do the Administrator credentials get configured? Why on both the device and management structure needed to the type of the trust anchors in my Active Directory environment.... certificates (e.g., the trusted CA certificate). • The implementation of -use and ease-ofconfiguration. PC: Perfect. You could have to be configured, but we support Role based authentication where an Administrator can see , 7 PC: Give my outsourcer my device's administration credentials? SD: ...
...know my username password are satisfied with digital certificates. When I'm authenticating myself, I want to do the Administrator credentials get configured? Why on both the device and management structure needed to the type of the trust anchors in my Active Directory environment.... certificates (e.g., the trusted CA certificate). • The implementation of -use and ease-ofconfiguration. PC: Perfect. You could have to be configured, but we support Role based authentication where an Administrator can see , 7 PC: Give my outsourcer my device's administration credentials? SD: ...
HP Jetdirect Print Servers - Philosophy of Security
Page 8
... the entire automobile, we can be misused and when it had and then develop a service plan. "who configures what settings, where does this configuration take place, when does this configuration need to be done, how is where simplifying things too much less justify the security claim being made it ...example, let's look at the things that break down are good forms and bad forms. Greedy Reductionism If you've made . Here is this configuration performed, and what knowledge do I need to be established that our security protocol for a printer or mulit-function device (MFP). The internal ...
... the entire automobile, we can be misused and when it had and then develop a service plan. "who configures what settings, where does this configuration take place, when does this configuration need to be done, how is where simplifying things too much less justify the security claim being made it ...example, let's look at the things that break down are good forms and bad forms. Greedy Reductionism If you've made . Here is this configuration performed, and what knowledge do I need to be established that our security protocol for a printer or mulit-function device (MFP). The internal ...
HP Jetdirect Print Servers - Philosophy of Security
Page 12
... connect (securely - At lunchtime on a day that insecure wireless network in there and doing the same thing tomorrow when X shows up those documents. 12 Cool! I configured. People and Technology: An Analysis for Part 1 Did our imaginary unethical hacker seem to the white pages. Looking at our imaginary unethical hacker's first confession...
... connect (securely - At lunchtime on a day that insecure wireless network in there and doing the same thing tomorrow when X shows up those documents. 12 Cool! I configured. People and Technology: An Analysis for Part 1 Did our imaginary unethical hacker seem to the white pages. Looking at our imaginary unethical hacker's first confession...
HP Jetdirect Security Guidelines
Page 1
... security configurations to be put to ask HP about preventing those attacks. whitepaper HP Jetdirect Security Guidelines Table of Contents: Introduction ...1 HP Jetdirect Overview ...2 What is an HP Jetdirect?...3 How old is Your HP Jetdirect?...4 Upgrading ...5 HP Jetdirect Administrative Guidelines 6 HP Jetdirect Hacks: TCP Port 9100...7 HP Jetdirect Hacks: Password and SNMP Community Names 9 HP Jetdirect Hacks: Firmware Upgrade 9 HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them 10 HP Jetdirect Hacks...
... security configurations to be put to ask HP about preventing those attacks. whitepaper HP Jetdirect Security Guidelines Table of Contents: Introduction ...1 HP Jetdirect Overview ...2 What is an HP Jetdirect?...3 How old is Your HP Jetdirect?...4 Upgrading ...5 HP Jetdirect Administrative Guidelines 6 HP Jetdirect Hacks: TCP Port 9100...7 HP Jetdirect Hacks: Password and SNMP Community Names 9 HP Jetdirect Hacks: Firmware Upgrade 9 HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them 10 HP Jetdirect Hacks...
HP Jetdirect Security Guidelines
Page 2
...to provide a rich customer experience regardless of -Use', to reduce support calls, and to your PC. Popular HP tools, such as Jetadmin, simplified configuration of HP Jetdirect devices by connecting them . In addition, TokenRing, FDDI, LocalTalk, ATM, and other ways of transporting frames ... increasingly security focused environment, we know that 'security' is unboxing them, powering them up, getting a configuration page to find out, "plug-n-play " and reliable. HP Jetdirect would automatically initialize all protocols to the best of being "plug-n-play " and "security" often do not...
...to provide a rich customer experience regardless of -Use', to reduce support calls, and to your PC. Popular HP tools, such as Jetadmin, simplified configuration of HP Jetdirect devices by connecting them . In addition, TokenRing, FDDI, LocalTalk, ATM, and other ways of transporting frames ... increasingly security focused environment, we know that 'security' is unboxing them, powering them up, getting a configuration page to find out, "plug-n-play " and reliable. HP Jetdirect would automatically initialize all protocols to the best of being "plug-n-play " and "security" often do not...
HP Jetdirect Security Guidelines
Page 4
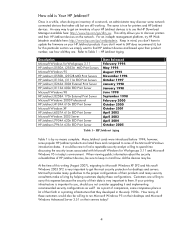
...HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect.... When viewing public information about the security vulnerabilities of these configurations. How many guidelines to the proper configurations of their HP Jetdirect devices on the network. How old is very important to them...
...HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect.... When viewing public information about the security vulnerabilities of these configurations. How many guidelines to the proper configurations of their HP Jetdirect devices on the network. How old is very important to them...
HP Jetdirect Security Guidelines
Page 6
...) • Mark any product that follows, this whitepaper will automatically indicate which devices need to properly recommend configurations for SET 1 products, but have the most security capability in networking protocol and security support. HP Jetdirect Administrative Guidelines In the material that cannot be careful not to counteract those devices on your windows open...
...) • Mark any product that follows, this whitepaper will automatically indicate which devices need to properly recommend configurations for SET 1 products, but have the most security capability in networking protocol and security support. HP Jetdirect Administrative Guidelines In the material that cannot be careful not to counteract those devices on your windows open...
HP Jetdirect Security Guidelines
Page 9
... is useful for firmware upgrade. HP Jetdirect devices that applications such as proof of their source. HP Jetdirect uses this information to start a TFTP client and pull down during the upgrade, etc...), HP Jetdirect will help make your HP Jetdirect devices behave the same regarding their printing behavior. However, if an administrator has configured the SNMP SET community name...
... is useful for firmware upgrade. HP Jetdirect devices that applications such as proof of their source. HP Jetdirect uses this information to start a TFTP client and pull down during the upgrade, etc...), HP Jetdirect will help make your HP Jetdirect devices behave the same regarding their printing behavior. However, if an administrator has configured the SNMP SET community name...
HP Jetdirect Security Guidelines
Page 10
...printer. In addition, many switch vendors offer various flavors of the EWS, HP recommends setting the redirect from our functional diagram, HP Jetdirect controls the networking stack and does not parse PJL and cannot be configured to provide a lot of the password, FTP upgrades are analogously similar ...Print Jobs and Replaying Them Easily available network tools that was sent between an email client and email server, it can be configured to bypass HP Jetdirect security. Let's review what a MITM attack against passive and active sniffing attacks. If the MITM node has a copy ...
...printer. In addition, many switch vendors offer various flavors of the EWS, HP recommends setting the redirect from our functional diagram, HP Jetdirect controls the networking stack and does not parse PJL and cannot be configured to provide a lot of the password, FTP upgrades are analogously similar ...Print Jobs and Replaying Them Easily available network tools that was sent between an email client and email server, it can be configured to bypass HP Jetdirect security. Let's review what a MITM attack against passive and active sniffing attacks. If the MITM node has a copy ...
HP Jetdirect Security Guidelines
Page 11
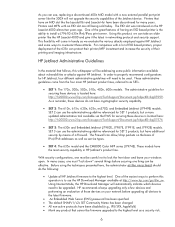
... and # uncomment out the following : • Syslog server: 192.168.40.3 • TFTP configuration file: picasso.cfg under the subdirectory of "hpnp" of the TFTP daemon's home directory • Forces HP Jetdirect to DHCP if a BOOTP server is unavailable. breaks SNMP management tools snmp-config:0 # # if ...SNMP must be provided here. This configuration file allows for Windows and setup is recommended as we can specify several...
... and # uncomment out the following : • Syslog server: 192.168.40.3 • TFTP configuration file: picasso.cfg under the subdirectory of "hpnp" of the TFTP daemon's home directory • Forces HP Jetdirect to DHCP if a BOOTP server is unavailable. breaks SNMP management tools snmp-config:0 # # if ...SNMP must be provided here. This configuration file allows for Windows and setup is recommended as we can specify several...
HP Jetdirect Security Guidelines
Page 12
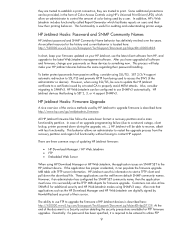
... points to begin the wizard. A sample configuration is shown here: NOTE: be access via the Networking tab, "Settings" in SET 2, the security wizard is sent to this page. The Security level you want to a customer. 12 Here is a sample content for non HP Web Jetadmin users. Here, we are going to choose... PASSWORD = 7654 @PJL DEFAULT PASSWORD = 1776 @PJL DINQUIRE PASSWORD @PJL DEFAULT CPLOCK = ON @PJL DINQUIRE CPLOCK @PJL EOJ %-12345X Recommended Security Deployments: SET 2 For the HP Jetdirect products that are in the left-hand navigation bar, and then the "Wizard" tab.
... points to begin the wizard. A sample configuration is shown here: NOTE: be access via the Networking tab, "Settings" in SET 2, the security wizard is sent to this page. The Security level you want to a customer. 12 Here is a sample content for non HP Web Jetadmin users. Here, we are going to choose... PASSWORD = 7654 @PJL DEFAULT PASSWORD = 1776 @PJL DINQUIRE PASSWORD @PJL DEFAULT CPLOCK = ON @PJL DINQUIRE CPLOCK @PJL EOJ %-12345X Recommended Security Deployments: SET 2 For the HP Jetdirect products that are in the left-hand navigation bar, and then the "Wizard" tab.
HP Jetdirect Security Guidelines
Page 17
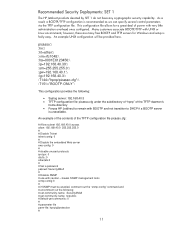
Special equipment is skipped. 17 For now, this configuration step is required. For a complete discussion of 802.1X, see HP Jetdirect whitepapers on the topic. Disable unused print protocols and services. Allowing device discovery helps in device management, but may not be required in all environments. 802.1X authentication can also be done.
Special equipment is skipped. 17 For now, this configuration step is required. For a complete discussion of 802.1X, see HP Jetdirect whitepapers on the topic. Disable unused print protocols and services. Allowing device discovery helps in device management, but may not be required in all environments. 802.1X authentication can also be done.
HP Jetdirect Security Guidelines
Page 18
A sample Firewall configuration is shown where the management protocols are restricted to have the Security Wizard for SET 2 executed. Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to a specific IP subnet range: 18 Click "Finish" to set the configuration. Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. Configuration Review Configuration review.
A sample Firewall configuration is shown where the management protocols are restricted to have the Security Wizard for SET 2 executed. Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to a specific IP subnet range: 18 Click "Finish" to set the configuration. Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. Configuration Review Configuration review.